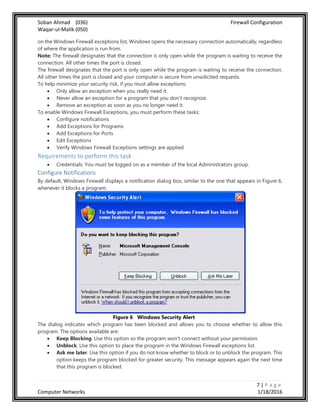
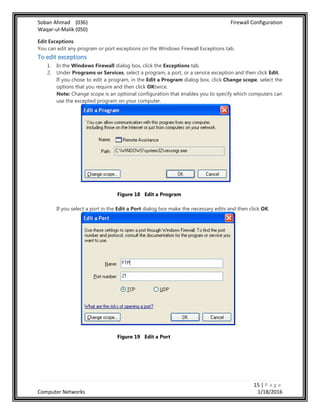
The document details how to configure the Windows Firewall, including general settings, exceptions for programs and ports, and advanced settings. It provides instructions for enabling/disabling the firewall, adding exceptions, and best practices for maintaining security. The purpose is to allow users to customize their firewall setup according to their specific needs while understanding the associated risks.
![]
FIREWALL CONFIGURATION
Report by : Soban Ahmad (036)
Waqar-ul-Malik (050)
Section : A
Program : BS-SE
Date 1/18/16](https://image.slidesharecdn.com/cnbilkulfinal-160208150427/75/Windows-Firewall-Its-Configuration-1-2048.jpg)