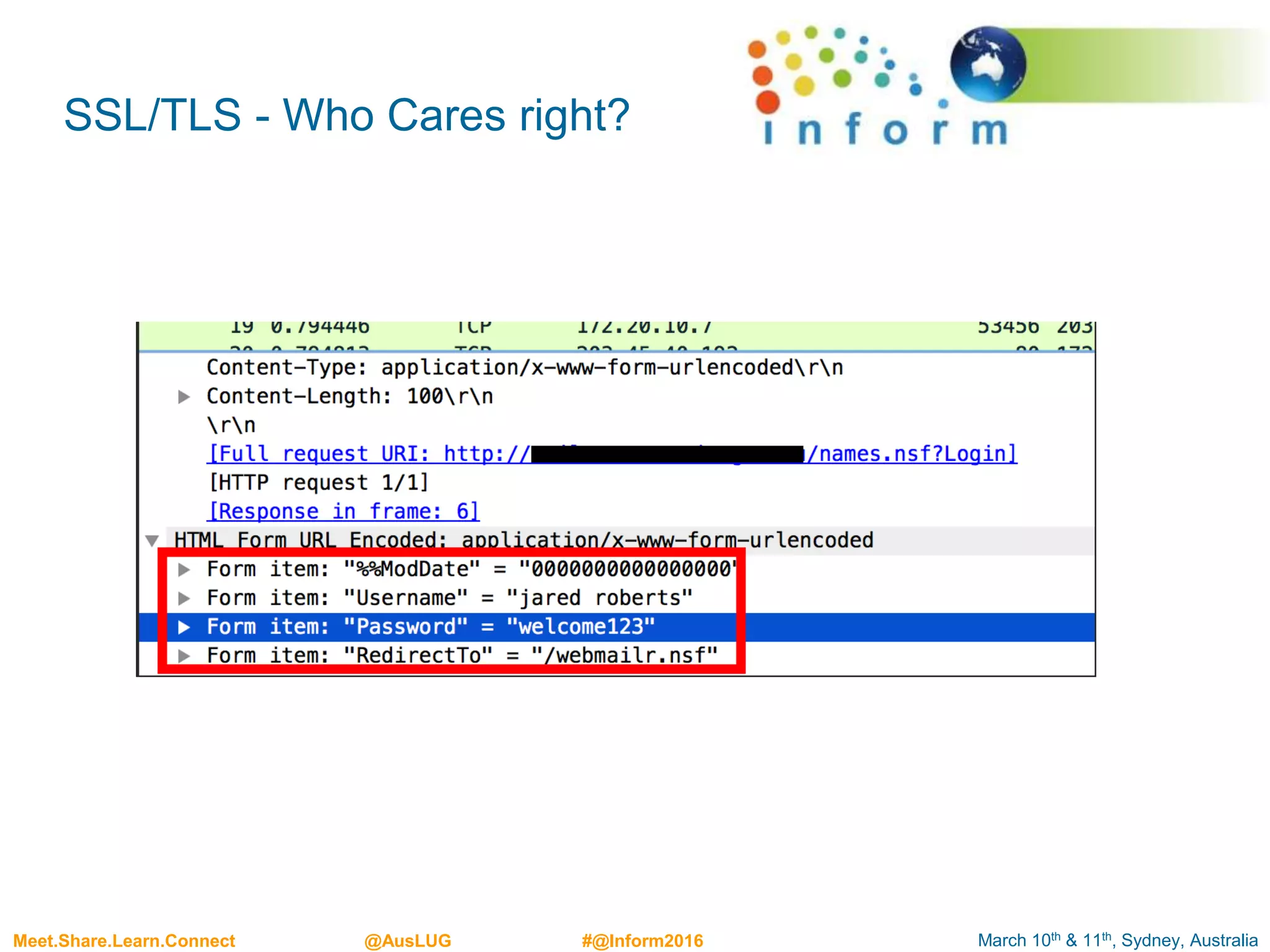
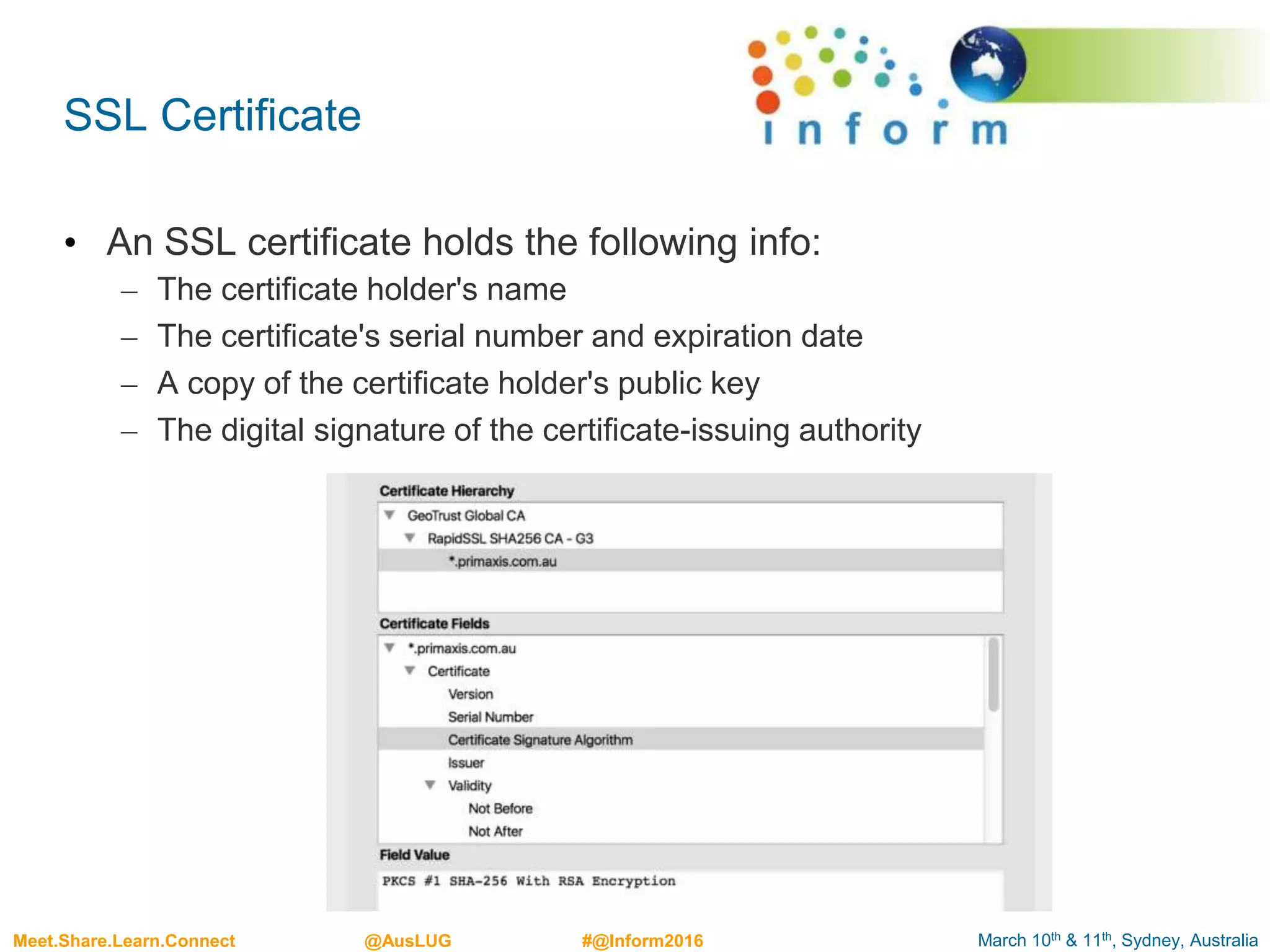
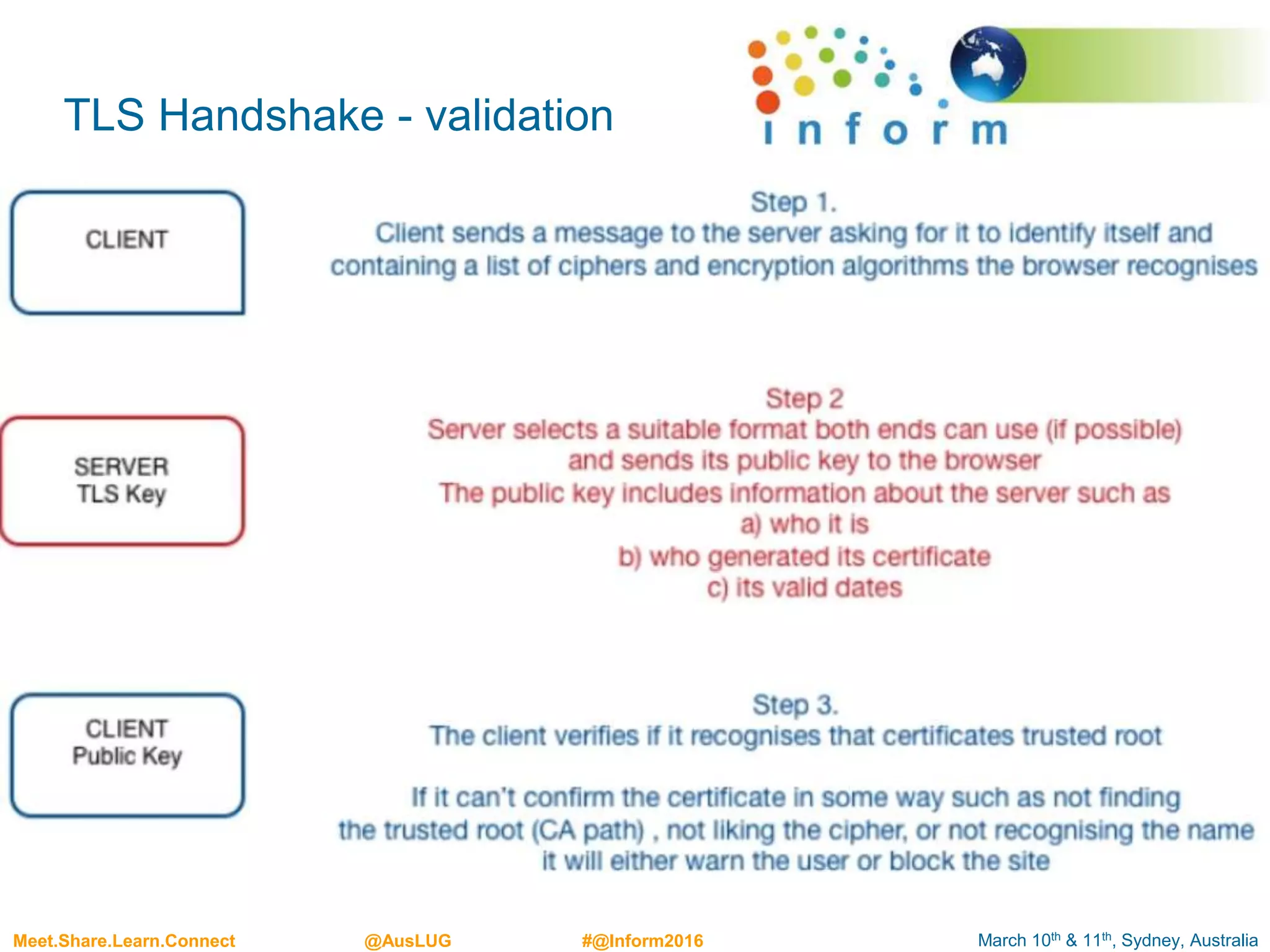
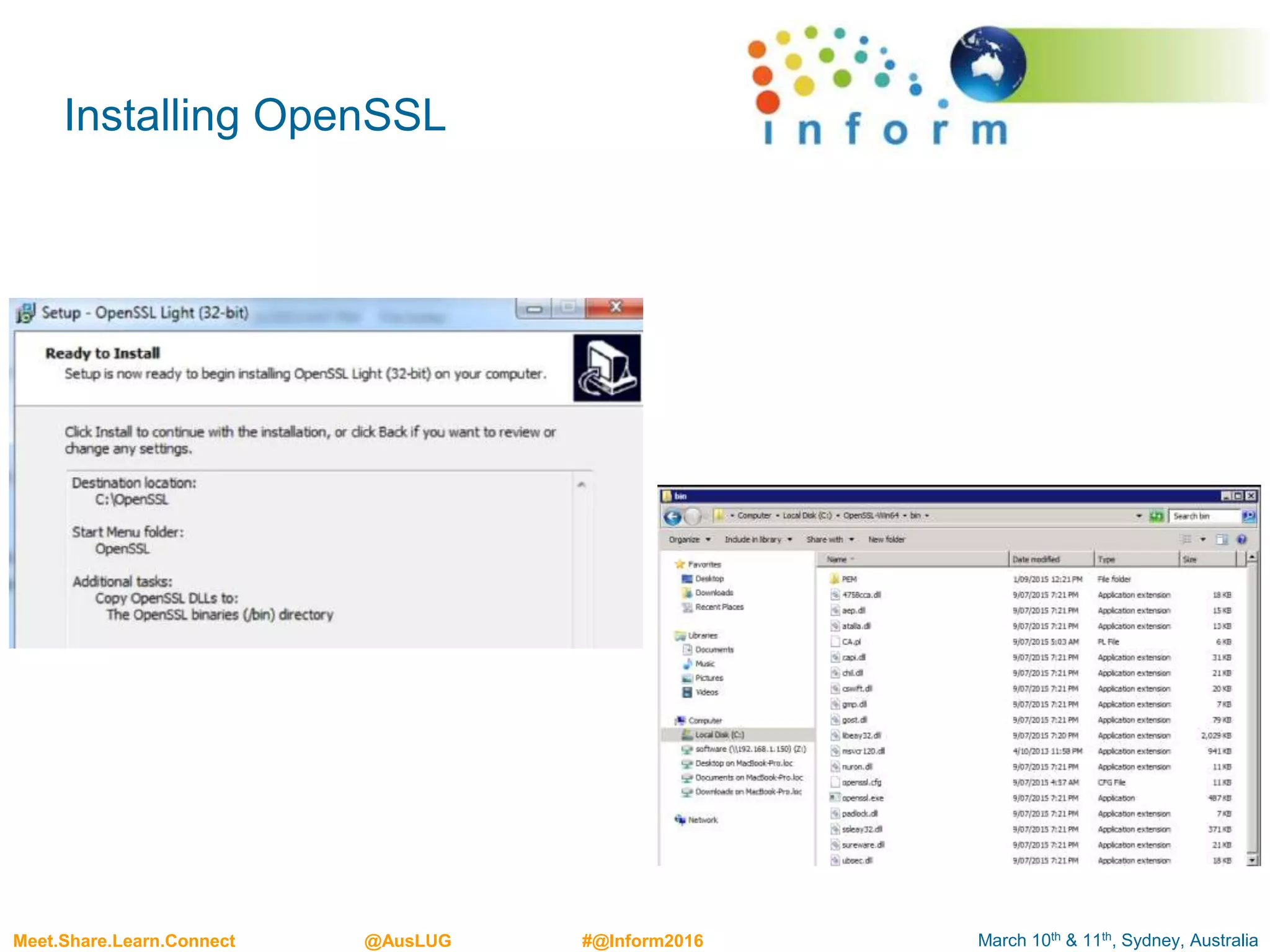
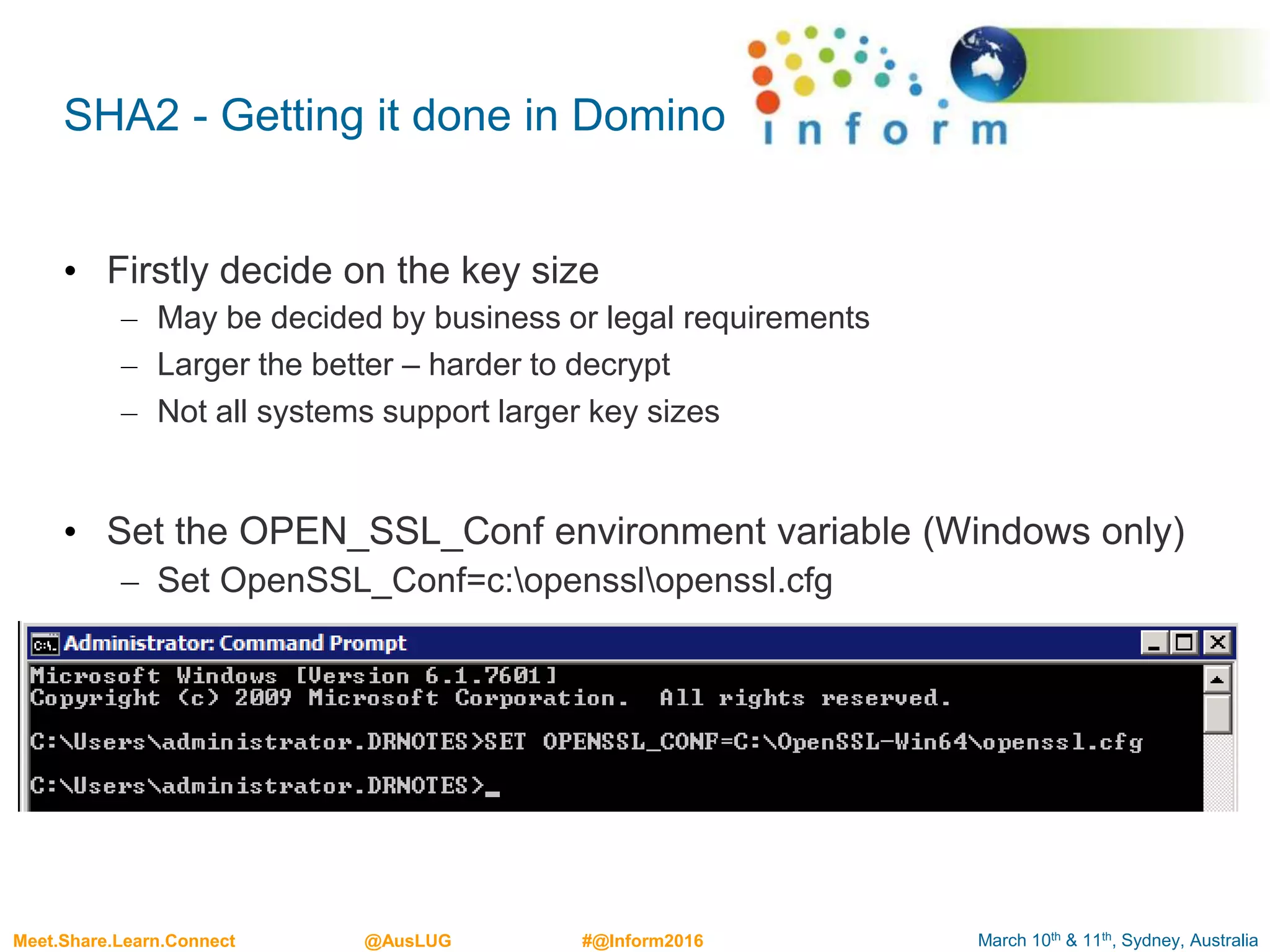
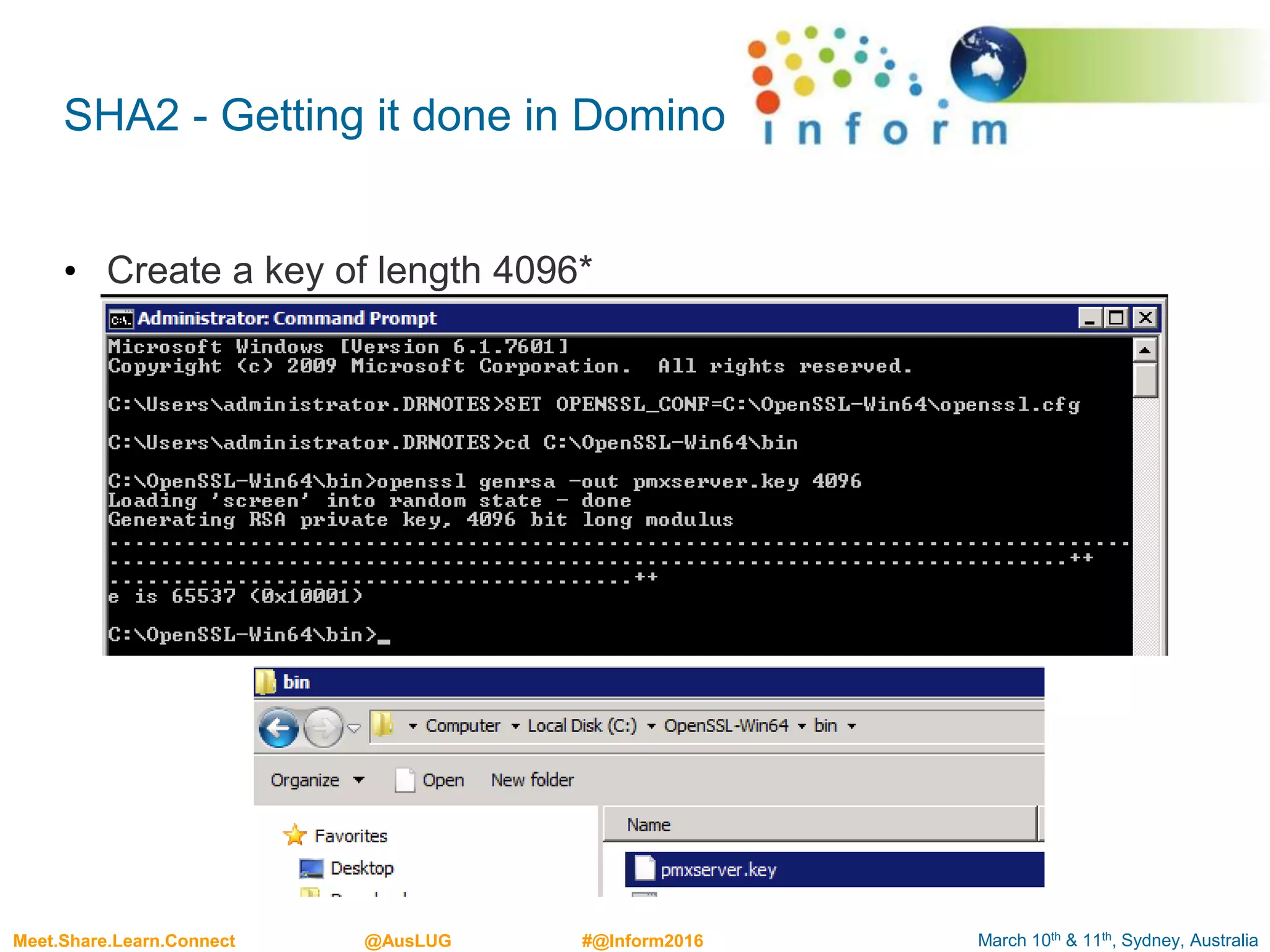
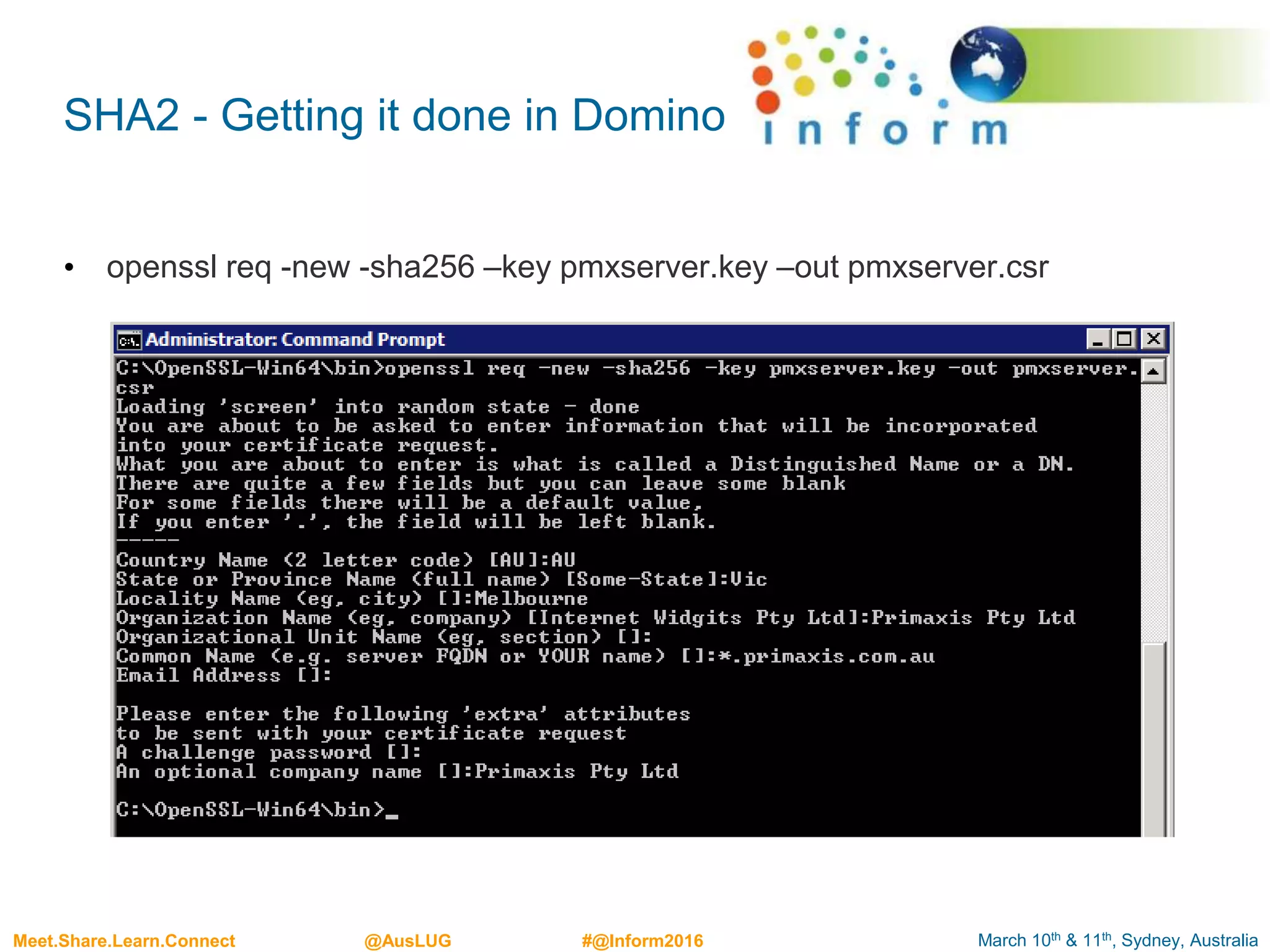
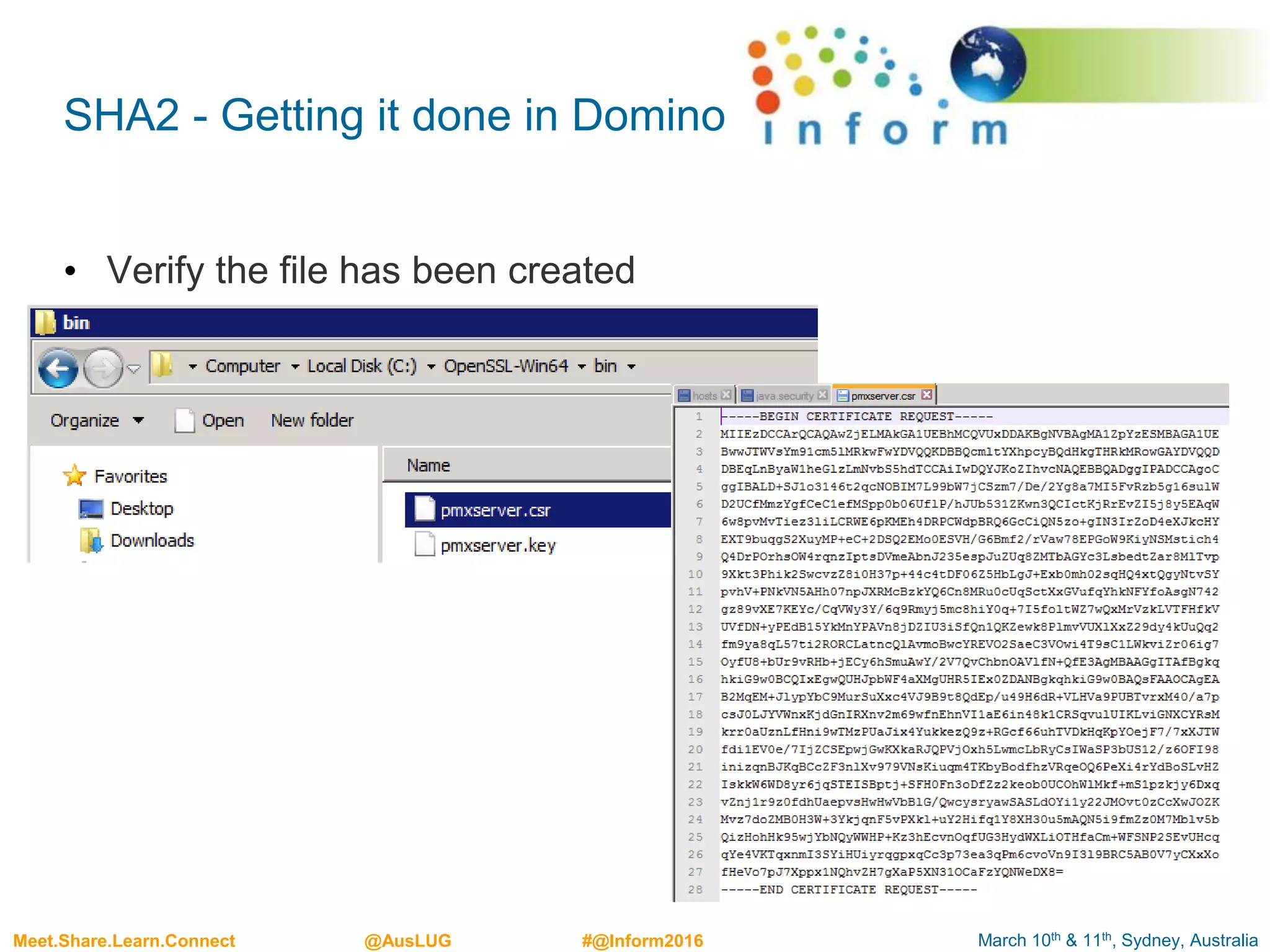
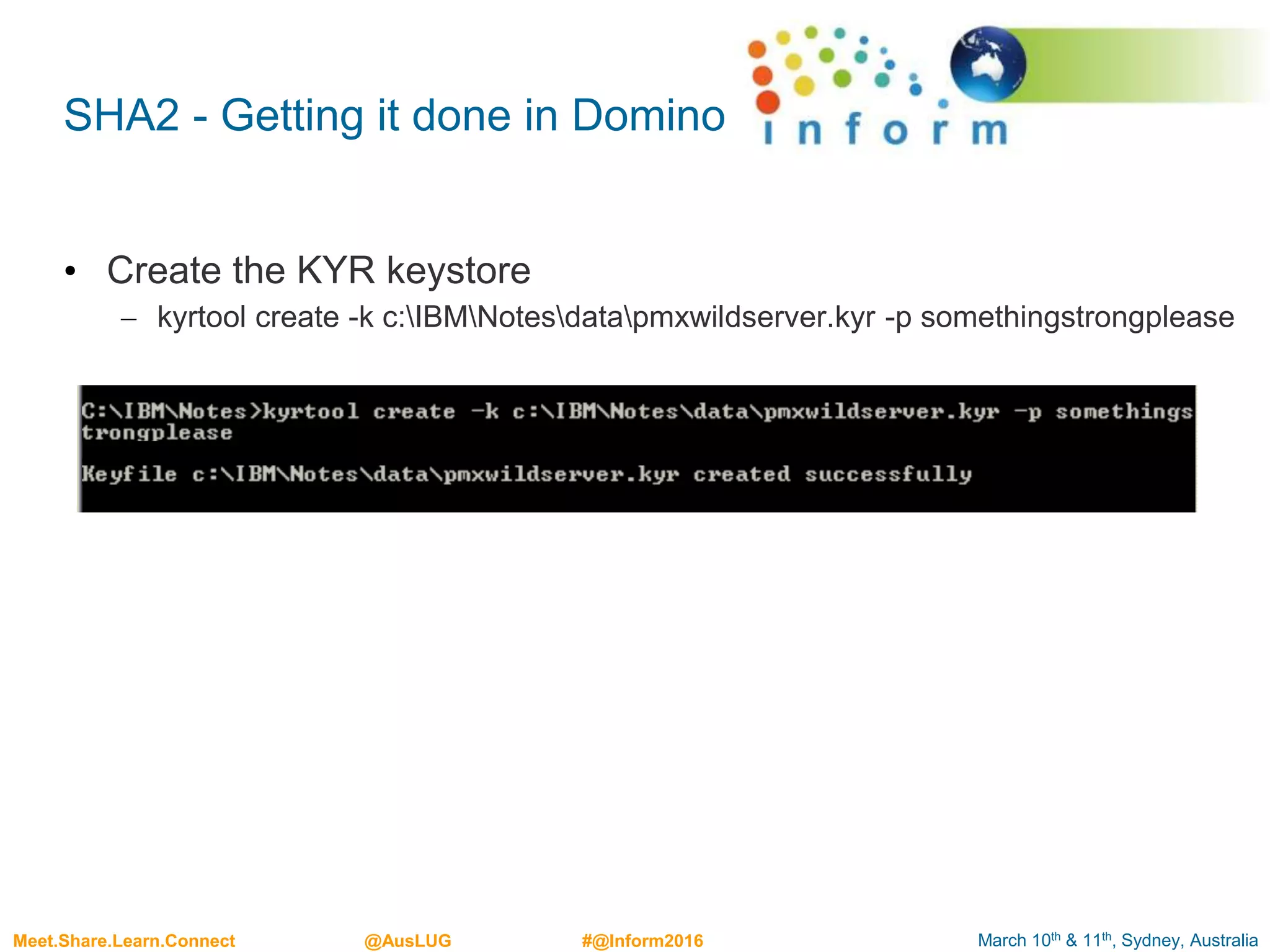
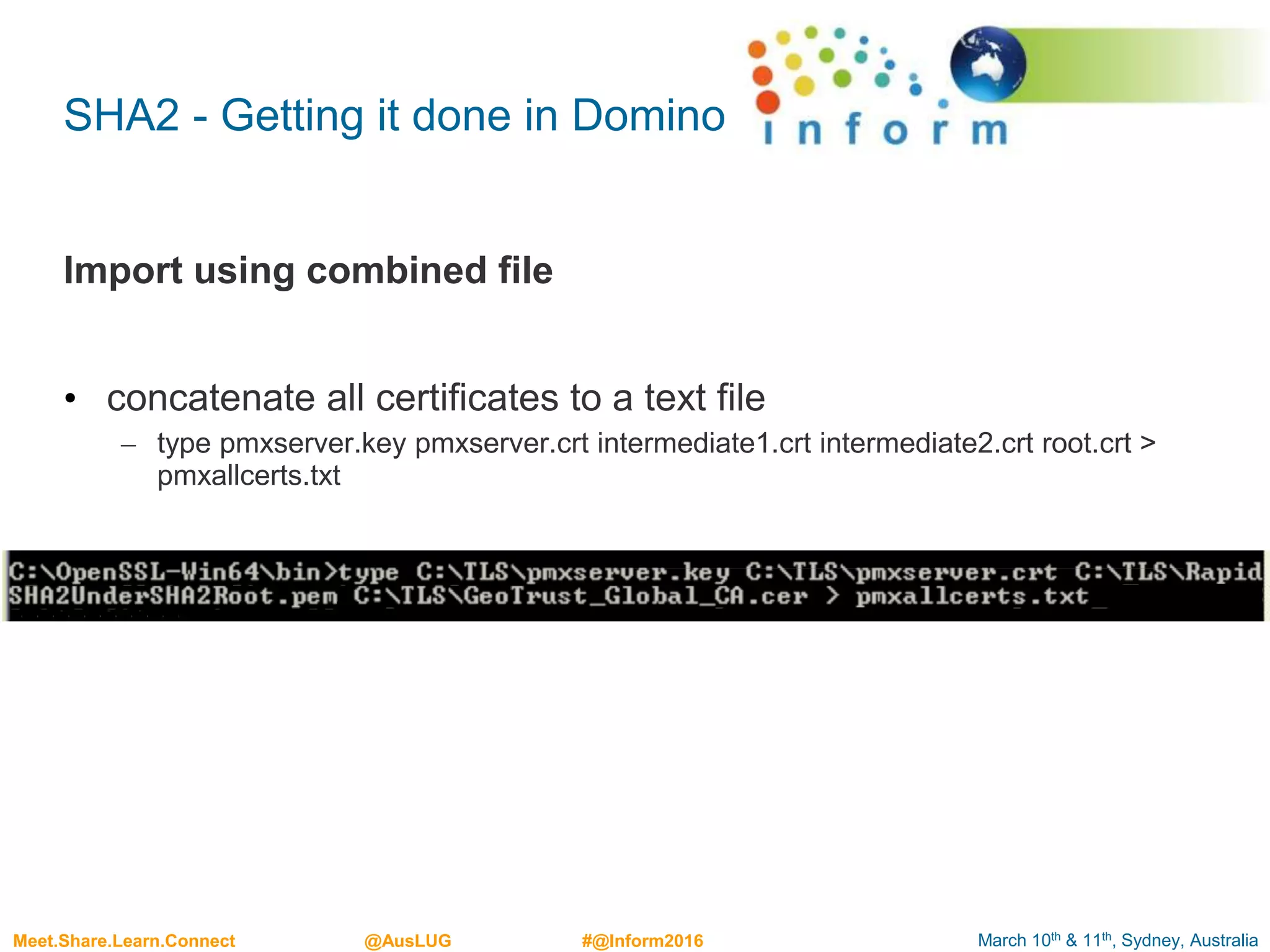
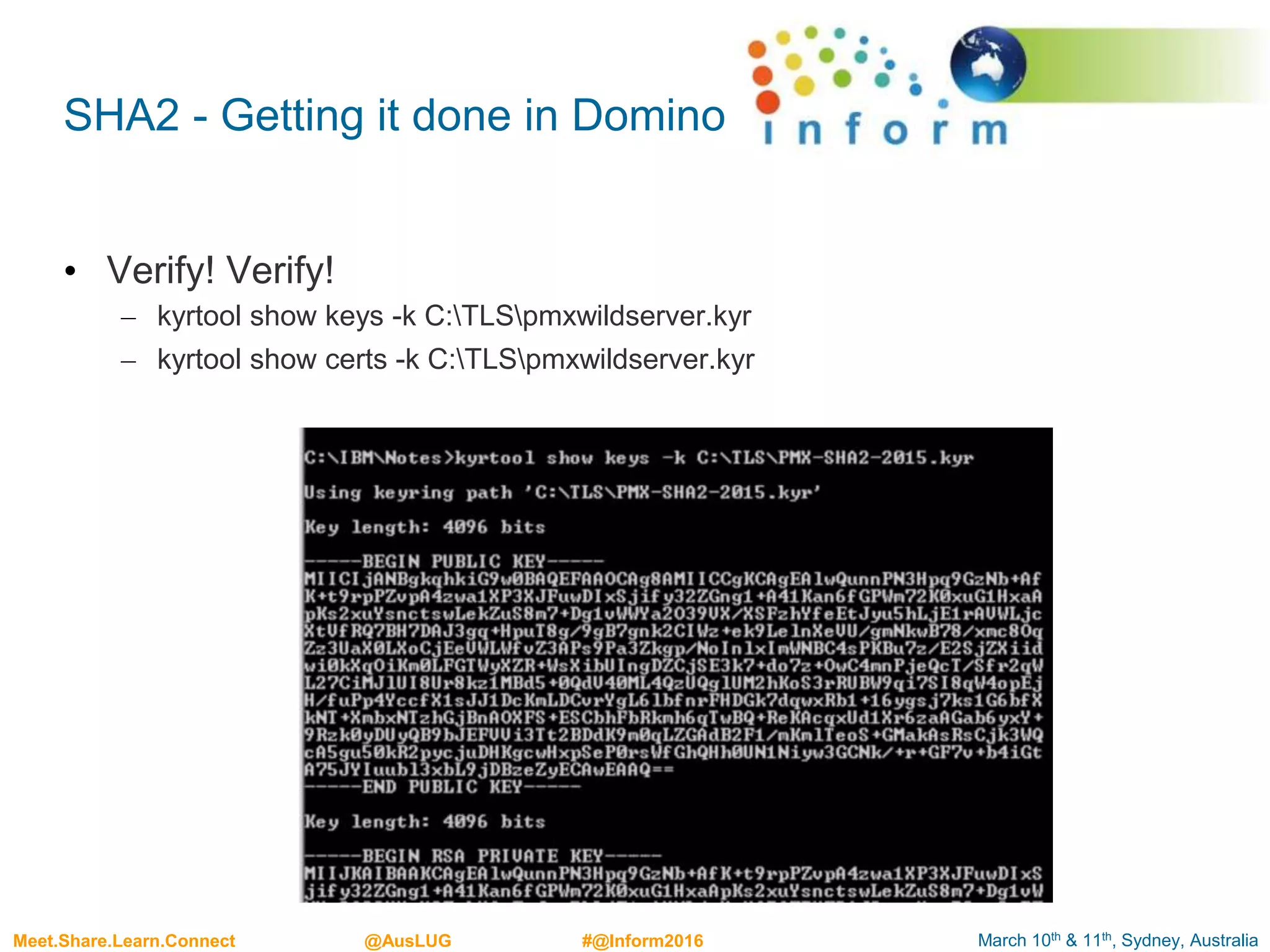
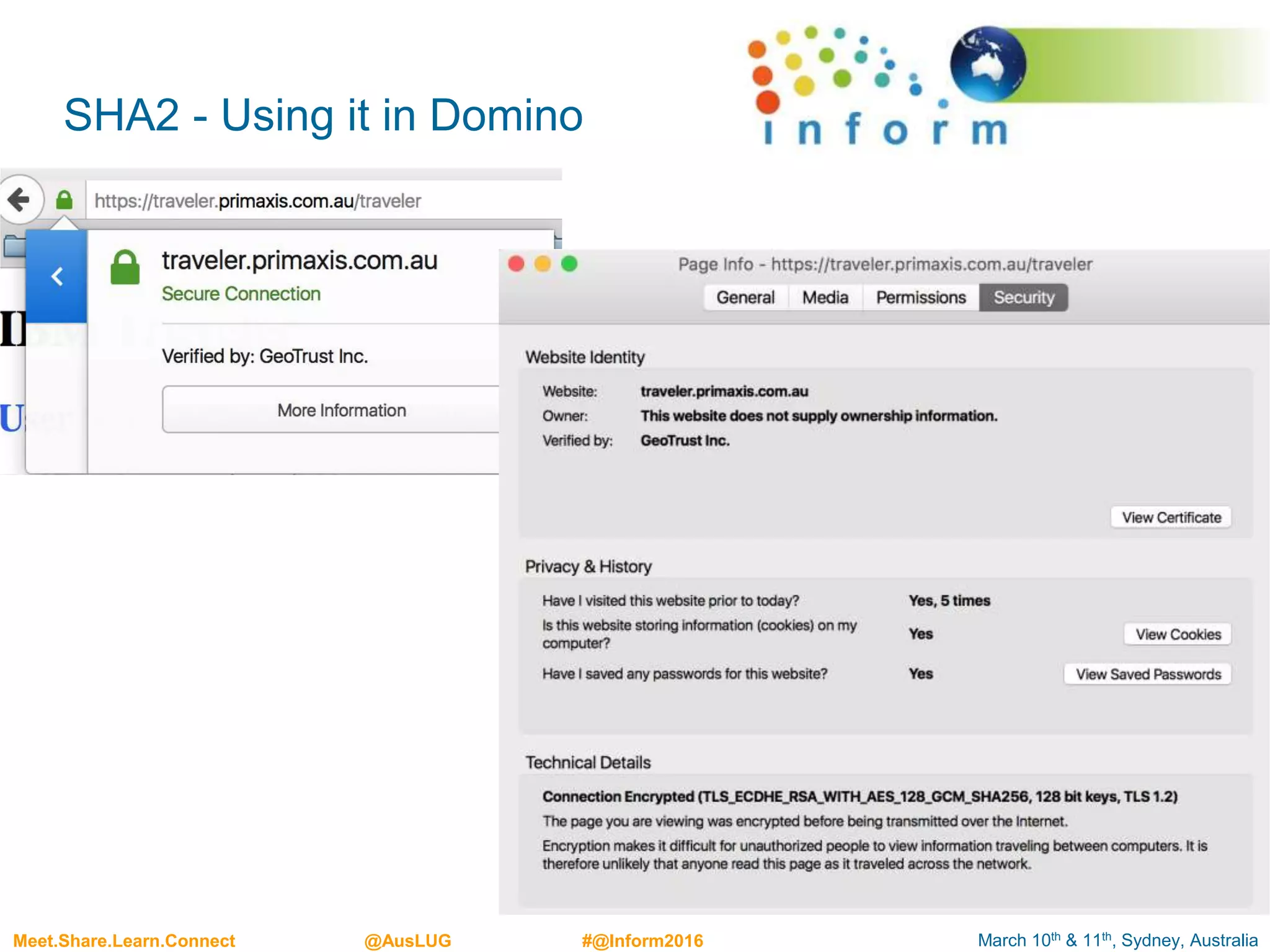
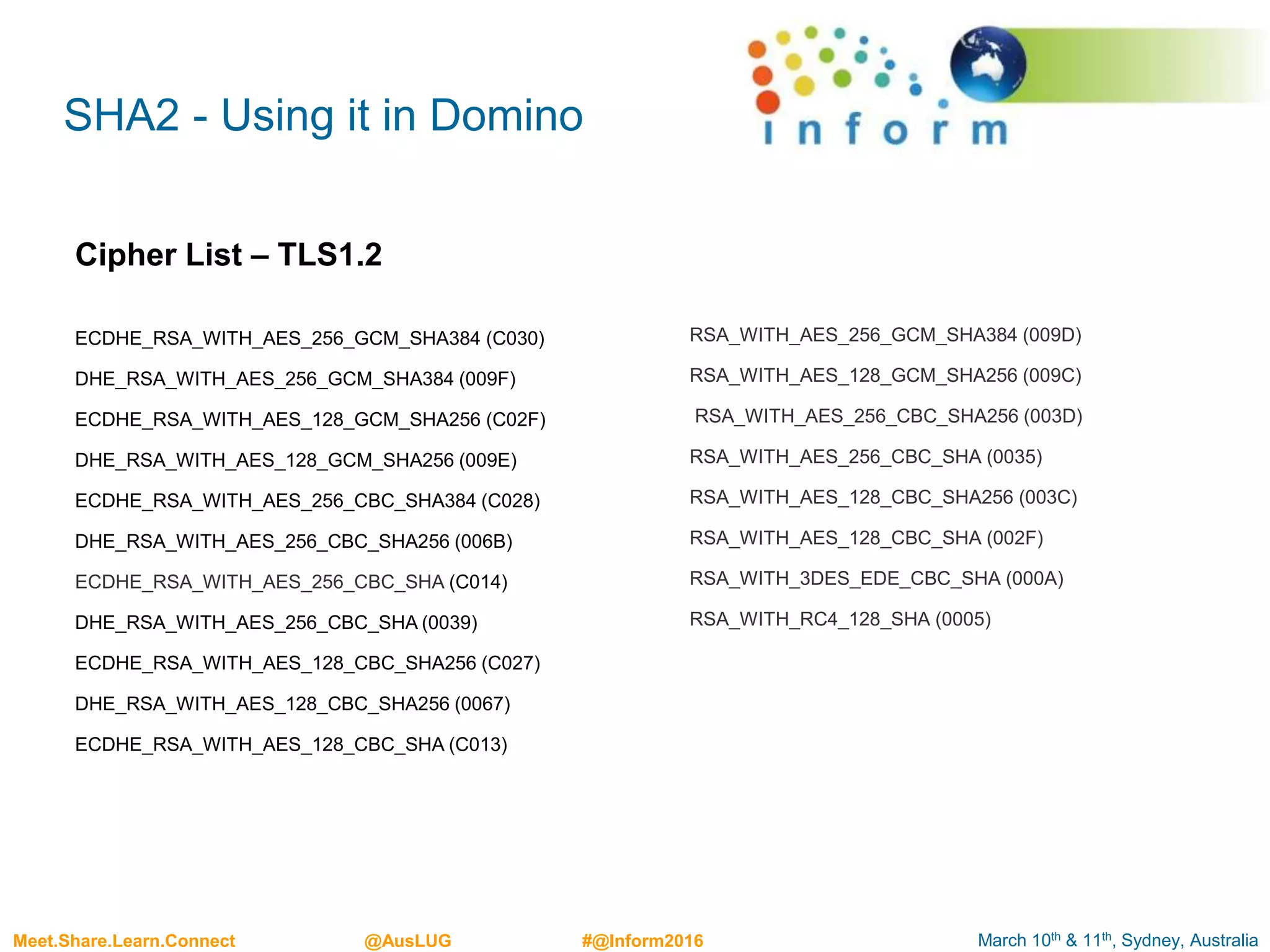
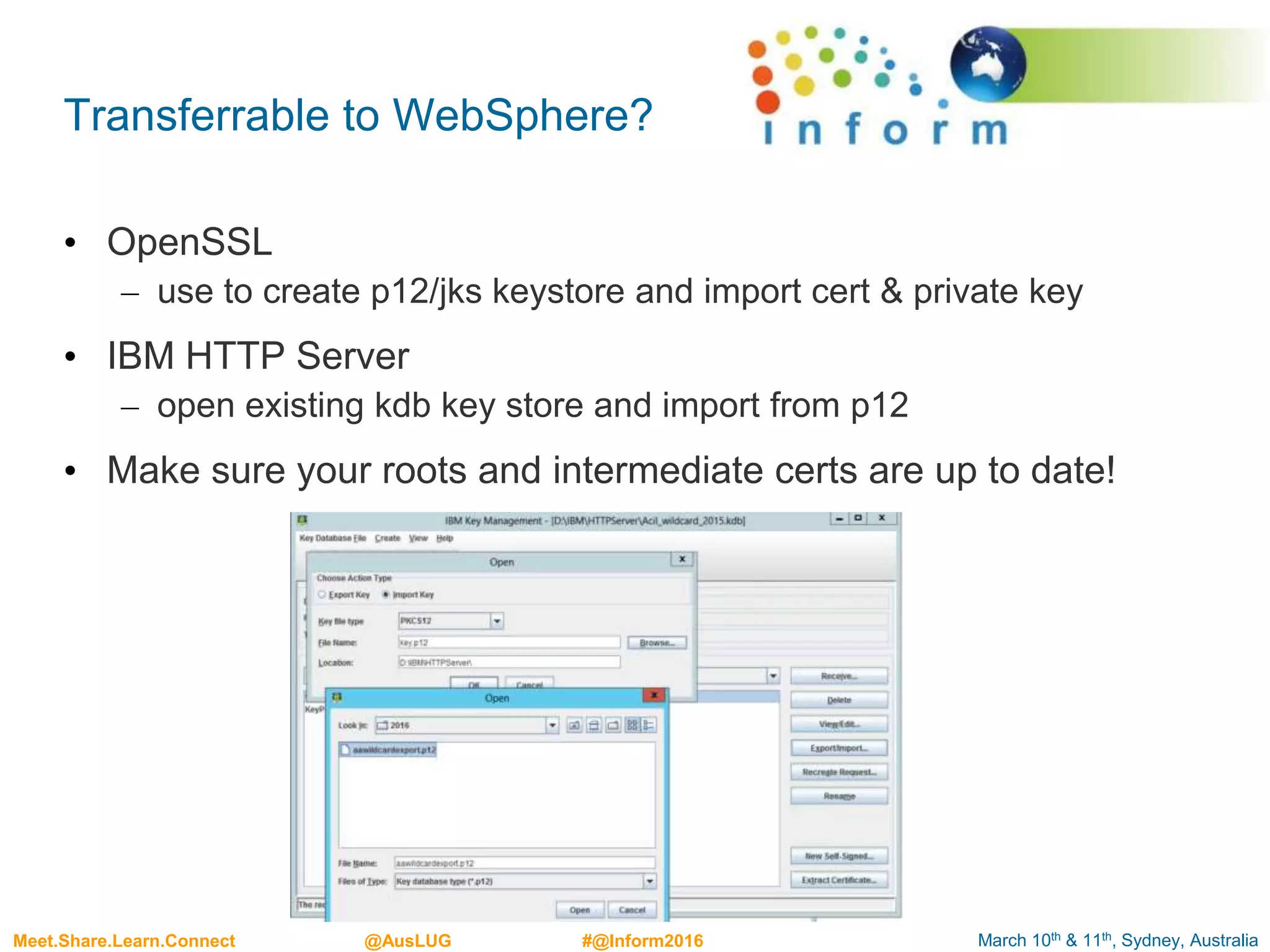
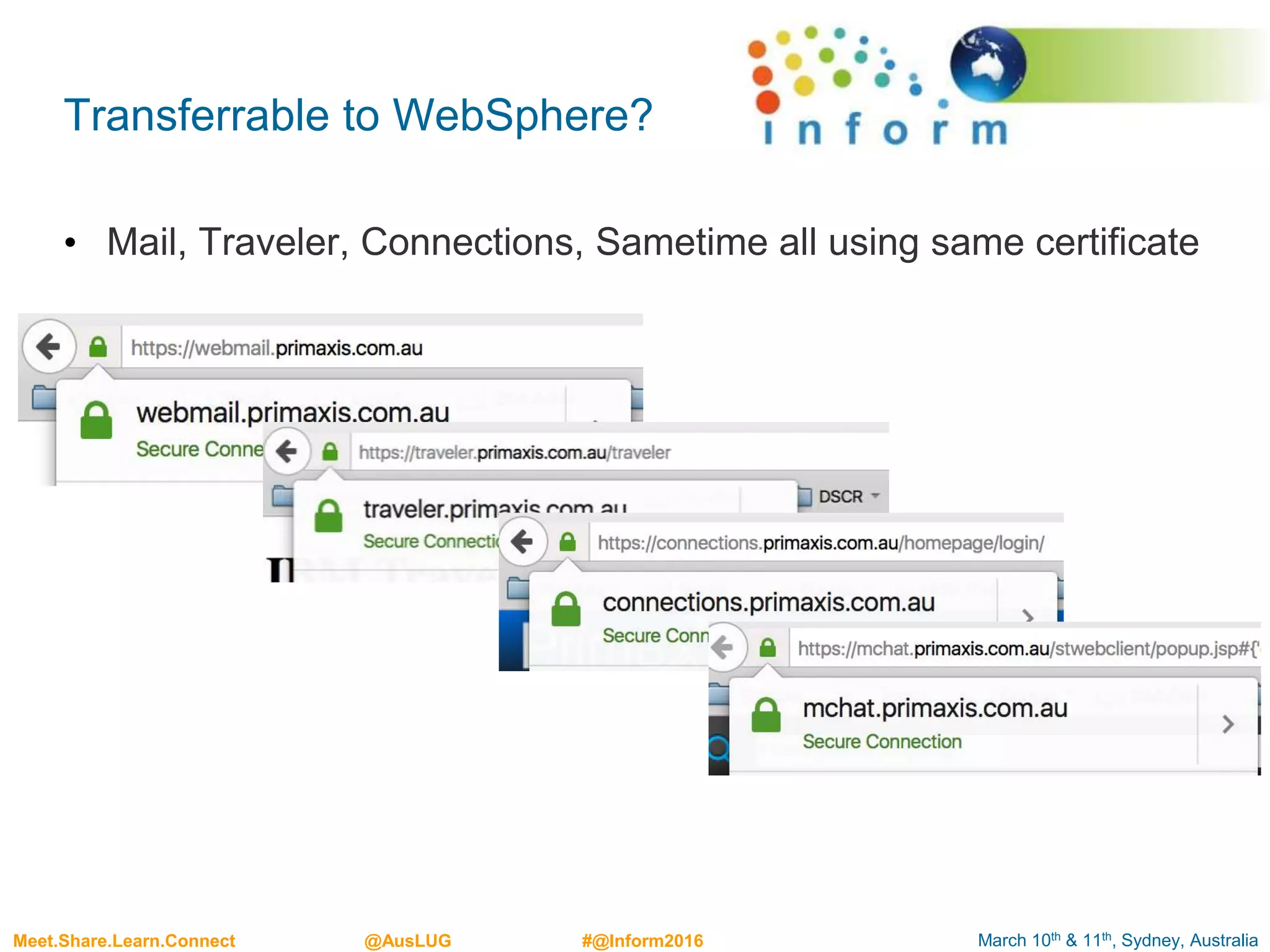
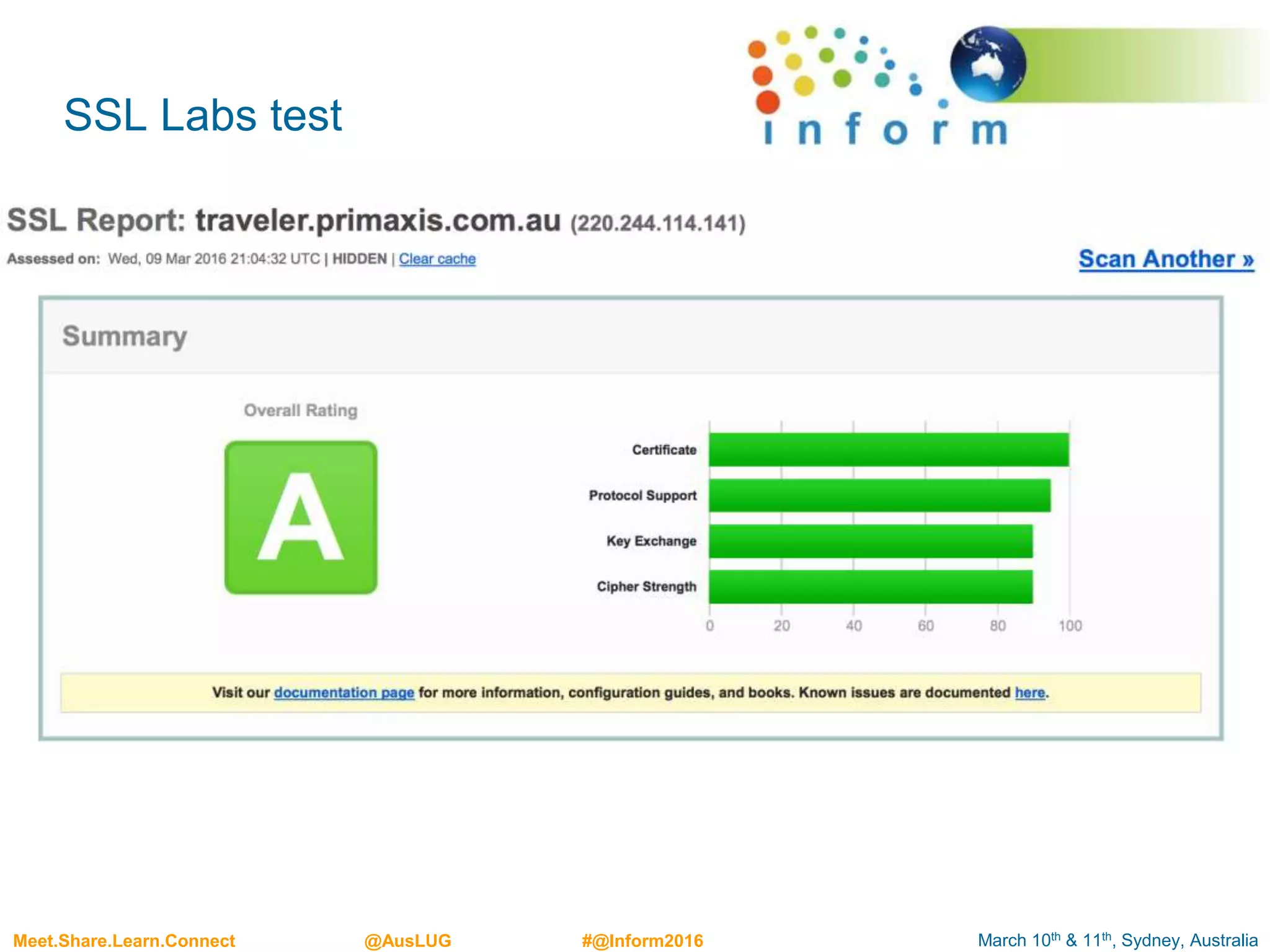
This document outlines best practices for implementing Transport Layer Security (TLS) 1.2 in IBM Domino, emphasizing the importance of encryption in securing data transmission. It discusses the evolution from SSL to TLS, the vulnerabilities associated with older protocols, and provides a detailed guide on creating and managing SSL certificates and key stores in Domino. The presentation includes practical steps for generating certificates and highlights tools needed for successful implementation.