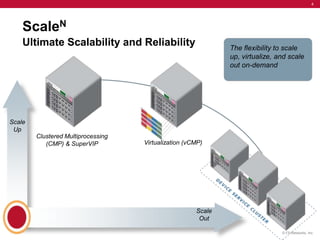
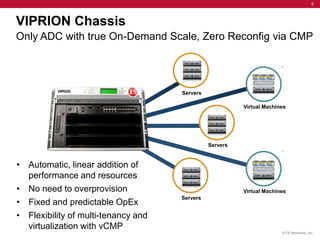
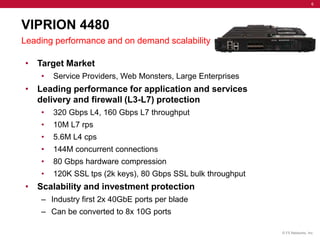
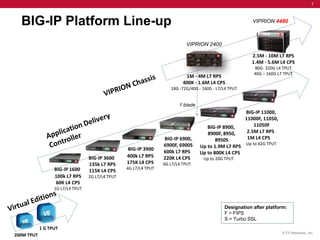
F5 Networks announced the new Viprion 4480 chassis and 4300 blade, delivering exceptional performance with 320 Gbps L4 throughput and industry-first 40 GbE ports. Targeting service providers and large enterprises, the Viprion platform offers scalable solutions for application delivery and advanced firewall protection. With features such as clustered multiprocessing and virtualization, it provides flexible, on-demand scalability without the need for overprovisioning.