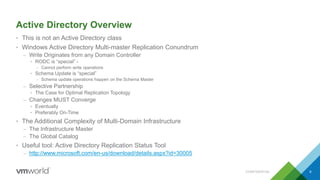
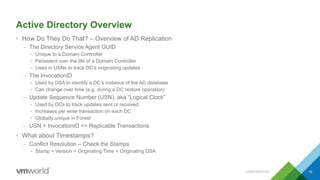
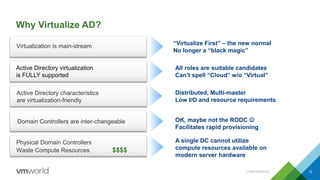
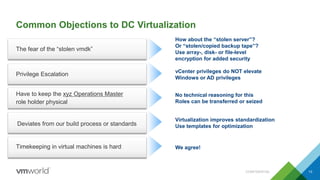
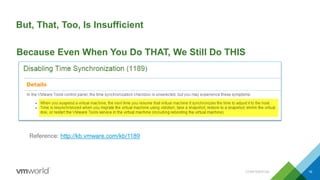
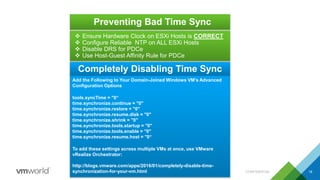
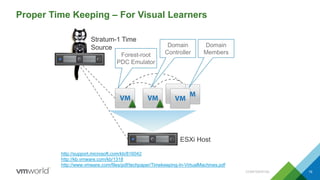
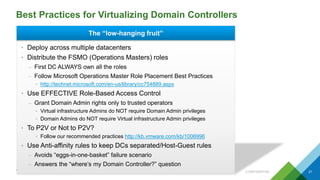
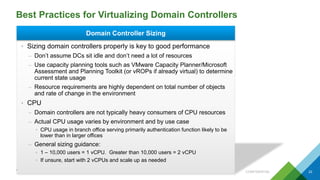
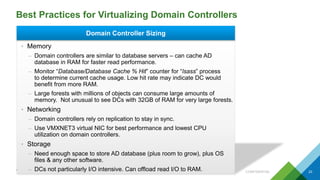
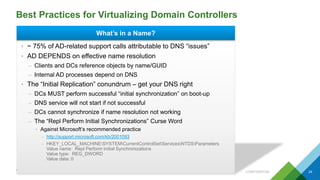
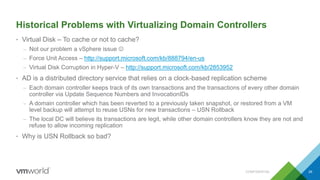
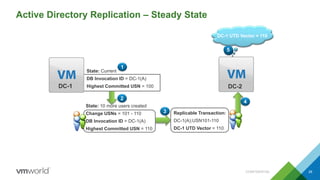
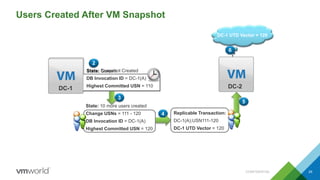
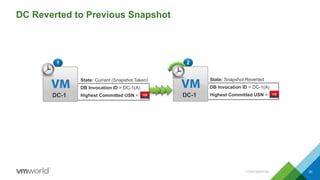
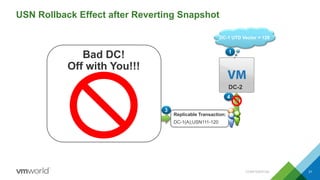
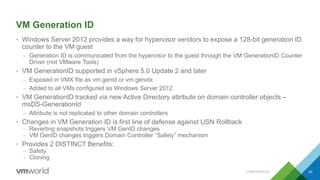
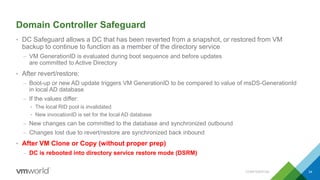
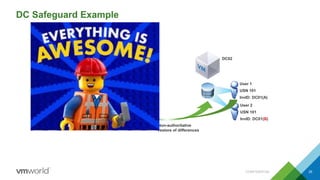
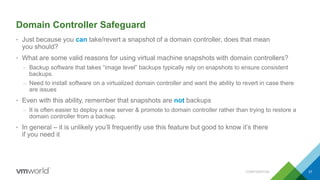
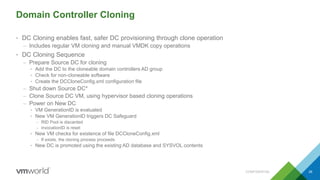
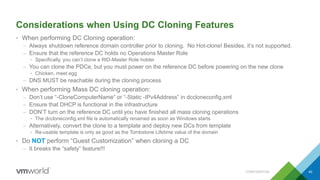
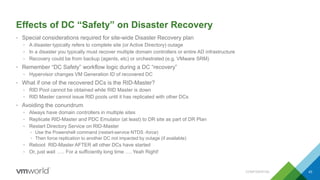
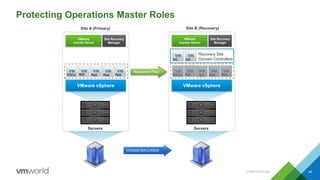
Virtualizing Active Directory domain controllers provides benefits like increased availability, scalability, and manageability. However, there are some technical challenges to address like ensuring proper time synchronization. This presentation provides best practices for virtualizing domain controllers including using host-guest affinity rules, disabling time synchronization settings, and ensuring the ESXi host clock is correct. It also introduces new "safety" features in Windows Server 2012 like VM GenerationID that help address issues from restoring or reverting snapshots like USN rollback.