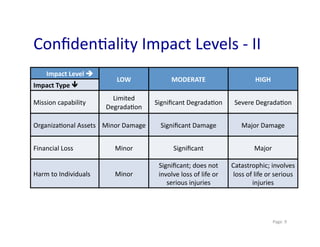
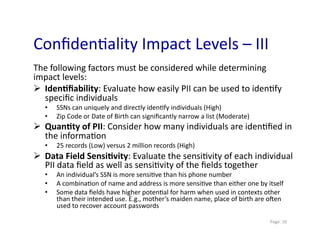
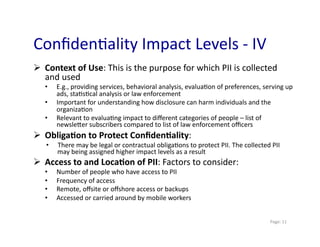
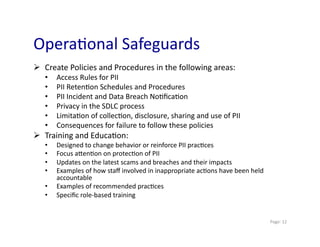
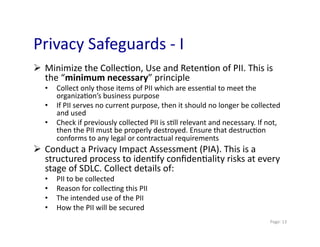
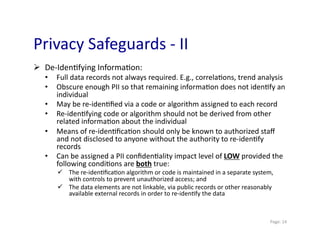
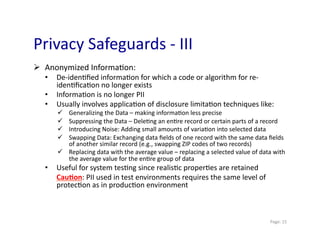
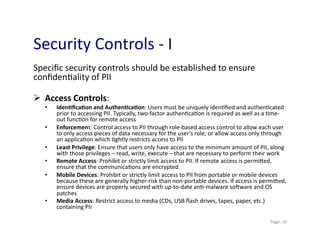
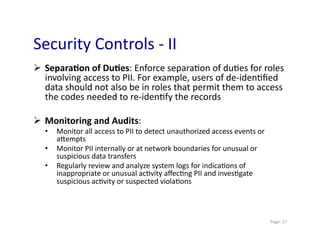
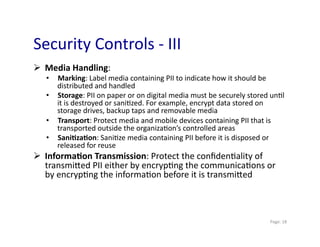
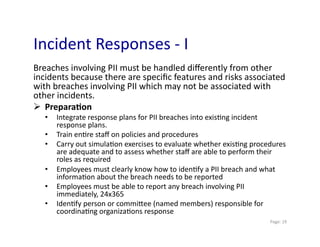
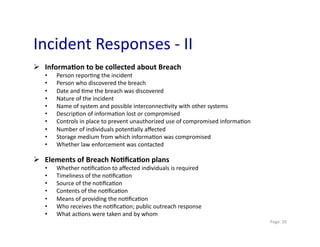
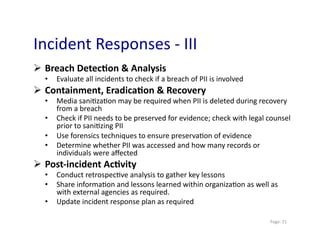
This document discusses personally identifiable information (PII) and provides guidance on managing PII. It defines PII as information that can be used to identify an individual. The document notes that data breaches involving PII are common and outlines legal issues related to PII. It recommends assessing the confidentiality impact of PII and implementing appropriate controls based on the impact level. Specific steps are outlined to help organizations properly manage PII.