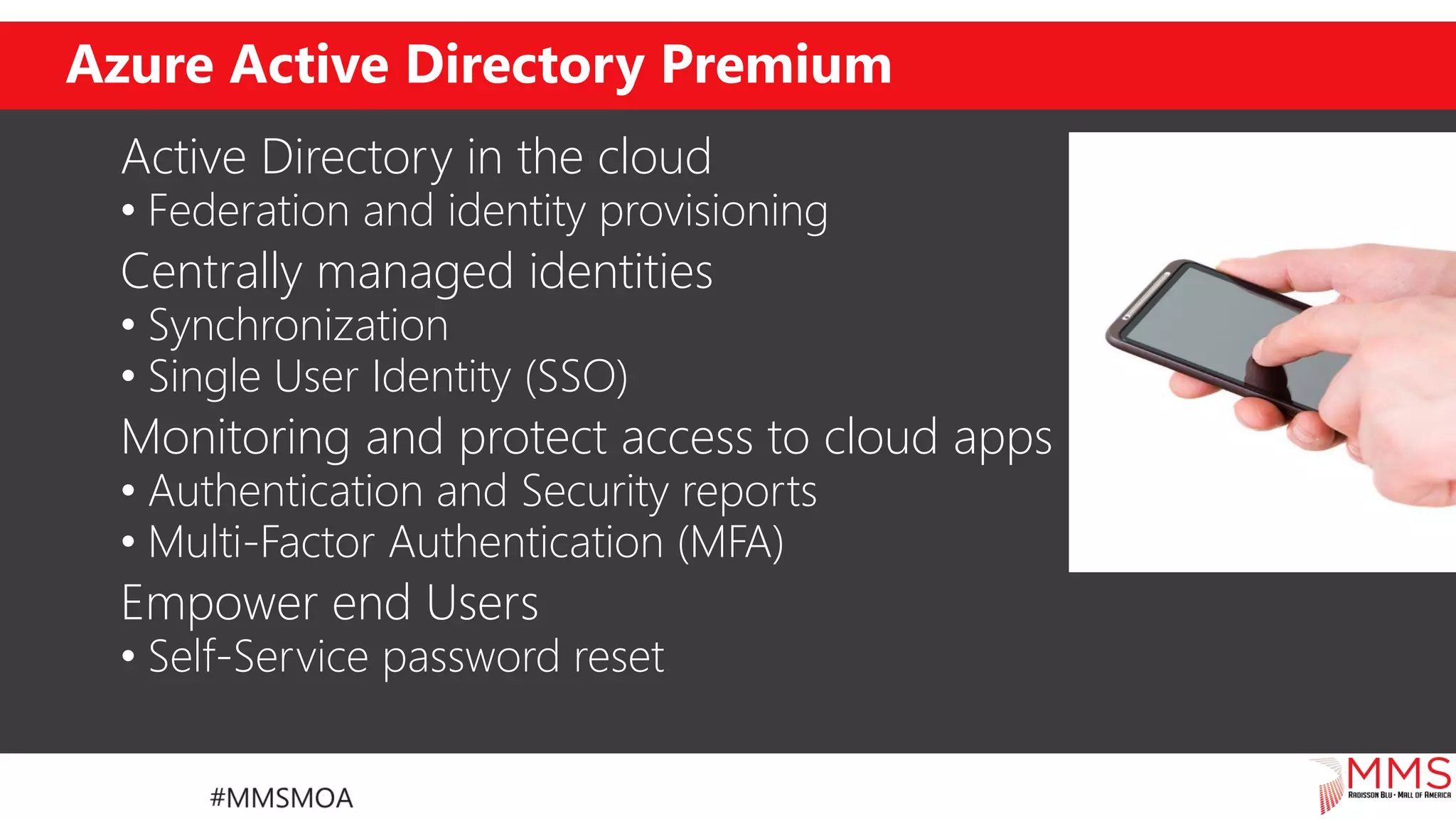
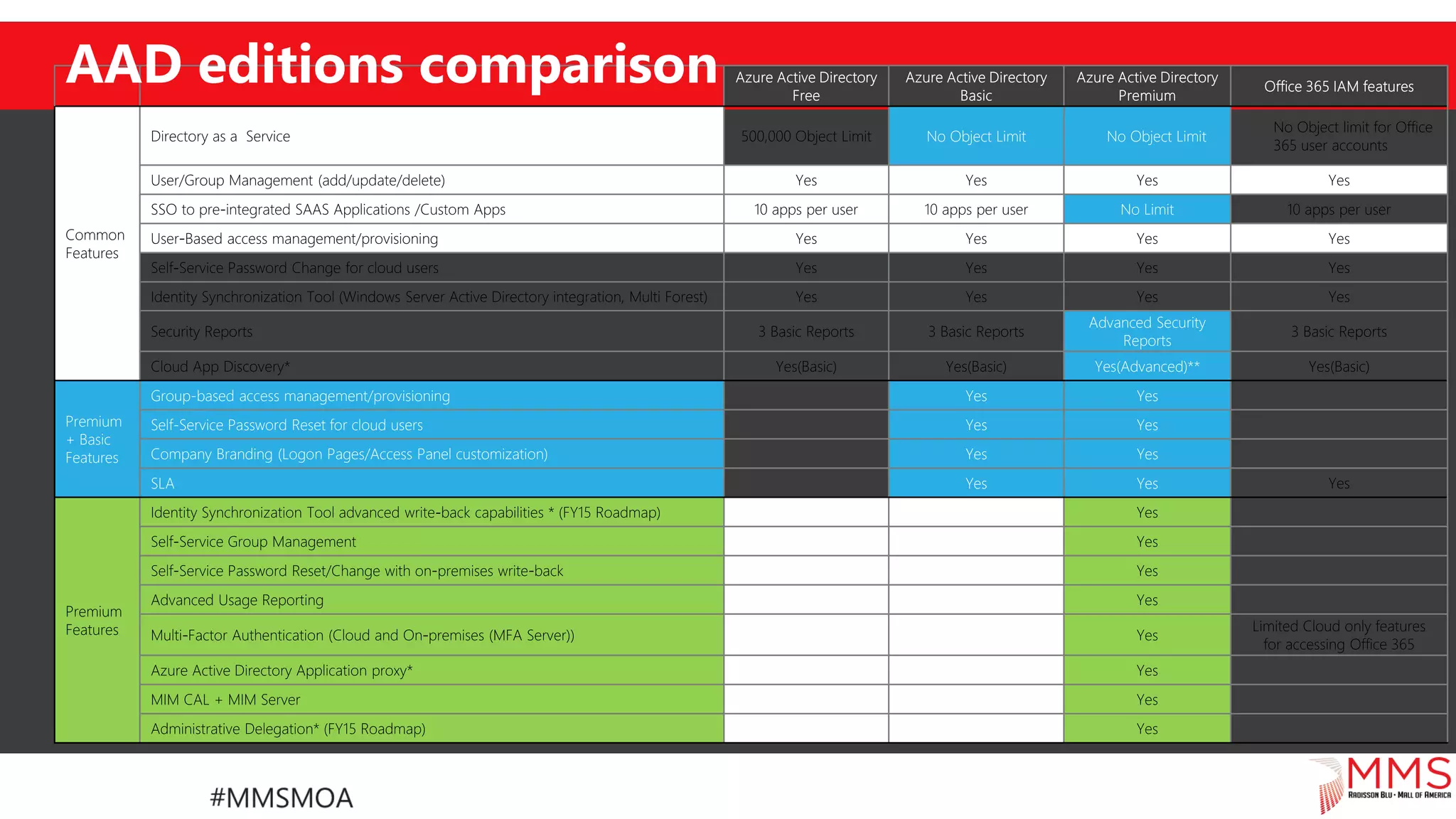
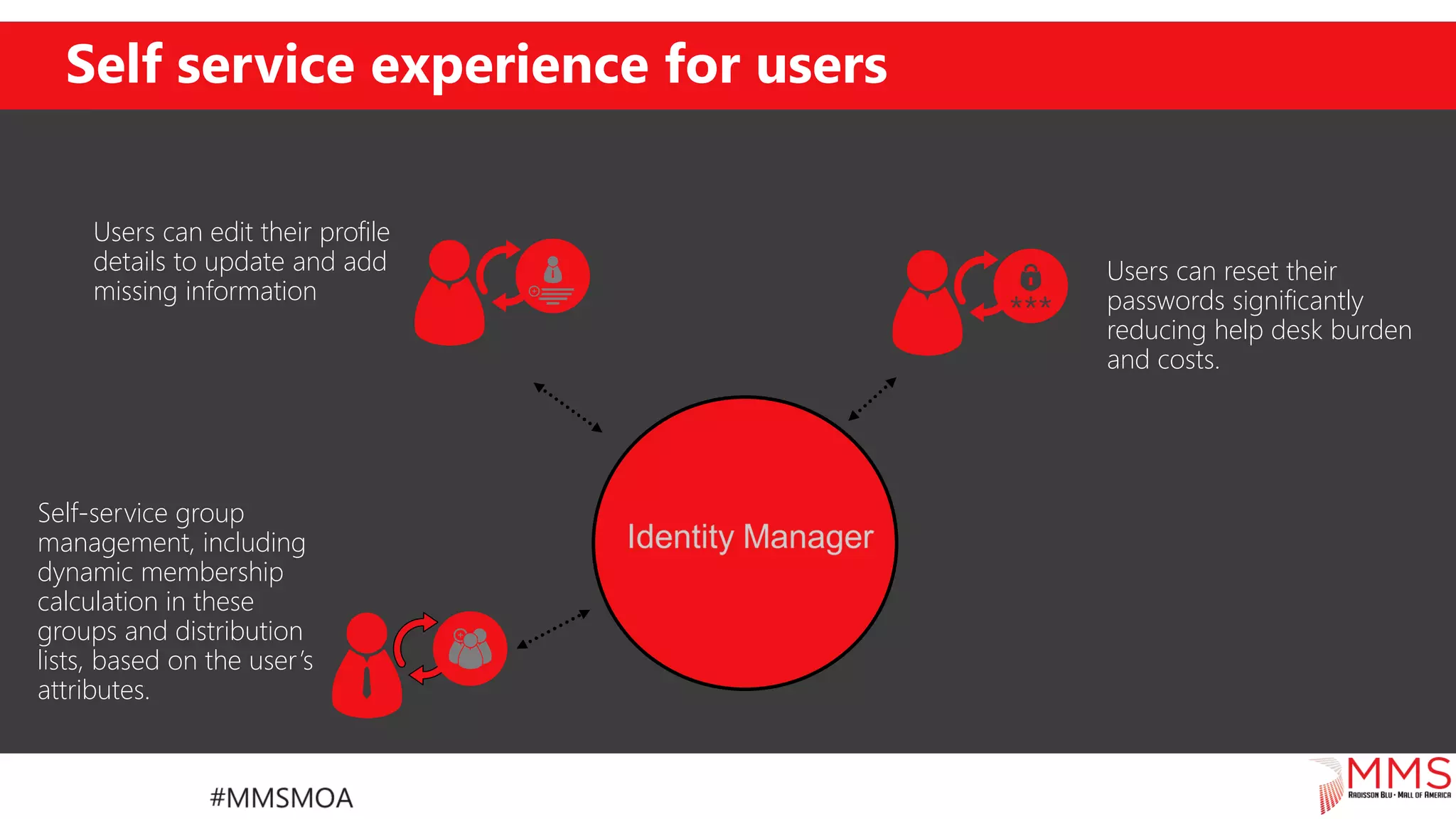
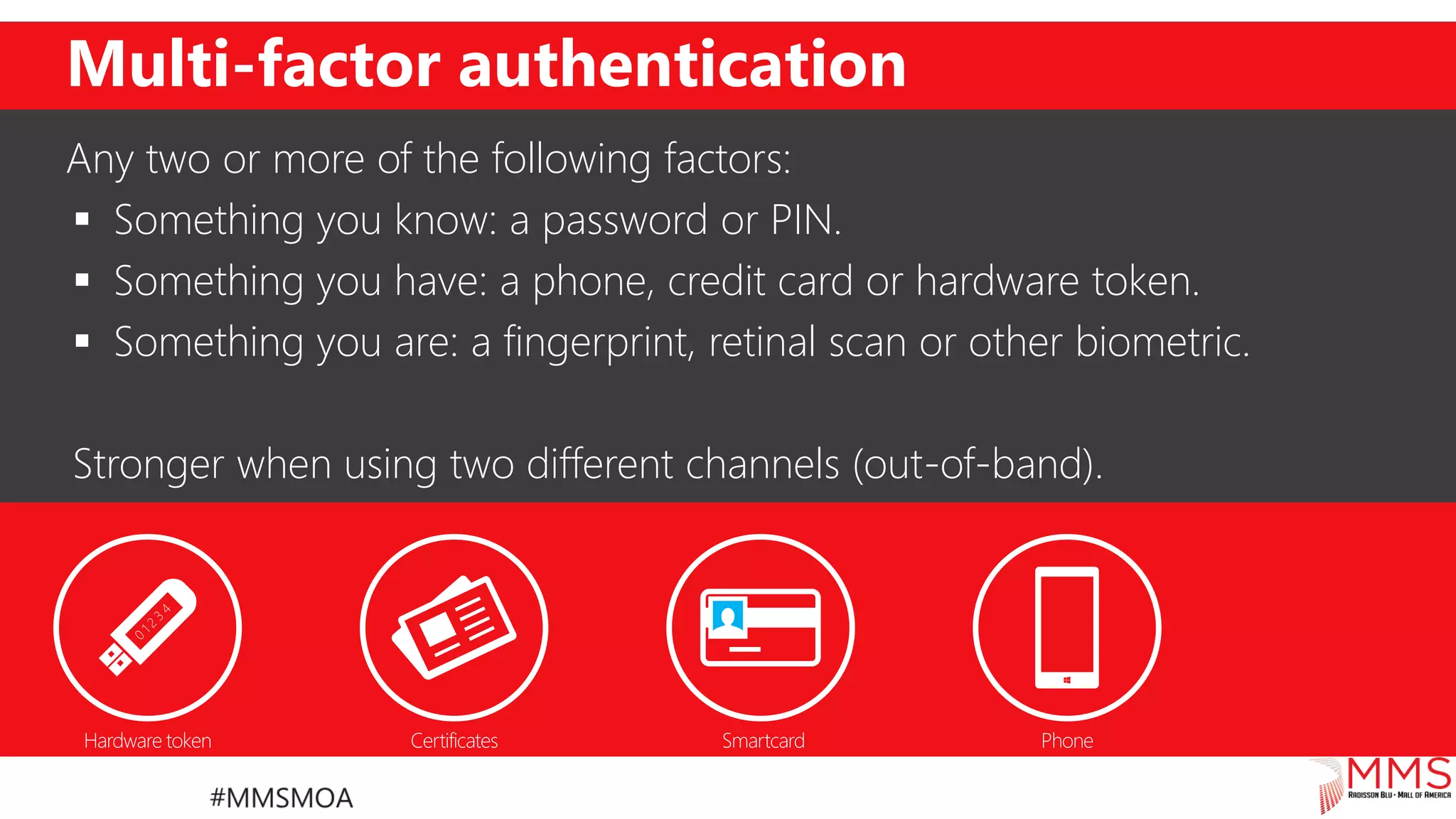
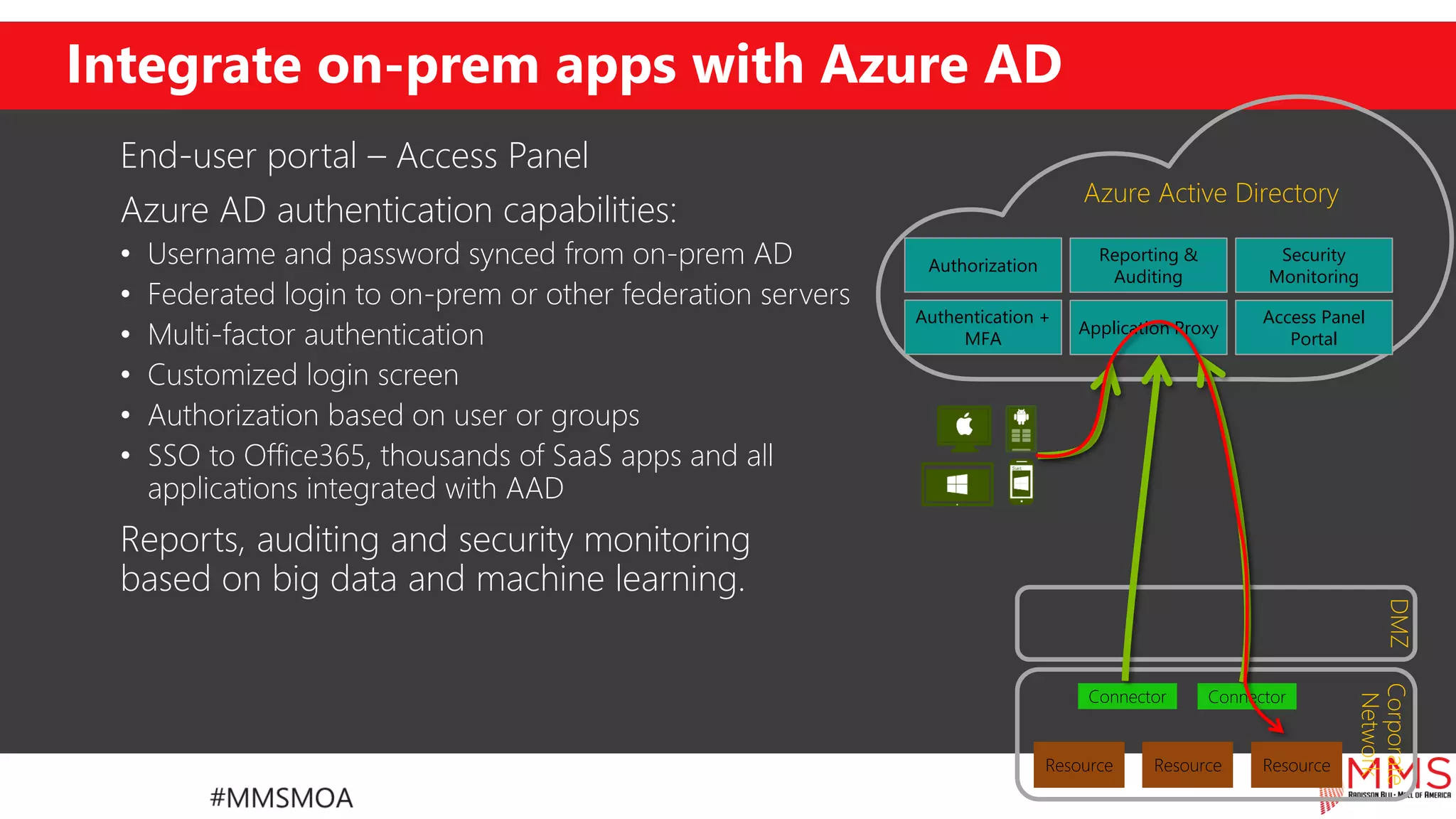
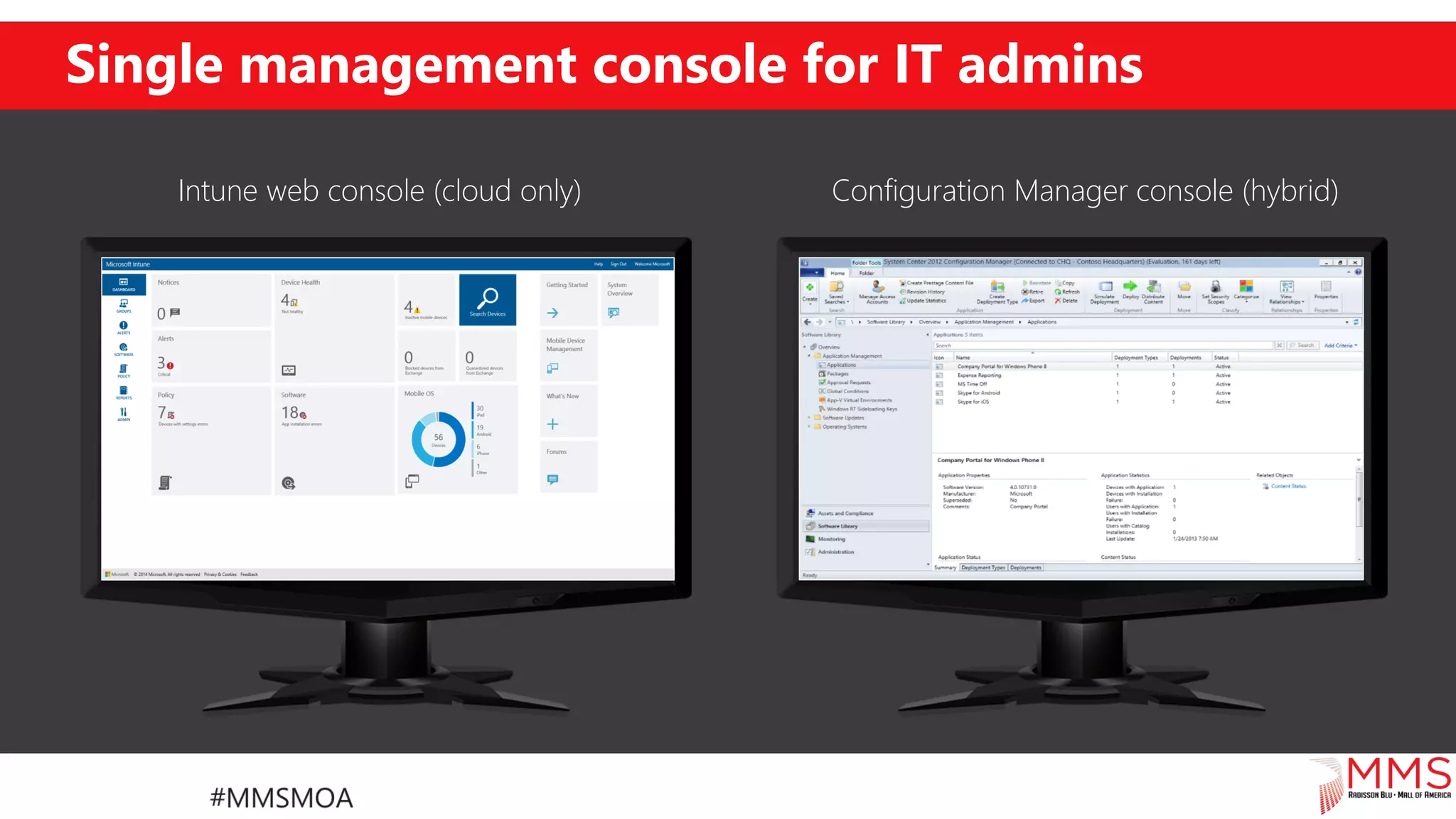
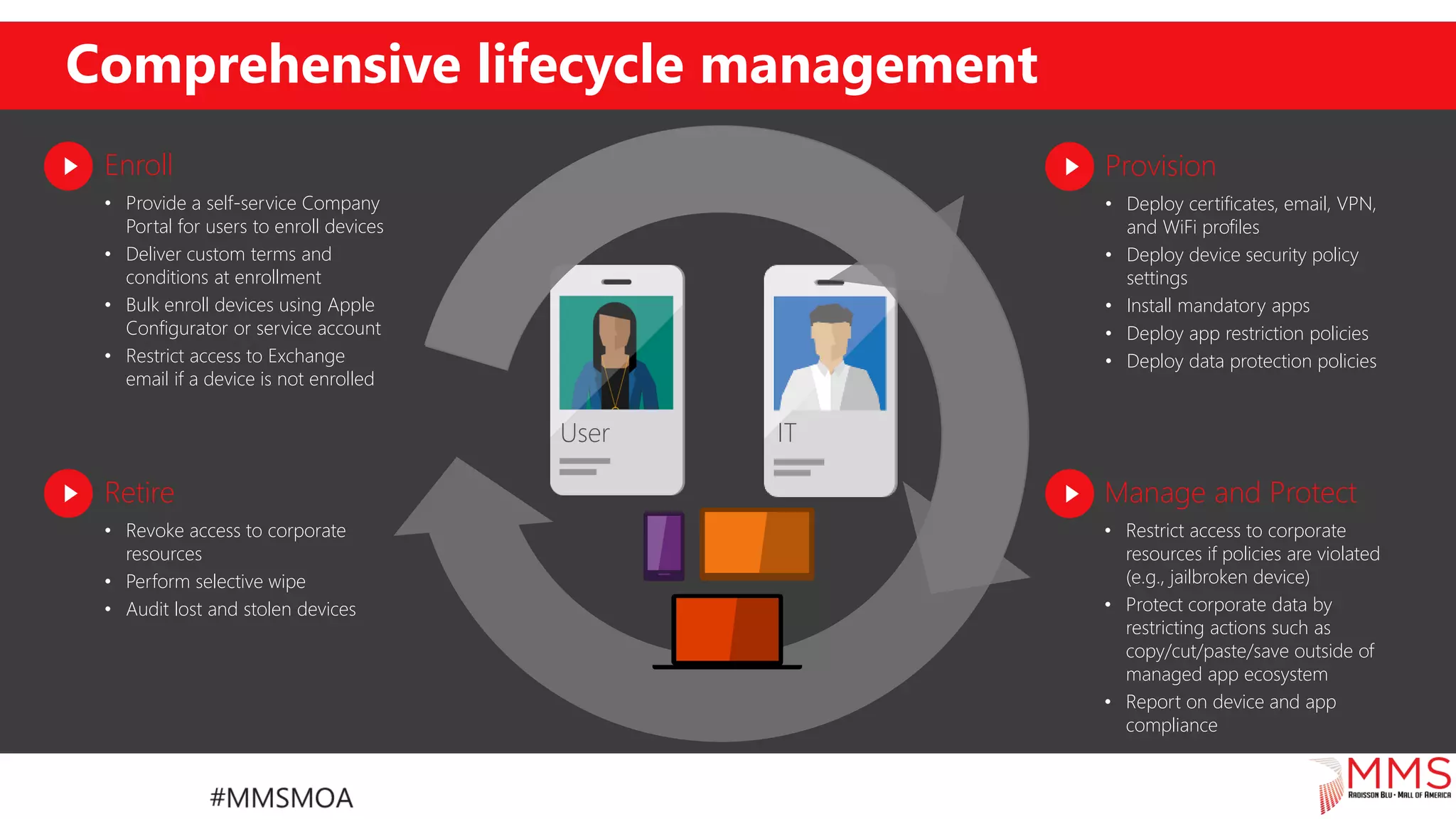
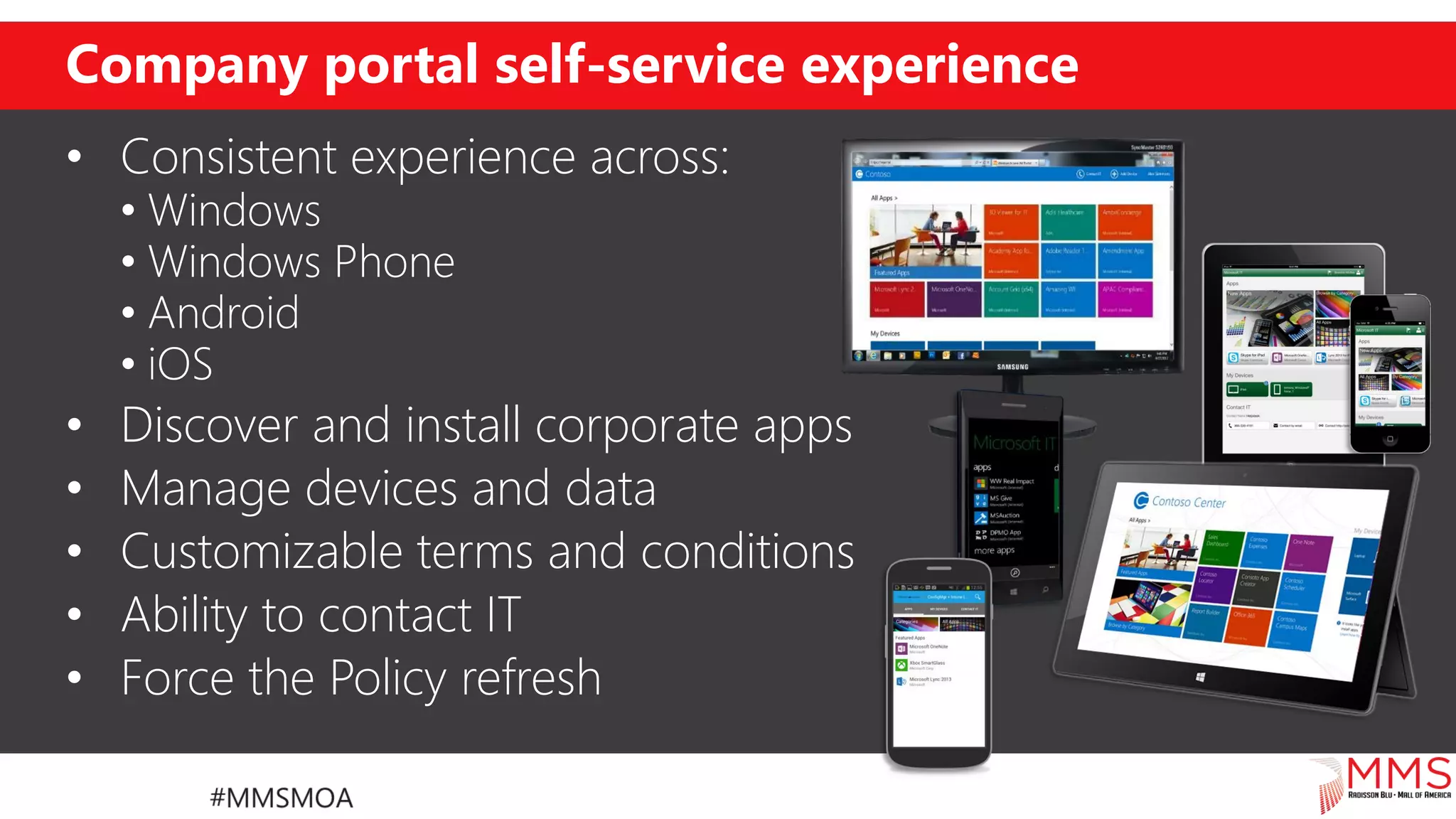
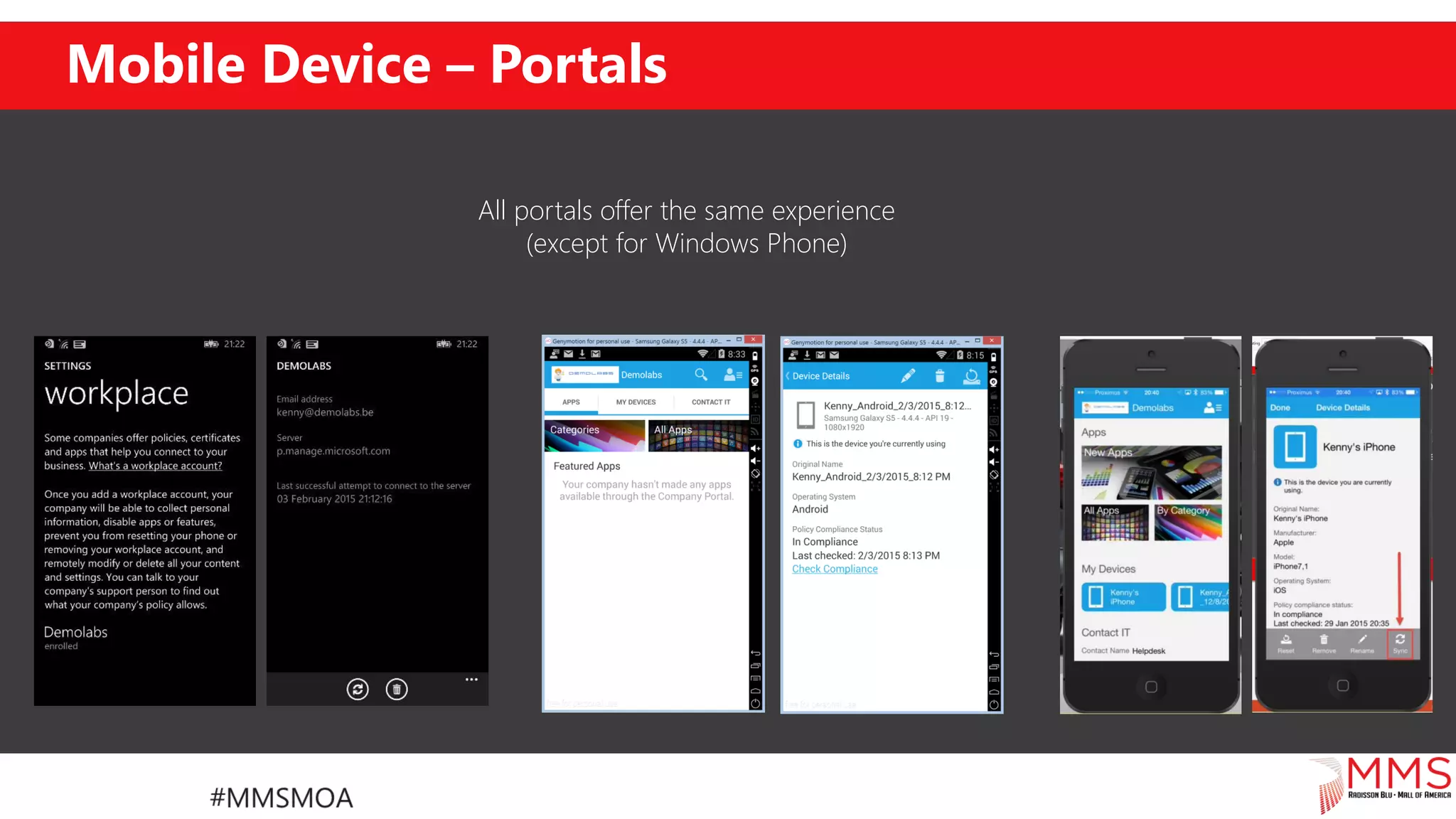
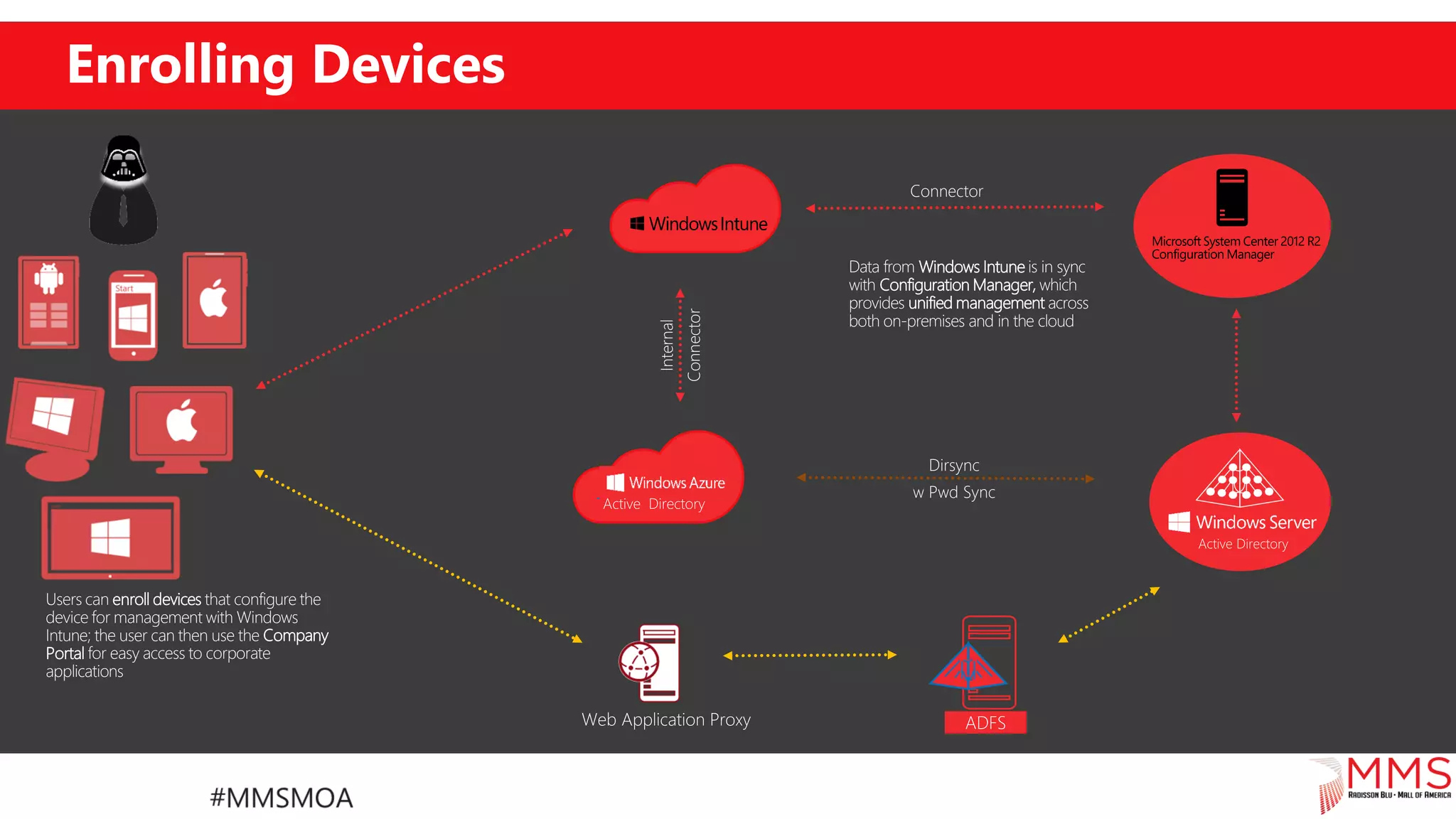
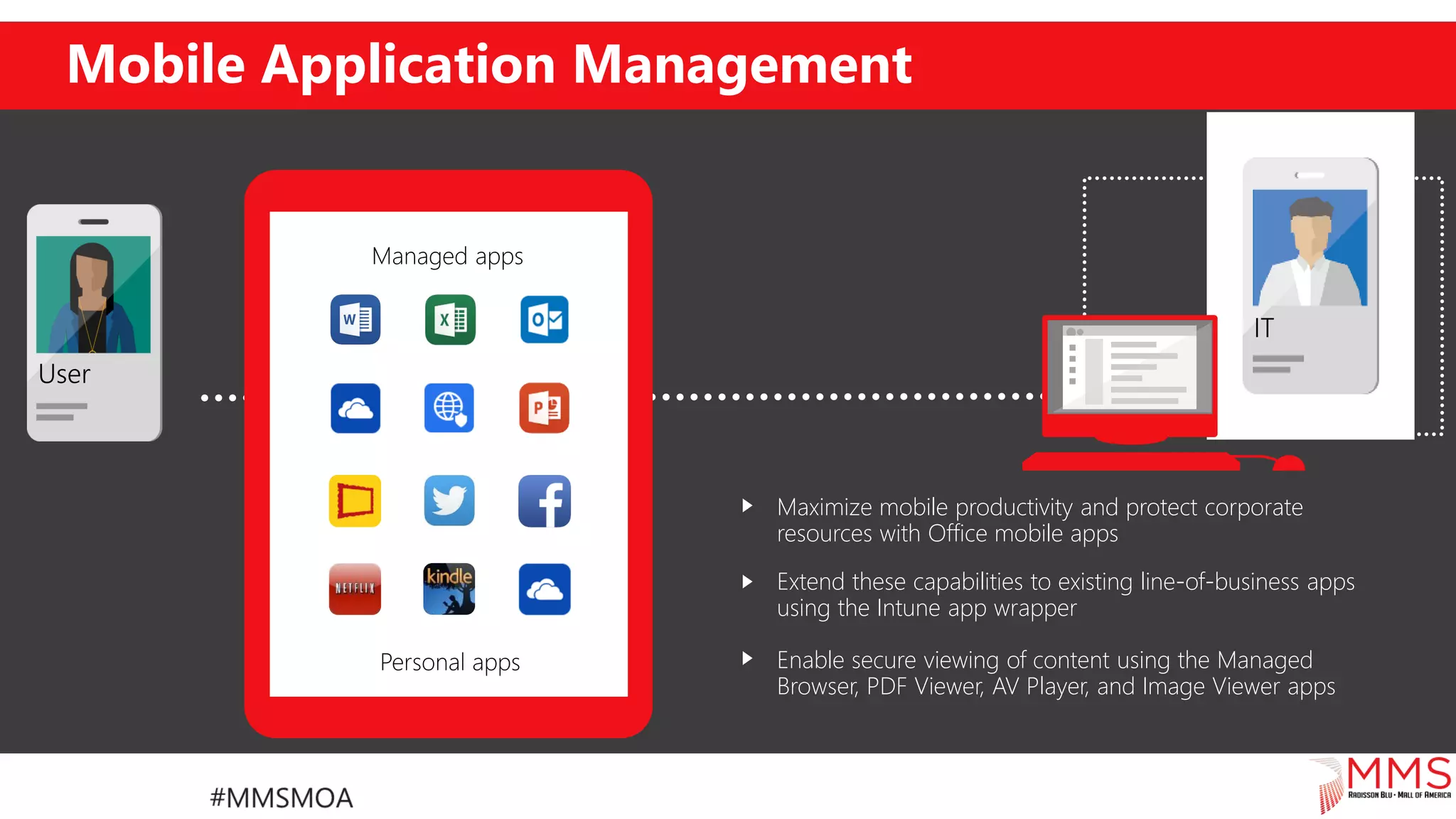
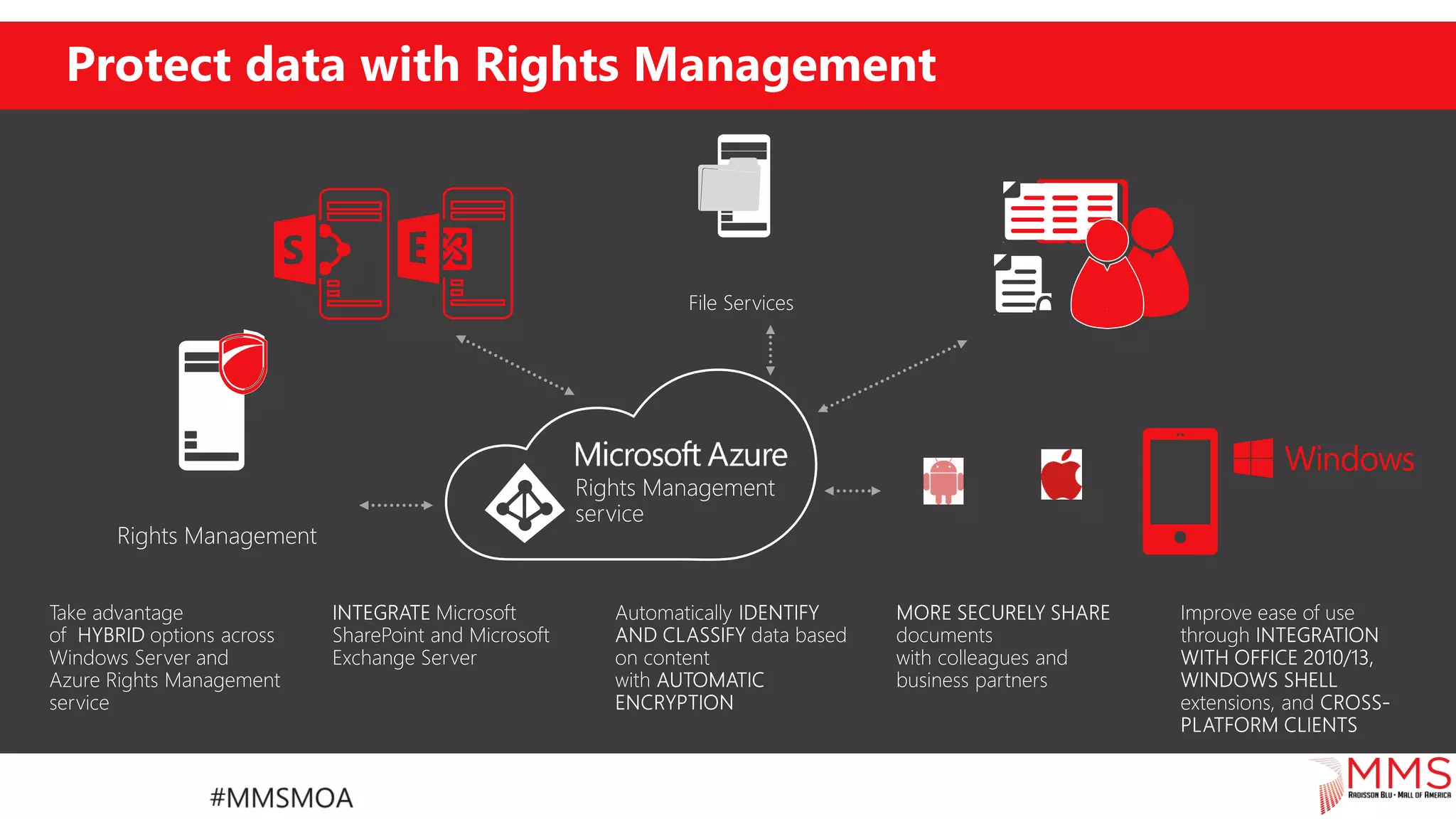
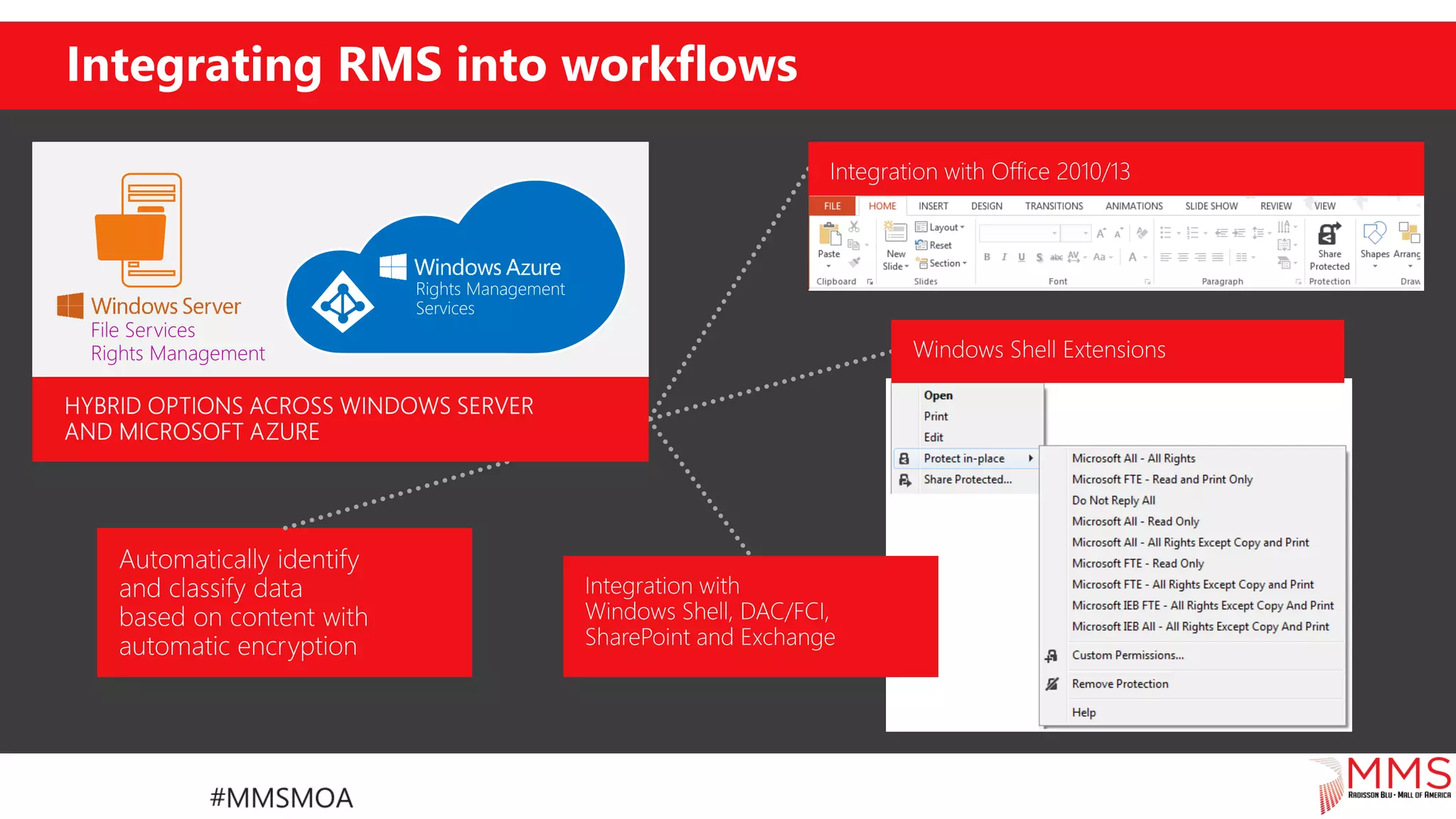
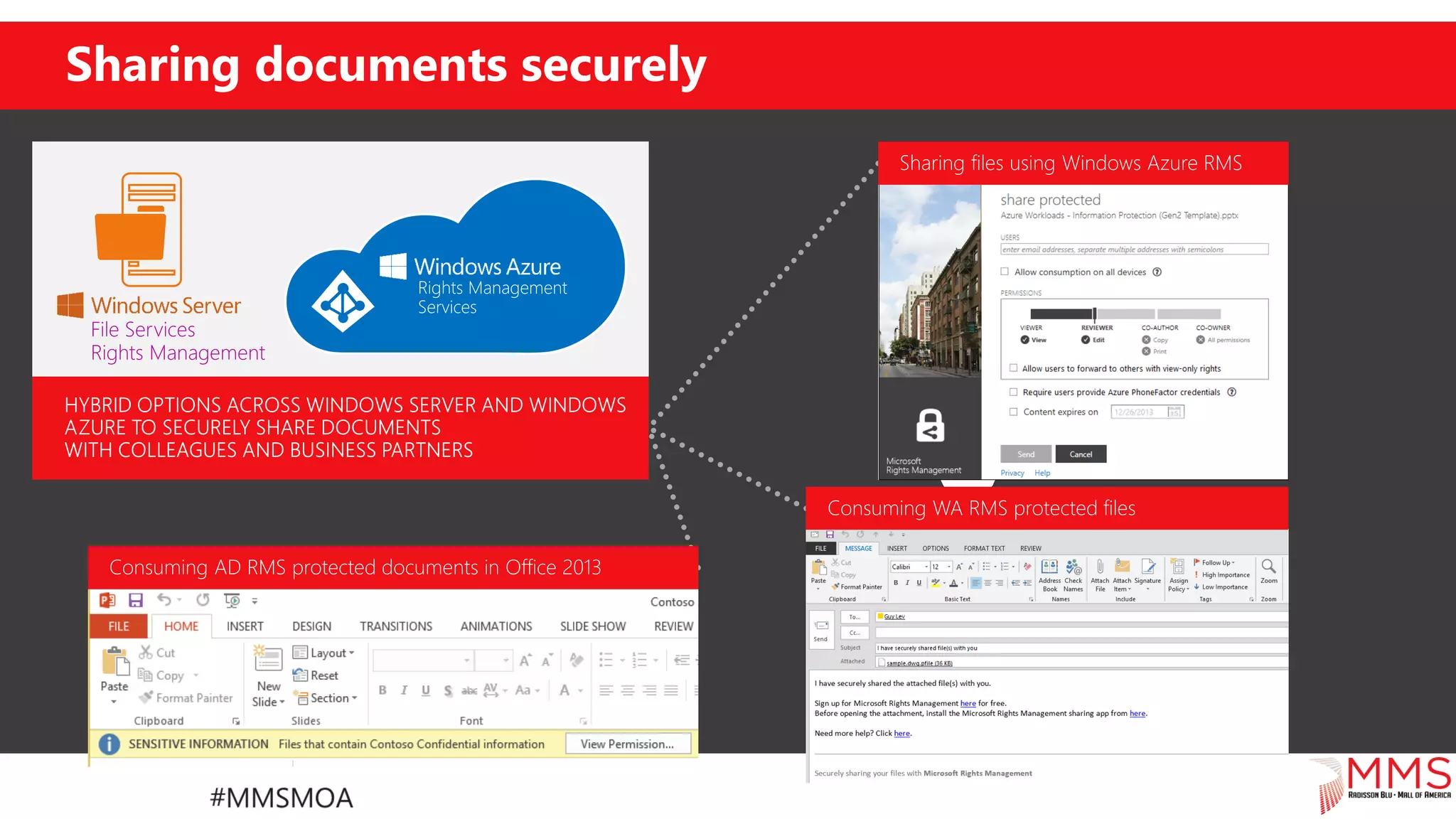
The document provides an overview of Microsoft's Enterprise Mobility Suite (EMS), which includes Azure Active Directory Premium, Microsoft Intune, and Azure Rights Management. It outlines key features such as mobile device management, identity synchronization, multi-factor authentication, and access control, as well as steps to configure and get started with EMS. It also emphasizes the benefits for organizations, such as enhanced security and user empowerment through self-service capabilities.