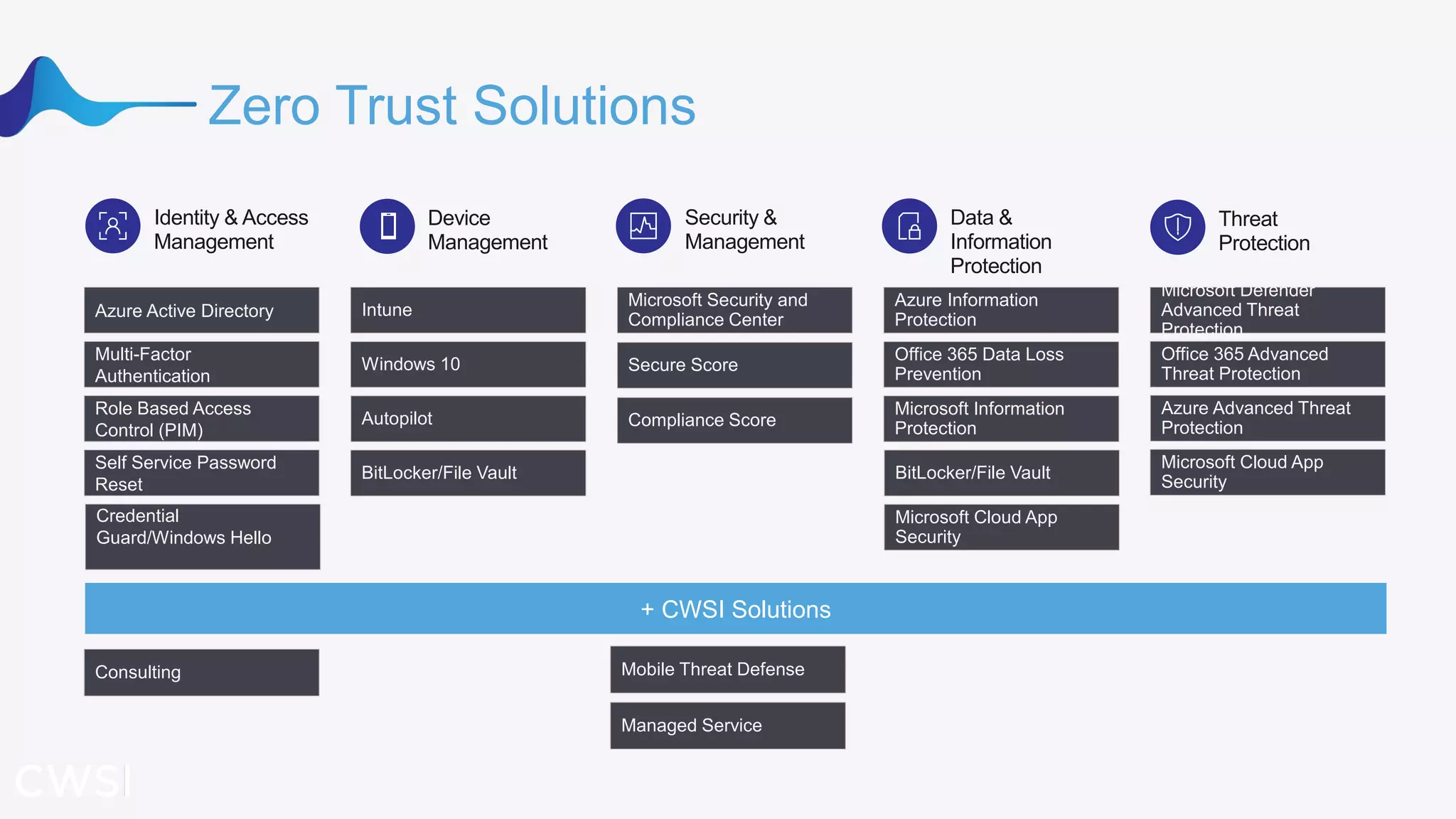
The document outlines a strategy for implementing a modern zero-trust security framework over 30 days, emphasizing the need for a security perimeter that adapts to evolving threats. Key principles include always verifying user identity and device health, minimizing access based on necessity, and utilizing adaptive policies for risk management. It highlights the increasing risks from identity attacks and recommends integrating strong authentication measures and robust identity and access management solutions.