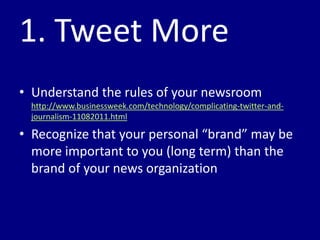
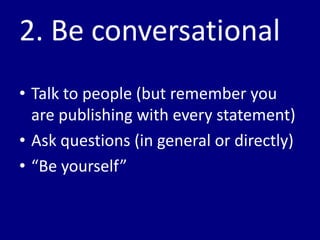
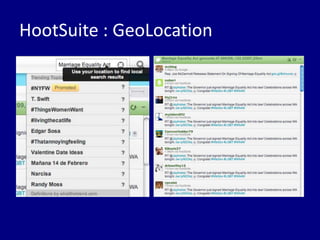
This document provides tips for reporters on using Twitter effectively. It recommends that reporters tweet more to develop their personal brand, have conversational tweets by asking questions, and use hashtags and tools to monitor stories and crowdsource ideas. Reporters are advised to listen on Twitter by following others in their beat and verify information. Various tools are outlined to help with monitoring hashtags, geotagging tweets, embedding tweets in stories, and signing up for Twitter lists and directories.