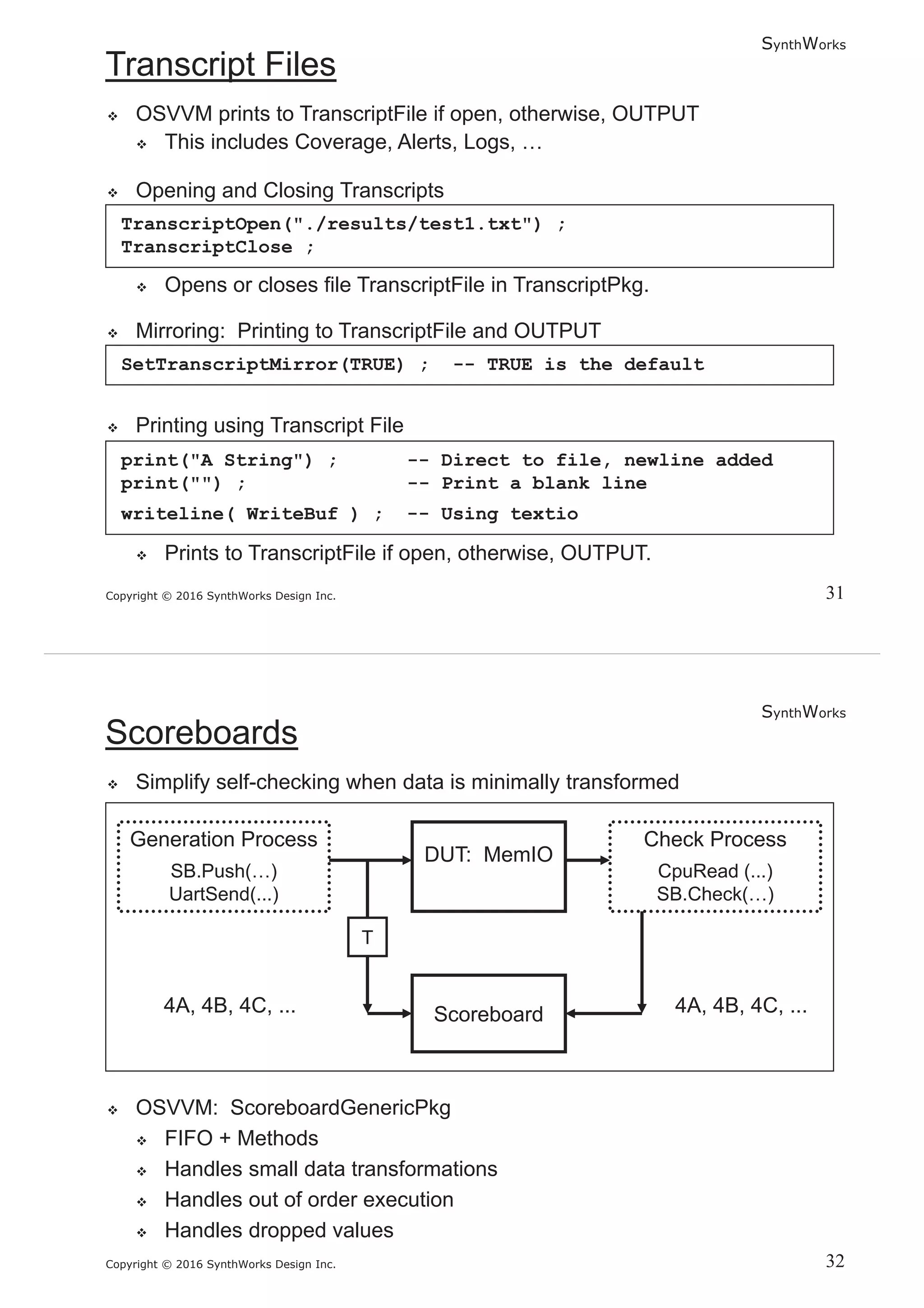
This document describes a presentation by Martin Rønne of MR Logic on SynthWorks. It provides copyright information and notes that the material is from SynthWorks' Advanced VHDL Testbenches and Verification class. It also includes contact information for Jim Lewis, President of SynthWorks Design Inc.