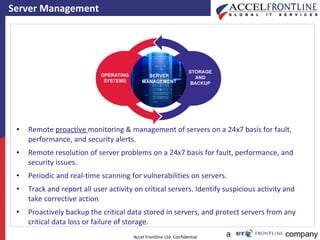
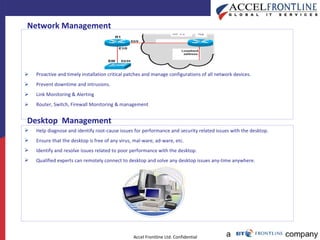
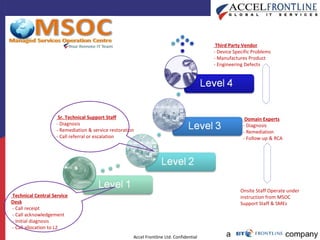
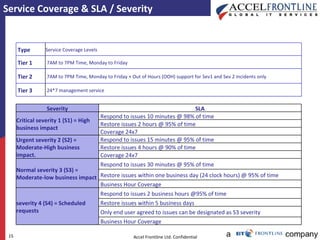
Remote Infrastructure Management Services (RIMS) allows Accel Frontline to remotely monitor, manage, and maintain a customer's IT infrastructure on a 24/7 basis. Key services include server management, infrastructure application management, storage management, network management, desktop management, and a service desk for user support. Accel provides monitoring tools, regular reporting, and service level agreements to ensure issues are addressed in a timely manner based on severity level.
![Remote Infrastructure Management Services [RIMS]](https://image.slidesharecdn.com/aflrimcapabilities-101004022730-phpapp01/75/Afl-rim-capabilities-1-2048.jpg)