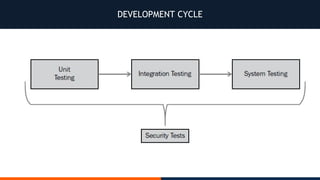
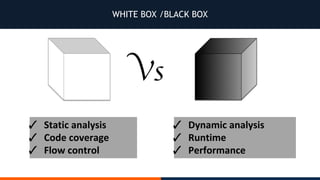
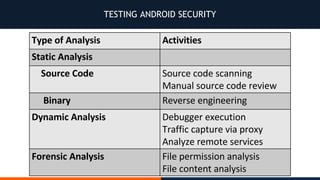
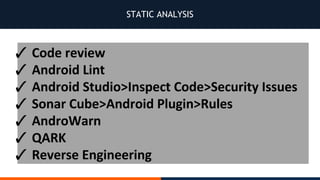
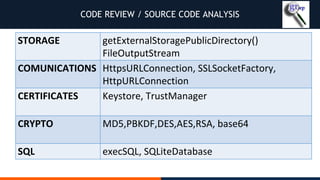
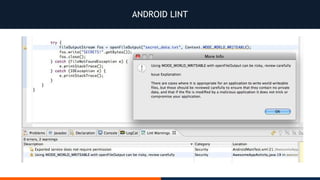
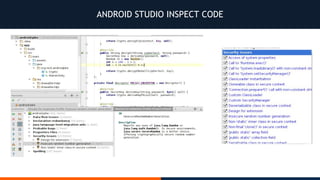
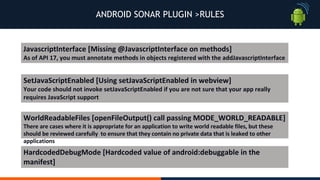
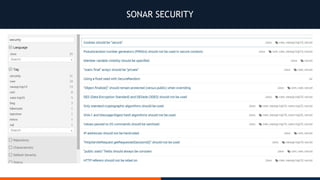
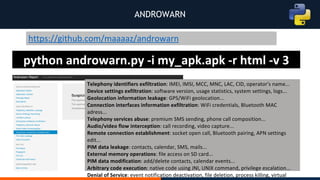
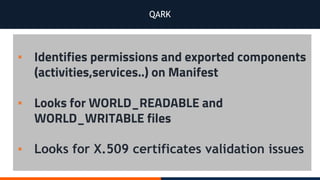
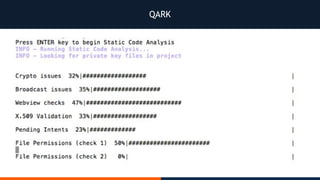
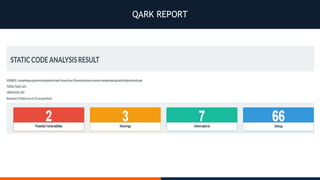
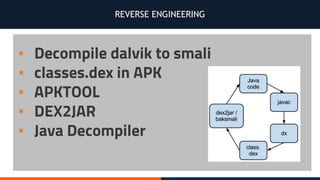
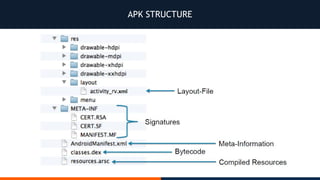
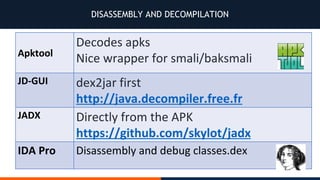
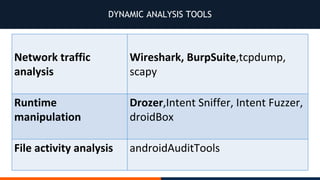
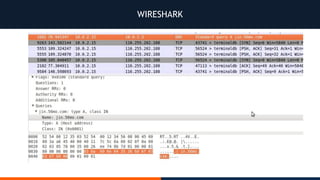
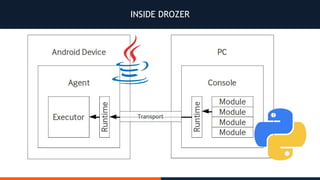
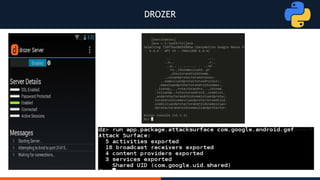
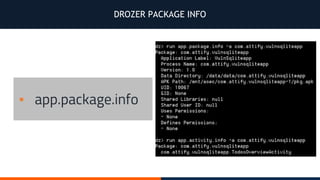
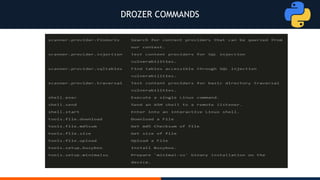
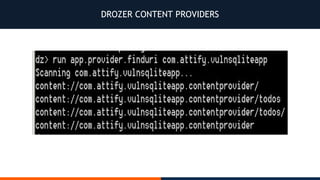
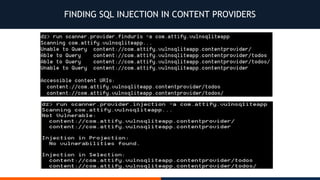
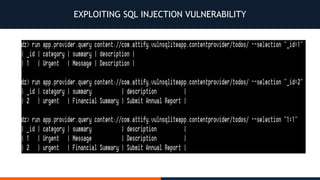
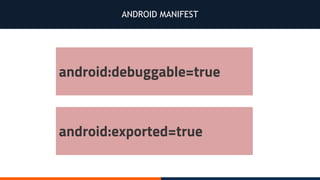
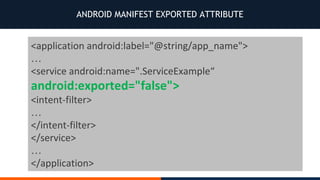
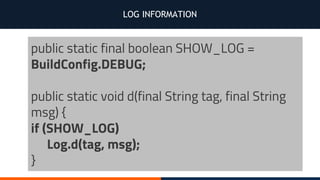
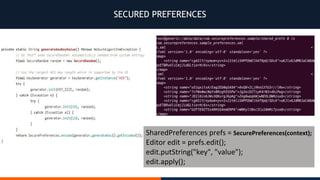
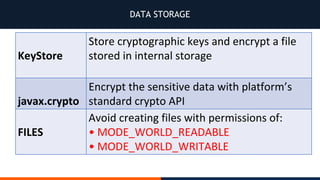
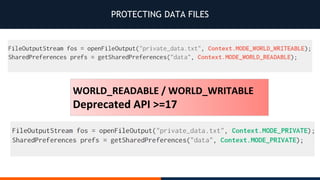
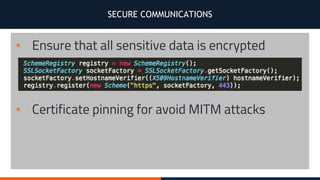
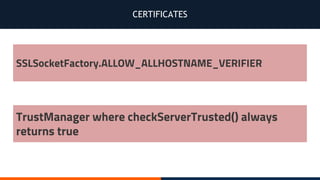
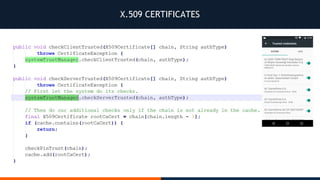
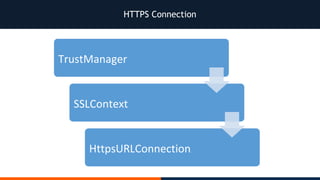
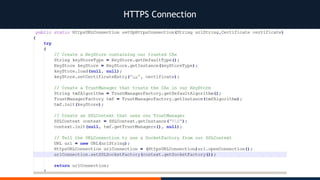
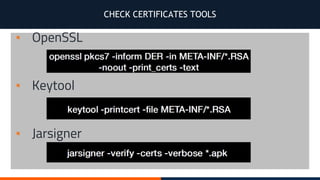
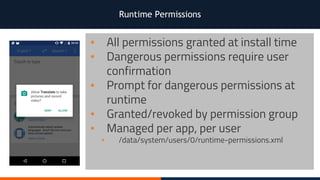
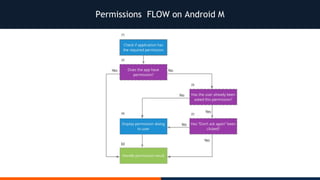
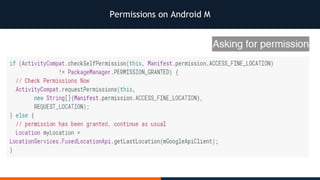
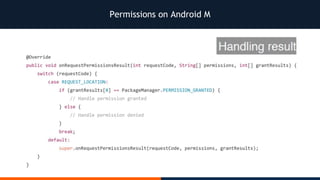
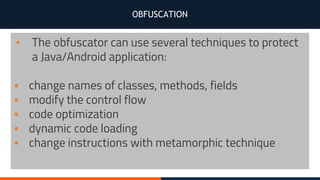
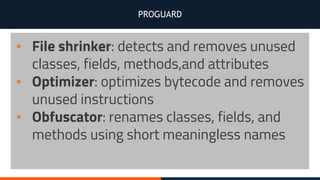
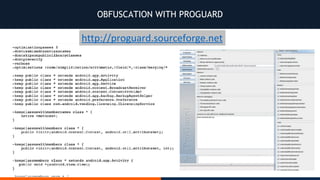
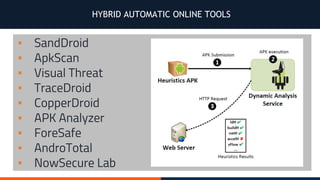
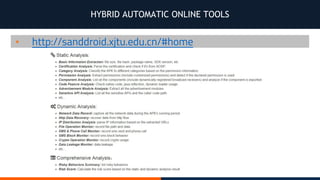
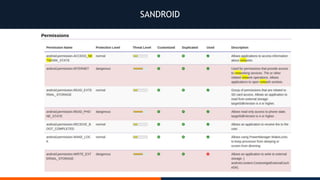
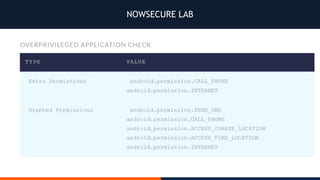
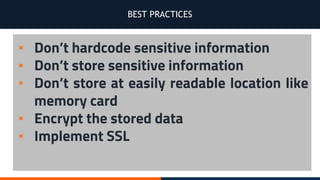
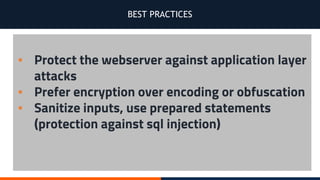
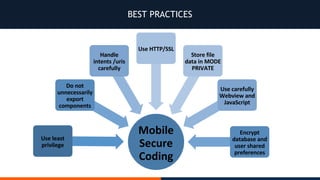
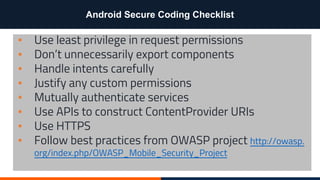
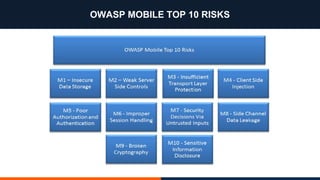
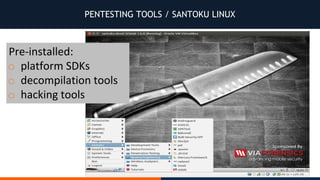
The document provides a comprehensive overview of testing Android security, covering development cycles, static and dynamic analysis, and best practices for securing Android applications. It discusses tools for vulnerability assessment, such as Qark and Drozer, and details methods for protecting data and ensuring secure communications. Additionally, the document emphasizes following established guidelines like the OWASP Mobile Security Project and using obfuscation techniques to safeguard app code.