14 1 qo_s_digitization
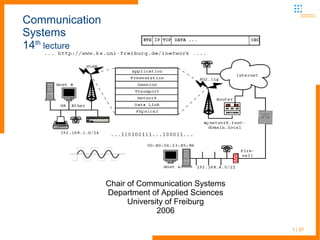
- 1. 1 | 57 Communication Systems 14th lecture Chair of Communication Systems Department of Applied Sciences University of Freiburg 2006
- 2. 2 | 57 Communication Systems Last lecture – UMTS, WCDMA, Wireless LAN ● Last session devoted to telephony networks and UMTS encoding – WCDMA on the air interface − WCDMA uses Code Division Multiplexing instead of Time Division Multiplexing and Frequency Division Multiplexing − Per participant a binary channalization code is used thus multiple signals on just one frequency ● Switched over then to other mobile technologies, especially Wireless LAN − Standardization of Wireless LAN technology started in1997 the IEEE approved 802.11 − The standard specifies the MAC and the physical layers for transmissions in the 2.4 GHz band
- 3. 3 | 57 Communication Systems Last lecture – Wireless LAN standards ● Later on the first really popular standard IEEE 802.11b was created, which works at additional signal rates of 5.5 and 11 Mbit/s. ● By the end of the 90s, the IEEE approved the specifications of 802.11a, which uses the 5 GHz band, allowing brutto signal rates of 6, 9, 12, 18, 24, 36, 48 up to 54 Mbit/s ● In 2003, the IEEE approved 802.11g as a further evolution of the 802.11 standard, providing the same performance as 802.11a, while working in the 2.4 GHz band. Compatible with 802.11b devices − most modern devices are equipped with g standard adaptors by now − wireless technology becomes increasingly popular by now
- 4. 4 | 57 Communication Systems This lecture – Wireless LAN and wireless technologies ● Thus we will find more mobile solutions for data communication than GSM, UMTS and WLAN ● There are several reasons for the evolution of new wireless standards − not all requirements could be met with GSM, UMTS or WLAN − the data rates of GSM are rather small compared to todays multimedia content and demands of modern networked applications, delay is an important issue for real time applications and communication − UMTS covers greater areas, but costs are rather high and bandwidth is medium compared to WLAN technology − on the other side GSM and UMTS offer a well established framework for user administration, accounting and billing on a really world wide scale
- 5. 5 | 57 Communication Systems This lecture – Wireless LAN and wireless technologies ● WLANs of the most widely used b and g (a/h) standards on the other side offer rather high bandwidth and short delay, but often − suboptimal regarding power consumption − layer 2 security − every-where access − user-authentication − bandwidth compared to classical Ethernet infrastructure ● Therefore we have additional concepts tackling some of the issues mentioned above − Bluetooth for low-power, short-range, low-bandwidth communication
- 6. 6 | 57 Communication Systems This lecture – More on wireless technologies ● Bluetooth is widely established and accepted in small mobile devices like mobile phones, PDAs, headsets, ... to replace wiring ● UWB – Ultra Wide Band as an upcoming high bandwidth technology which should be able to share bandwidth with other users and is authorized to operate in the range of 3.1 upto 16GHz ● “Wireless DSL” - different wide area network technologies in the former band of old analogous mobile phone networks to cover rural areas and offer high speed Internet access in sparsely populated areas ● WiMaX as a new wireless standard for MANs ● WiMaX and Bluetooth are covered in this lecture
- 7. 7 | 57 Communication Systems This lecture – Network fusion ● UWB is a rather new technology and not many products are available by now, but you will find some articles on it in the net ● In the second part of lecture we will switch over again and talk on fusion of telephony and IP networks
- 8. 8 | 57 Communication Systems WiMAX - Worldwide Interoperability for Microwave Access ● Broadband Wireless MAN Standard ● Defines wireless service that provide a communications path between a subscriber site and a core network such as the public telephone network and the Internet. ● "a standards-based technology enabling the delivery of last mile wireless broadband access as an alternative to cable and DSL." ● Standards: − IEEE Std 802.16-2004: addresses fixed and portable systems. − Amendment 802.16e: Adds mobility components to the standard, called “Mobile WiMAX”. ● WiMAX Forum coordinates interoperability testing -- “WiMAX Forum Certified”.
- 9. 9 | 57 Communication Systems WiMAX- characteristics ● Frequency ranges 10-66 GHz and 2-11 GHz. ● Broad bandwidth: Up to 134 Mbit/s in 28 MHz channel (10-66 GHz air interface) ● Accommodate either TDD or FDD. ● Supports higher layer or transport protocols such as ATM, Ethernet or IP. ● MAC is designed for very high bit rates (up to 268 mbps each way), while delivering ATM compatible Quality of Service. ● Frame structure allows terminals to be dynamically assigned uplink and downlink burst profiles according to their link conditions. ● MAC uses variable length PDU and other concepts to increase efficiency. ● MAC uses a self-correcting bandwidth request/grant scheme that eliminates the overhead and delay of acknowledgements, while simultaneously allowing better QoS handling. ● High security: supports AES and 3DES. ● IEEE 802.16e allows full mobility at speeds up to 160 km/hr.
- 10. 10 | 57 Communication Systems WiMAX - standards
- 11. 11 | 57 Communication Systems WiMAX – architecture and application
- 12. 12 | 57 Communication Systems WiMAX – architecture and application ● WiMAX system consists of two parts ● WiMAX Base station (tower): can cover up to 10 km radius ● WiMAX Subscriber station (receiver): sits in your laptop or computer. ● Several base stations are connected with one another by high-speed backhaul microwave links, allowing for roaming by a WiMAX subscriber from one base station to another base station area. ● WiMAX has two main topologies ● Point to Point for backhaul ● Point to Multi-Point Base station for Subscriber station ● Typical areas of application of WiMAX ● Residential and SOHO High Speed Internet Access. ● Small and Medium Business. ● WiFi Hot Spot Backhaul
- 13. 13 | 57 Communication Systems WiMAX – wireless services ● Line-of-sight − A fixed dish antenna points straight at the WiMAX tower from a rooftop or pole. − 11 GHz to 66 GHz frequency range − At higher frequencies - there is less interference and lots more bandwidth − The connection is stronger and more stable, so it is able to send a lot of data with fewer errors. ● Non-line-of-sight − A small antenna on your computer connects to the WiMAX tower − 2 GHz to 11 GHz frequency range − At lower frequencies – longer wavelength transmissions are not as easily disrupted by physical obstructions – they are better able to diffract, or bend, around obstacles
- 14. 14 | 57 Communication Systems WiMAX – reference model
- 15. 15 | 57 Communication Systems WiMAX – reference model ● Service-Specific Convergence Sublayer (CS): − provides transformation or mapping of external network data, received through the CS service access point (SAP), into MAC SDUs received by the MAC Common Part Sublayer (CPS) through the MAC SAP. ● MAC Common Part Sublayer (MAC CPS): − provides the core MAC functionality of system access, bandwidth allocation, connection establishment, and connection maintenance. − receives data from the various CSs, through the MAC SAP, classified to particular MAC connections. − Data, PHY control, and statistics are transferred between the MAC CPS and the PHY via the PHY SAP. ● A seperate security sublayer provides authentication, secure key exchange, and encryption. ● Physical Layer (PHY) includes multiple specification, each appropriate to a particular frequency range and application.
- 16. 16 | 57 Communication Systems Comparison of WiMAX and Wi-Fi
- 17. 17 | 57 ● Bluetooth is a radio standard and communications protocol primarily designed for low power consumption, with a short range (power class dependent: 1 meter, 10 meters, 100 meters) based around low-cost transceiver microchips in each device ● Intended to replace the cable(s) connecting portable and/or fixed electronic devices ● Designed to operate in noisy frequency environments, the Bluetooth radio uses a fast acknowledgement and frequency hopping scheme to make the link robust ● Bluetooth radio modules operate in the unlicensed ISM band at 2.4GHz, use frequency hopping and change freq. every 42 times a millisecond, hop is synchronized by cell master Communication Systems Bluetooth technology - introduction
- 18. 18 | 57 ● Compared with other systems in the same frequency band, the Bluetooth radio hops faster and uses shorter packets ● Currently at version 1.2. ● Since March 2002, an IEEE standard, namely IEEE 802.15.1. ● Unlicensed 2.4GHz radio band, ISM (industrial, scientific,medical) band - available worldwide, also used by Microwave ovens, 802.11, HomeRF… ● Gross data rate of 1 Mbit/s ● Basic 10m range extended to 100m with amplifiers Communication Systems Bluetooth - characteristics
- 19. 19 | 57 ● TDMA - TDD - Frequency hopping ● Mixed voice / data paths ● Encryption, low power, low cost ● Extremely small ● Ubiquitous radio link ● Bluetooth technology offers built-in simple networking on layer 2 − thus it attracted the academic world to do research on dynamic networks basing on scattered, moving, emerging and disappearing mobile devices ● A Bluetooth device may operate in master mode or in slave mode Communication Systems Bluetooth - characteristics
- 20. 20 | 57 ● A maximum of 8 devices (7 active slaves plus 1 master) form a Piconet ● A piconet is characterized by the master: frequency hopping scheme, access code, timing synchronization, bit rate allocated to each slave ● Only one master: dynamically selected, roles can be switched ● Up to 7 active slaves; up to 255 parked slaves ● No central network structure: “Ad-hoc” network Communication Systems Bluetooth network topology - Piconet
- 21. 21 | 57 ● Interconnected piconets, one master per piconet ● A few devices shared between piconets ● No central network structure: “Ad-hoc” network Communication Systems Bluetooth network topology -Scatternet
- 22. 22 | 57 Communication Systems Bluetooth protocol stack
- 23. 23 | 57 ● Radio layer: defines the requirements for a Bluetooth transceiver operating in the 2.4 GHz ISM band ● Baseband layer: describes the specification of the Bluetooth Link Controller (LC) which carries out the baseband protocols and other low-level link routines ● Link Manager Protocol (LMP): is used by the Link Managers (on either side) for link set-up and control ● Host Controller Interface (HCI): provides a command interface to the Baseband Link Controller and Link Manager, and access to hardware status and control registers ● Logical Link Control and Adaptation Protocol (L2CAP): supports higher level protocol multiplexing, packet segmentation and reassembly, and the conveying of quality of service information Communication Systems Bluetooth protocol stack
- 24. 24 | 57 ● RFCOMM protocol: provides emulation of serial ports over the L2CAP protocol. The protocol is based on the ETSI standard TS 07.10 ● Service Discovery Protocol (SDP): provides a means for applications to discover which services are provided or available ● For experimenting the Linux BT stack (www.bluez.org) might be a good start − it is a really good implementation of the standard and supports the various Bluetooth profiles offered by the different devices − it is OpenSource and provides the necessary programming libraries Communication Systems Bluetooth protocol stack
- 25. 25 | 57 Communication Systems Bluetooth profiles and dependencies ● A profile can be described as a vertical slice through the protocol stack ● A profile has dependencie s on the profiles in which it is contained directly and indirectly
- 26. 26 | 57 ● Bluetooth Profiles were written to make sure that the application level works the same way across different manufacturers' products ● Bluetooth applications: − Wireless control of and communication between a cell phone and a hands free headset or car kit. − Wireless networking between PCs in a confined space and where little bandwidth is required − Wireless communications with PC input devices such as mice and keyboards − Wireless communications to PC output devices such as printers Communication Systems Bluetooth - applications
- 27. 27 | 57 − Wireless communications with PC input devices such as mice and keyboards. − Wireless communications to PC output devices such as printers − Transfer of files between devices via OBEX − Replacement of traditional wired serial communications in test equipment, GPS receivers and medical equipment − Thus often a serial interface is emulated over the BT link as shown on the following slides ... − Remote controls where infrared was traditionally used − ... Communication Systems Bluetooth - applications
- 28. 28 | 57 ● Often Bluetooth is the best way to link devices like mobile phones to a laptop mobile linux # hcitool scan Scanning ... 00:0E:07:47:93:1B T610 mobile linux # hcitool cc 00:0E:07:47:93:1B mobile linux # hcitool dc 00:0E:07:47:93:1B ● Scan for Bluetooth devices within the range of the BT adaptor − this is much more fun to do on specific fairs like the Cebit, where you can compile a list of more then 20 devices within range − if your are lucky some of the devices use broken firmware and security could be overridden – with special tools you can access the mobile device, get the phone books, alter entries and so on ... ● hcitool is just a helper to connect, authenticate, disconnect, ... to/from a device Communication Systems Bluetooth in Linux OS – an example for the rfcomm layer
- 29. 29 | 57 ● hciconfig - show the Bluetooth device and its properties mobile linux # hciconfig hci0: Type: PCCARD BD Address: 00:04:76:C8:4A:E8 ACL MTU: 128:8 SCO MTU: 64:8 UP RUNNING PSCAN ISCAN AUTH ENCRYPT RX bytes:1046 acl:0 sco:0 events:58 errors:0 TX bytes:850 acl:0 sco:0 commands:35 errors:0 mobile linux # hcitool dev Devices: hci0 00:04:76:C8:4A:E8 mobile linux # l2ping 00:0E:07:47:93:1B Ping: 00:0E:07:47:93:1B from 00:04:76:C8:4A:E8 (data size 20) ... 0 bytes from 00:0E:07:47:93:1B id 200 time 63.05ms 0 bytes from 00:0E:07:47:93:1B id 201 time 48.13ms 0 bytes from 00:0E:07:47:93:1B id 202 time 45.13ms 3 sent, 3 received, 0% loss ● l2ping is a layer 2 ping utility to check connection on a specific linked device ● as you can see, the average trip time is much higher than e.g. in WLAN Communication Systems Bluetooth in Linux OS – an example for the rfcomm layer
- 30. 30 | 57 ● In next step the emulated serial link could be started mobile linux # rfcomm connect 1 00:0E:07:47:93:1B 1 Connected /dev/rfcomm1 to 00:0E:07:47:93:1B on channel 1 Press CTRL-C for hangup mobile linux # pppd call gprs-o2wap Press CTRL-C to close the connection at any stage! defining PDP context... rATZ OK AT&F OK ATV1E0S0=0&D2&C1 OK ● Which is just used as the lower layer protocol for a PPP connection part between the computer and device ● The mobile phone “translates” the data stream for the WAN GSM interface, GPRS protocol as explained in earlier lecture ● Of course there are more options for BT protocols between the two devices, like OBEX for file transfer (e.g. stored MP3, ...) Communication Systems Bluetooth in Linux OS
- 31. 31 | 57 ● Bluetooth is oriented to connecting close devices, serving as a substitute for cables ● Wi-Fi is oriented towards computer-to-computer connections, as an extension of or substitution for cable LANs. ● 802.11b and Blutooth both utilize the free 2.4GHz band ● no exclusive use ● no guarantees ● special protocol implementations needed to cope with noise, fading, ... ● Bluetooth uses frequency hopping and changes freq. every 42 times a millisecond, hop is synchronized by cell master ● 802.11a/h WLAN standards use the free 5Ghz band ● band is reserved for WLAN only ● range is more restricted than with 802.11b ● bandwidth is increased up to 54Mbit Communication Systems Bluetooth v. Wi-Fi
- 32. 32 | 57 Communication Systems Bluetooth v. Wi-Fi - comparison
- 33. 33 | 57 Communication Systems Bluetooth v. Wi-Fi – comparison (cont.)
- 34. 34 | 43 Communication Systems network technologies and network fusion ● By now we have presented a certain range of communication networks and their underlying technologies ● The “early” (means standards dating from the 70s and 80s) digital wired and wireless networks were focused on the transportation of voice ● The developers of the first drafts on internet protocols had data communication in mind when defining their standards ● The processes of standardization were really different − closed clubs of telephony providers and equipment manufacturers backed up by their states and a rather open process in the definition of internet protocols and applications − but by now both worlds learn of each other and closing the gaps in between ...
- 35. 35 | 43 Communication Systems network fusion ● For a rather long time telephone and data networks were different entities – remember the network taxonomy − packet orientated vs. circuit switched − packet orientation is rather efficient in bandwidth using but cannot give any guarantees on packet delivery − bandwidth growth and optional QoS helped to offer service quality near to circuit switching ● Why to provide two completely different infrastructures for rather the same services? − voice is just another piece of data (and not the biggest one compared to other applications and services in use)
- 36. 36 | 43 Communication Systems real time communication ● traditional telephony networks are circuit switching networks − rather centrally operated − setup of connection inband or out of band before communication starts − no routing delays in transmit − reserved bandwidth for every connection − rather homogeneous transport media ● more and more real time services are handled over the Internet, but − hop-by-hop routing without clear hierarchy − different media and bandwidth
- 37. 37 | 43 Communication Systems real time communication ● Voice-over-IP (VoIP) is a big hype at the moment − every network equipment vendor has some products in its portfolio (even companies like Siemens are able to offer products conforming to standards!!) − many new “telephone companies” evolve to offer services, the old providers have to think on new strategies − all of them hope for reduction of costs and a source for roaring profits :-) ● so TCP/IP is just used for another application/service
- 38. 38 | 43 Communication Systems delay in communication ● This service has to meet some requirements ● Important issue in communication – delay and packet loss (infinite delay) ● Many applications heavily depend on near no delay (e.g. real time communication, like VoIP, Video and multi- user online gaming ... :-) ) ● Routing delay − High setup delay in virtual circuit networks – no delay if path is set up (imagine telephone network) − No setup delay in datagram networks, but routing decision for every packet in every router
- 39. 39 | 43 Communication Systems delay in communication ● Other types of delay − Transmission, nodal processing, queuing, propagation delay ● Transmission delay (example given with message segmentation) − Is L/R (L size of packet in bit, R rate in bit/s) − e.g. Packet of 1500Byte (standard MTU – max. transfer unit in ethernets) on 100MBits LAN travels 0,000015s (=15µs) to be transferred completely
- 40. 40 | 43 Communication Systems delay in communication ● Ping between two hosts connected via 100Mbits ethernet − Linux-OS, between 550MHz PII/Cel and P4/2,4GHz, 100Mbits interface cards
- 41. 41 | 43 Communication Systems delay in communication ● Processing delay is time for − Evaluating header information − Check for bit errors − Decision on outgoing route ● Should be in order of microseconds in high speed routers and servers ● Queuing delay – in packet switching networks overbooking of resources may occur (no bandwidth reservation as with VC) − Packets have to wait (a certain time) until sent out
- 42. 42 | 43 Communication Systems delay in packet switched networks ● Propagation of signal in physical medium may add to delay too − Normally in order of nanoseconds in LAN and milliseconds in WAN − We cannot do much on it – but we get some problems: ● Imagine 300km WAN optical link of 10GBit/s (e.g. in GEANT) ● 300km/300.000km/s=0.001s (1ms) ● 10GBit/s*0.001s = 0.01GBit = 10MBit “on wire” (signal sent out but not received by destination) ● => rising “capacity of wire” with rising speed − Important problem in cluster and parallel computing (!) - you need extremely fast connections on very short distances
- 43. 43 | 43 Communication Systems delay in packet switched networks ● Propagation and transmission delays are different − Propagation is the travel time of one signal (single bit) − Transmission measures time for transferring one packet (independent on distance, but dependent on bandwidth and packet size) ● Processing delay is sum of delays mentioned above dnodal = dtrans + dproc + dqueue + dprop ● Contribution of every delay to dnodal may vary heavily
- 44. 44 | 43 Communication Systems delay in packet switched networks ● The delay of packets in the output queue dqueue is most important − Depends on the traffic intensity − Even when average traffic rate is lower than bandwidth long queues may build up with very bursty traffic − First packet is sent out directly all following can suffer increasing delay − Standard problem on routers with different uplink bandwidth ● If outgoing queue is full packets are dropped ● Packet losses increase with traffic intensity
- 45. 45 | 43 Communication Systems delay in packet switched networks ● End system to end system delay is sum of all nodal delays along the path from source to destination ● Helper program to get an idea on path and delay is traceroute (exercises in practical course, see mtr too)
- 46. 46 | 55 ● Voice over IP and Quality of Service: − Major challenges: delay and delay variation (jitter) − Delay jitter is the variability of source-to-destination delays of packets within the same packet stream − Voice applications are usually interactive − delay requirement for a telephone system: 150ms-250ms ● We identified some of the sources of delay in a voice over IP system: − OS delay: 10s-100s milliseconds (digitisazion of data, compression and inter software data handling) ... ● Special multimedia protocol is introduced next lecture ... Internet Working requirements towards network
- 47. 47 | 57 Bluetooth v. Wi-Fi − http://dienst.isti.cnr.it/Dienst/Repository/2.0/Body/ercim.cnr.isti/2004-TR- 27/pdf?tiposearch=cnr&langver= − http://en.wikipedia.org/wiki/Bluetooth WiMAX − 802.16: http://standards.ieee.org/getieee802/download/802.16- 2004.pdf − IEEE 802.16a: http://www.wimaxforum.org/news/downloads/WiMAXWhitepaper.pd f − Telephoy's complete guide to WiMAX: http://www.wimaxforum.org/news/press_releases/Telephony_WiMAX.pdf − http://computer.howstuffworks.com/wimax1.htm − http://searchnetworking.techtarget.com/searchNetworking/downloads/Finneran.pd f − Can WiMAX address your application: http://www.wimaxforum.org/news/downloads/Can_WiMAX_Address_You r_Applications_final.pdf − http://www.wimaxforum.org/technolog Communication Systems End/Literature
- 48. 48 | 35 Bluetooth − http://www.palowireless.com/infotooth/tutorial.asp − 802.15.1 2005: http://standards.ieee.org/getieee802/download/802.15.1-2005.pdf − http://bluetooth.com/NR/rdonlyres/7F6DEA50-05CC-4A8D-B87B- F5AA02AD78EF/0/Protocol_Architecture.pdf Network delay - Kurose & Ross: Computer Networking (3rd) Tanenbaum: Computer Networks (4th) Communication Systems End/Literature
