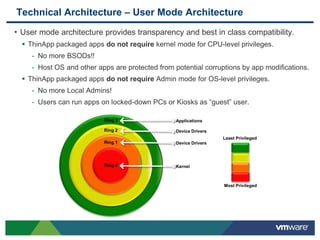
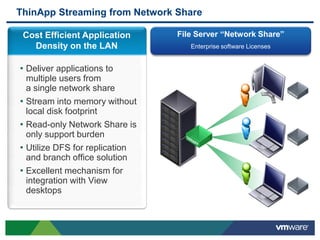
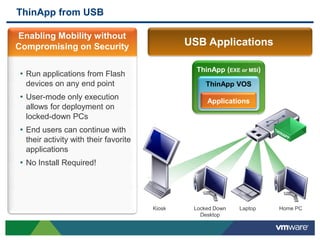
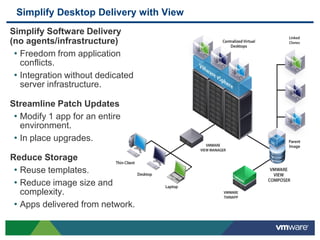
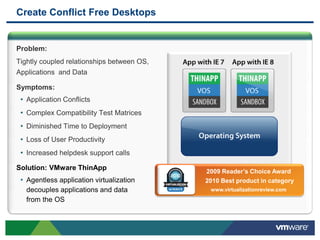
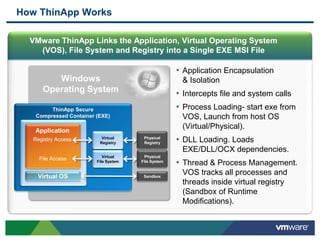
VMware ThinApp is an agentless application virtualization solution that allows any Windows application to be run virtually from various devices without installing it locally or making changes to the underlying operating system. It uses a single executable or MSI file to encapsulate and isolate applications. ThinApp packages can be seamlessly deployed on any existing management framework and streamed from a file server to multiple users without additional infrastructure. It ensures security by executing applications in user-mode and sandboxing any registry or file system changes made by the application.


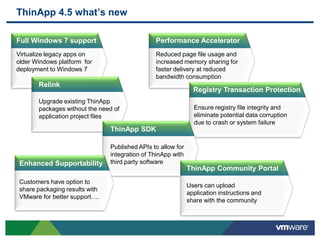
![Seamless Package Upgrades with Relink Tool
• Upgrades ThinApp runtime within existing
packages.
Makes older ThinApp packages Win 7
compatible.
• Does NOT require original project rebuild.
• Preserves original ThinApp packages as
.BAK files.
Ensure disk space is available!
• Supports wildcards and recursion.
• Easy command line & scripting potential.
Syntax:
relink [-Recursive] <path_to_package> *.exe *.dat *.msi
Examples: relink -recursive c:Thinapps*.exe
relink AdobeReader.exe](https://image.slidesharecdn.com/vmwarethinapp4-5-100609090753-phpapp01/85/VMware-ThinApp-4-5-8-320.jpg)