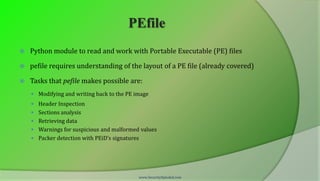
The document outlines an advanced malware analysis training series provided by SecurityXploded, highlighting the use of tools such as pefile, pydbg, and IDA Python. It includes hands-on instructions for working with portable executable files and debugging techniques essential for malware analysis. The training is currently offered for free at local meets, with the trainers expressing appreciation for community support and resources.











![Reference
Complete Reference Guide for Advanced Malware Analysis Training
[Include links for all the Demos & Tools]
www.SecurityXploded.com](https://image.slidesharecdn.com/advancedmalwareanalysistrainingsession5-reversingautomation-130414005826-phpapp01/85/Advanced-Malware-Analysis-Training-Session-5-Reversing-Automation-19-320.jpg)
