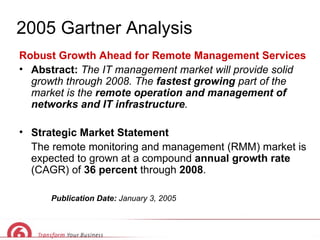
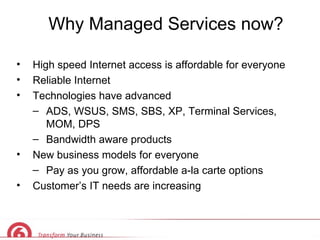
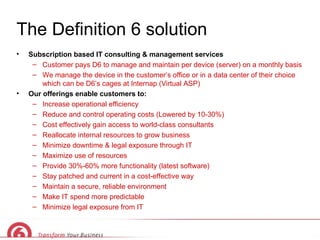
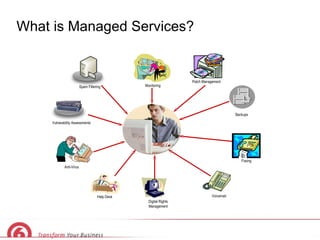
This document discusses how managed IT services can lower costs, reduce risks, and increase capabilities and productivity for businesses. It describes managed services as a $63 billion industry that allows businesses to focus on their core operations while an outside partner remotely manages IT infrastructure through subscription-based services. This helps businesses improve efficiency, reduce costs, and gain access to expert consultants while ensuring their systems remain secure, optimized and up to date.