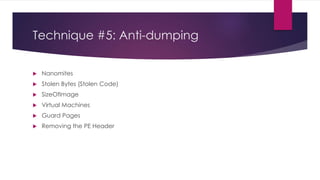
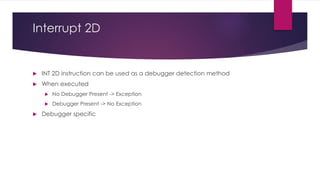
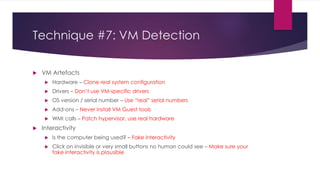
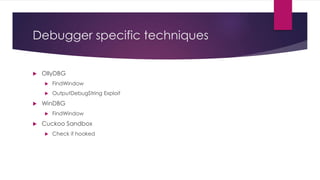
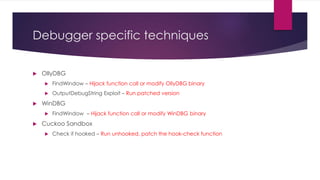
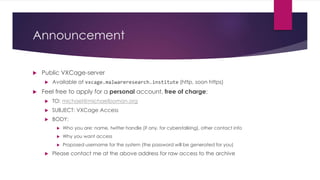
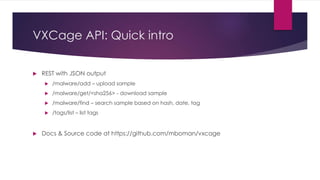
This document discusses techniques that malware authors use to frustrate malware analysts, including inserting breakpoints, manipulating timing functions, exploiting Windows internals like debug flags and objects, anti-dumping methods, VM detection, and debugger-specific tricks. The author also announces a public malware repository and API called VXCage for sharing samples.
![About me
4th year speaking at 44CON
- 2012: Malware as a hobby [P]
- 2013: Controlling a PC using Arduino [WS]
- 2014: Malware analysis as a big data problem [P]
- 2015: Malware anti-reversing [P], Indicators of Compromise [WS]
Malware Researcher, Founder Malware Research Institute
6 kids, one more on the way…](https://image.slidesharecdn.com/pbccrcljrbu6kfqbkjx5-signature-7f4476bdbc458de08a52069bea7e85e657379d50b1caa293e7e3560baf0b908a-poli-150911110735-lva1-app6891/85/How-to-drive-a-malware-analyst-crazy-2-320.jpg)


![How INT3 breakpoints work
mov eax, fs:[0x30]
mov eax, [eax + 0x0c] // <- Break here
mov eax, [eax + 0x0c]
mov dword ptr [eax + 0x20], NewSize](https://image.slidesharecdn.com/pbccrcljrbu6kfqbkjx5-signature-7f4476bdbc458de08a52069bea7e85e657379d50b1caa293e7e3560baf0b908a-poli-150911110735-lva1-app6891/85/How-to-drive-a-malware-analyst-crazy-7-320.jpg)
![How INT3 breakpoints work
mov eax, fs:[0x30]
int 3h [garbage] // <- EP
mov eax, [eax + 0x0c]
mov dword ptr [eax + 0x20], NewSize](https://image.slidesharecdn.com/pbccrcljrbu6kfqbkjx5-signature-7f4476bdbc458de08a52069bea7e85e657379d50b1caa293e7e3560baf0b908a-poli-150911110735-lva1-app6891/85/How-to-drive-a-malware-analyst-crazy-8-320.jpg)
![How INT3 breakpoints work
mov eax, fs:[0x30]
mov eax, [eax + 0x0c] // <- restored by debugger
mov eax, [eax + 0x0c]
mov dword ptr [eax + 0x20], NewSize](https://image.slidesharecdn.com/pbccrcljrbu6kfqbkjx5-signature-7f4476bdbc458de08a52069bea7e85e657379d50b1caa293e7e3560baf0b908a-poli-150911110735-lva1-app6891/85/How-to-drive-a-malware-analyst-crazy-9-320.jpg)
![Technique #1: Breakpoints
INT 3h
Look for code that scans memory for 0xCC [INT3] and/or 0xCD 0x03 [INT
(immediate) 3]
Memory Breakpoints
Look for memory allocations with PAGE_GUARD flag set
Hardware Breakpoints
Win32 GetThreadContext and SetThreadContext
Structured Exception Handling](https://image.slidesharecdn.com/pbccrcljrbu6kfqbkjx5-signature-7f4476bdbc458de08a52069bea7e85e657379d50b1caa293e7e3560baf0b908a-poli-150911110735-lva1-app6891/85/How-to-drive-a-malware-analyst-crazy-12-320.jpg)
![Technique #2: Timing
RDTSC (ReaD TimeStampClock)
Win32 Timing Functions
GetTickCount
timeGetTime
QueryPerformanceCounter
[…]](https://image.slidesharecdn.com/pbccrcljrbu6kfqbkjx5-signature-7f4476bdbc458de08a52069bea7e85e657379d50b1caa293e7e3560baf0b908a-poli-150911110735-lva1-app6891/85/How-to-drive-a-malware-analyst-crazy-13-320.jpg)

![Technique #3: Windows Internals
ProcessDebugFlags
Check NtQueryProcessInformation() calls for [undocumented] ProcessDebugFlags (0x1f) object
Hook NtQueryProcessInformation(), lie about the ProcessDebugFlags value
Debug Object Handle
Hook NtQueryInformationProcess(), remove any links to debug objects
Thread Hiding
Remove any HideThreadFromDebugger class passed into NtSetInformationThread
BlockInput
Hook it to a NO-OP
OutputDebugString
Hook it to always return error](https://image.slidesharecdn.com/pbccrcljrbu6kfqbkjx5-signature-7f4476bdbc458de08a52069bea7e85e657379d50b1caa293e7e3560baf0b908a-poli-150911110735-lva1-app6891/85/How-to-drive-a-malware-analyst-crazy-21-320.jpg)