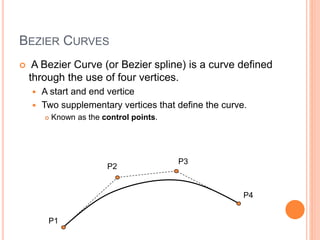
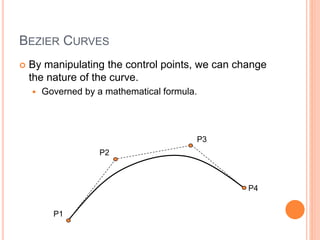
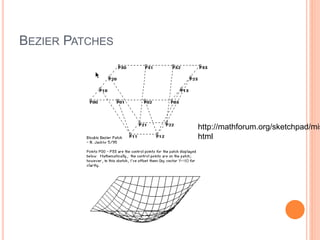
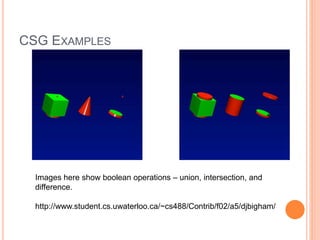
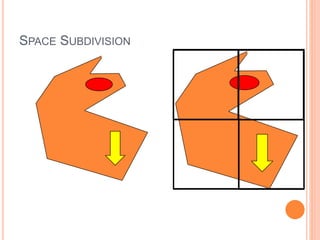
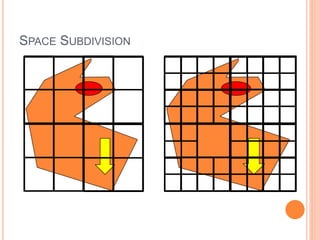
The document discusses various techniques for representing 3D graphics beyond polymeshes, including Bezier curves, Bezier patches, NURBS, constructive solid geometry (CSG), and space subdivision. Each method is described with its advantages, drawbacks, and applications, highlighting how the choice of representation affects the intended use and efficiency. The lecture emphasizes the mathematical modeling and control points involved in shaping these graphical representations.