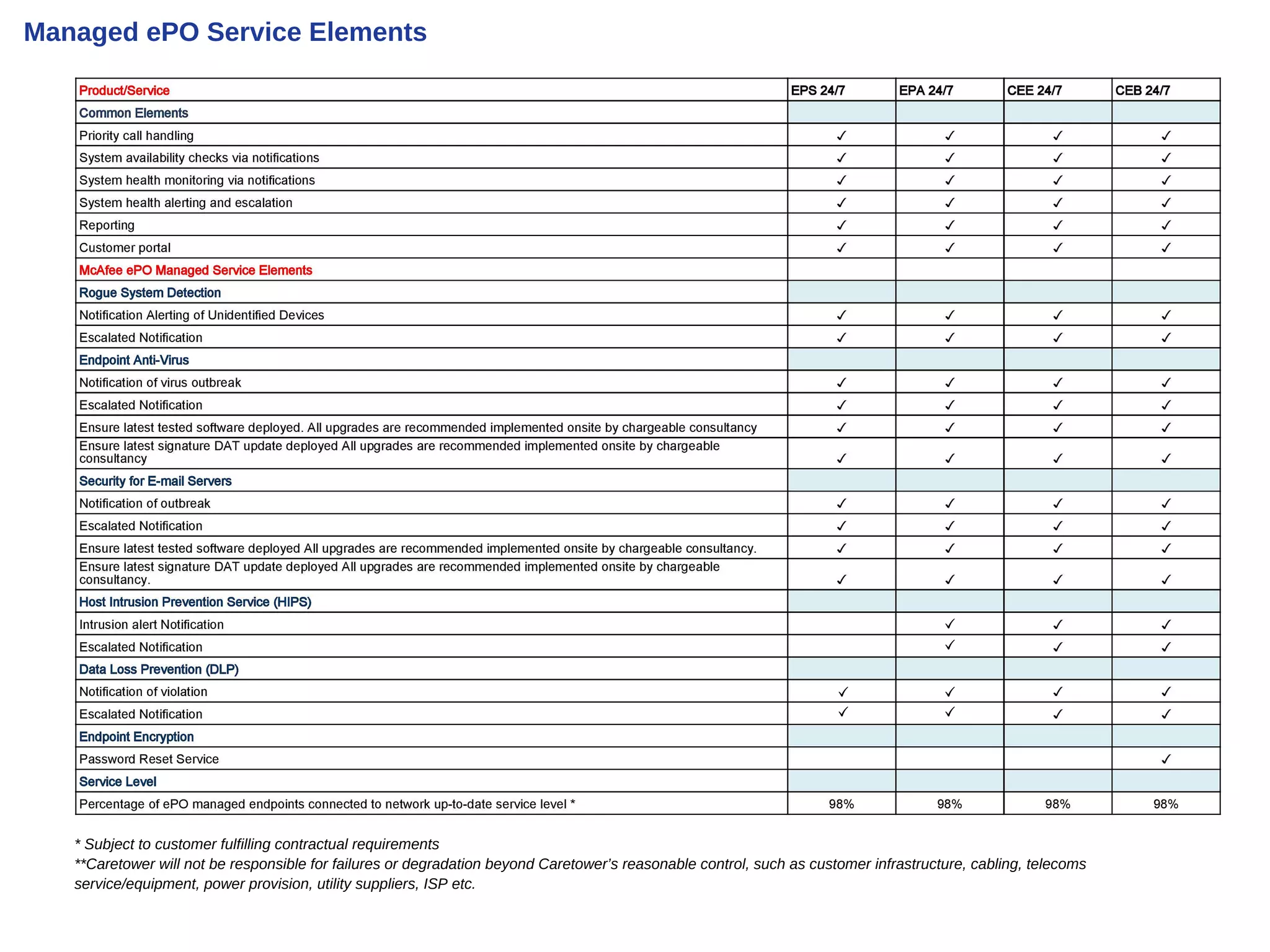
Caretower provides managed endpoint security services through its Security Operations Center. This includes around-the-clock monitoring and management of McAfee ePO and other endpoint security consoles. The service uses a network management system to generate tickets from the ePO console and proactively address incidents. Customers can access reporting and raise tickets through a web portal.