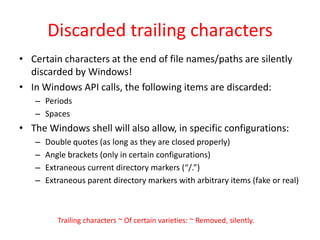
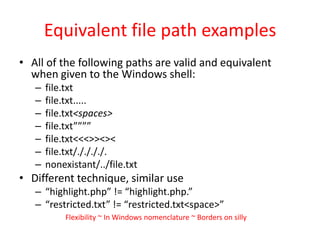
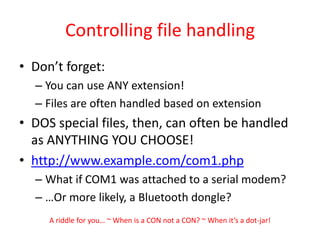
The document discusses various aspects of Windows file naming conventions and their potential security implications, particularly focusing on 8.3 aliases, special device files, and the ways applications may misinterpret file paths. It emphasizes how these features can lead to vulnerabilities such as authentication bypass, denial-of-service, and buffer overflow attacks. Through poetic haikus, the author highlights the complexities and quirks of Windows file systems, demonstrating that filenames can significantly impact security in web applications.



![8.3 AliasesIn DOS, file names must conform to the 8.3 format, meaning:A basename of (max) 8 charactersFollowed by one periodFollowed by a (max) three character extensionWindows likes backwards compatibilityEach file (and directory!) created on default Windows installations has a DOS-compatible nameIf the name isn’t 8.3 compatible, a second name (an 8.3 alias or short file name [SFN]) is madeSimplified, they are generated as follows:Remove some characters (0x80-0xff) and convert some characters to underscores (like + and space)Start with the first six charactersAdd a tildeAnd a digit to distinguish from other files starting with the same charactersAdd a periodAnd up to the first three characters of the file extensionWindows might as well ~ Be backwards-compatible ~ With the abacus](https://image.slidesharecdn.com/windowsfilepseudonyms-100720111702-phpapp01/85/Windows-File-Pseudonyms-5-320.jpg)

![Web App Authentication BypassConsider the following scenario:Admin.php checks for authenticationIf authenticated, several external scripts can be called through Admin.php at the whim of the userDeleteUser.php, AddUser.php, UpdateWebPage.phpThese external scripts cannot be called directlyif($_SERVER[‘PHP_SELF’] == ‘/admin/DeleteUser.php’){ die(‘O RLY?’);}else{ do_something_privileged(); }YA RLY‘/admin/DeleteUser.php’ != ‘/admin/DELETE~1.PHP’I’m taking a break ~ From sensible haiku now ~ Tonsillectomy](https://image.slidesharecdn.com/windowsfilepseudonyms-100720111702-phpapp01/85/Windows-File-Pseudonyms-7-320.jpg)