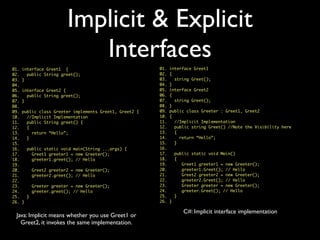
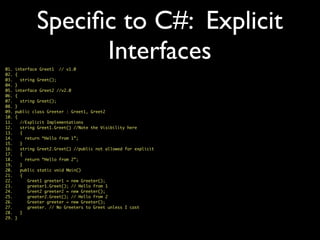
This document provides an overview comparison of key concepts between Java and C# programming languages. It covers differences in language syntax, frameworks, and platforms. Some key differences highlighted include C# using the .NET framework instead of Java's JVM, C# properties instead of getter/setter methods, and C# supporting structs as value types while Java only supports classes as reference types. The document also provides examples of implicit and explicit interface implementation in both languages.


![Language Comparison
Java C#
Program Entry Point
Namespace
Including Classes
Inheritance
Overriding
Accessing Parent Ctor
Accessing Parent Method
Visibility
main(String ...args)
Main() or
Main(string [] args)
package namespace
import using
class (extends),
interface (implements)
class and interface (:)
virtual by default
non-virtual by default
use virtual keyword
super(...) : base(...)
super.method(...) base.Method(...)
private, package,
protected, public
private, protected, internal,
internal protected, public](https://image.slidesharecdn.com/understandingcforjava-130820002527-phpapp01/85/Understanding-c-for-java-4-320.jpg)
![Language Comparison
Java C#
Method Parameters
Variable Arguments
Exceptions
ADT Meta Type
Meta Information
Static class
Properties
Non-Deterministic Object
Cleanup
Object References are
passed by Value only
Object reference are passed
by Value(default), ref & out
method(type... args) Method(params type[] args)
Checked and Unchecked
(enforced by javac, not by JIT
compiler)
All Unchecked Exceptions
Class
Class klass = X.class;
Type
Type type = typeof(X);
@Annotation [Attribute]
Simulated by private Ctor
and static methods
Static class and ctor with
static methods
getProperty(),
setProperty()
Property { get; set; }
compiler generated
get_Property() and
set_Property() methods
finalize() destructor ~X()](https://image.slidesharecdn.com/understandingcforjava-130820002527-phpapp01/85/Understanding-c-for-java-6-320.jpg)
![Language Comparison
Java C#
Deterministic Object Cleanup
Generics
Class Loading
synchronized block
synchronized method
Thread Local Storage
Smallest Deployment Unit
Signing
AutoCloseable or Closeable
try-with-resources (Java 7)
try ( ... ) { ... }
IDisposable
using ( ... ) { ... }
<T>, <T extends Type>, <?>
Type Erasure
<T>, where T : type, new()
Preserves Type Info
Class.forName(“fqn”)
ClassLoader.getResources()
Activator.CreateInstance<T>()
Assembly.Load()
synchronized (this) { ... } lock (this) { ... }
synchronized method()
{ ... }
[MethodImpl(MethodImplOptions.Synchronized)]
void Method() { ... }
Thread relative static fields
Thread relative static fields
[ThreadStatic] and Data Slots
Jar
EXE/DLL
Private Assembly, Shared Assembly
Jar Signing Assembly Signing](https://image.slidesharecdn.com/understandingcforjava-130820002527-phpapp01/85/Understanding-c-for-java-7-320.jpg)

![C# Example
01. abstract class Animal {
02. public abstract string Speak();
03. }
04.
05. class Cat : Animal {
06. public string Speak() {
07. return “Meow!”;
08. }
09. }
10.
11. class Dog : Animal {
12. public string Speak() {
13. return “Bark!”;
14. }
15. }
16.
17. class Printer {
18. public static Print(Animal [] animals) {
19. animals[0] = new Dog();
20. for (var i = 0; i < animals.Length; i++) {
21. System.out.println(animals[i].speak();
22. }
23. }
24.
25. public static Print(IList<Animal> animals) {
26. for (var animal in animals) {
27. System.out.println(animal.Speak());
28. }
29. }
30.](https://image.slidesharecdn.com/understandingcforjava-130820002527-phpapp01/85/Understanding-c-for-java-27-320.jpg)
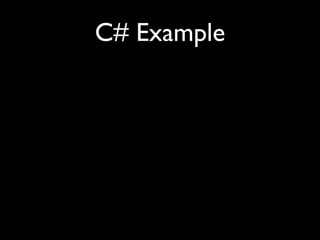
![C# Example
01. abstract class Animal {
02. public abstract string Speak();
03. }
04.
05. class Cat : Animal {
06. public string Speak() {
07. return “Meow!”;
08. }
09. }
10.
11. class Dog : Animal {
12. public string Speak() {
13. return “Bark!”;
14. }
15. }
16.
17. class Printer {
18. public static Print(Animal [] animals) {
19. animals[0] = new Dog();
20. for (var i = 0; i < animals.Length; i++) {
21. System.out.println(animals[i].speak();
22. }
23. }
24.
25. public static Print(IList<Animal> animals) {
26. for (var animal in animals) {
27. System.out.println(animal.Speak());
28. }
29. }
30.
01. public static Print(IEnumerable<Animal> animals)
02. {
03. for (var animal in animals) {
04. Console.Out.WriteLine(animal.Speak());
05. }
06. }
07. }
08. class TestCollections {
09. public static void main(String []args) {
10. Cat cat = new Cat();
11. Animal animal = cat;
12. animal.speak();
13.
14. animal = new Dog();
15. animal.speak();
16.
17. Animal [] animals = new Animal [] { cat, dog };
18. Cat [] cats = new Cat[] { cat };
19. animals = cats;
20. Print(animals); //Exposes Hole in Type System
21.
22. // In absence of above Print method, the code
23. // does not compile as Generic Collections in
24. // C# are Invariant.
25. List<Animal> animals = new ArrayList<Dog>();
26
27. //We need Co-variance to allow this to compile
28. Printer.Print(dogs);
29.
30. }
31. }](https://image.slidesharecdn.com/understandingcforjava-130820002527-phpapp01/85/Understanding-c-for-java-28-320.jpg)

![Java Example
01. abstract class Animal {
02. public abstract String speak();
03. }
04.
05. class Cat extends Animal {
06. public String speak() {
07. return “Meow!”;
08. }
09. }
10.
11. class Dog extends Animal {
12. public String speak() {
13. return “Bark!”;
14. }
15. }
16.
17. class Printer {
18. public static print(Animal [] animals) {
19. animals[0] = new Dog();
20. for (int i = 0; i < animals.length; i++) {
21. System.out.println(animals[i].speak();
22. }
23. }
24.
25. public static print(List<Animal> animals) {
26. for(Animal animal : animals) {
27. System.out.println(animal.speak());
28. }
29. }
30. }](https://image.slidesharecdn.com/understandingcforjava-130820002527-phpapp01/85/Understanding-c-for-java-30-320.jpg)
![Java Example
01. class TestCollections {
02. public static void main(String []args) {
03. Cat cat = new Cat();
04. Animal animal = cat;
05. animal.speak();
06.
07. animal = new Dog();
08. animal.speak();
09.
10. Animal [] animals = new Animal [] { cat, dog };
11. Cat [] cats = new Cat[] { cat };
12. animals = cats;
13. print(animals); //Exposes Hole in Type System
14.
15. // Fails to compile as Generic Collections in
16. // Java are Invariant
17. List<Animal> animals = new ArrayList<Dog>();
18.
19. List<Dog> dogs = new ArrayList<Dog>();
20. dogs.add(dog);
21. dogs.add(dog);
22. print(dogs);
23. }
24. }
01. abstract class Animal {
02. public abstract String speak();
03. }
04.
05. class Cat extends Animal {
06. public String speak() {
07. return “Meow!”;
08. }
09. }
10.
11. class Dog extends Animal {
12. public String speak() {
13. return “Bark!”;
14. }
15. }
16.
17. class Printer {
18. public static print(Animal [] animals) {
19. animals[0] = new Dog();
20. for (int i = 0; i < animals.length; i++) {
21. System.out.println(animals[i].speak();
22. }
23. }
24.
25. public static print(List<Animal> animals) {
26. for(Animal animal : animals) {
27. System.out.println(animal.speak());
28. }
29. }
30. }](https://image.slidesharecdn.com/understandingcforjava-130820002527-phpapp01/85/Understanding-c-for-java-31-320.jpg)