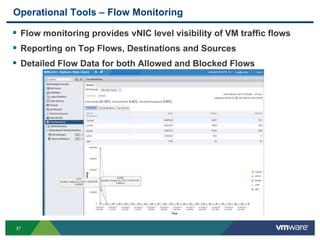
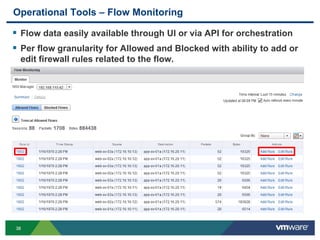
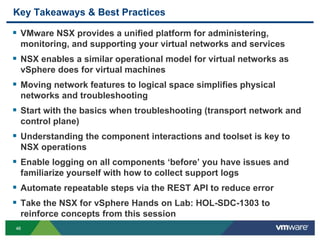
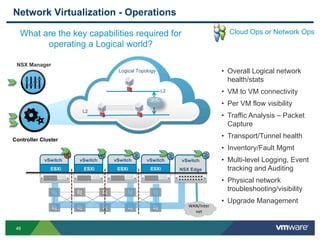
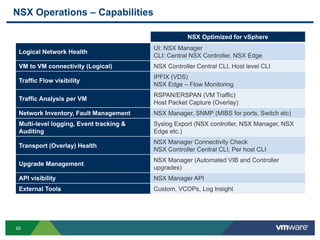
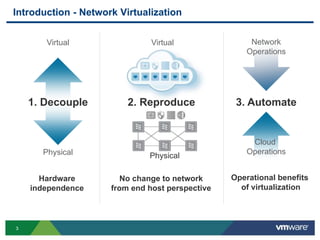
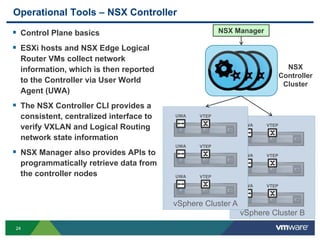
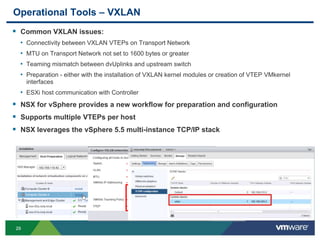
The document outlines operational best practices for using NSX in VMware environments, focusing on network virtualization, operational impacts, and available tools. It discusses the benefits of decoupling physical and virtual networks, troubleshooting strategies, and automation capabilities through NSX components. Additionally, the document details various operational tools for monitoring, troubleshooting, and maintaining network health within VMware environments.
![3434
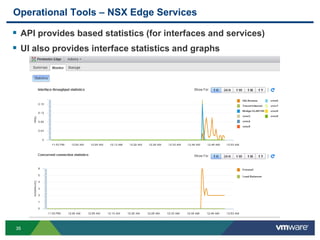
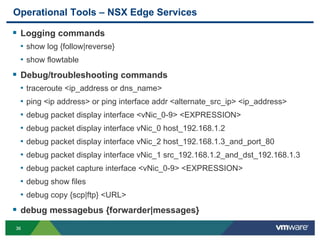
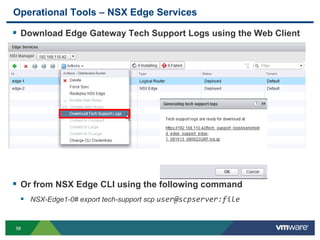
Operational Tools – NSX Edge Services
NSX Edge VM CLIs
• NSX Edge provides a familiar CLI command
set for troubleshooting network services
• Documented in a dedicated CLI guide
Sample Configuration Commands
• show configuration {ospf|bgp|isis|static-routing}
• show configuration {firewall|nat|dhcp|dns}
• show configuration {loadbalancer|ipec|sslvpn-plus}
Sample Status Commands
• show interface [IFNAME]
• show firewall
• show ip {route|ospf|bgp|forwarding}
• show arp
• show system {cpu|memory|network-stats|storage|uptime}
• show service {dhcp|dns|highavailability|ipsec|loadbalancer|sslvpn-plus}](https://image.slidesharecdn.com/net5790formattedv2-140613124845-phpapp02/85/VMworld-2013-Operational-Best-Practices-for-NSX-in-VMware-Environments-34-320.jpg)