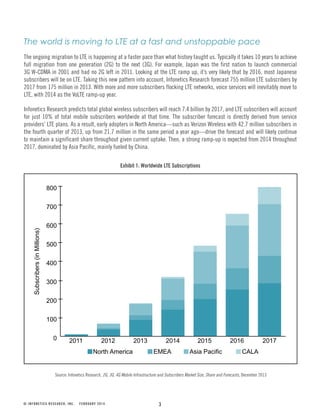
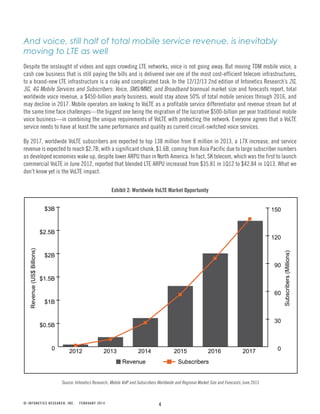
The Infonetics Research white paper discusses the urgent need for securing LTE networks as they rapidly evolve, noting that the transition from traditional mobile networks increases vulnerability to cyber threats. It emphasizes the importance of IPsec encryption and the deployment of security gateways to protect against both malicious and non-malicious attacks, particularly as voice services migrate to VoLTE. The paper forecasts a significant growth in LTE and VoLTE subscribers and revenue, while highlighting the complexity and necessity of robust security measures within these networks.