The document discusses how web servers work and the technologies involved, including web browsers, TCP/IP, DNS, HTTP, SSL, CGI, MIME, URLs, programming languages like PHP and ASP.NET. It explains the differences between static and dynamic content, in-process and out-of-process dynamic content execution, and server-side versus client-side execution. Sample code is provided for PHP, ASP, and JavaScript to demonstrate dynamic content generation.


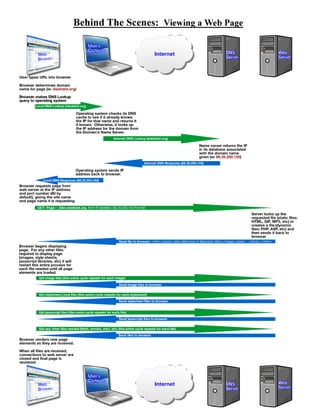










![Note the last line the browser sent to the server:
Authorization: Basic YWRtaW5pc3RyYXRvcjpzZWNyZXRwYXNzd29yZDk5OQ==
This is the how the browser sends the HTTP “Basic” Authentication data to the server. It looks like it contains
an encrypted password, which is probably quite secure. However, it doesn’t.
What it contains is an encoded, not encrypted, password. This means that you can easily decode it if you
know what the encoding method is. In this case, we know that the encoding method is Base64 because the
HTTP protocol specification says that is what is used here.
If we decode the string (just Google for “base64 decoder”), the line changes into:
Authorization: Basic administrator:secretpassword999
We can now see that the user name was administrator and the password is secretpassword999.
This information could (and is) easily “sniffed” (listened for and copied) off the network by any machine
between you and the web server you are connecting to. This means that an ISP, network provider, hosting
company or anyone who has compromised (virus, worm, Trojan, hack) any machine along the way can simply
collect usernames and passwords “off the wire” without anyone ever knowing it has been done.
The only way to securely use HTTP Basic Authentication is to use it over a secure SSL connection.
Web Server Security – Secure Sockets Layer (SSL)
The Secure Socket Layer (SSL) is a “Holy Grail” of Internet security. It is a protocol that fully encrypts, using
robust and reliable encryption, all the communication between the web server and the web browser. This means
that anything that is viewed will be invisible (except for the web server and hostname being connected to) to
anyone else on the Internet.
To access a web site using SSL, instead of using the http://domain.com format of URL, use HTTPS for the
protocol instead, like this: https://domain.com .
This will ensure that all communication between the server is fully encrypted (again, except for the web
server’s IP address being contacted and the hostname of the web site being accessed).
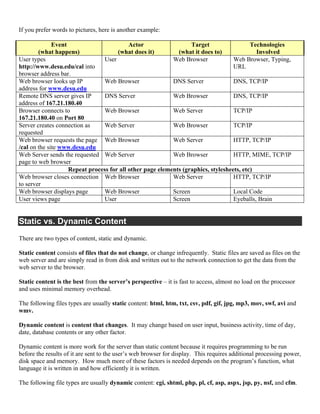
For example, here is the same session over SSL:
..................{...{.55.....9f..&mb8..jn ...'I.P...<.|.J..>mM.............8.
...9.8.....5.........3.2............./.........
.....
...-.........www.diamondsea.com.
....................J...F..Gg.....aX..x..Sd.}$$m4c...r.t..F
...'I.P...<.|.J..>mM.............9...........0...E.......k.D....A.k.Yu.hp.^.../."..u...W.
..o............0...........<O.t.....t:..a.xf....`..8..IK..EB........p......p.x..86R+.j...
..w.U^...{^."C
..>.3........^...DHy...KH.......*...:...g.c...hV.X.J.W...z....e..........f%n.N.....(,..,
.i...(.^..8.h..dB...n....==o...{..G..=( ..(B....n..w&..m.].t/i..............)...-
.Ju.....Dq.[.Qa......,.....p..}.....I..u...{...S
.m'Z..m2.B...](https://image.slidesharecdn.com/webservers-howtheywork-130224010854-phpapp01/85/Web-Servers-How-They-Work-16-320.jpg)
![Vp"6..._..[.....2..Ha....-
.Y.kNUH.9..w.S..`...Z#..f.uS.:...X...u...h..=....[r.n#@...._.k,0.Tm..9;......
....e.DTf..........E.:........|+;T'^...l)...........'Y.H....k.x...i..@.......8>o.%e.R...
..7..+]...y|.b.e3[..{...]....U7^.-
....}.x9.A.L........Q.d.1...MP2vz..;.A....R...@..t.B...OC.e..=..$....1..-
j.m.I?...,....*.a.%.5oZ....|.].{Z..9.+...
.....M.2 ..v-W+Q9.qV.".xF...|.7......v.....s.*.q....
.0...j..6.....*.P.....W..9..wQrNs.-
......."bK.B.E..,V....q.M..V..j.~..Y...R;.V..,v.q..kbI..|..x...Gq...VmAR.X..
......).9fpw..8....(d..k.....r.<0.......D...}s.c....M~.L...{..l..Fg.p..Q!..^...VewLUb.C.c
....q...B.d....9s2...5R..[k
........p......t...C.....K....-[.....YG..b.
!....O..#f.....Es0.......[v=.z[.7..3.....Z...>..h........_.Y..s._.>|.Y0I....T.}%g.....%M.
.8.x.^...=.+..'.eq3E.k.`.V..@.T"/.0.>..%B..x.....57.s<...r...i.6....N.....FN.....k.w.....
.....Q.T.T..+..P/m...np......J.#&..t._....j>.t.h9....r...
..Z$^...Z^..T..I......../...e....ZjJK.Oi.8.........7IT.W....<?^1.2ej.l..PS&G.......L.S..}
....Zv.........^.Q..o......"..G..(..e.E._cA..5h......x...WyFhl...W.....Z..^. ......=
.)...U.7..._...A:.v...|.An.HH..}.[K>..C...%H}.n..D(.V.....h..%..n
f.....f...,tzvq{I.>yg..,.^|.4|Qae<.....,....i..Qi.M...o....
!..o.....Q.0..{....[...~...!Q.N........."8[.A.g..=......G{F._..LNw.;.........J.,.(..e..[.
...c...Q]/E.9....e.2|..).....|
..Y2.5q..t.._ZFi:..)*,.........q"..~..i.....!..E....K+.SK....>D{6..X.B.0..U....Knn......H
FS.z.V...n.L....I..h.u.W.Yv...l.+
.0CD........9...V..Q@& .....Fv.T.q[........gDl.....!H..H...T.S.%.U'D+t.@
Z...2...{1!.Ue..y.|.#...x..A.*....{.3.dB.#..*...'...U/.?../.C...OJ.K..lo.4.j.yx.r2LU....
.P.^Y..8Na.u...(`.
...m....9..b.}C...
Z{GoU...e..&A..7.RN....../..u3W?....3.1..e..........-
=..<.L....I[..].S9.m..J..b.7~..{.a.B.%j.M...:M..b'...;.....o.J....$i.0wo..._e.........{..
.dq..D..7^G...gA..B.....19...'/.c*u.T.b..i... ....{...t
i.6d....l........3...m.u..m...
.....x.....})...v..I.M.^.#t.....0qD.....N.....o./D.....N..$0..rSHsc.{v>y...].~"...X.t.&.z
|cm.:m..D.~..Q.........b.....xm+.C+e/DP.8O....Y.*S.....LS...2...%.F.....T..tK0.t...A#.z..
...?.#.J.X....jdQ..[.........%S(.f.R...k(g....e.eI........|T....y.....|..........H..d).N.
...>...E.C)...].z.lK....w...t.
.;..*....,.....V.u.iCQ...o.#fK..;..o+....`...........c...........f...C.....`u=.C....MQ..
.L.C{.R..r6.E.jJ....FmH...N).[A.......~K.!...T,.@....`...V..1._.........
.d.mD.r.J..o..m}.R2.<.9......u.*Y....`j?.7.i.%.-
.q...(......0l.}.......h......e.`P1.:.i......../.0.O1....g..M-
..6.`.#T6...'.....20kD......./.#....o.s.`..k8...=m....uZ.J
.......*y.K.......yO......yq~..)..0N4wFO..r&q-
p..:......3._.........V..r.lph...~.B..}..M._....4....W.!..X.7......h.#f..2.....X.L_..Y0&.
.D........G............*O..3..i..y%.a?.,&F.v:....G.c..........u....:...D..g........#..c.
.oxe....?......*.W,.....S.........oX.....@......!......3.Z...............>t.7.....6>s....
..ei4g}.......j~*=.DnPq.;hX/......'...V'.....xS....k..1[....HS>+.=03...x..M...x.fxF.d/...
..F....,.I...K ....qy>.....'........O+.....K.U.K.$...9{...-....
x......).]&...5E.:.>(..FM.H...
H.... cDe..Y7..U..b[.-,.kj4.Fg....r..f
That insecure HTTP Basic Authentication string is still in there, but nobody’s ever going to decode it because
they would have to decrypt the SSL-encrypted connection beforehand, and that would take a huge amount of
computing power to do.
Nobody will be able to tell anything other than the name of the site you connected to (which has to be sent
unencrypted due to the way the HTTPS protocol works).
The basic rule is: Anything that you do not want to be readable by someone between you and the server, use an
SSL (https) connection.](https://image.slidesharecdn.com/webservers-howtheywork-130224010854-phpapp01/85/Web-Servers-How-They-Work-17-320.jpg)
