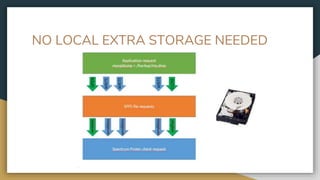
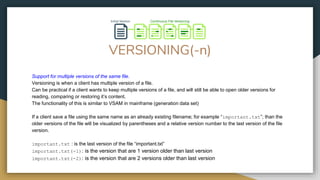
SPFS is a filesystem that can be used with Spectrum Protect as an agentless backup solution. It provides versioning, encryption, data redundancy, data reduction techniques, data filtering, and data retention functionalities without requiring any additional storage, education, or agents. SPFS allows databases and applications to be protected by Spectrum Protect without needing custom backup agents or specialized knowledge through a simple filesystem interface.