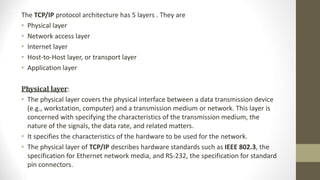
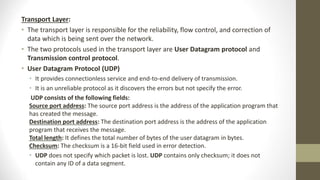
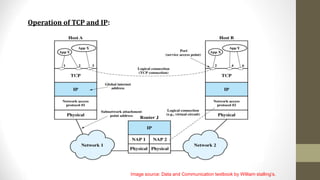
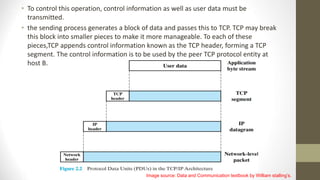
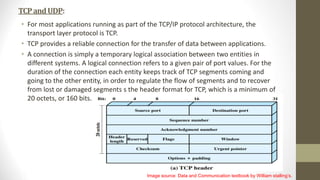
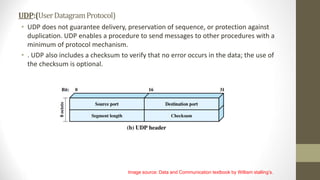
The document provides an overview of the TCP/IP protocol architecture. It discusses the five layers of TCP/IP including the physical, network access, internet, transport, and application layers. It describes the protocols used at each layer, such as IP, TCP, UDP, HTTP, and FTP. The document also discusses how data is encapsulated as it passes through each layer of the TCP/IP model and is transmitted from one host to another across networks and the internet.