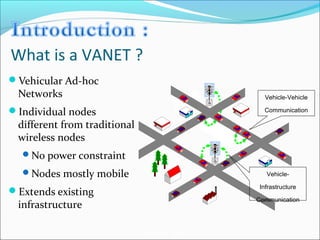
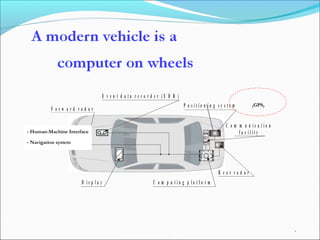
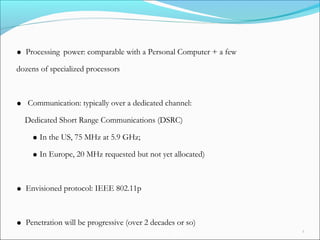
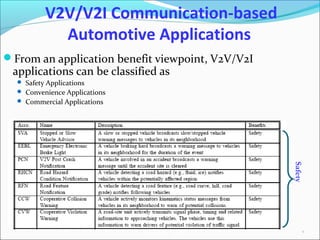
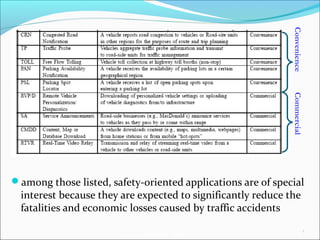
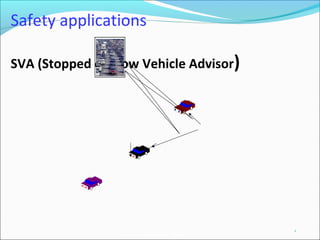
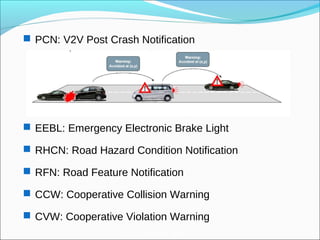
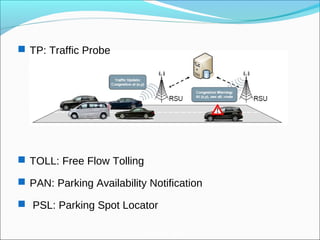
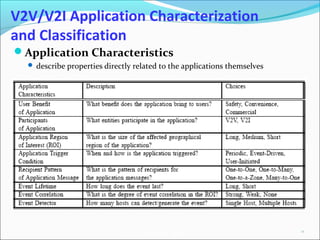
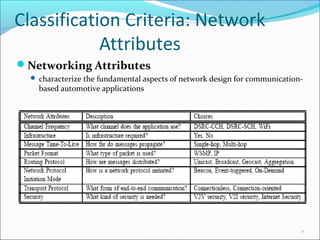
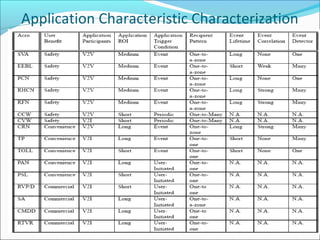
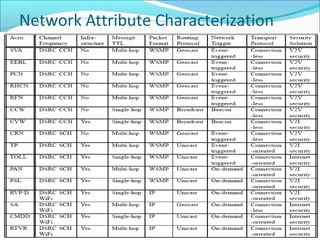
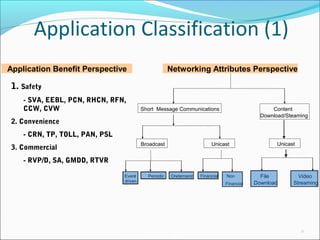
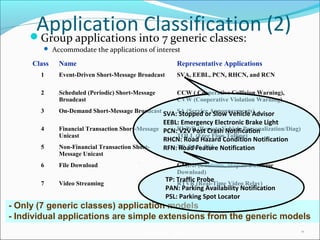
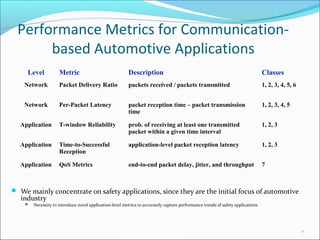
The document discusses vehicular ad-hoc networks (VANETs) and their applications, particularly focusing on vehicle-to-vehicle (V2V) and vehicle-to-infrastructure (V2I) communications. It classifies applications into safety, convenience, and commercial categories, highlighting their impact on reducing traffic accidents and enhancing vehicular communication efficiency. Additionally, it addresses the challenges and future directions for improving traffic management using these communication technologies.