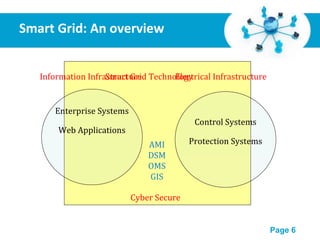
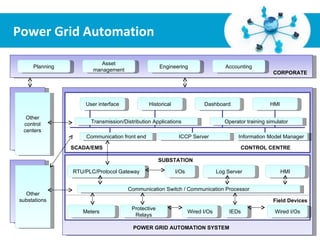
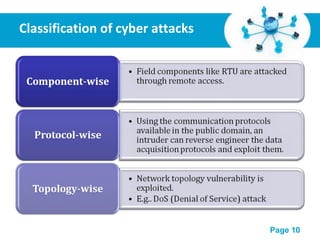
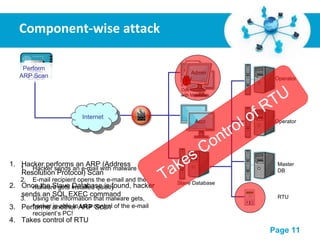
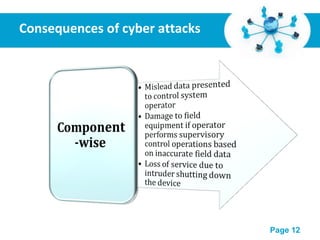
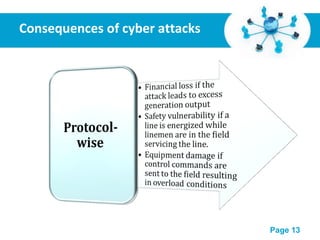
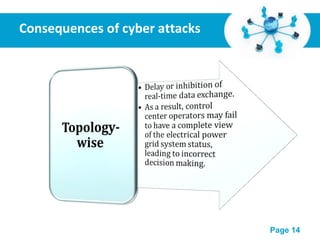
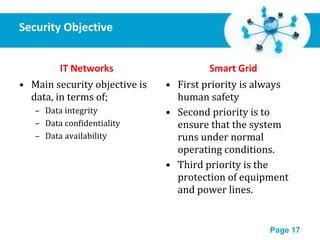
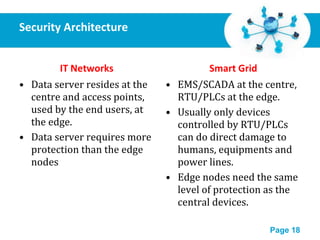
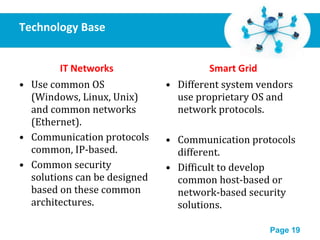
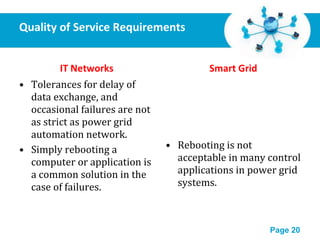
This document discusses the cyber security risks of smart grids and proposes an integrated security framework to address these risks. Smart grids integrate information infrastructure with electrical infrastructure, improving performance but also increasing vulnerability to cyber attacks. The framework features security agents, managed security switches, and a security manager to provide layered protection, intrusion detection, and access control across the power automation network in a scalable and extensible manner. This integrated approach is needed as power systems have different security needs than traditional IT networks.