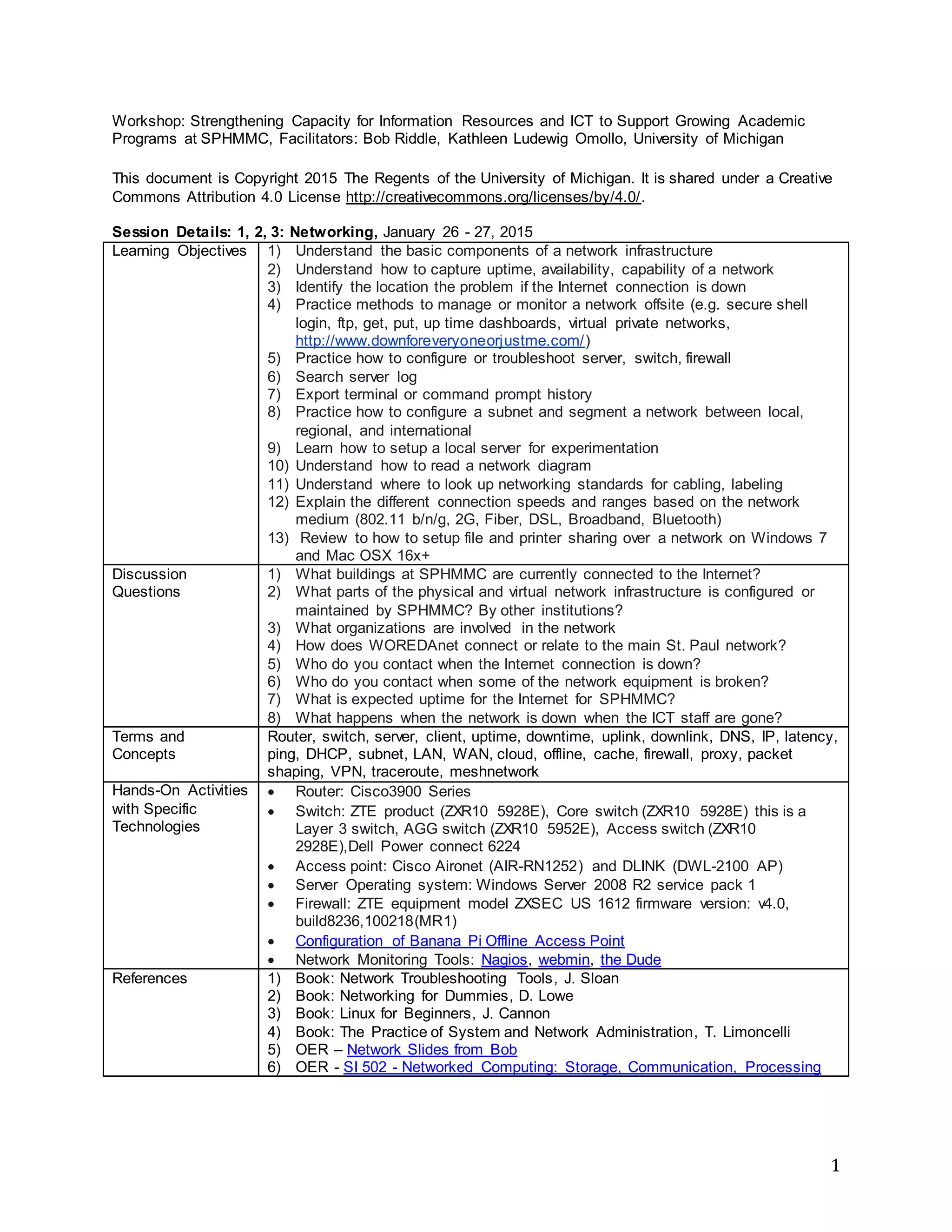
The document outlines a workshop aimed at strengthening information resources and ICT capacity to support academic programs at SPHMMC, including learning objectives related to network infrastructure, management, and troubleshooting. It details specific technologies and hands-on activities related to routers, switches, and monitoring tools, as well as discussion questions and best practices for network management. Additionally, it references several resources for further learning about networking concepts and technologies.