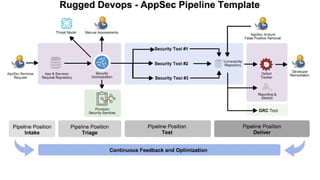
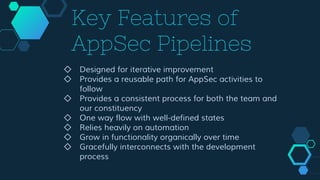
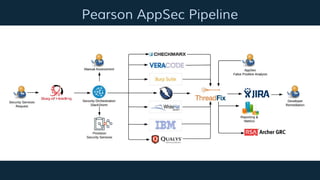
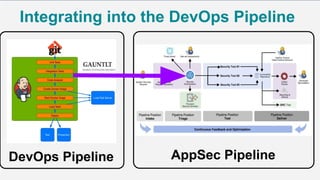
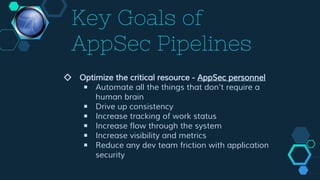
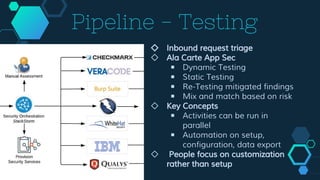
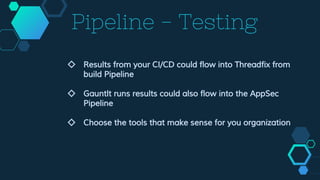
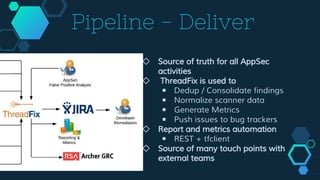
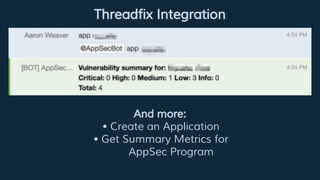
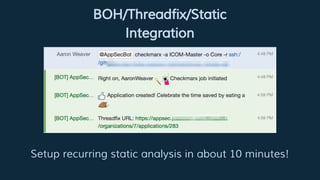
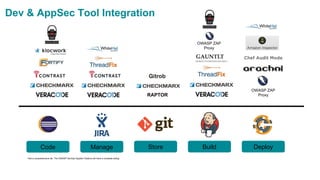
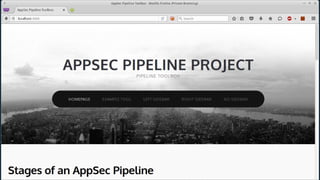
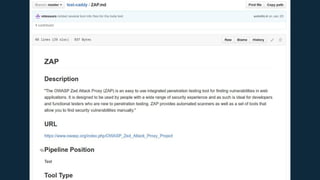
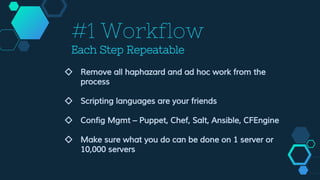
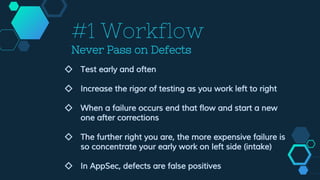
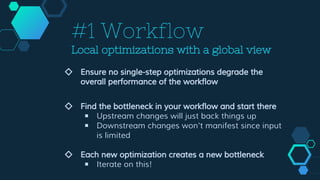
This document summarizes Matt Tesauro's presentation "Taking AppSec to 11" given at Bsidess Austin 2016. The presentation discusses implementing application security (AppSec) pipelines to improve workflows and optimize critical resources like AppSec personnel. Key points include automating repetitive tasks, driving consistency, increasing visibility and metrics, and reducing friction between development and AppSec teams. An AppSec pipeline provides a reusable and consistent process for security activities to follow through intake, testing, and reporting stages. The goal is to optimize people's time spent on customization and analysis rather than setup and configuration.


![Timeline
Business Operations Customer
Flow [rate] – the speed work goes through the process
Development](https://image.slidesharecdn.com/bsidesaustin2016-takingappsecto11-matttesauro-160404181753/85/Taking-AppSec-to-11-BSides-Austin-2016-7-320.jpg)