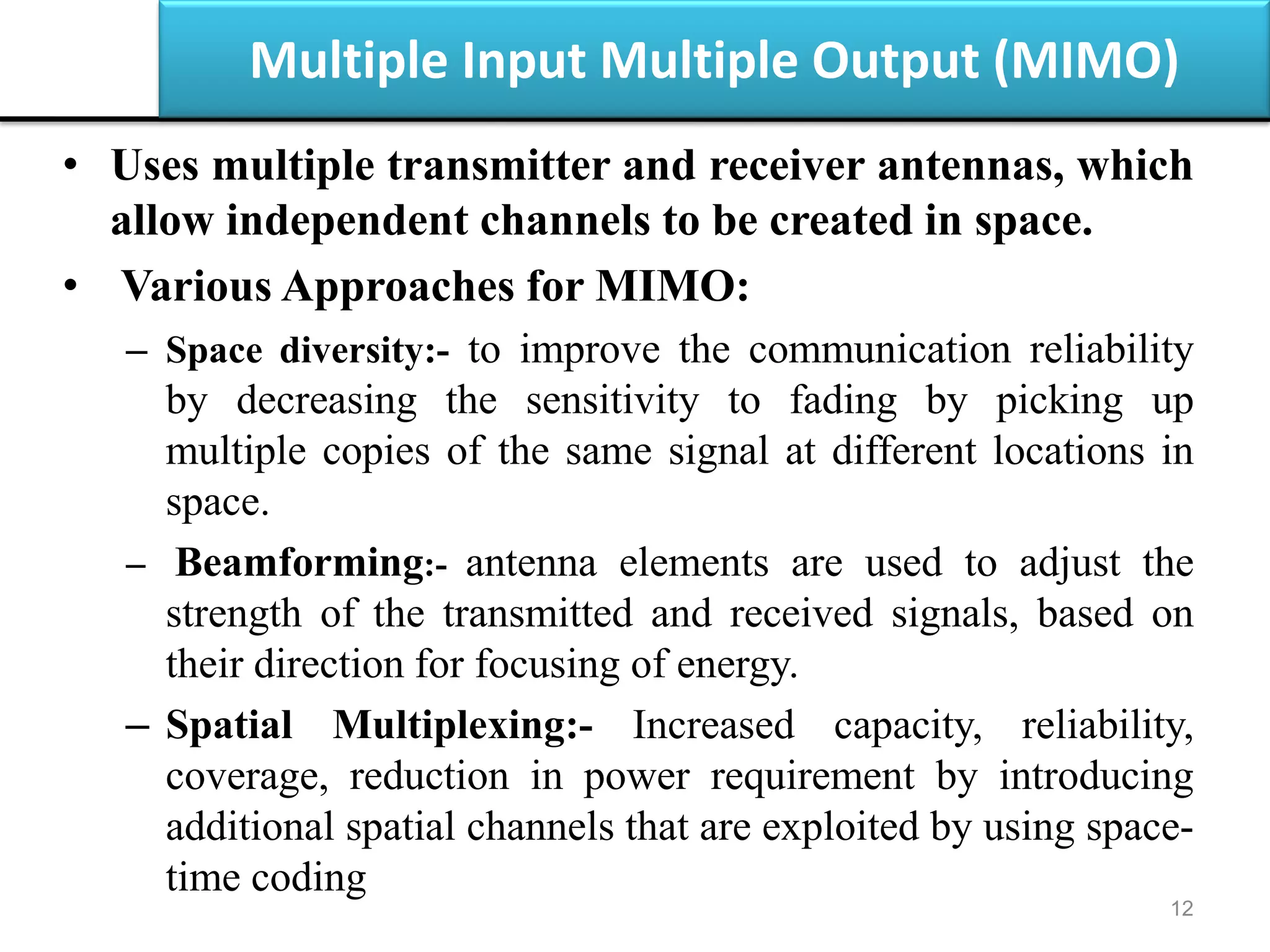
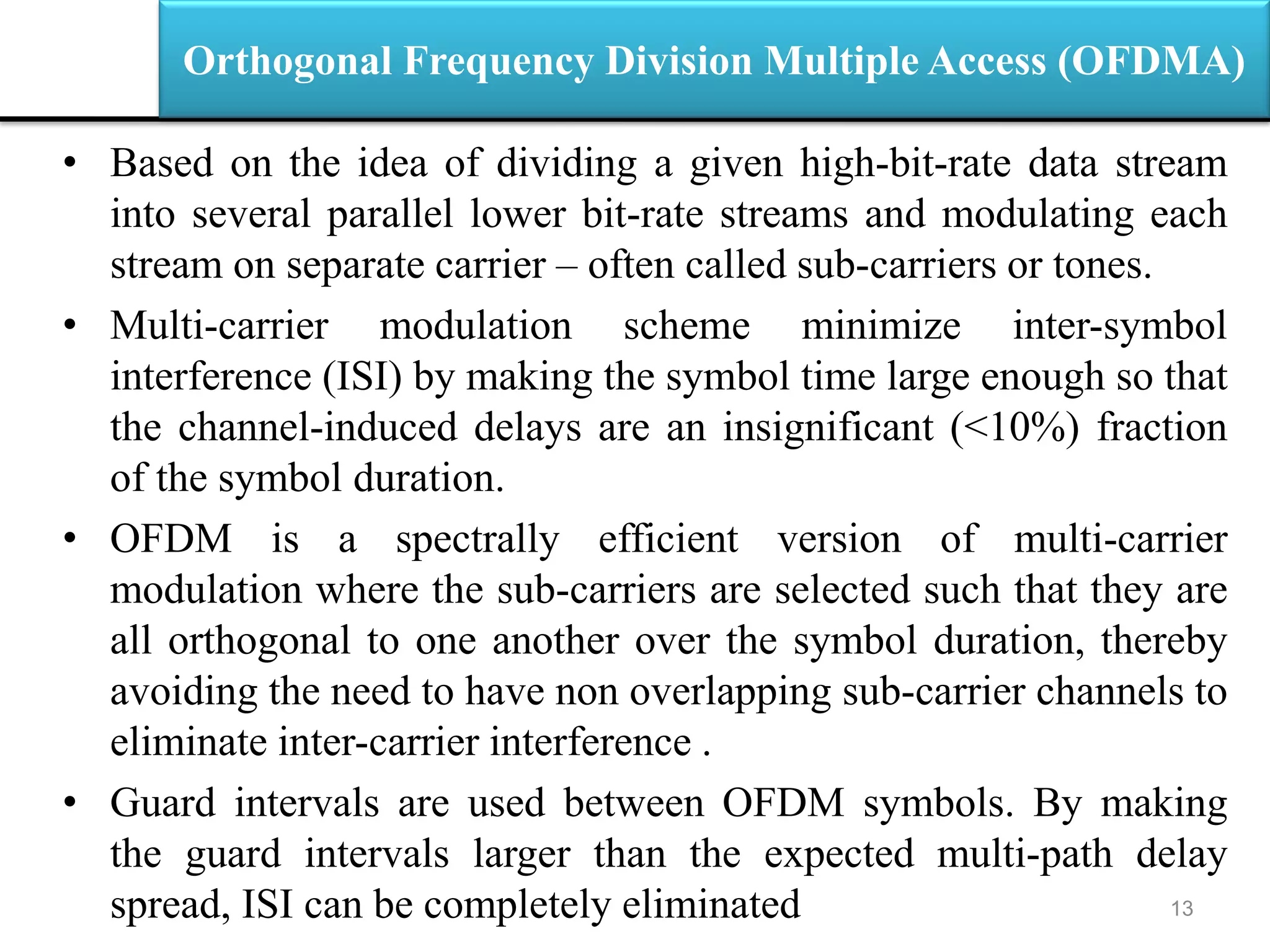
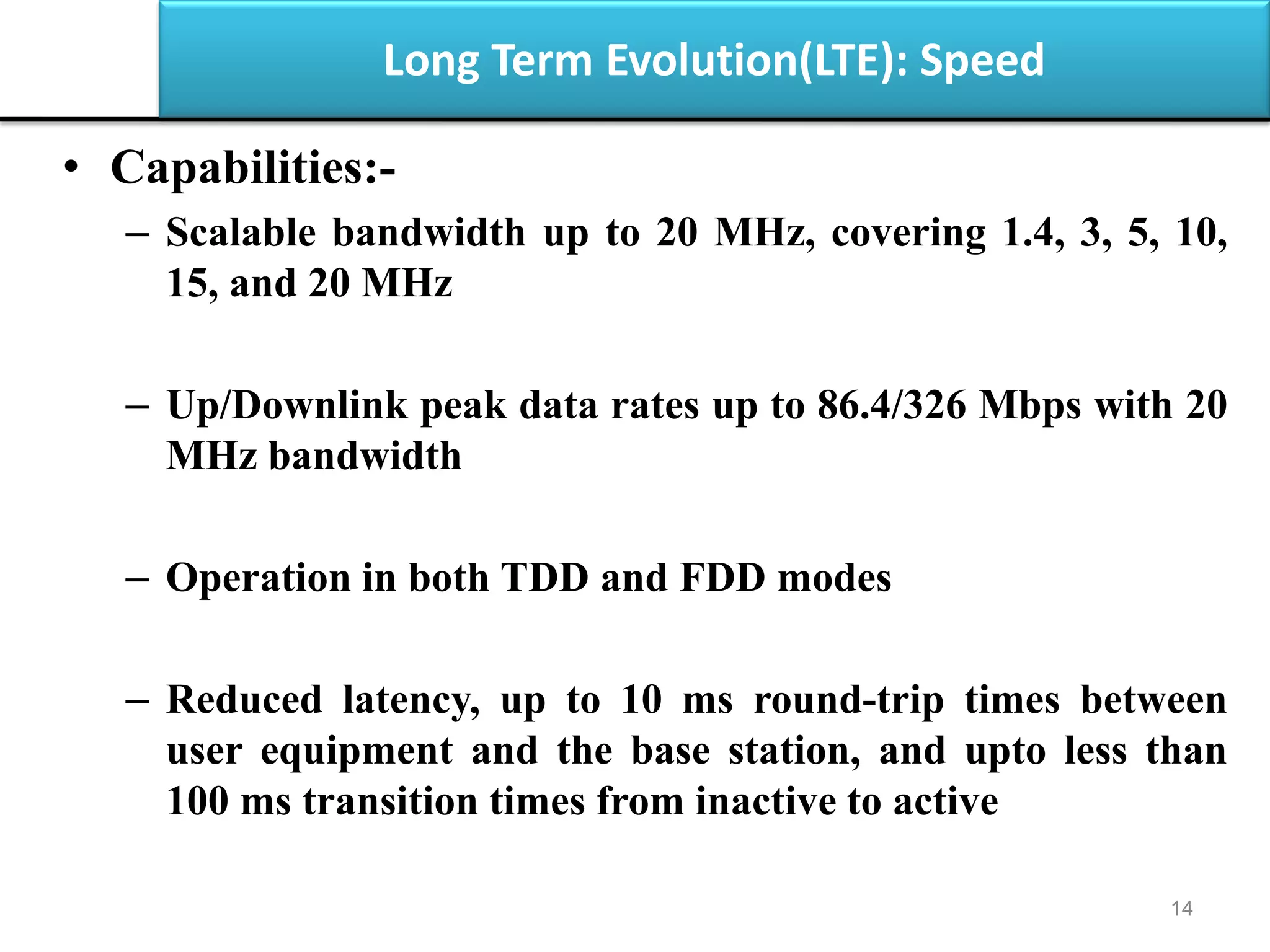
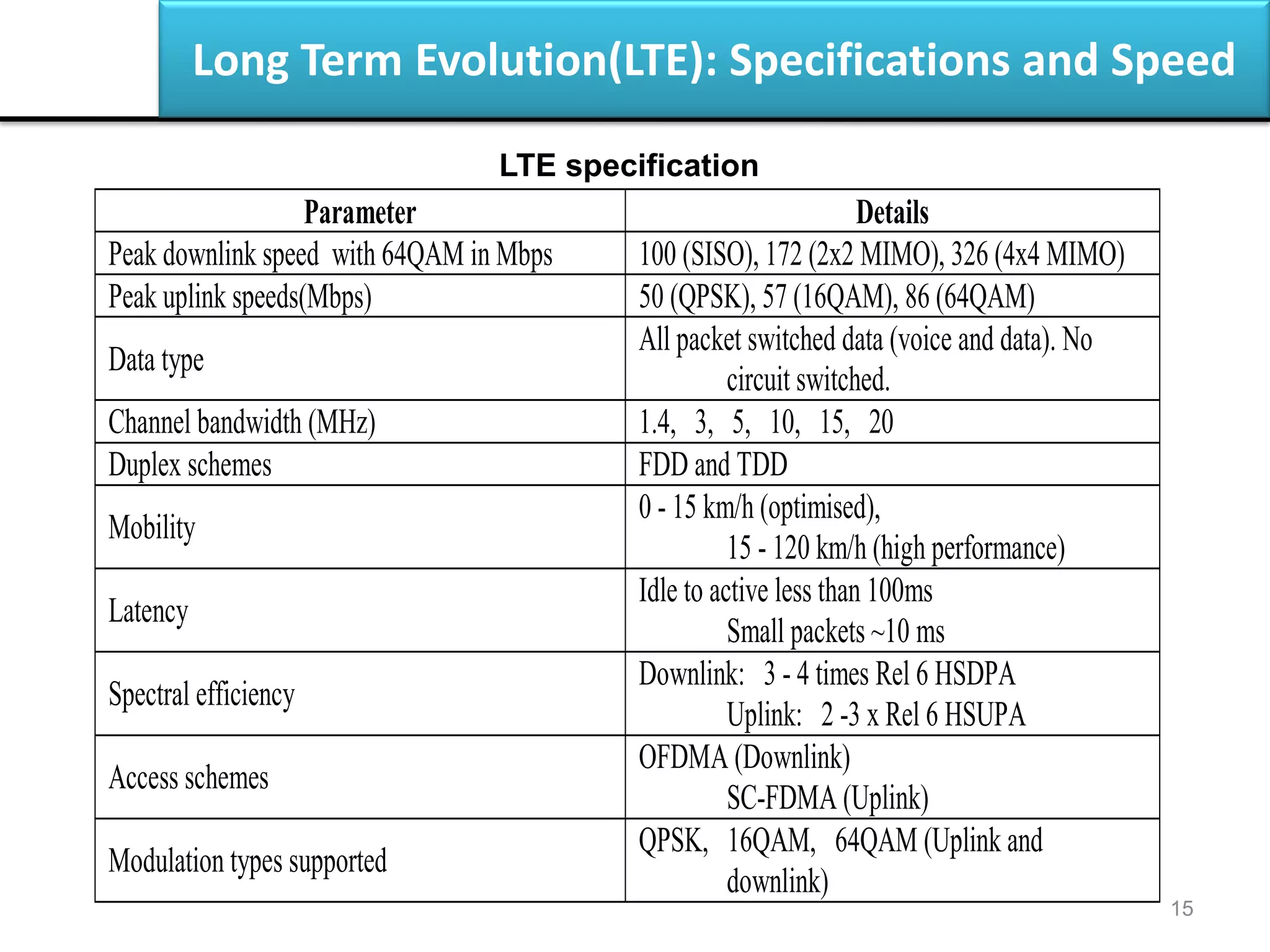
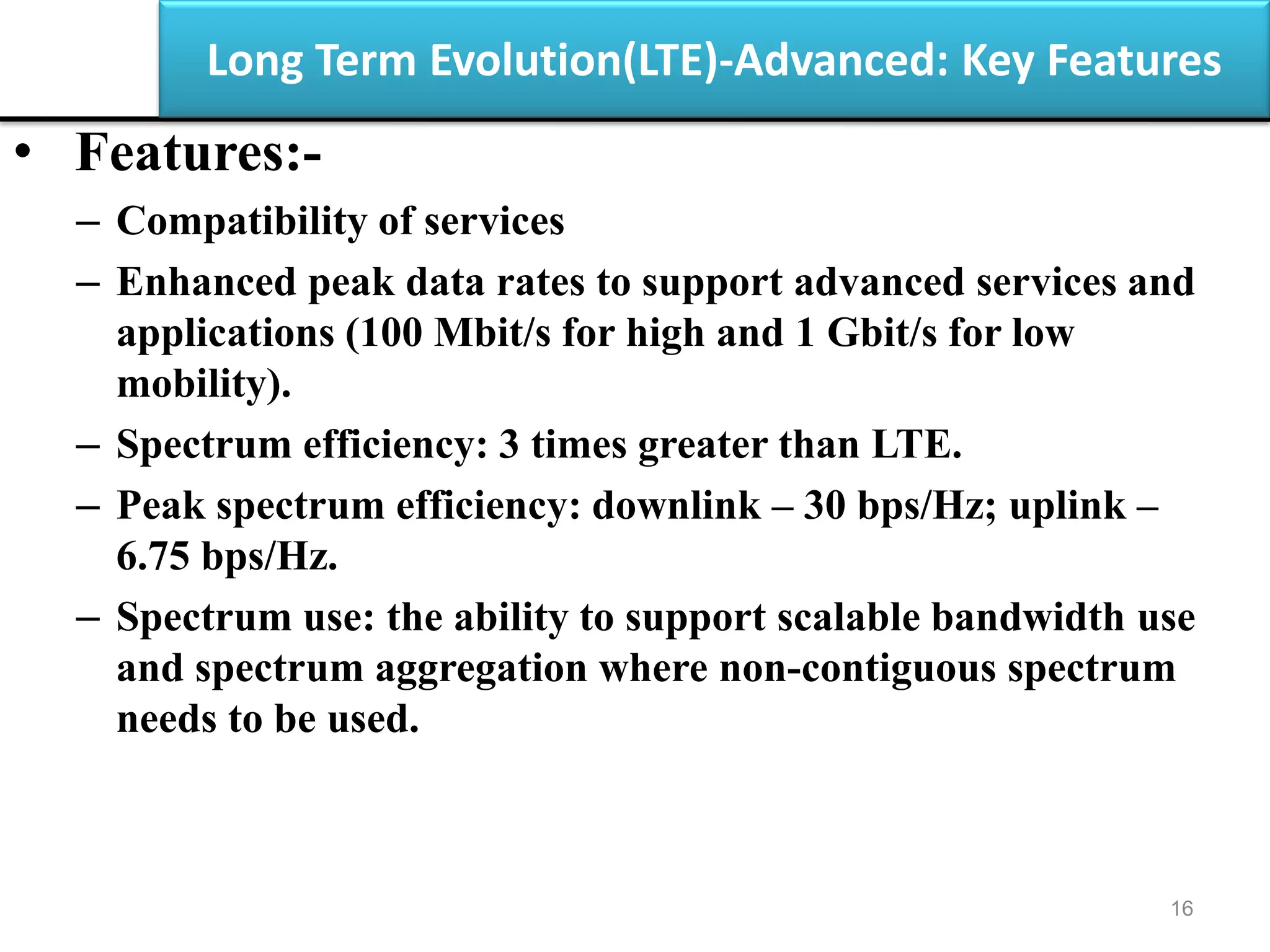
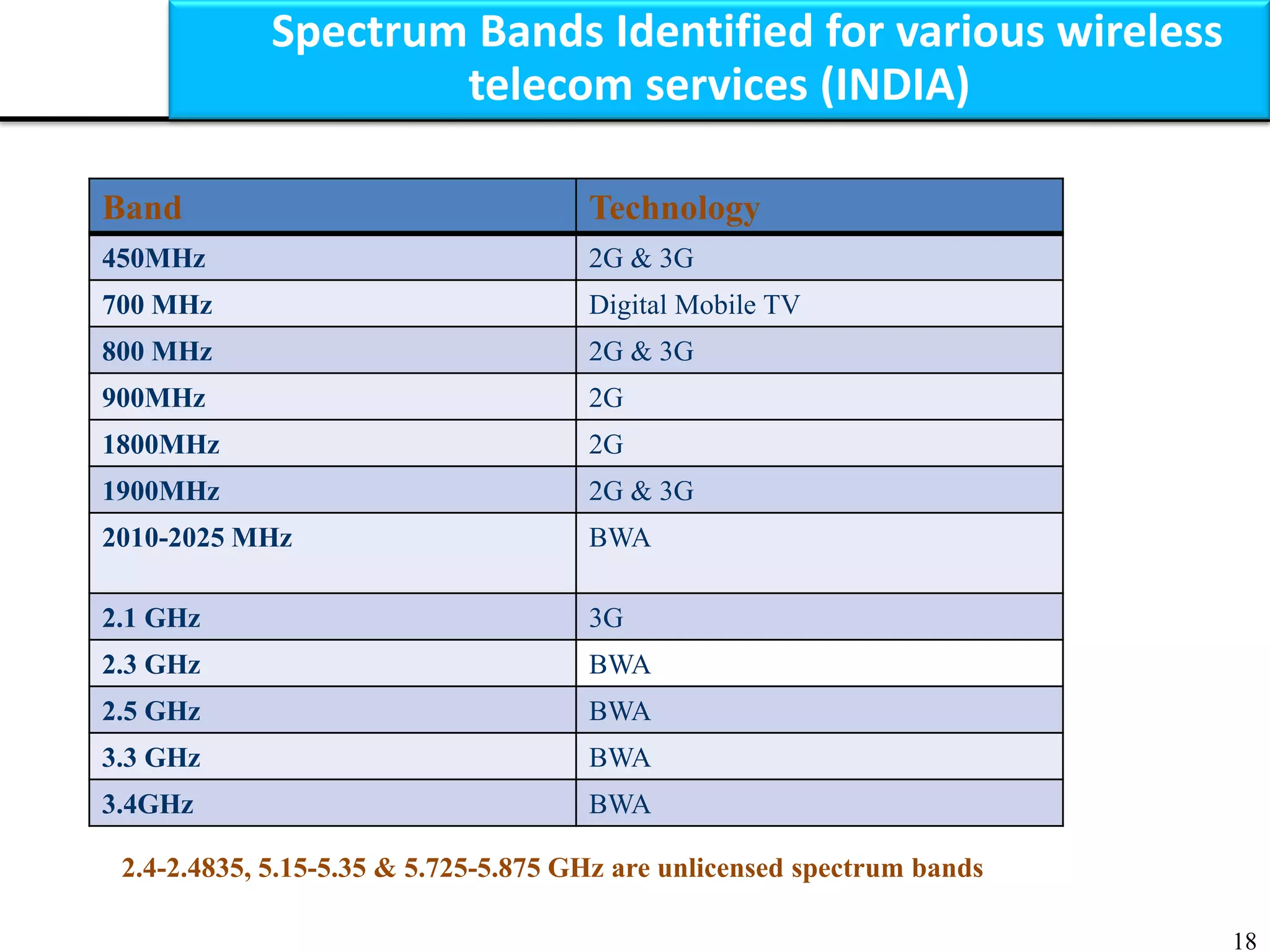
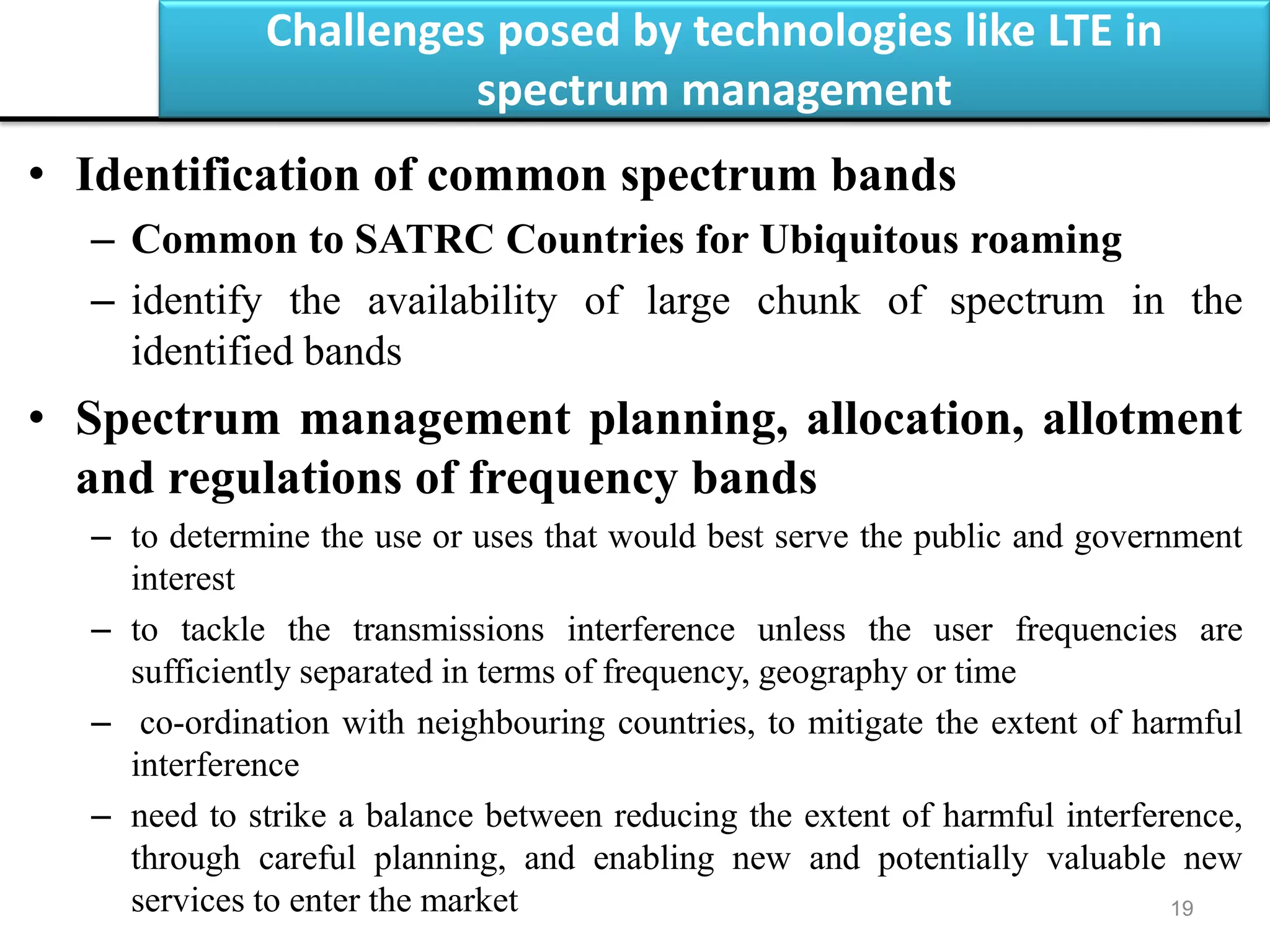
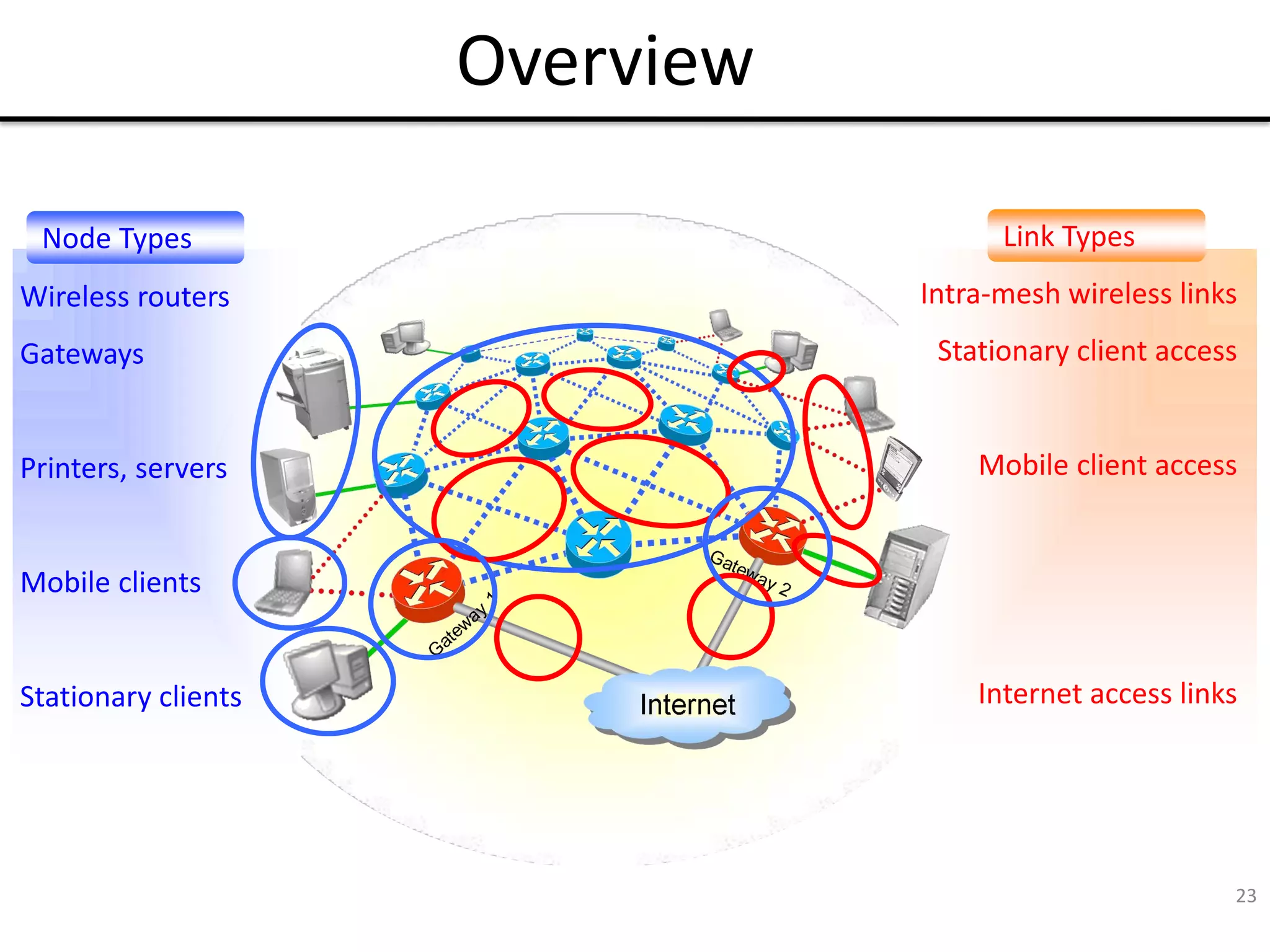
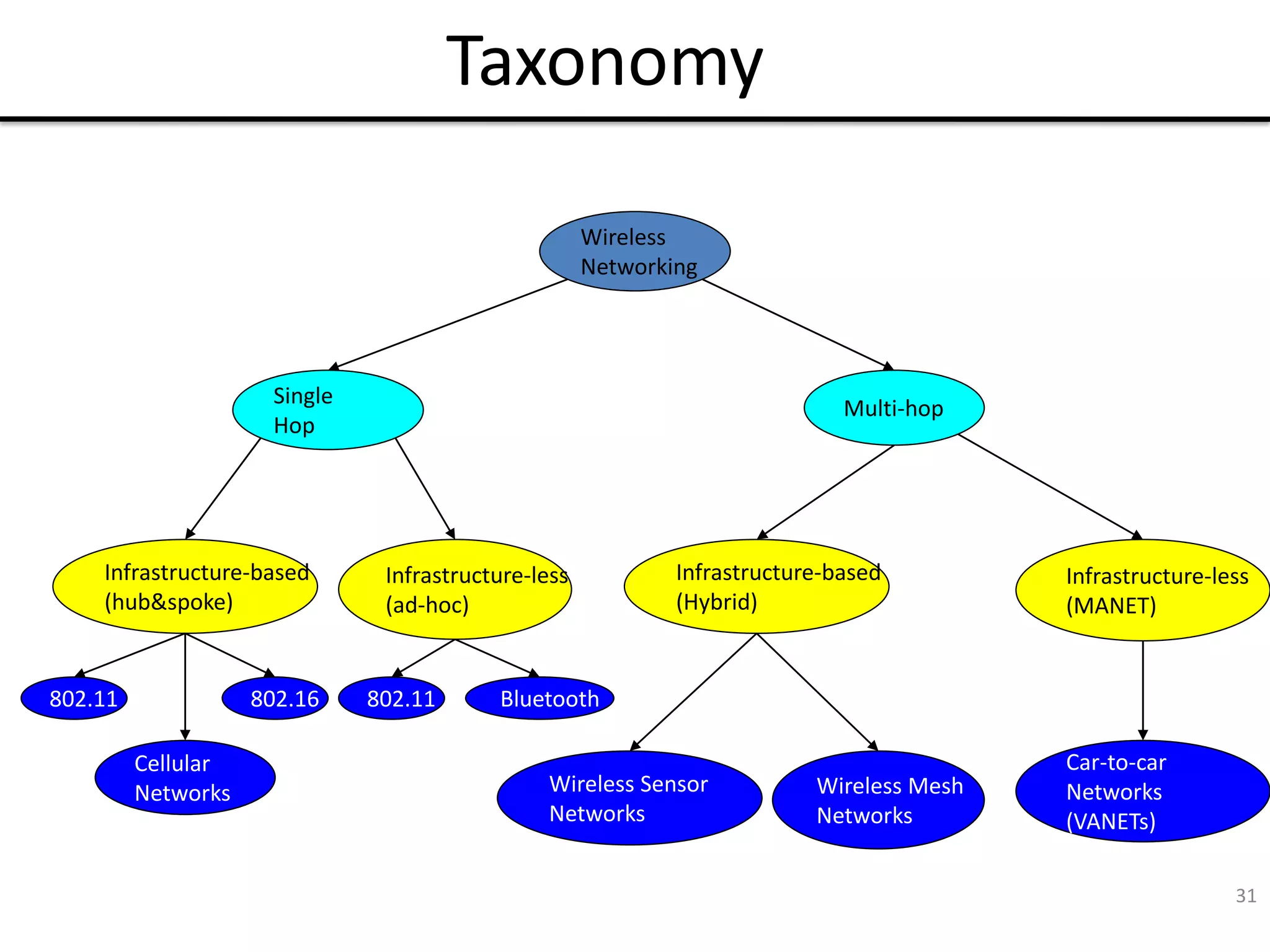
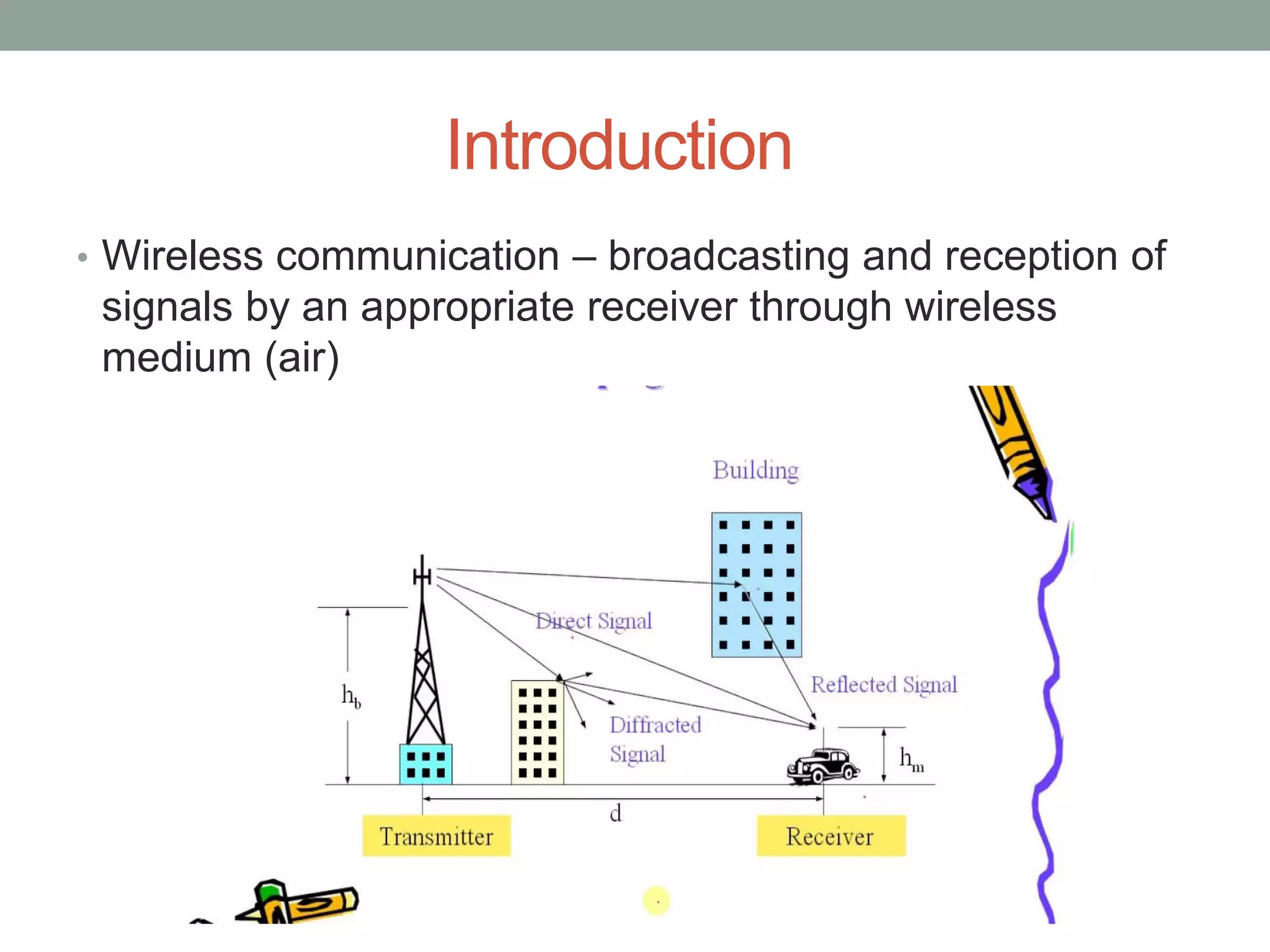
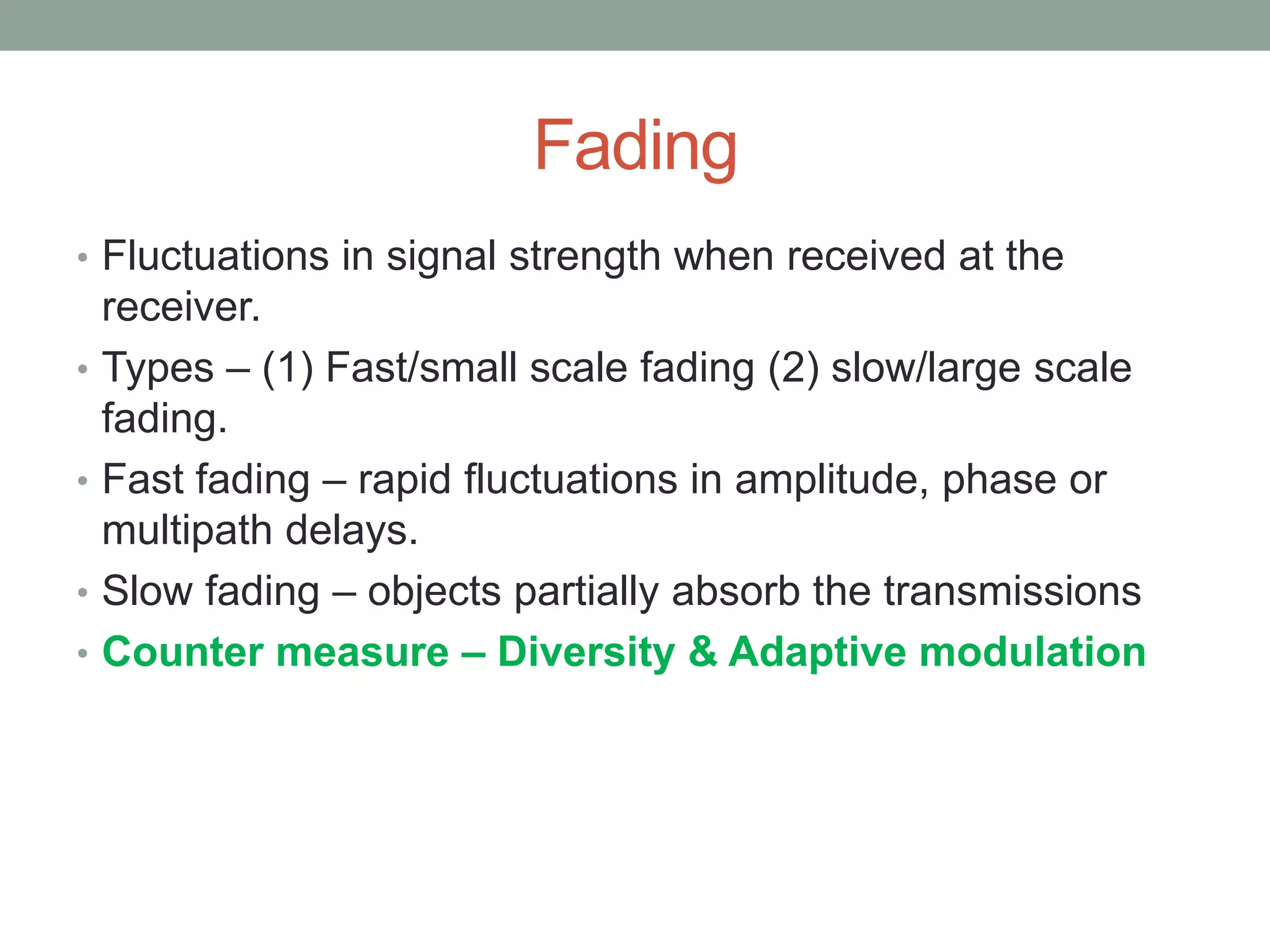
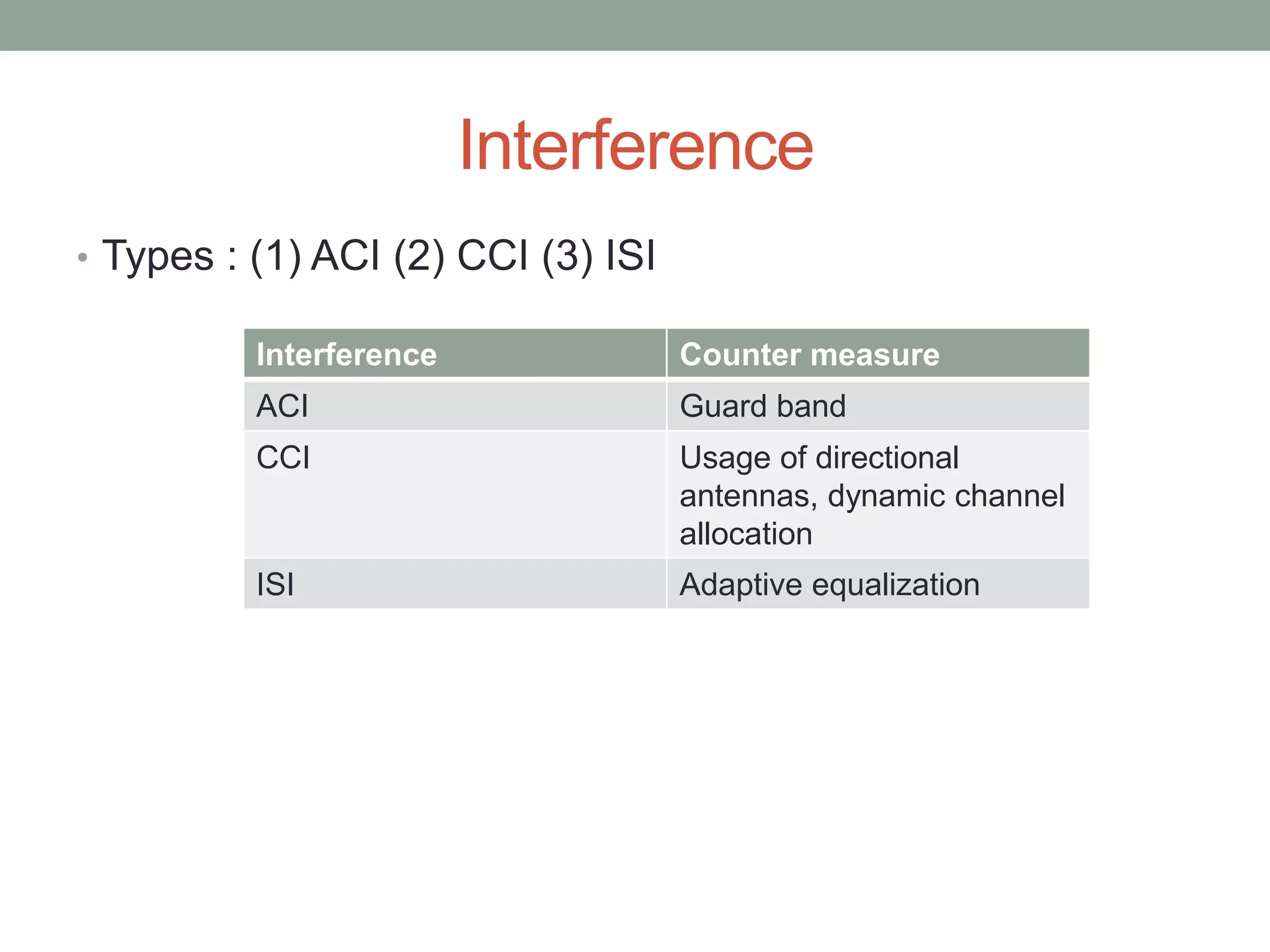
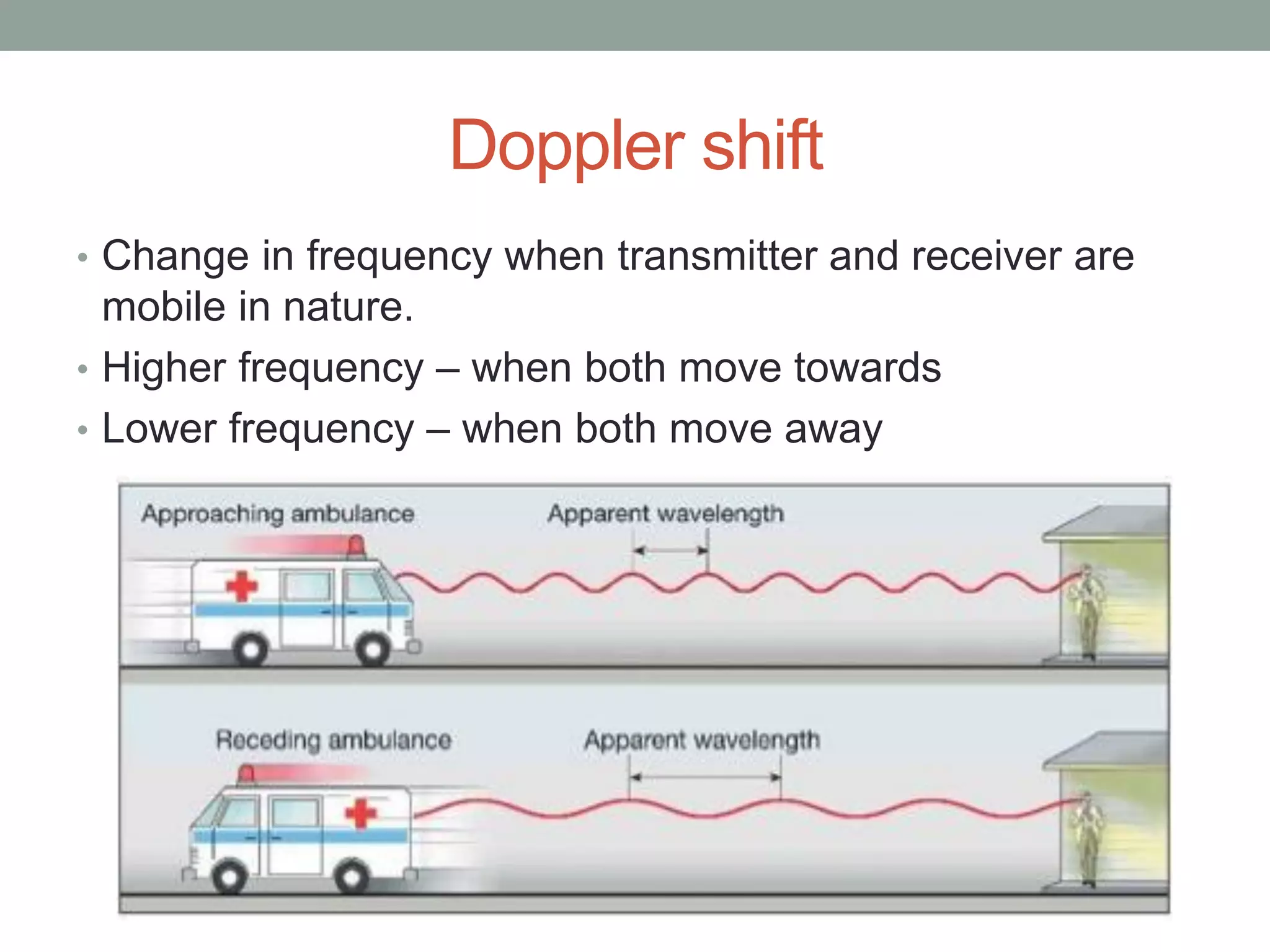
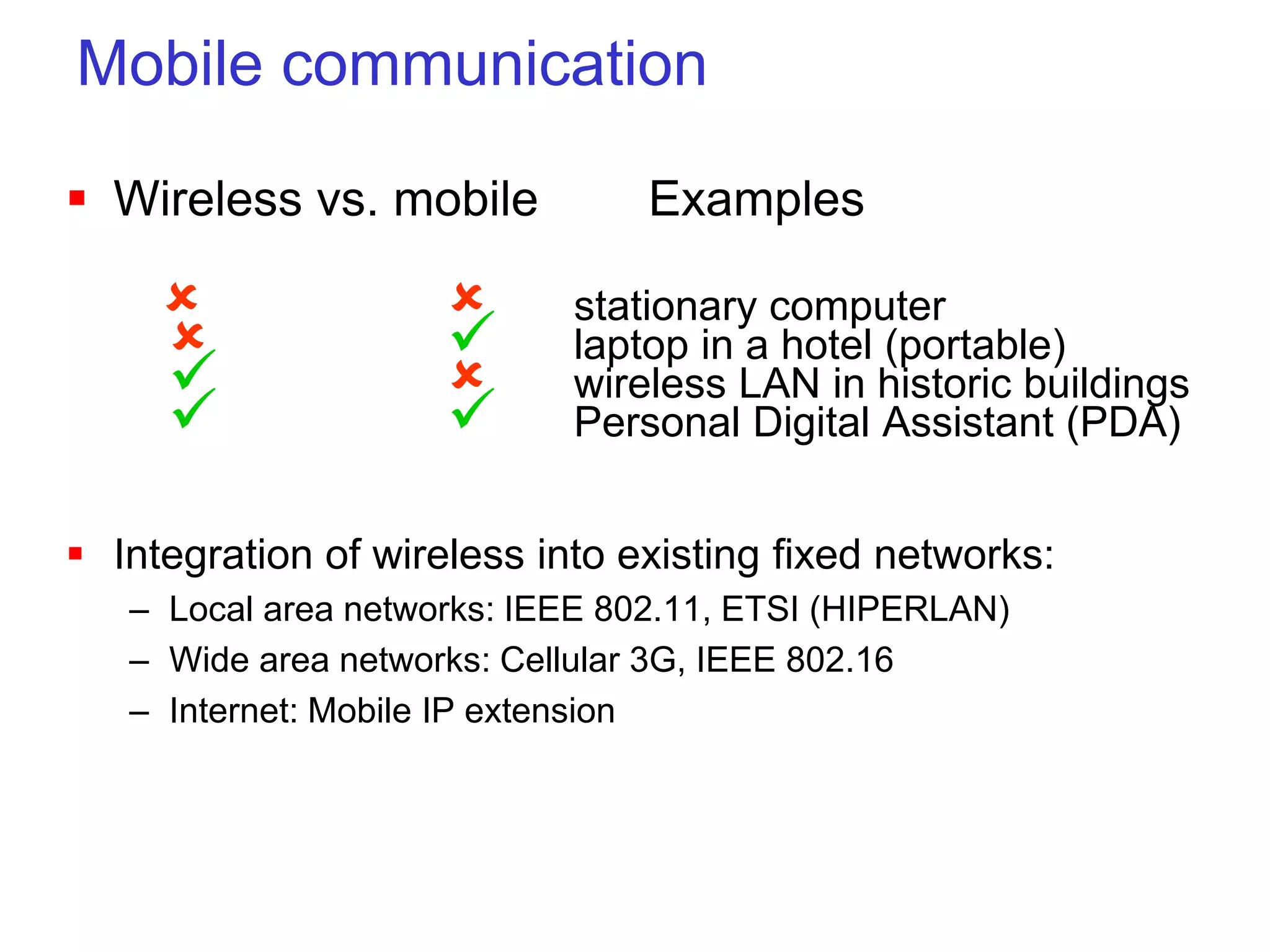
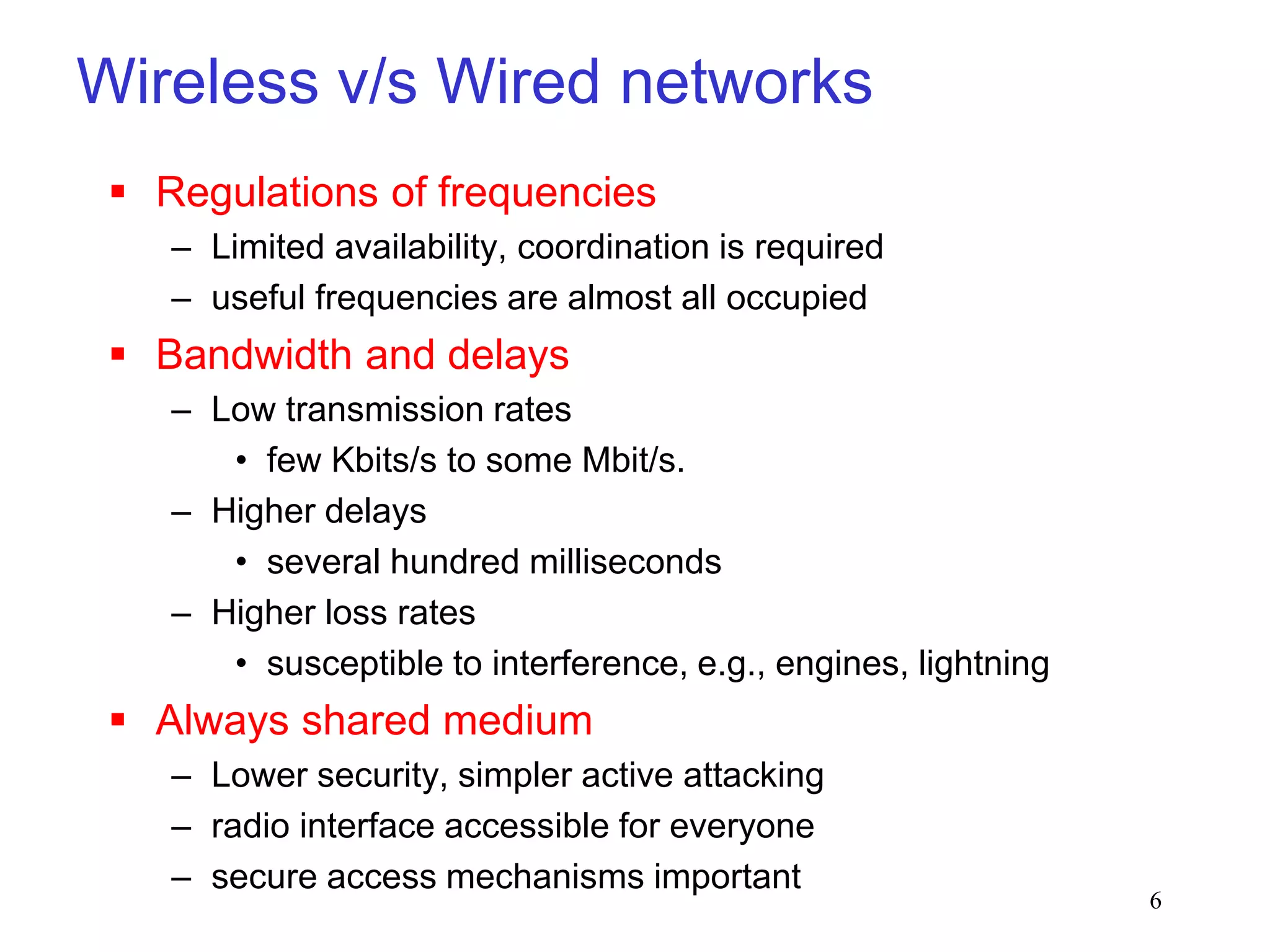
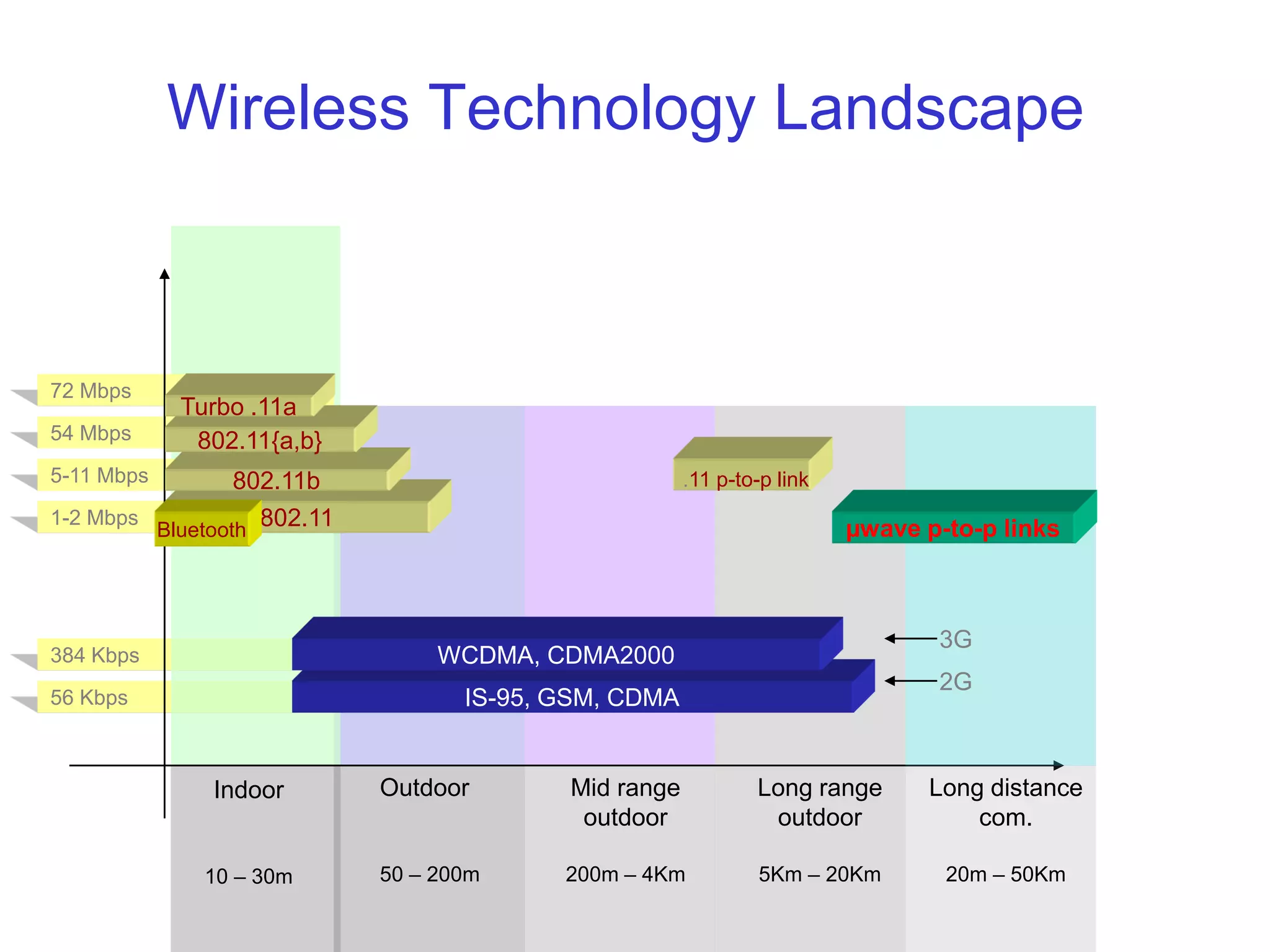
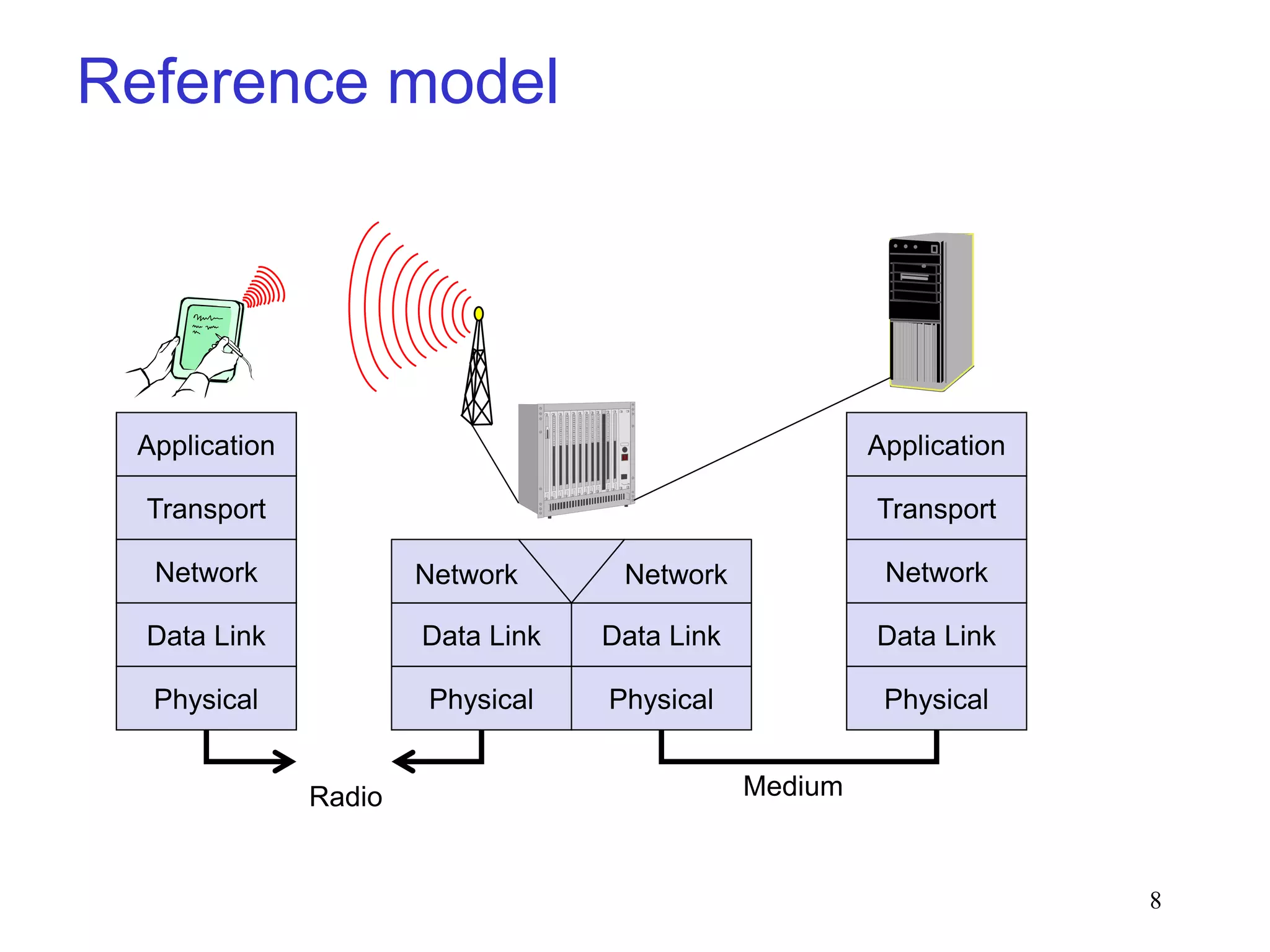
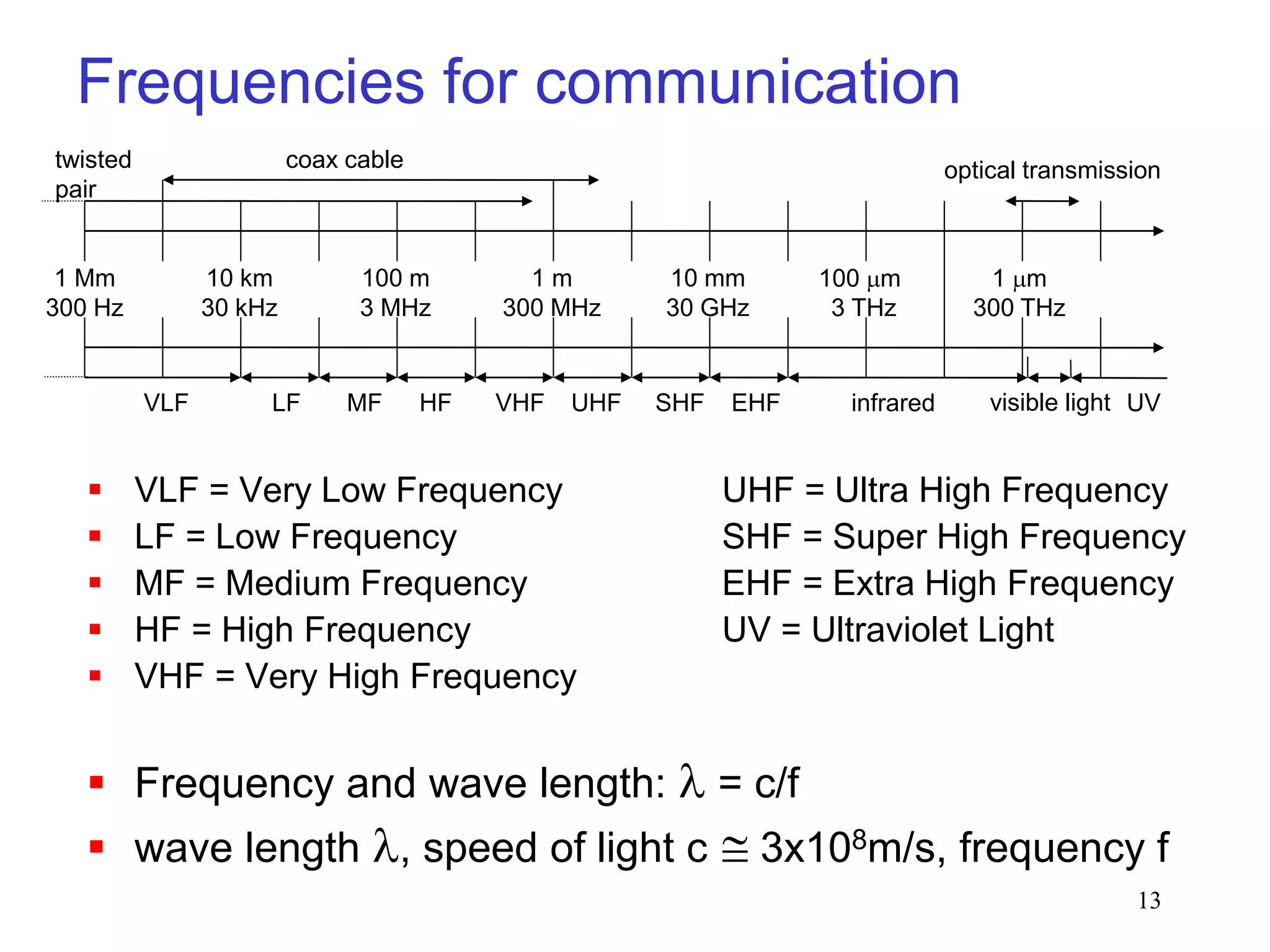
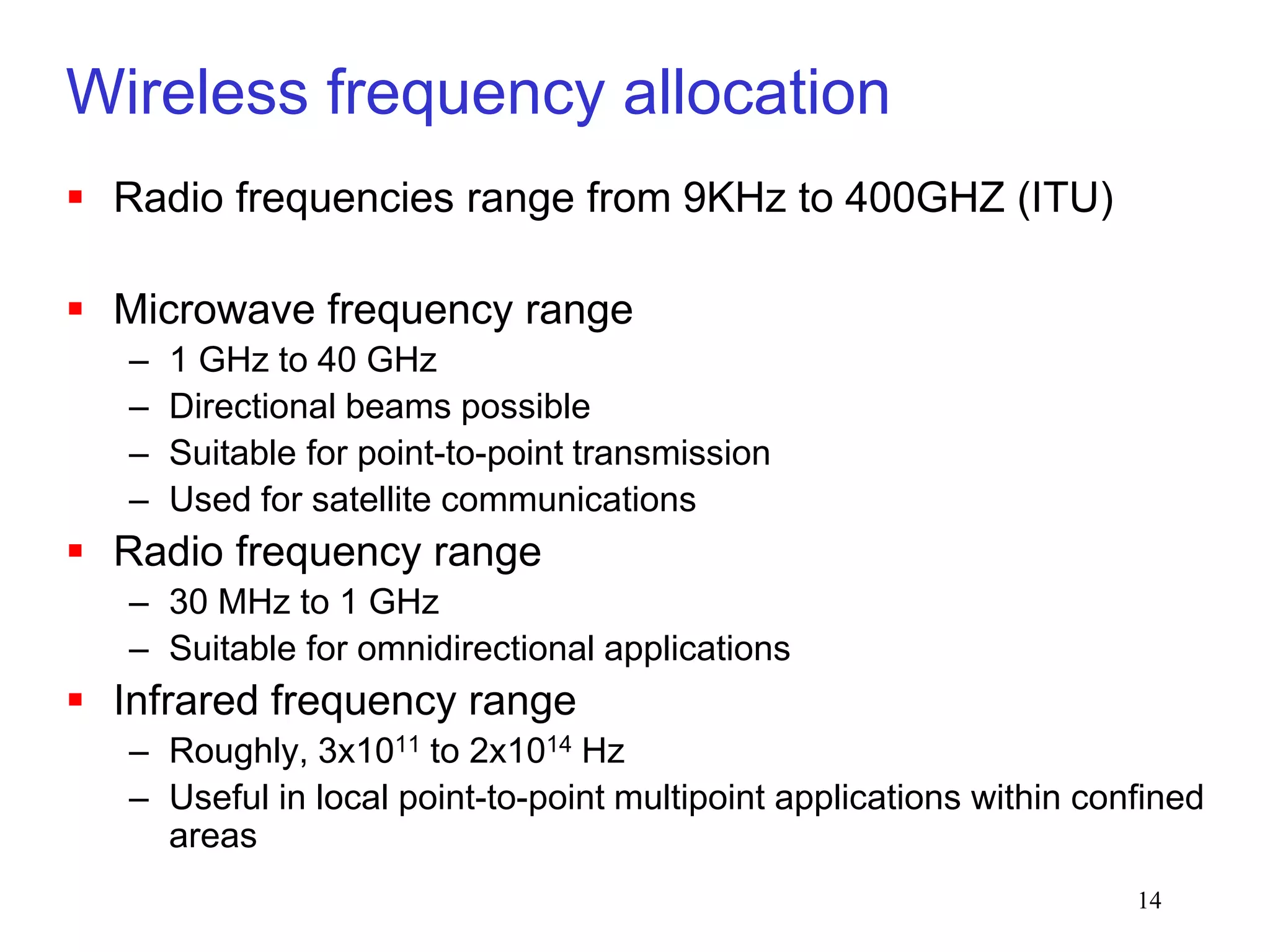
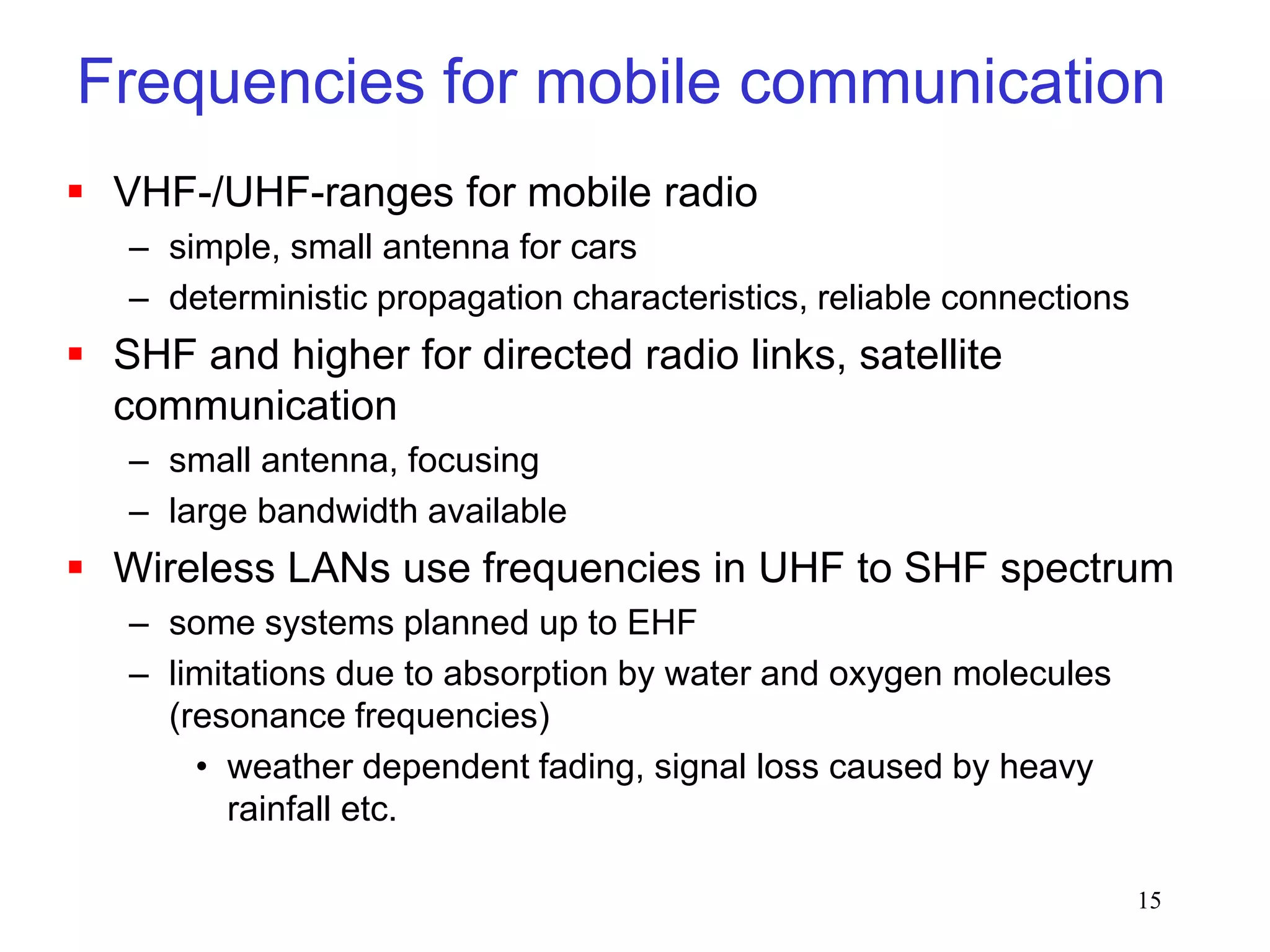
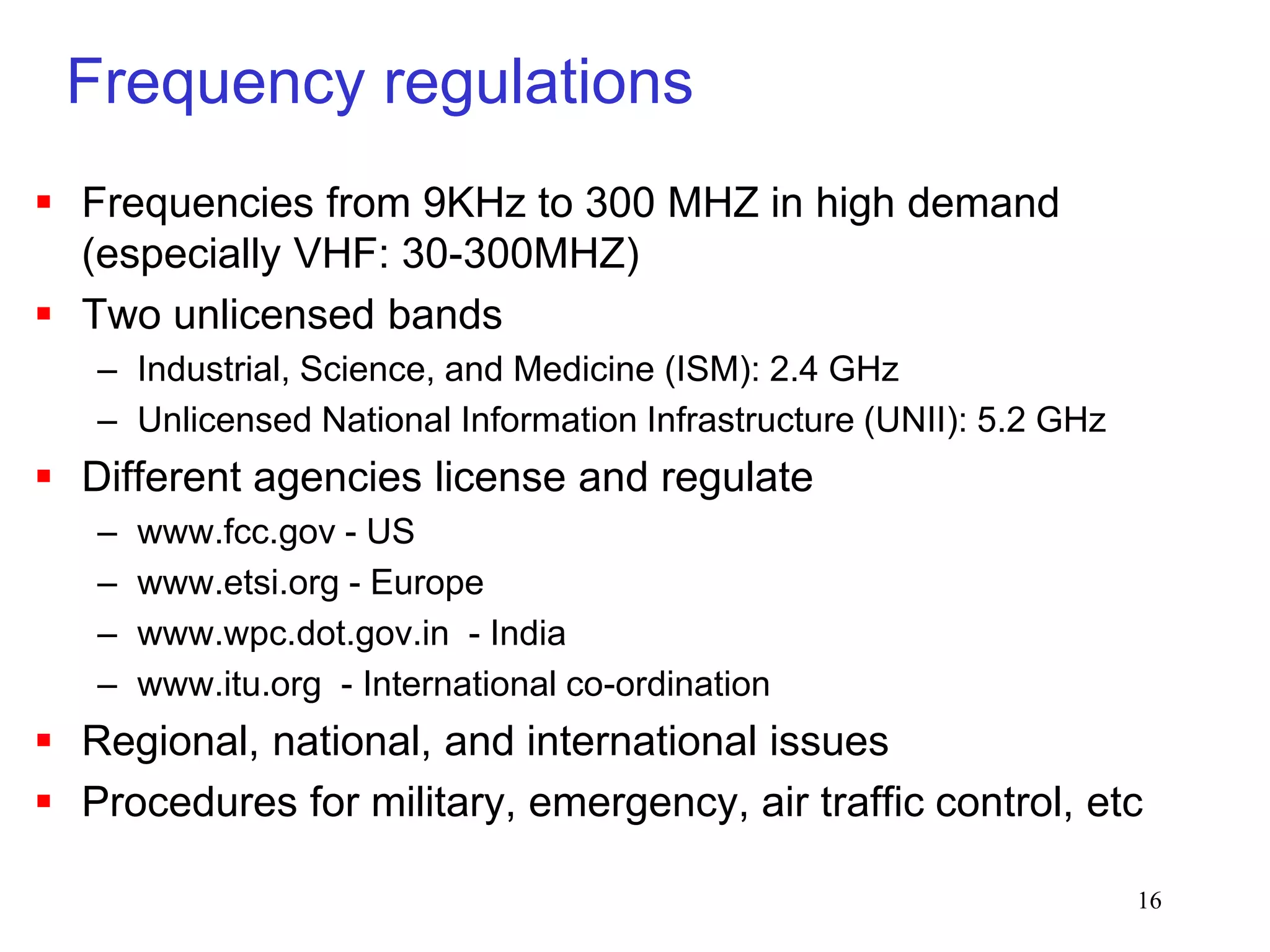
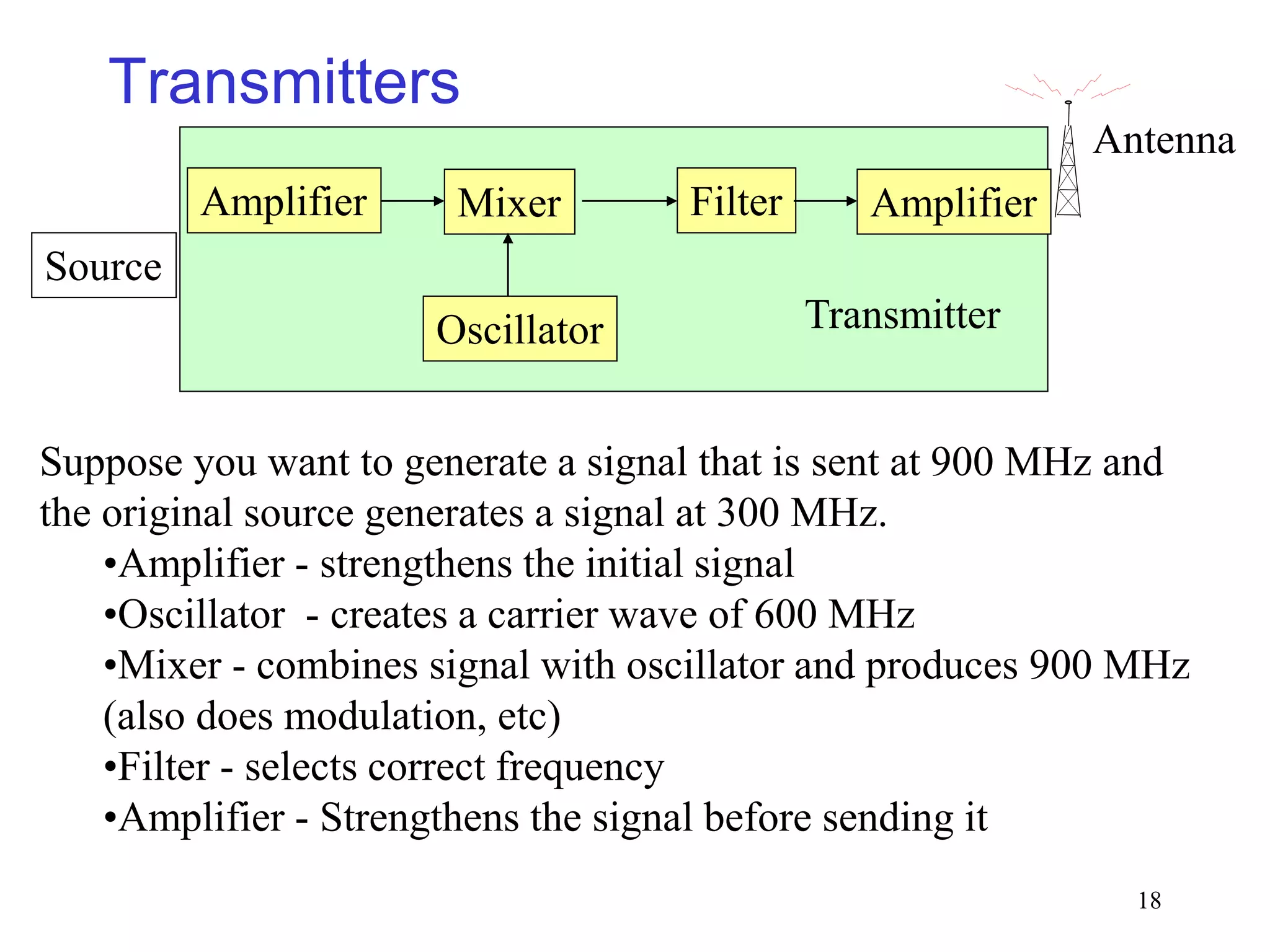
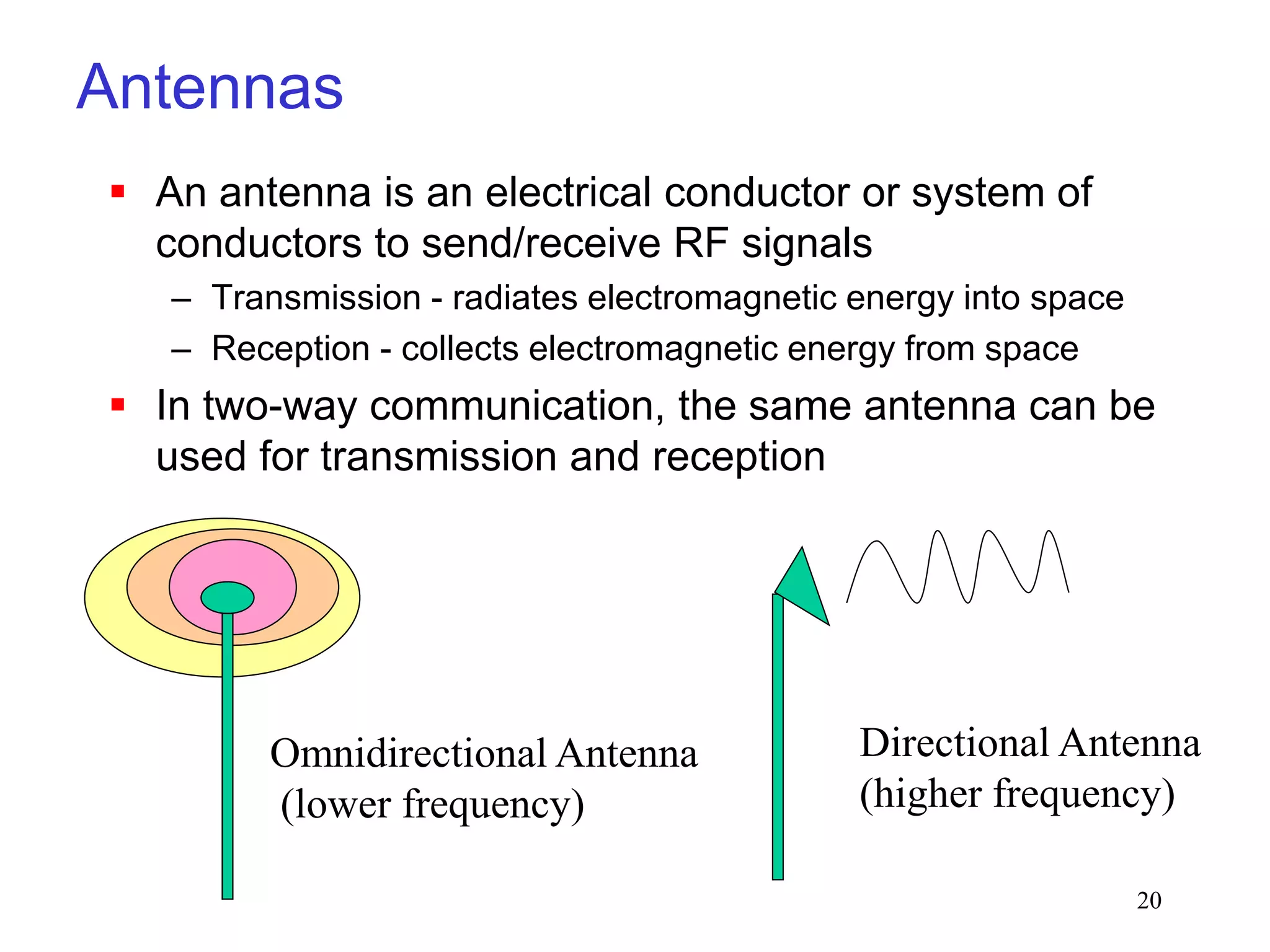
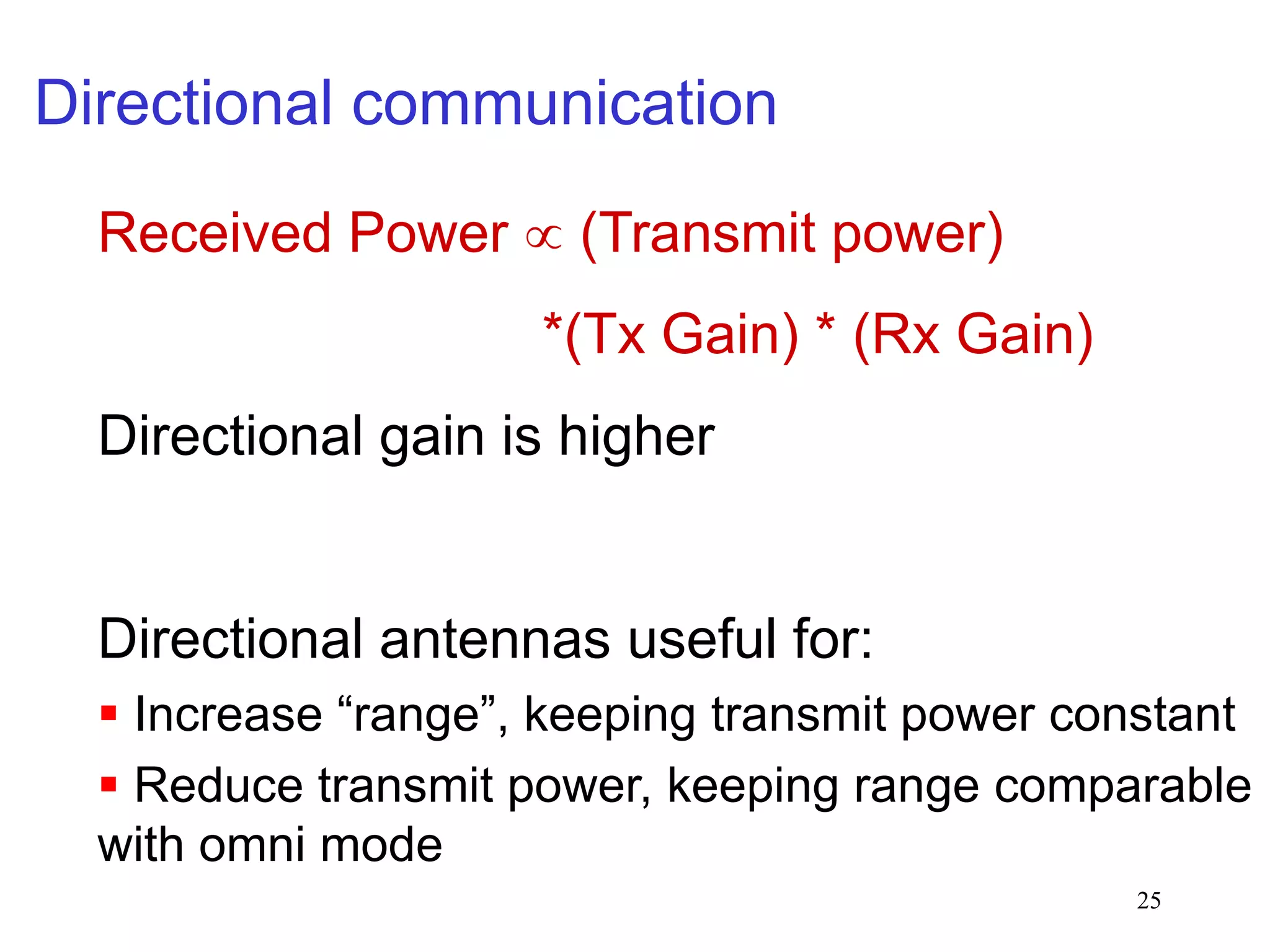
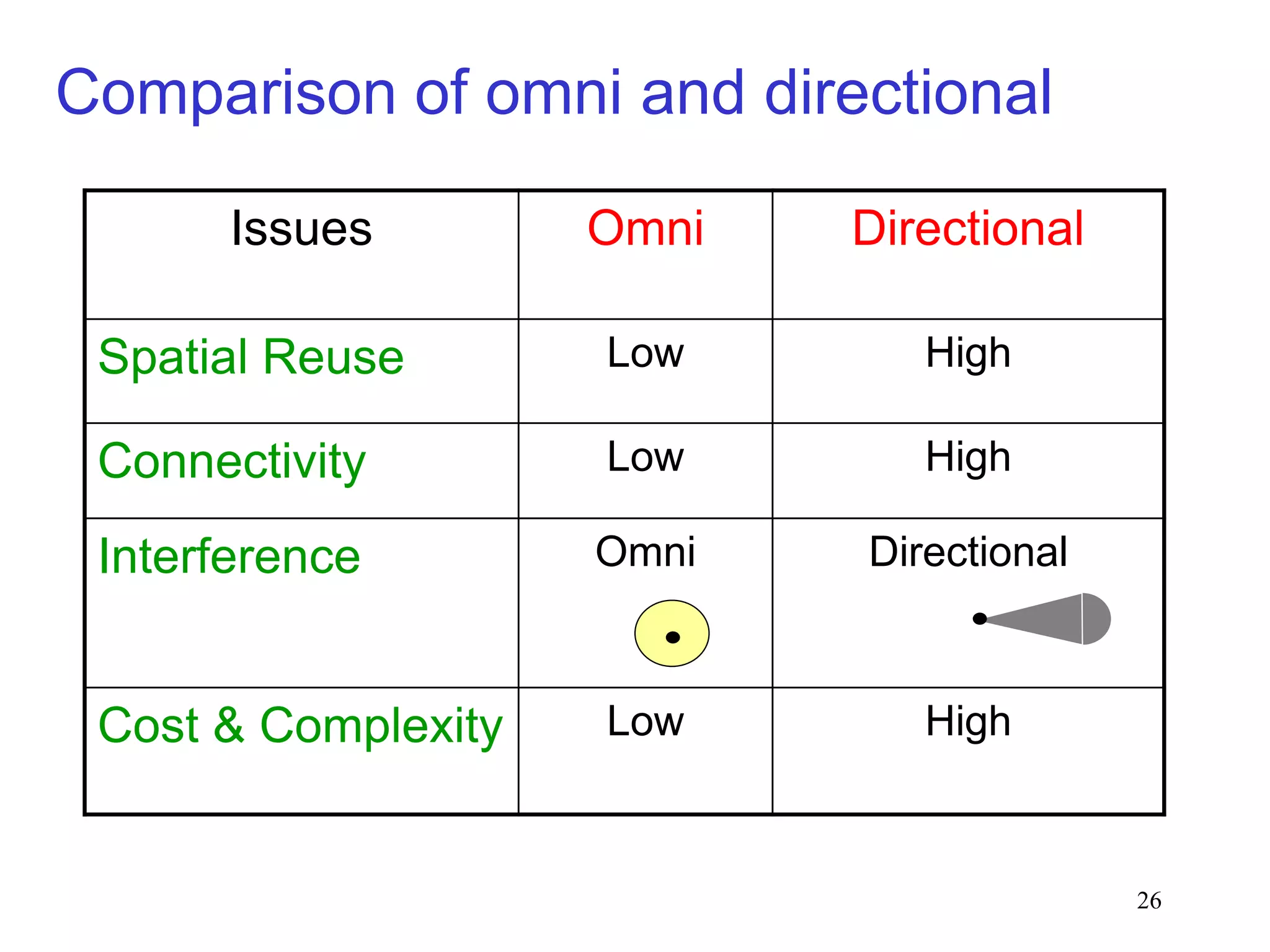
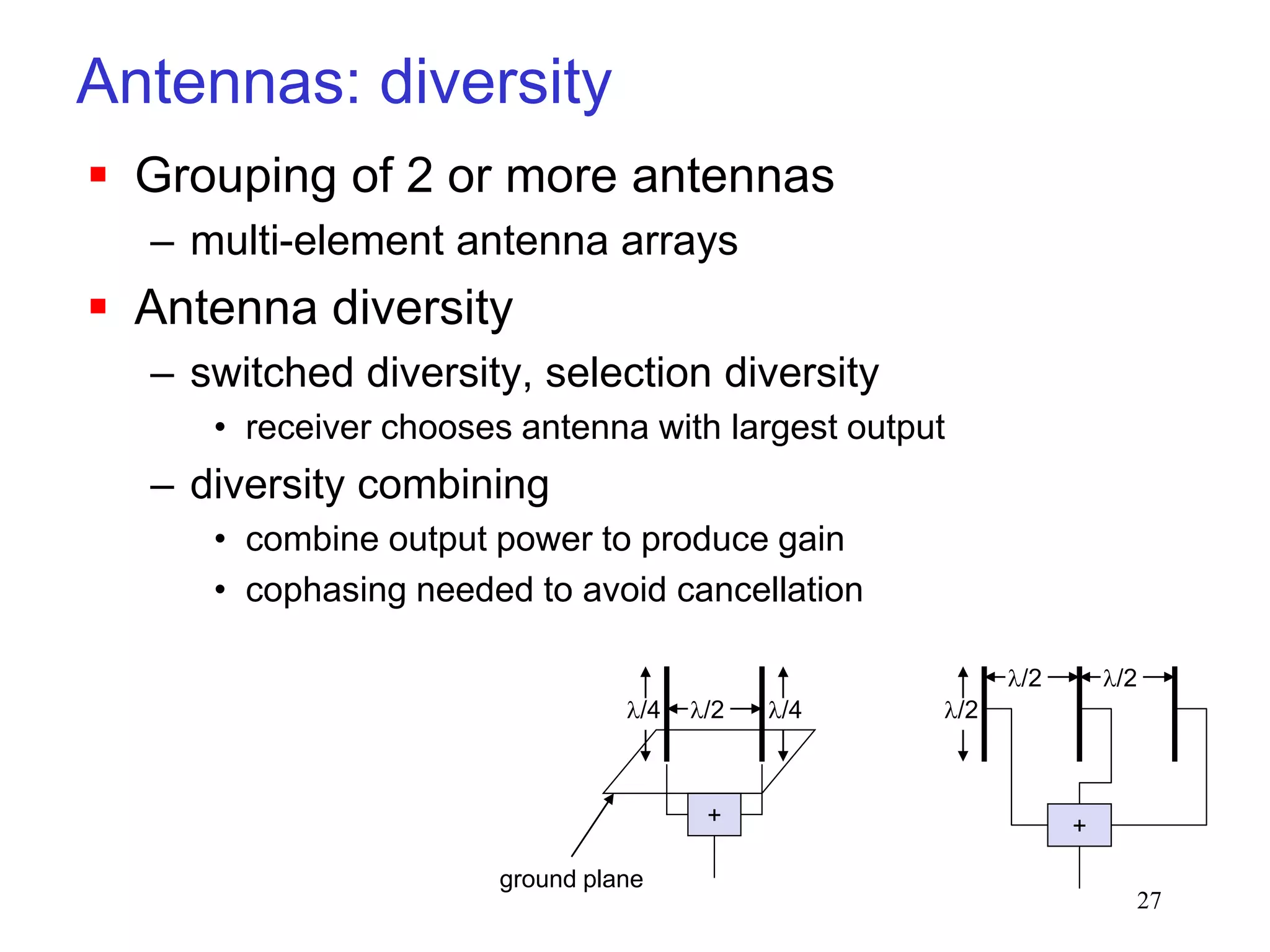
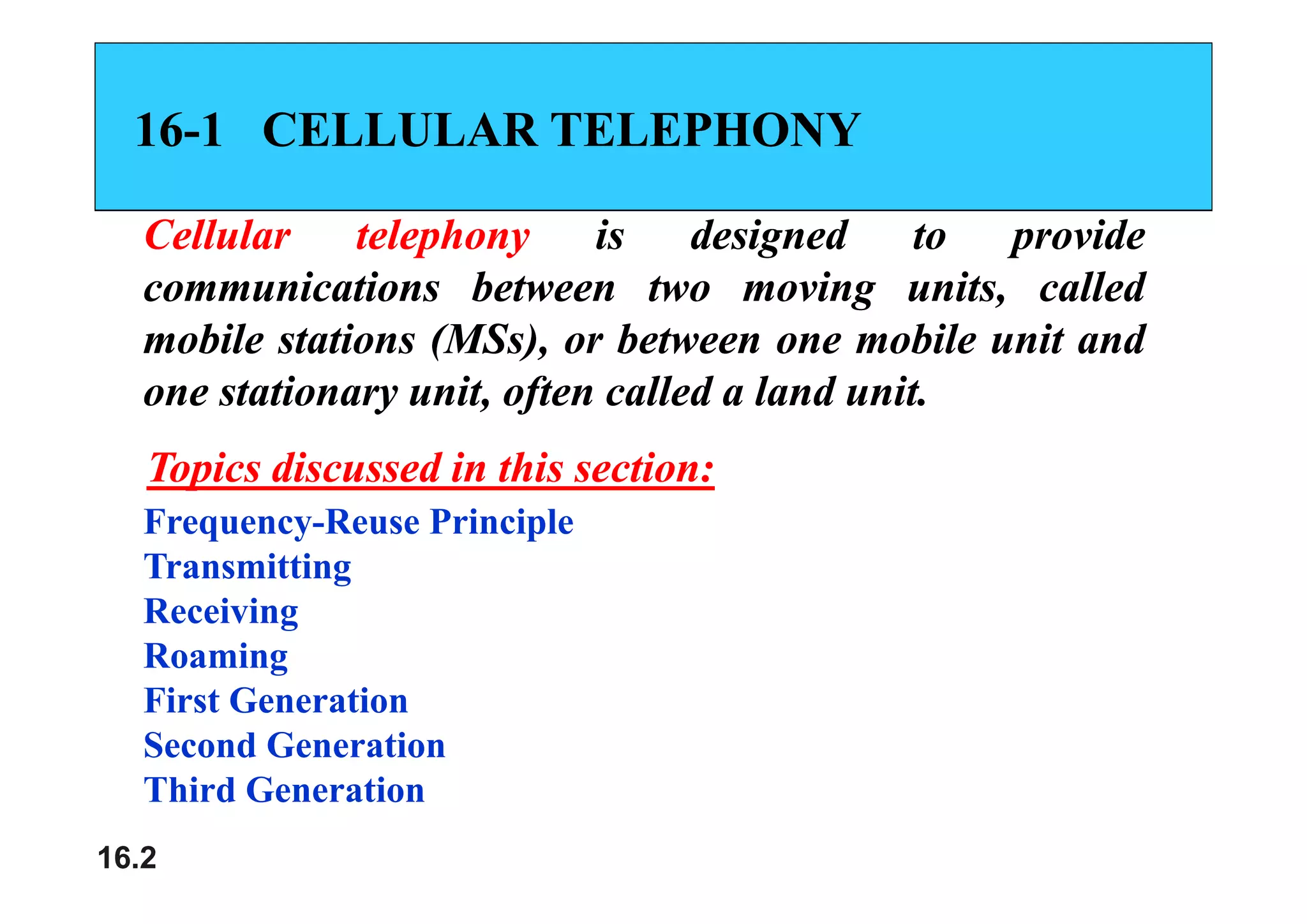
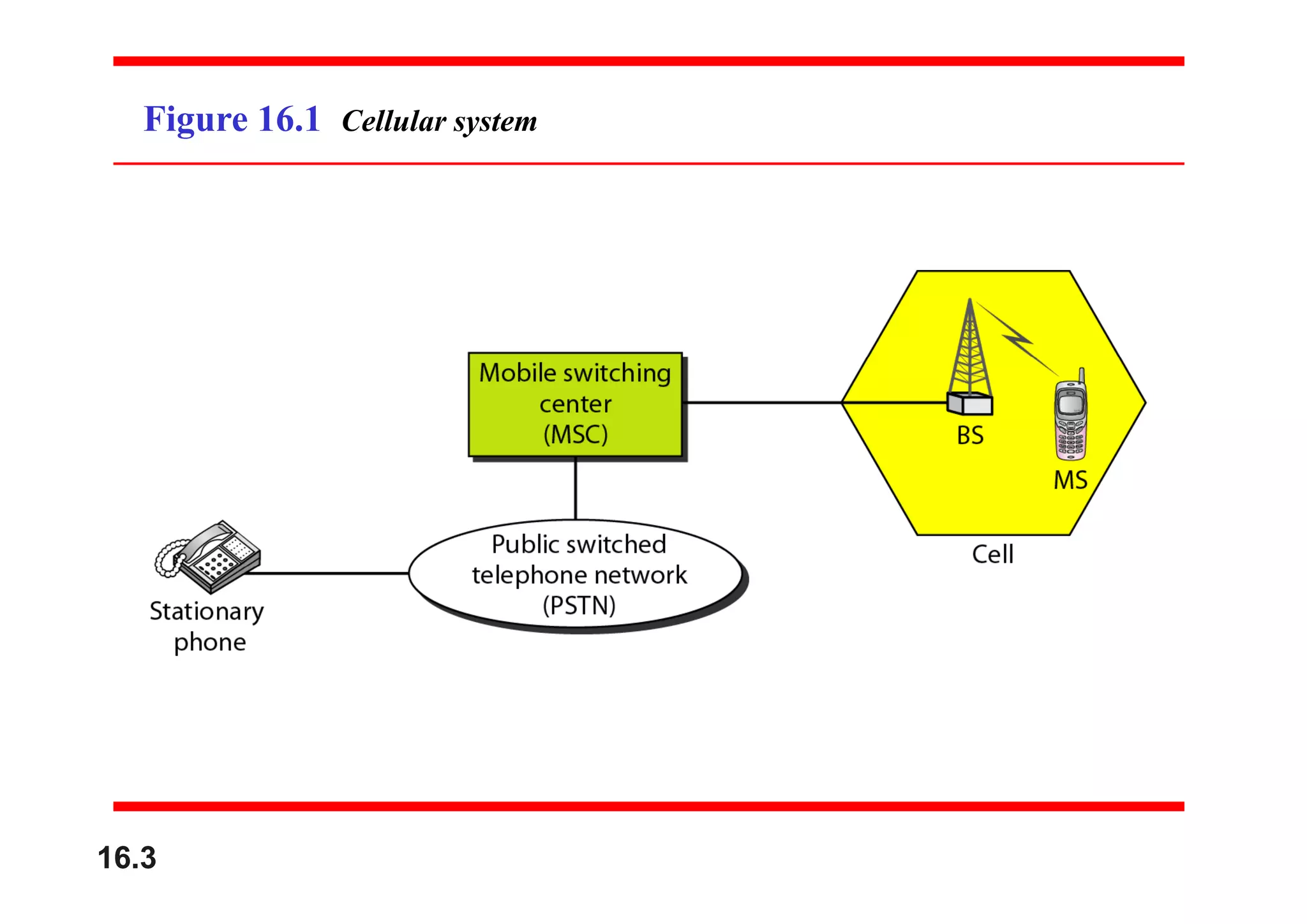
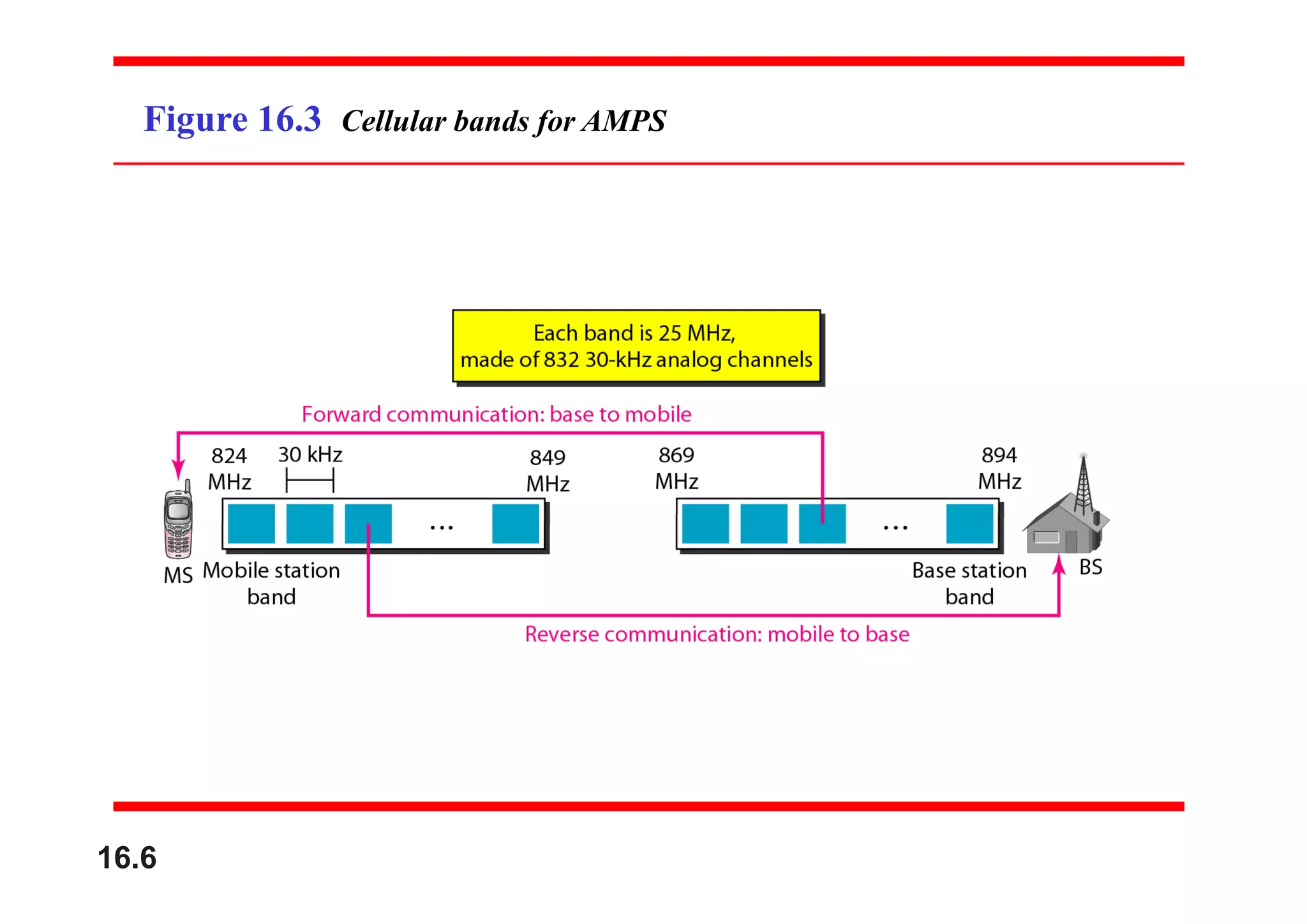
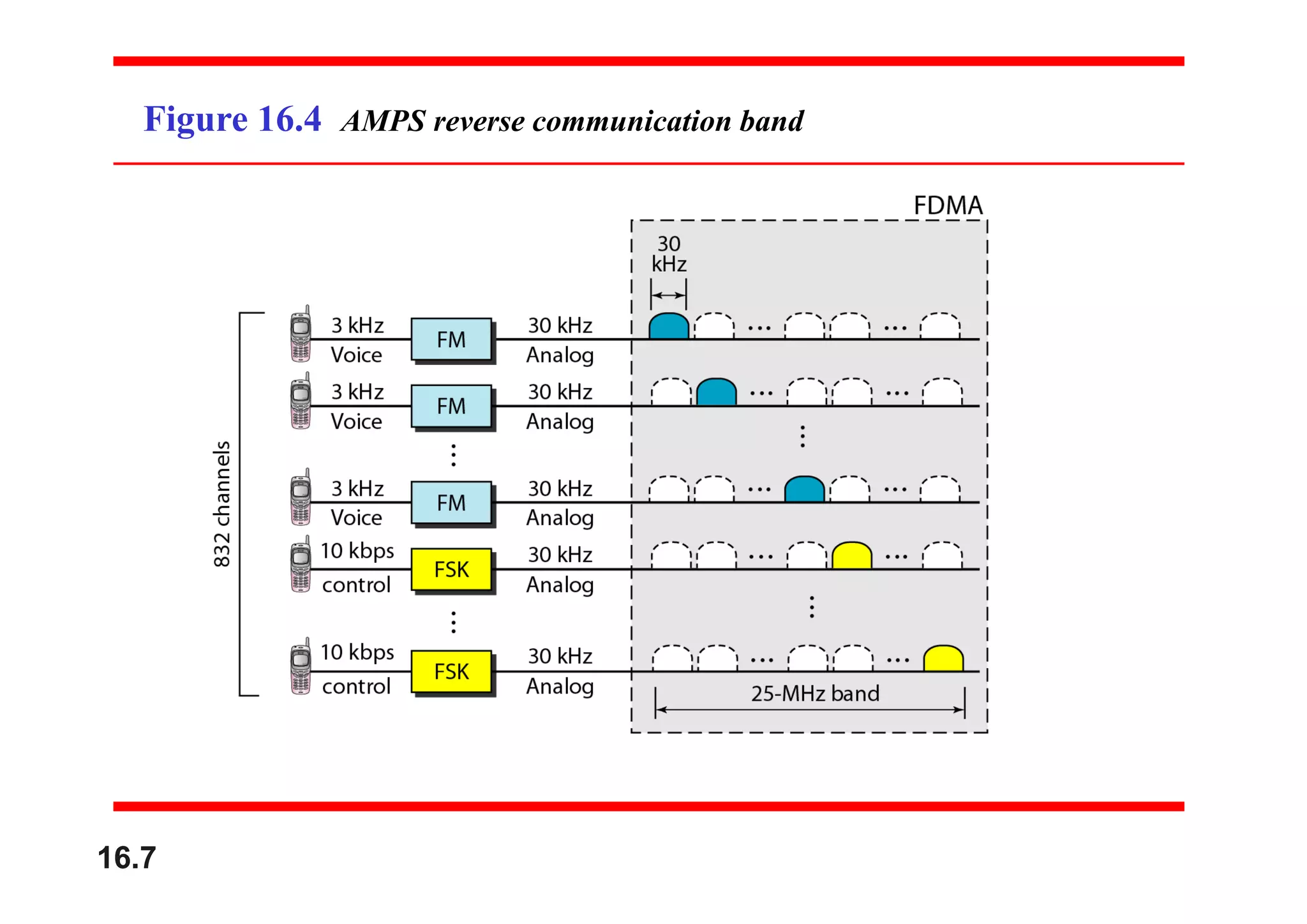
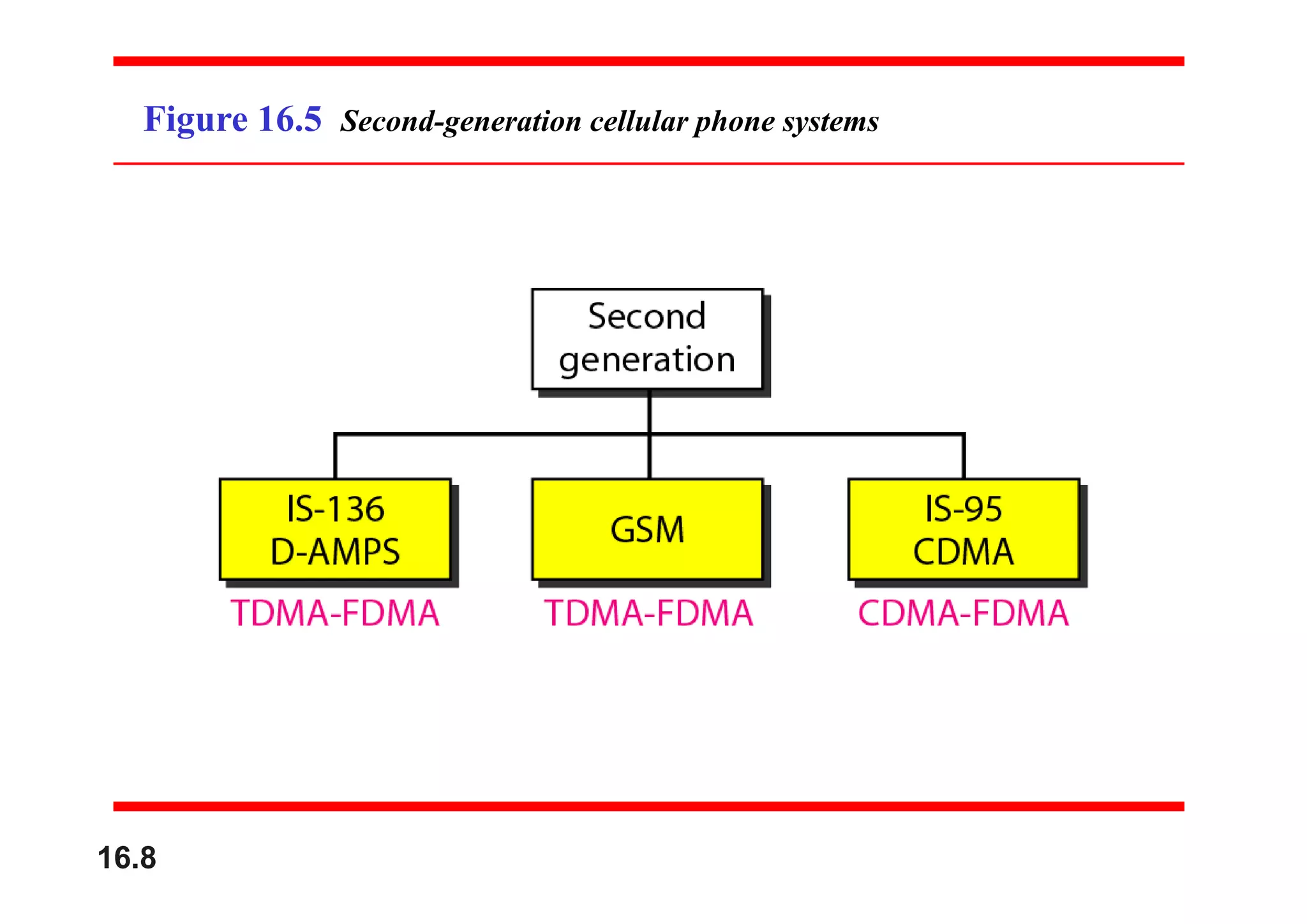
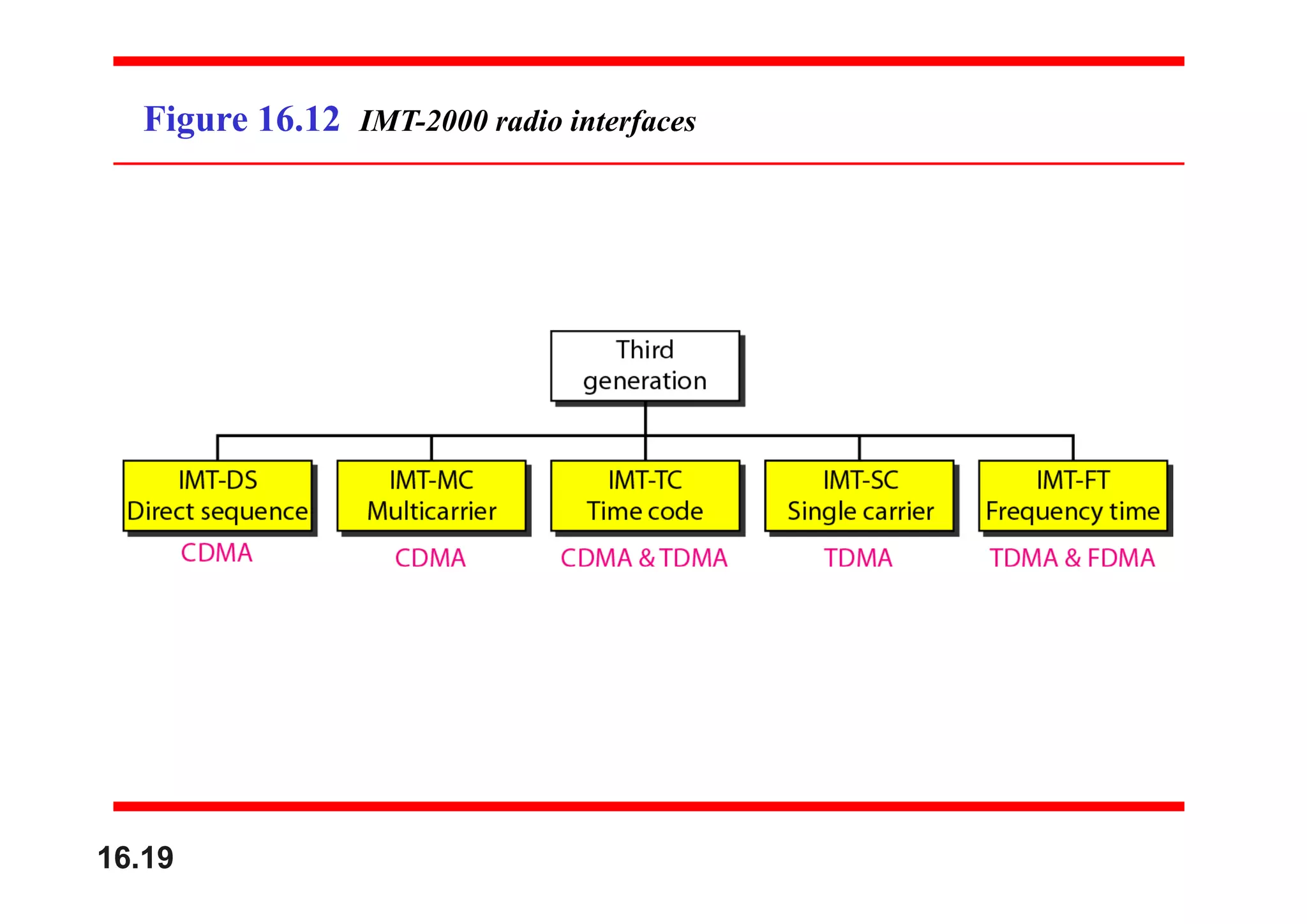
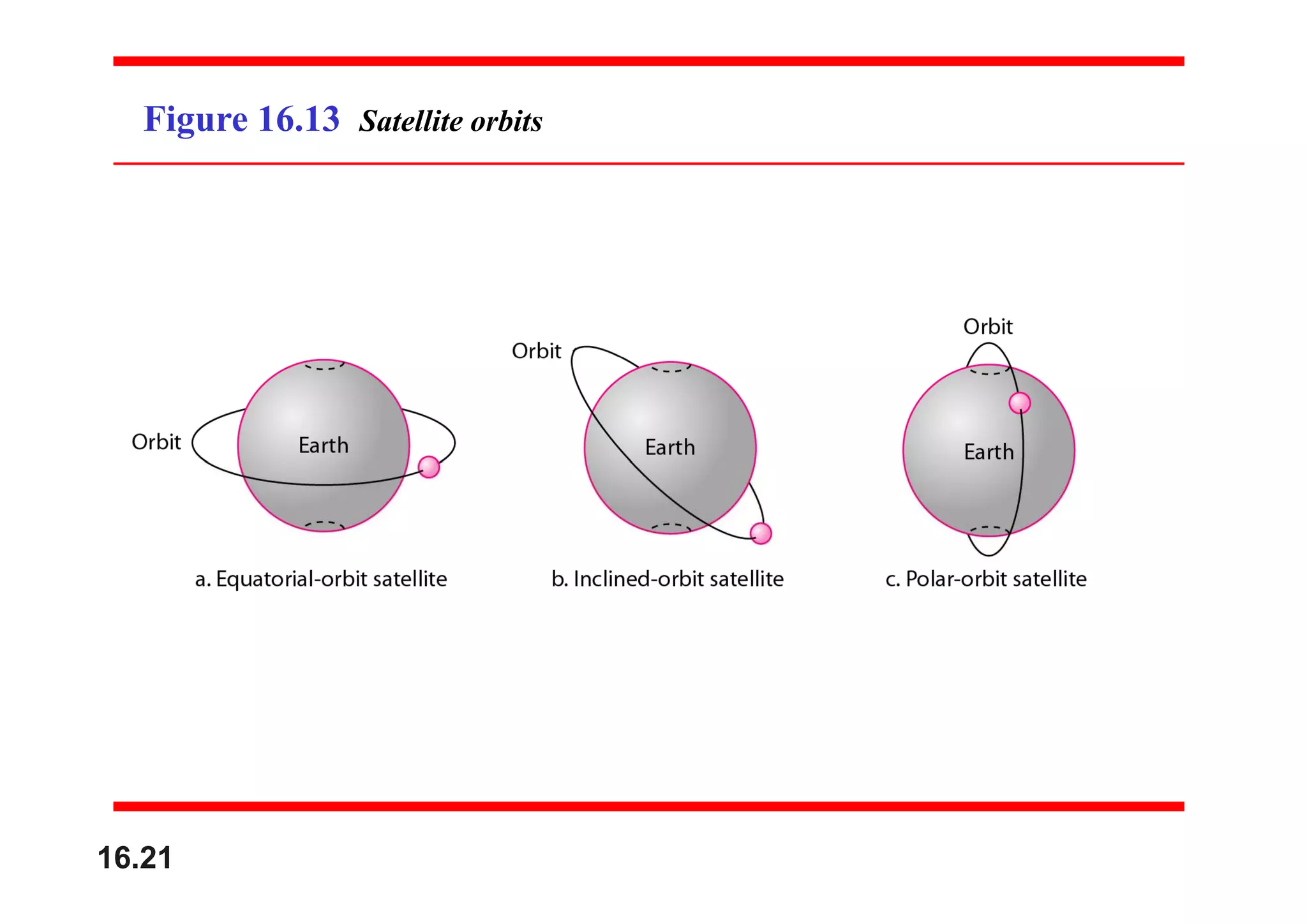
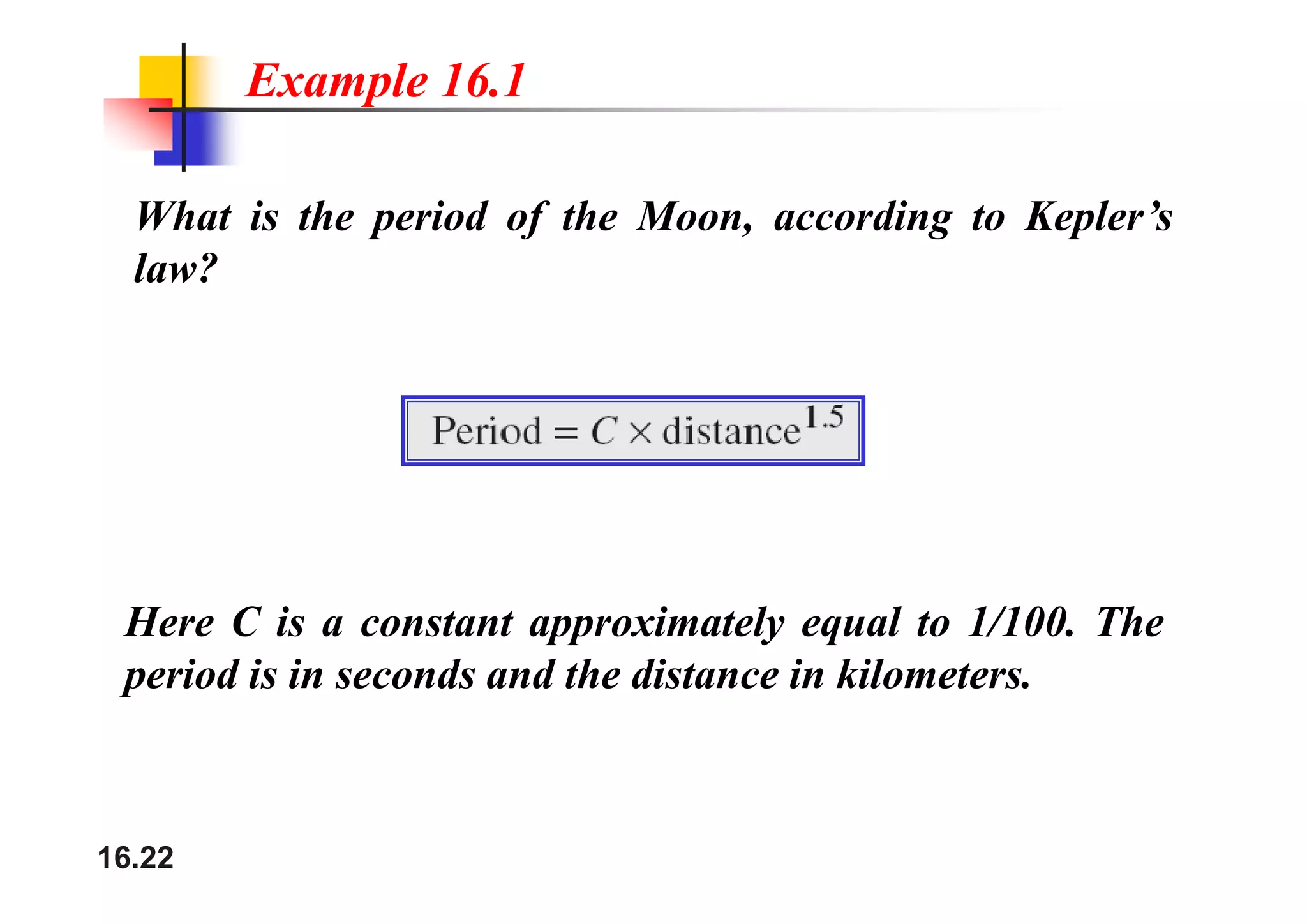
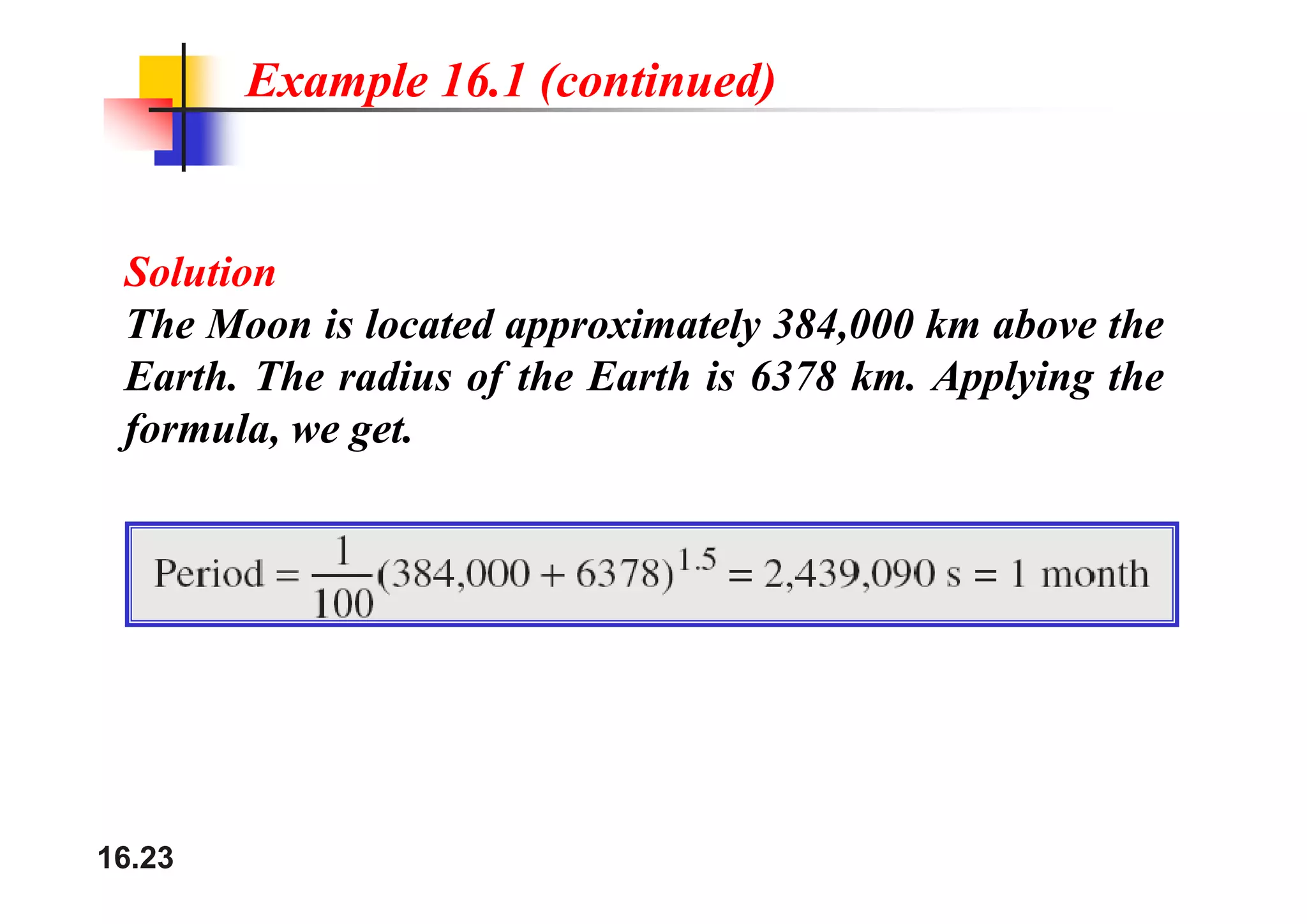
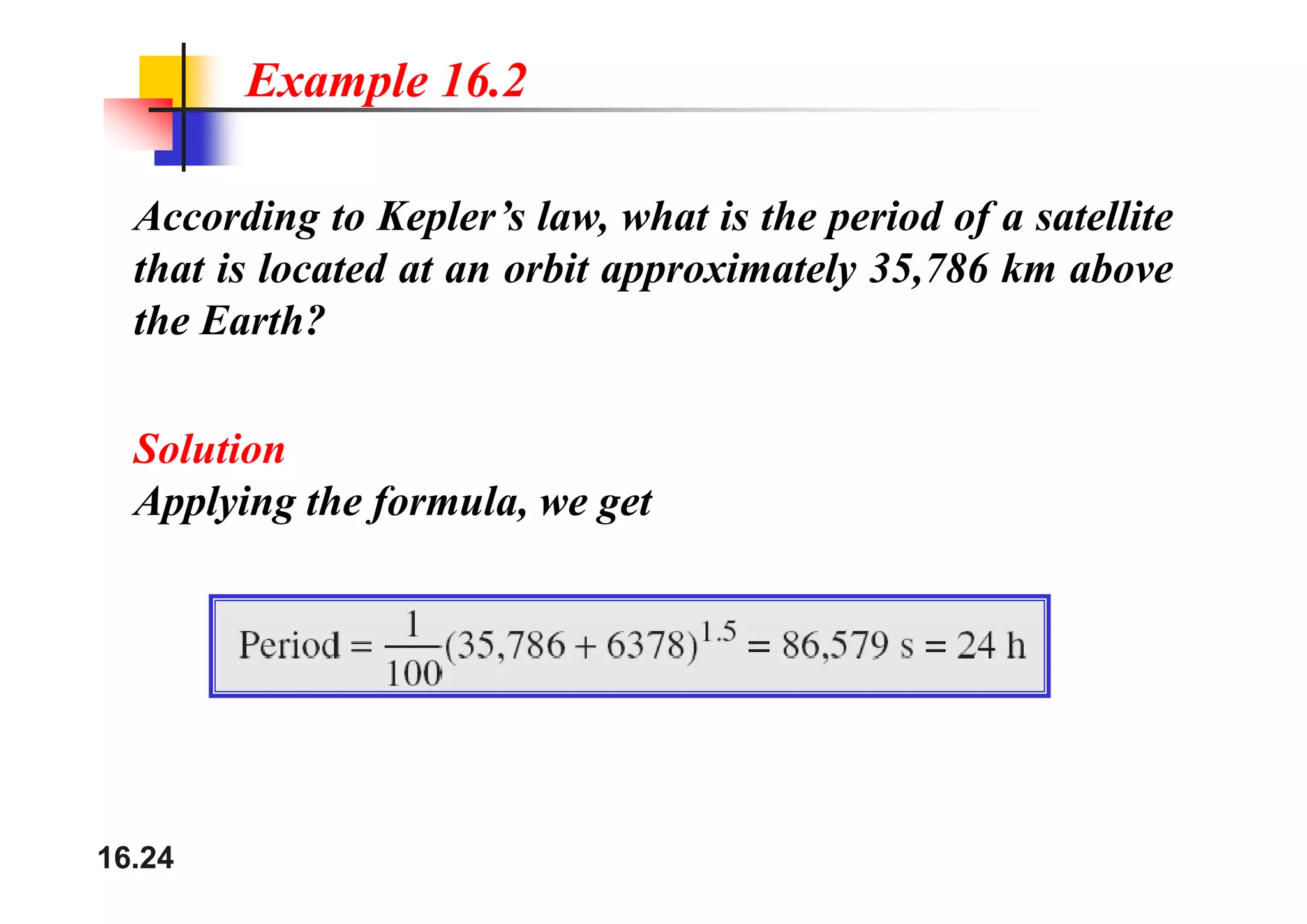
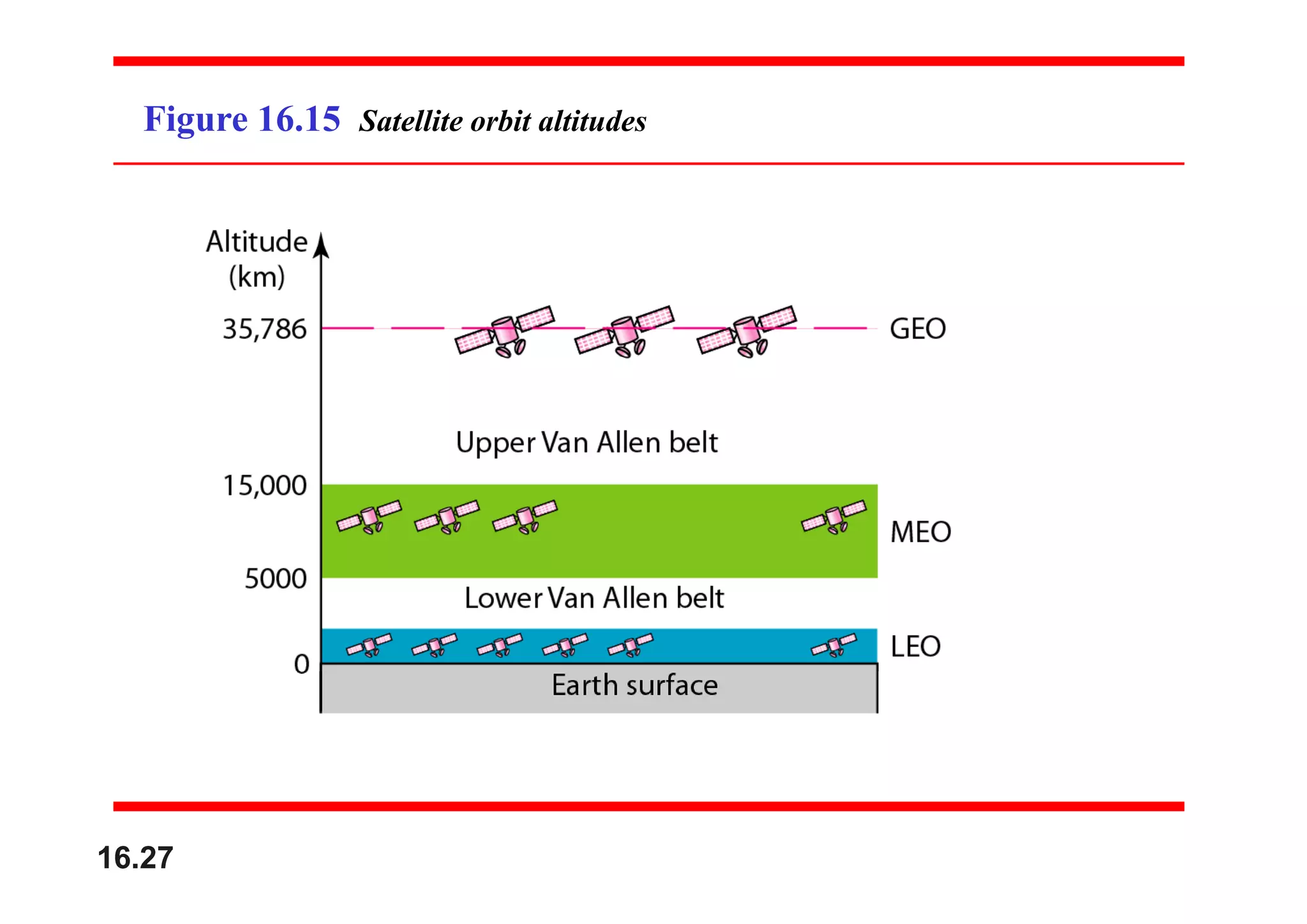
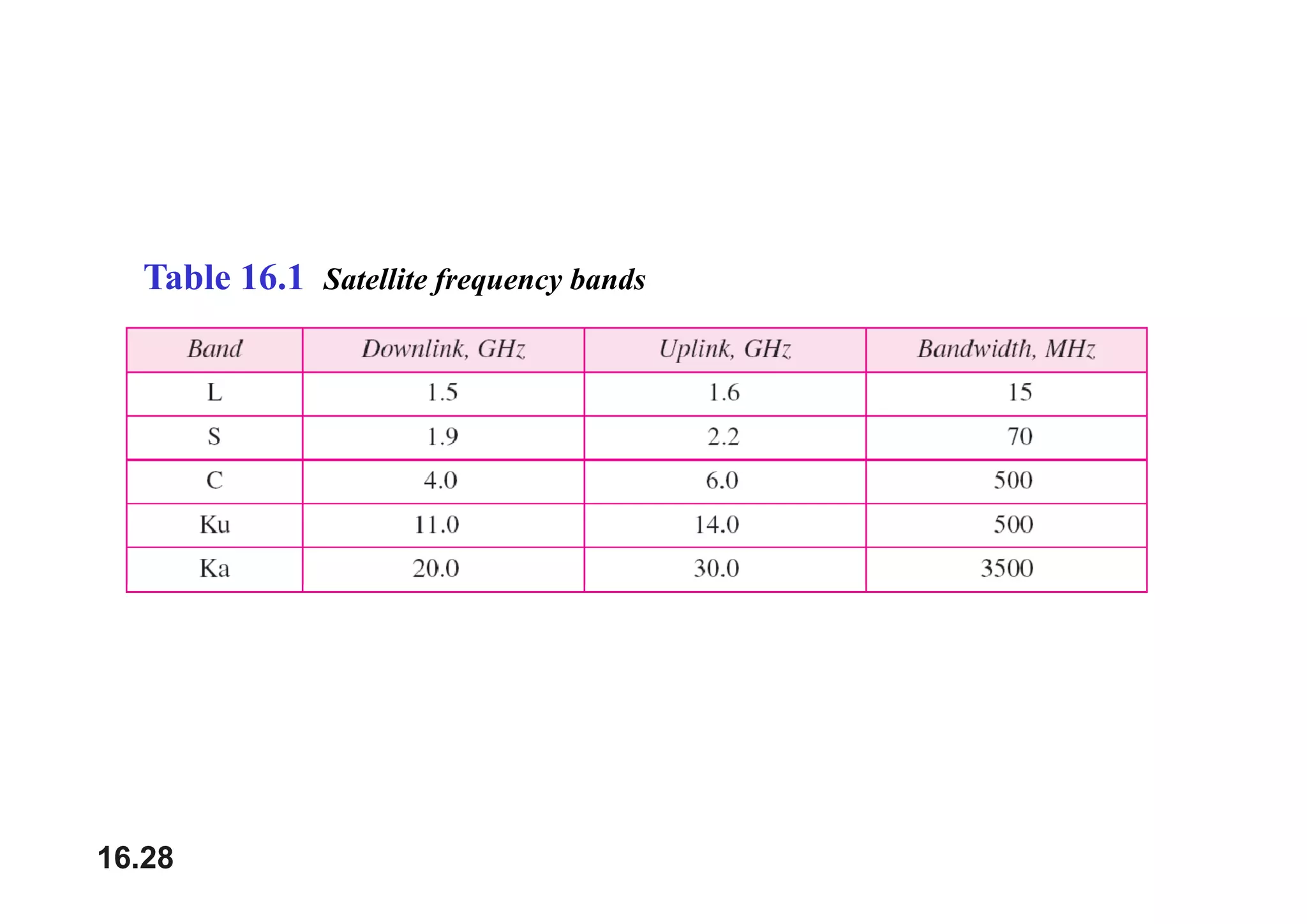
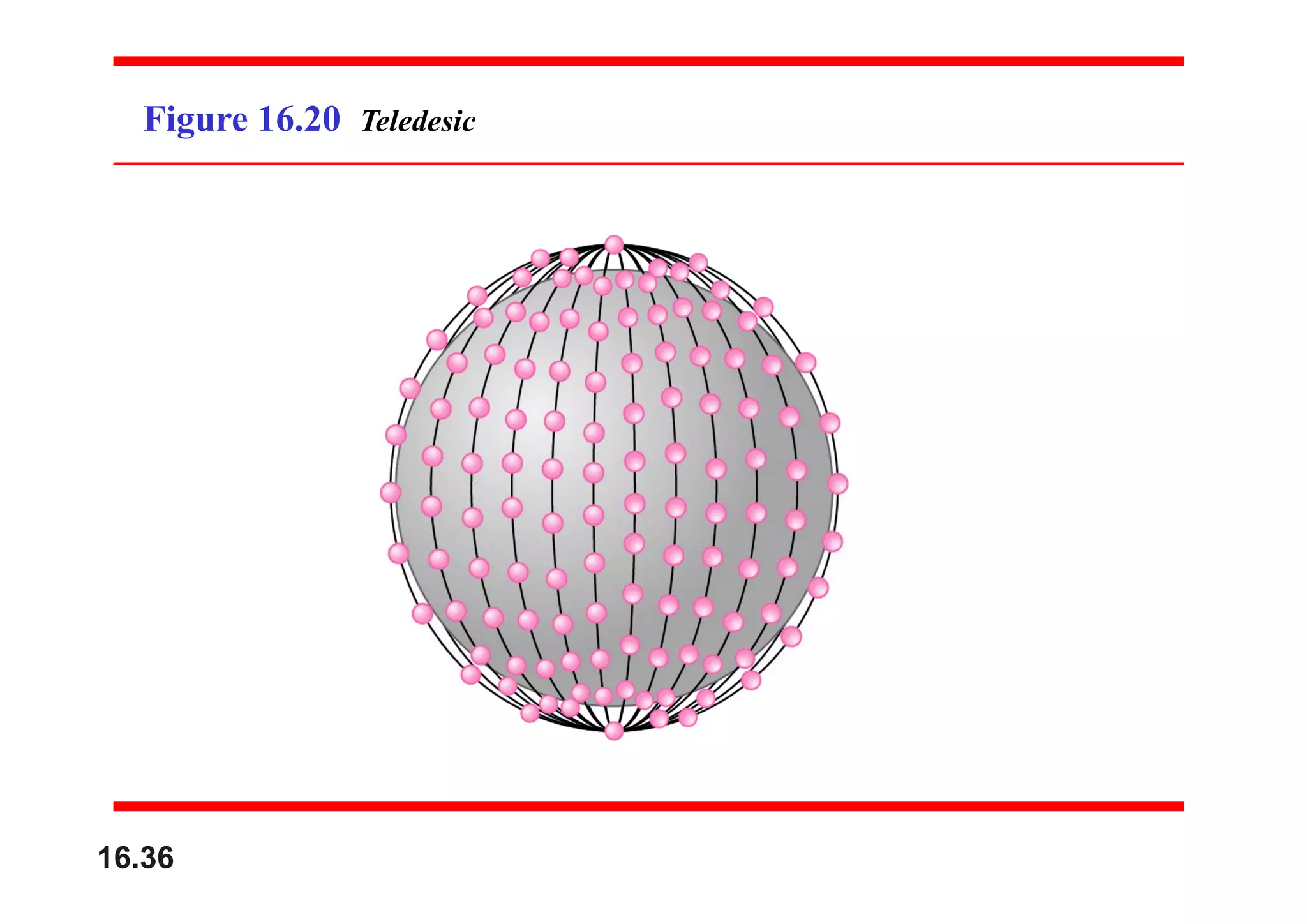
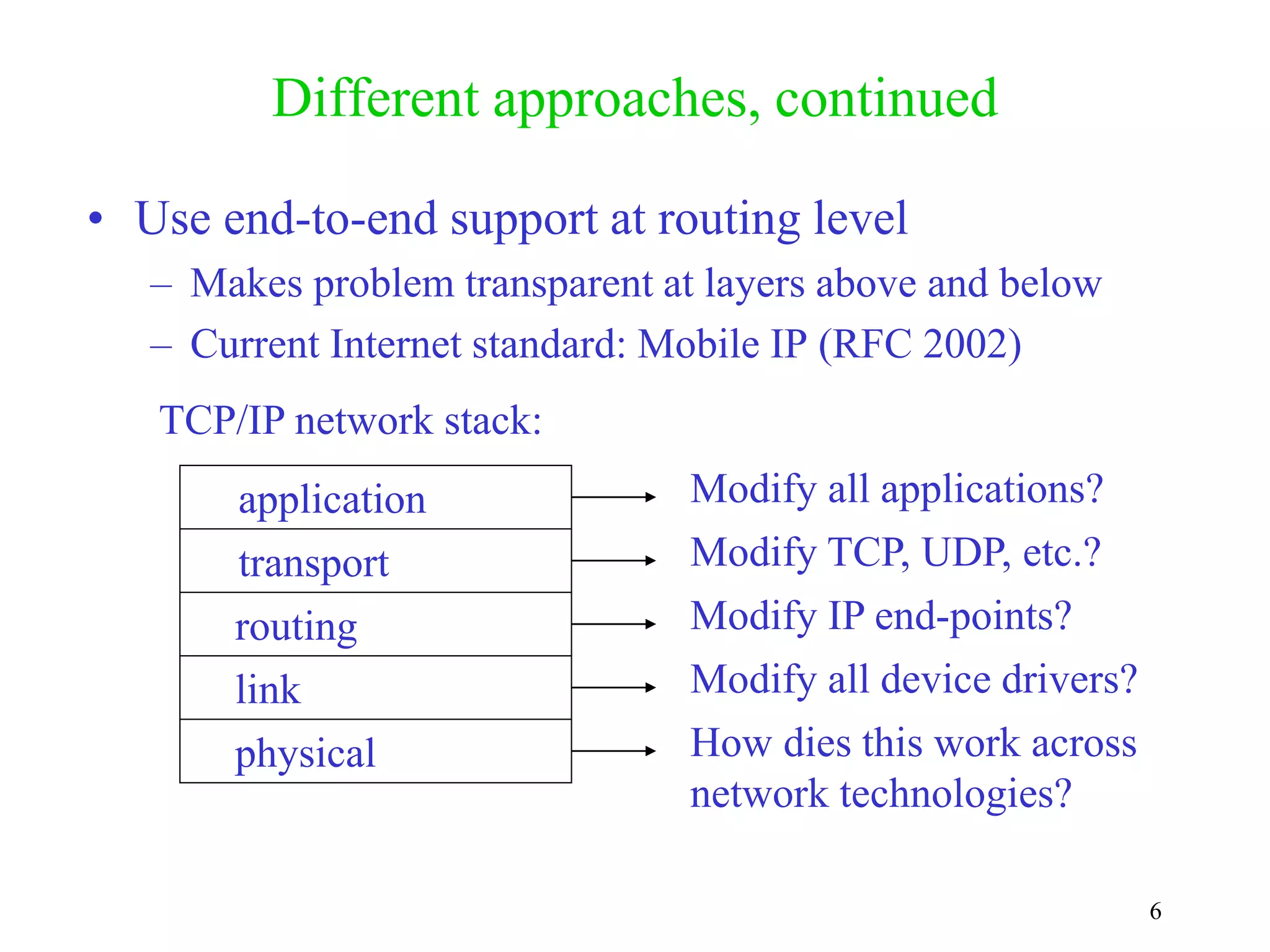
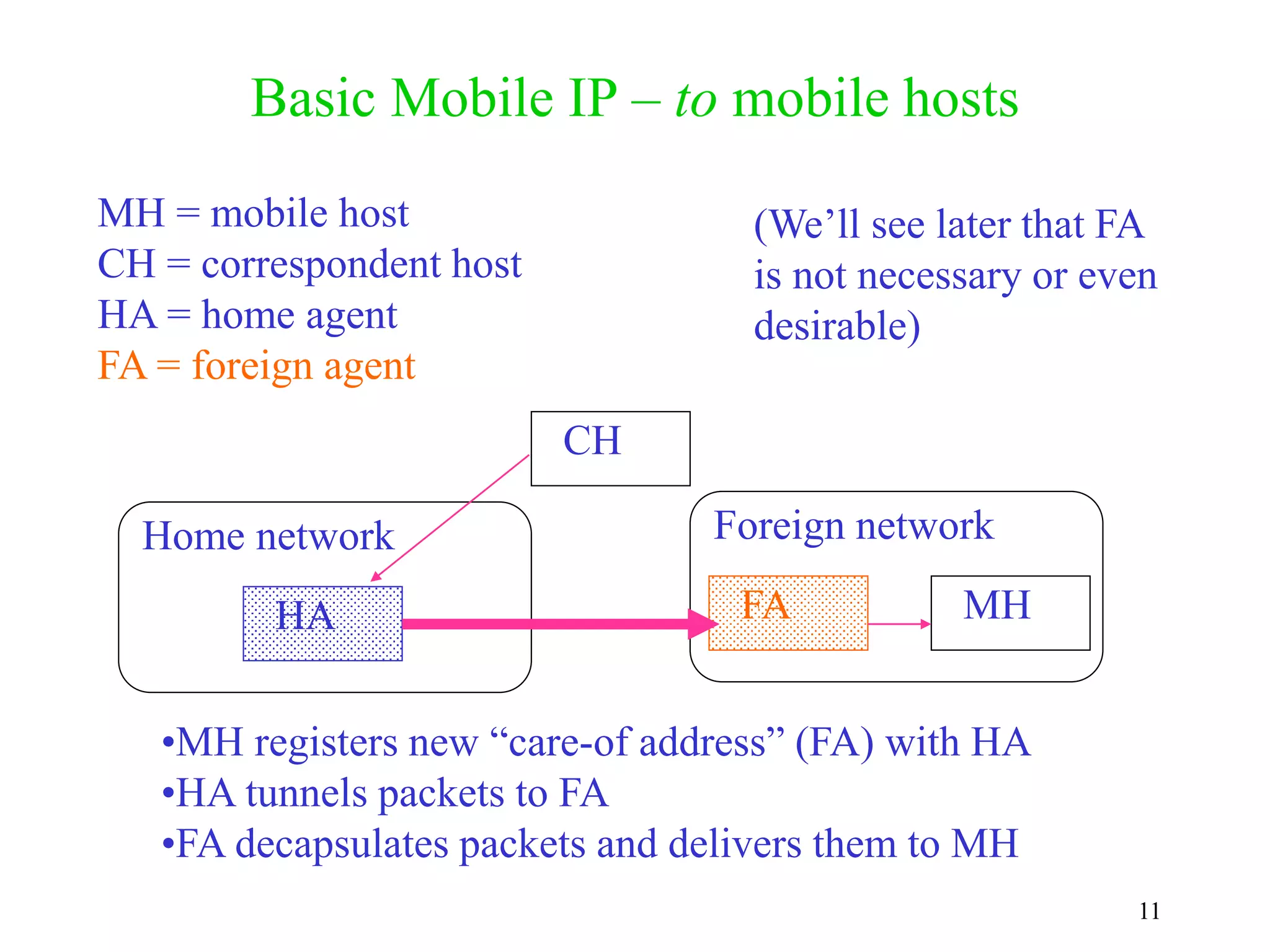
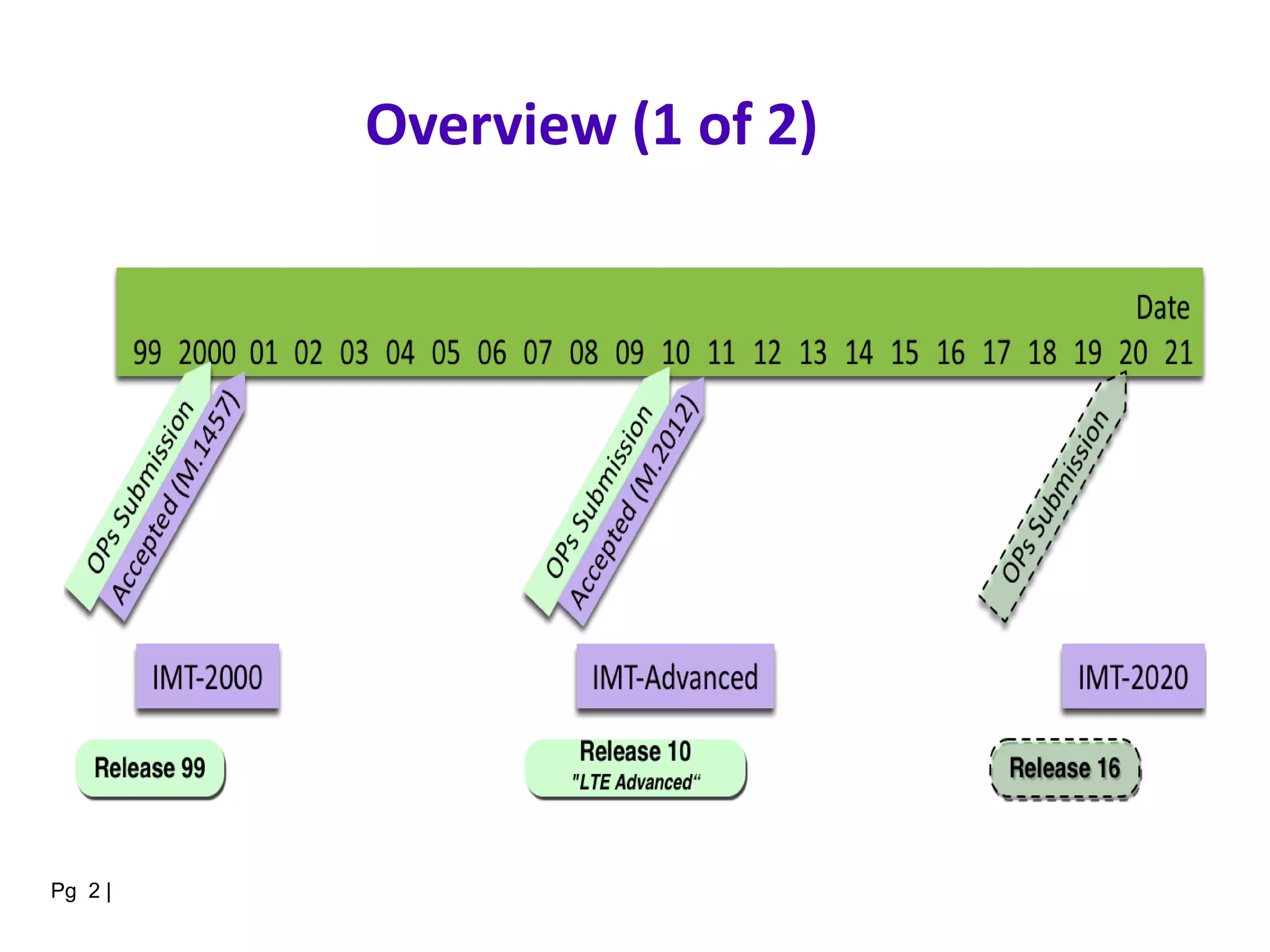
The document discusses various topics in computer communication networks, focusing specifically on wireless wide area networks (WANs) and LTE technology. It covers the characteristics, limitations, and integration of wireless networks, including mobile communications, cellular systems, satellite networking, and frequency regulations. Additionally, it addresses the challenges posed by mobility and describes the roles and concerns of network designers, users, and providers.
![IMT-2000 Submission Plan [of
Mar 2016]
Pg 3 |](https://image.slidesharecdn.com/u4-210914064106/75/20CS2007-Computer-Communication-Networks-107-2048.jpg)