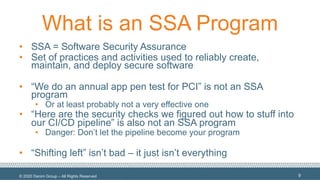
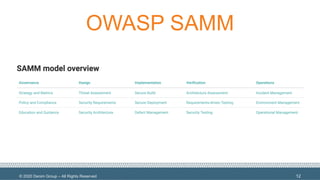
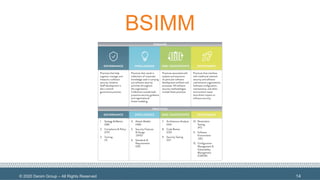
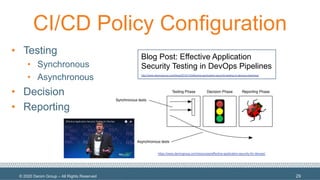
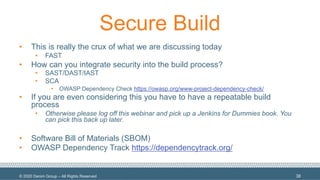
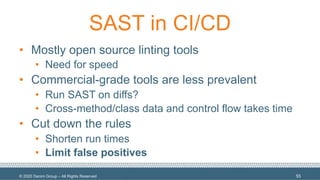
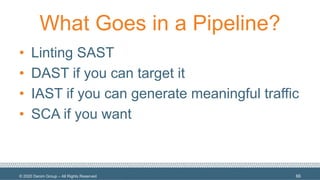
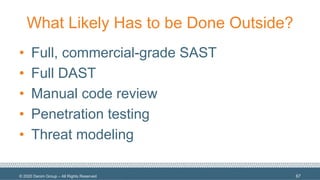
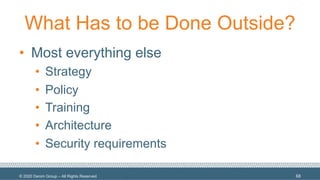
The document discusses the integration of security in the DevSecOps CI/CD pipeline, emphasizing that a pipeline should not replace a comprehensive Software Security Assurance (SSA) program. It highlights the importance of various security practices, tools, and methodologies such as OWASP SAMM and BSIMM, while identifying what can and cannot be automated in relation to security measures. The conclusion reinforces the need to balance speed and security, stating that while some security checks can be automated, many aspects must still be executed manually for effective security assurance.