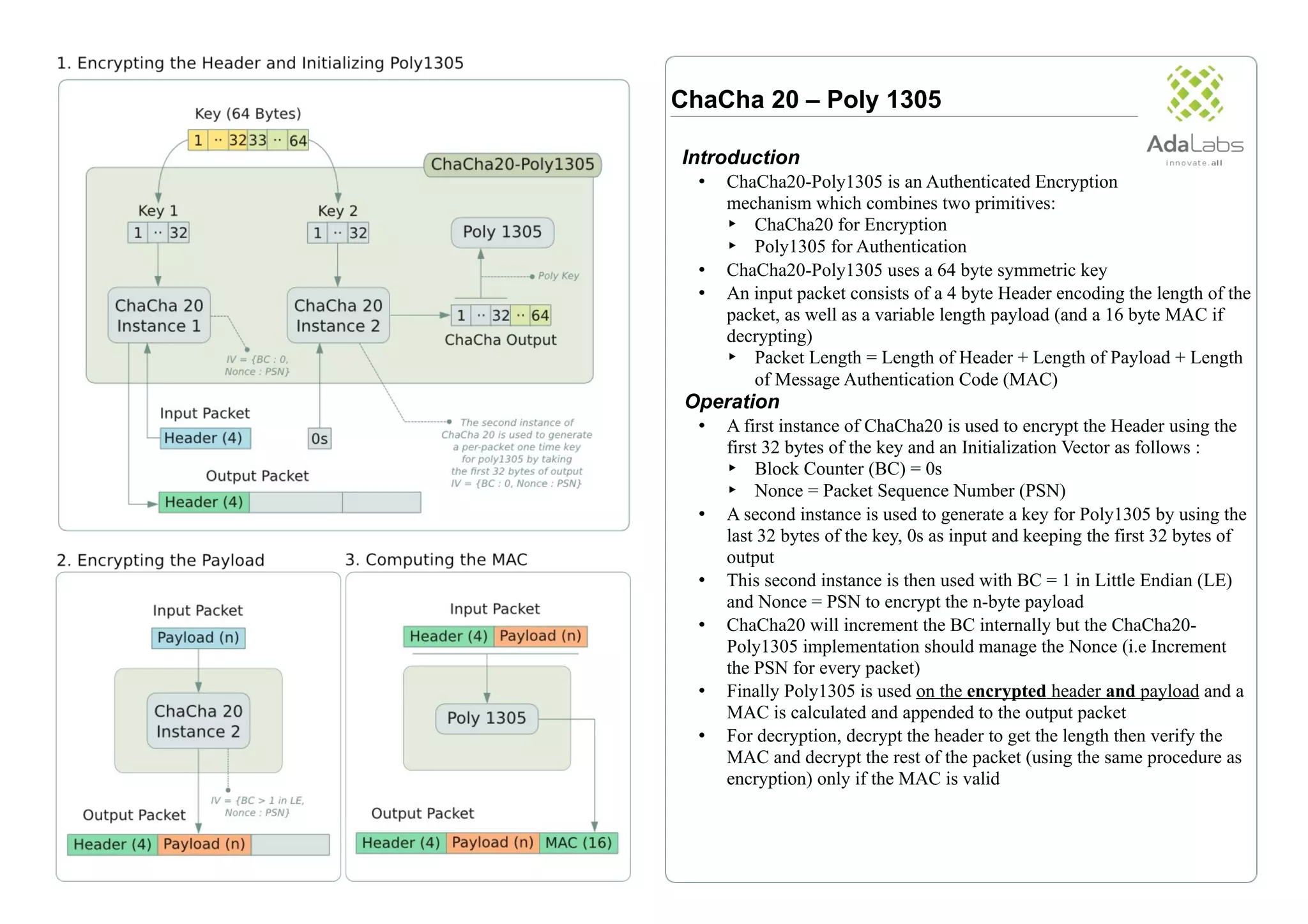
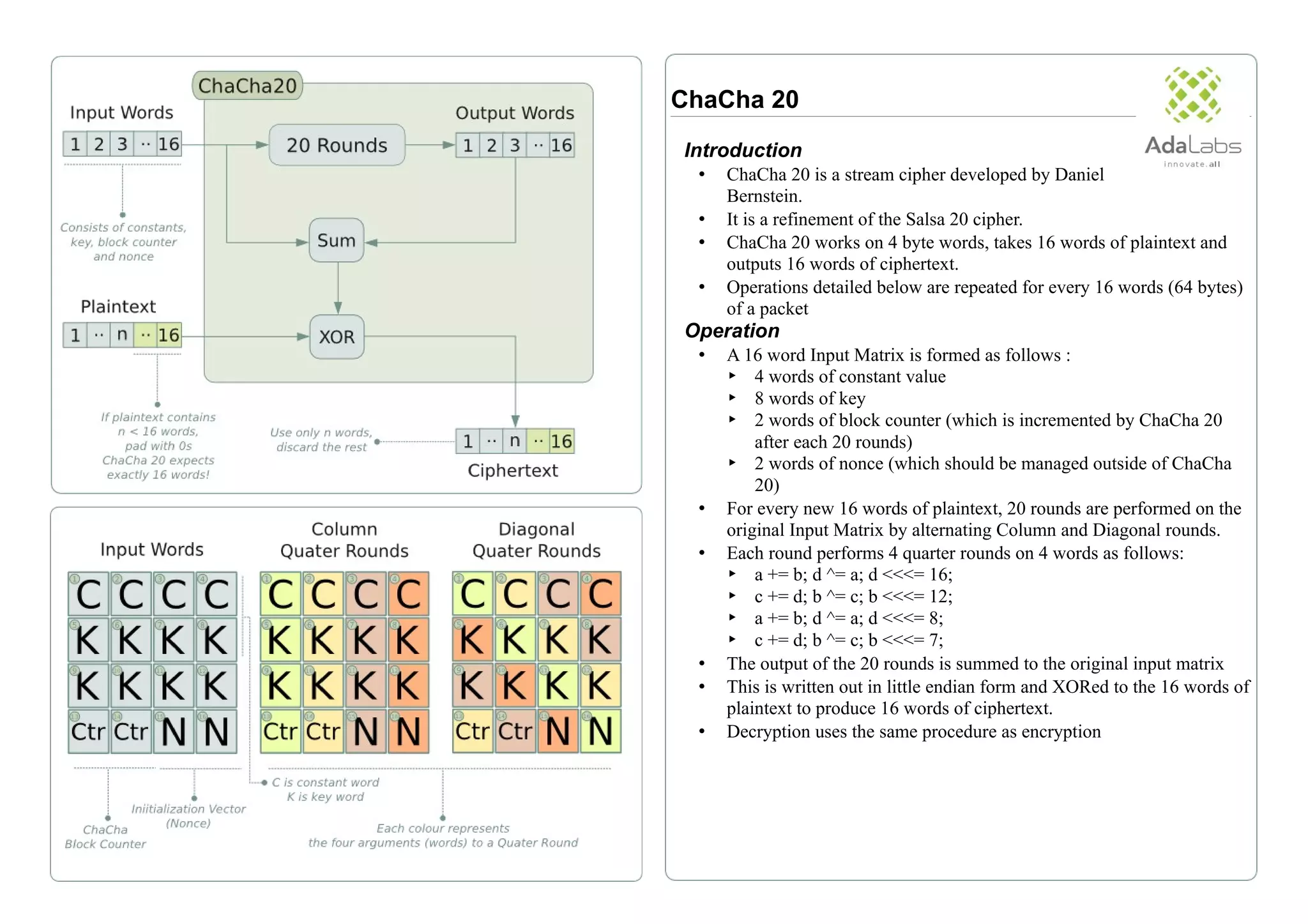
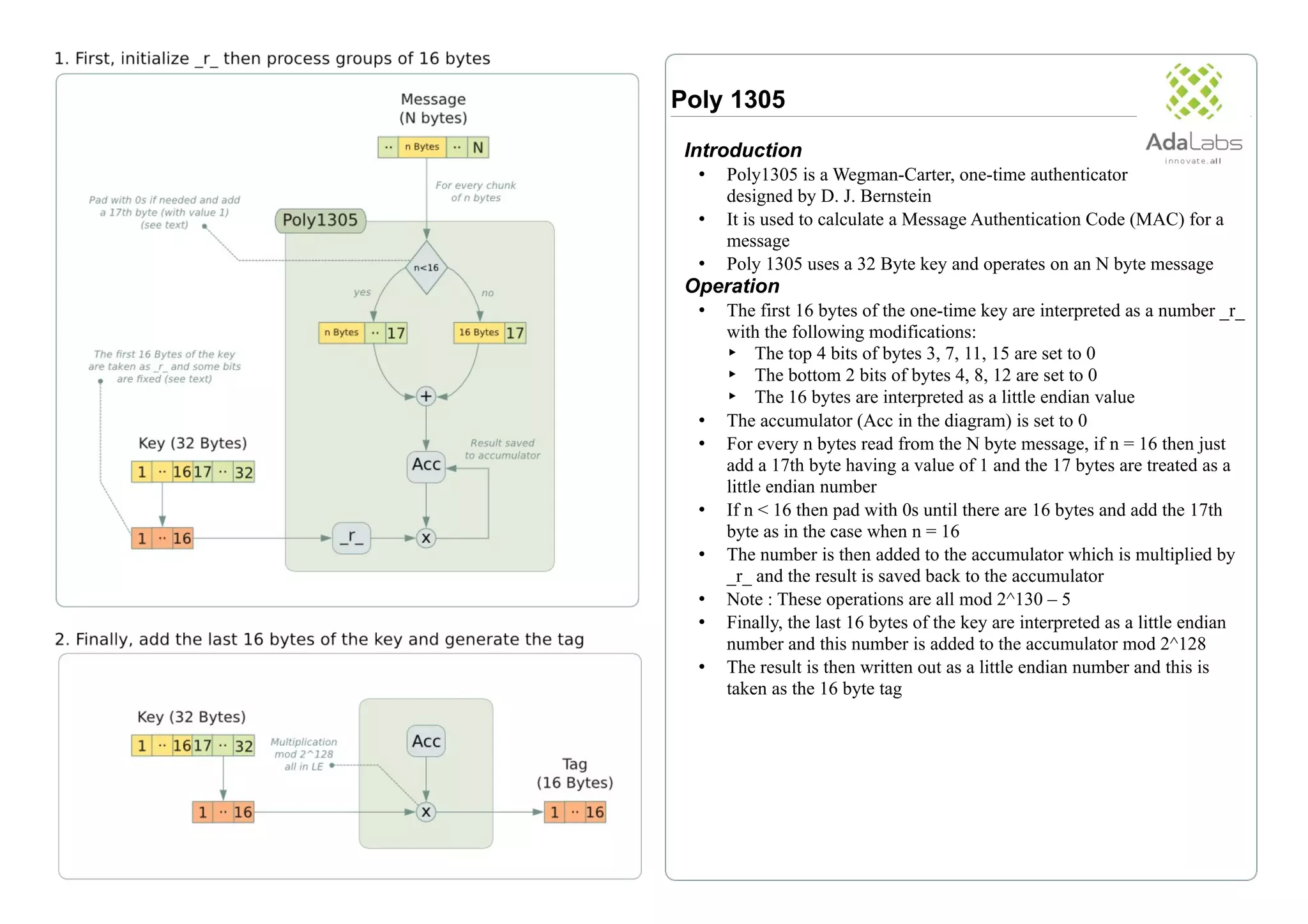
ChaCha20-Poly1305 is an authenticated encryption scheme combining the ChaCha20 stream cipher for encryption and Poly1305 for message authentication, utilizing a 64-byte symmetric key. The encryption process involves encrypting packet headers and payloads, while decryption verifies the message authentication code before proceeding. The document also details the operational mechanics of both ChaCha20 and Poly1305, including their respective input structures and encryption algorithms.