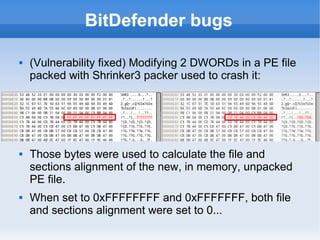
The document discusses breaking and attacking antivirus software. It begins by introducing common features of antivirus engines like being written in C/C++ and supporting various file formats. It then discusses how installing antivirus software increases a system's attack surface and how antivirus engines can contain vulnerabilities. Specific examples of vulnerabilities found in antivirus products from Panda, ClamAV, and others are then presented, including multiple local privilege escalation issues found in Panda Global Protection 2013. Exploitation techniques for antivirus engines are also covered.