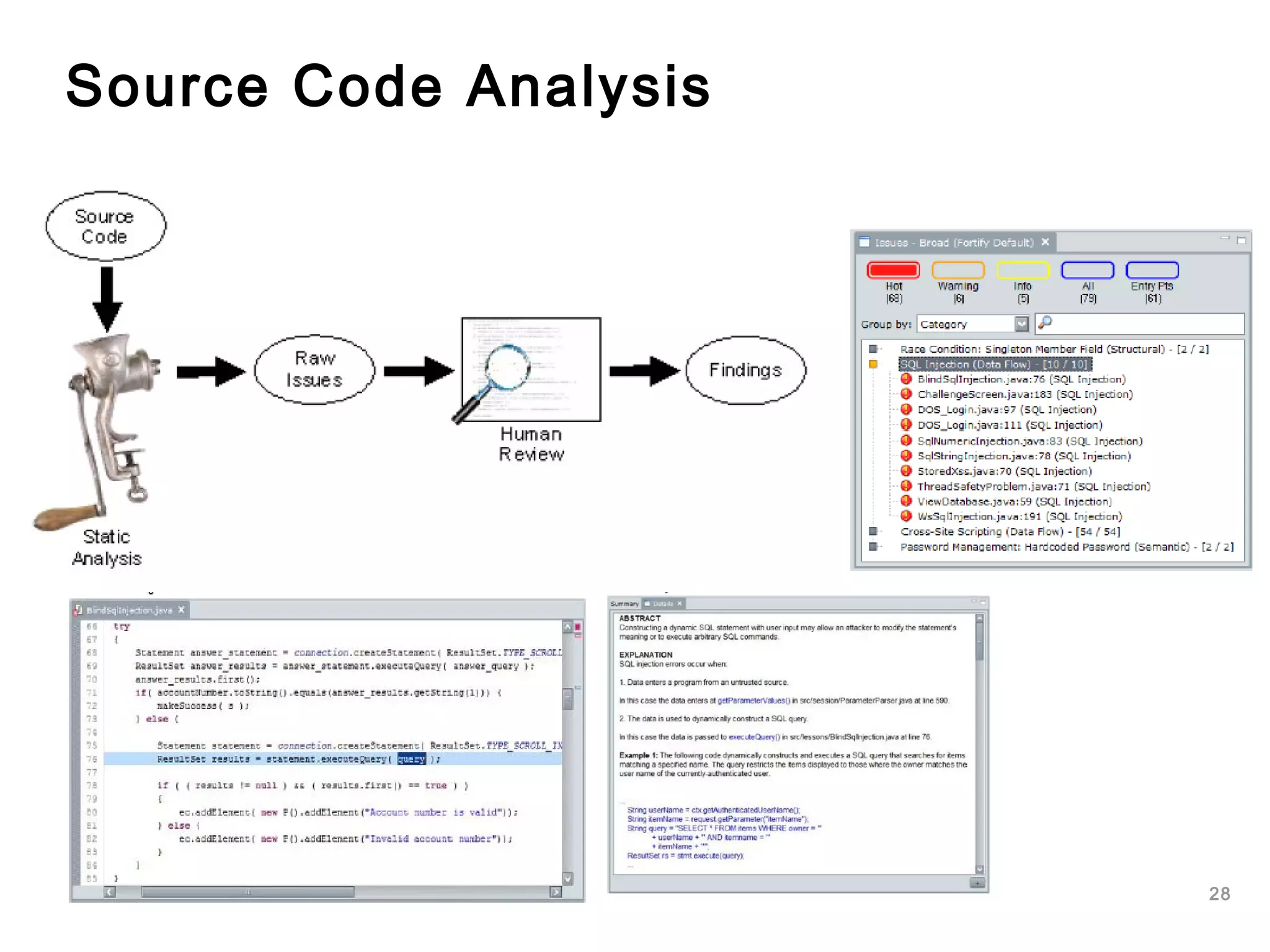
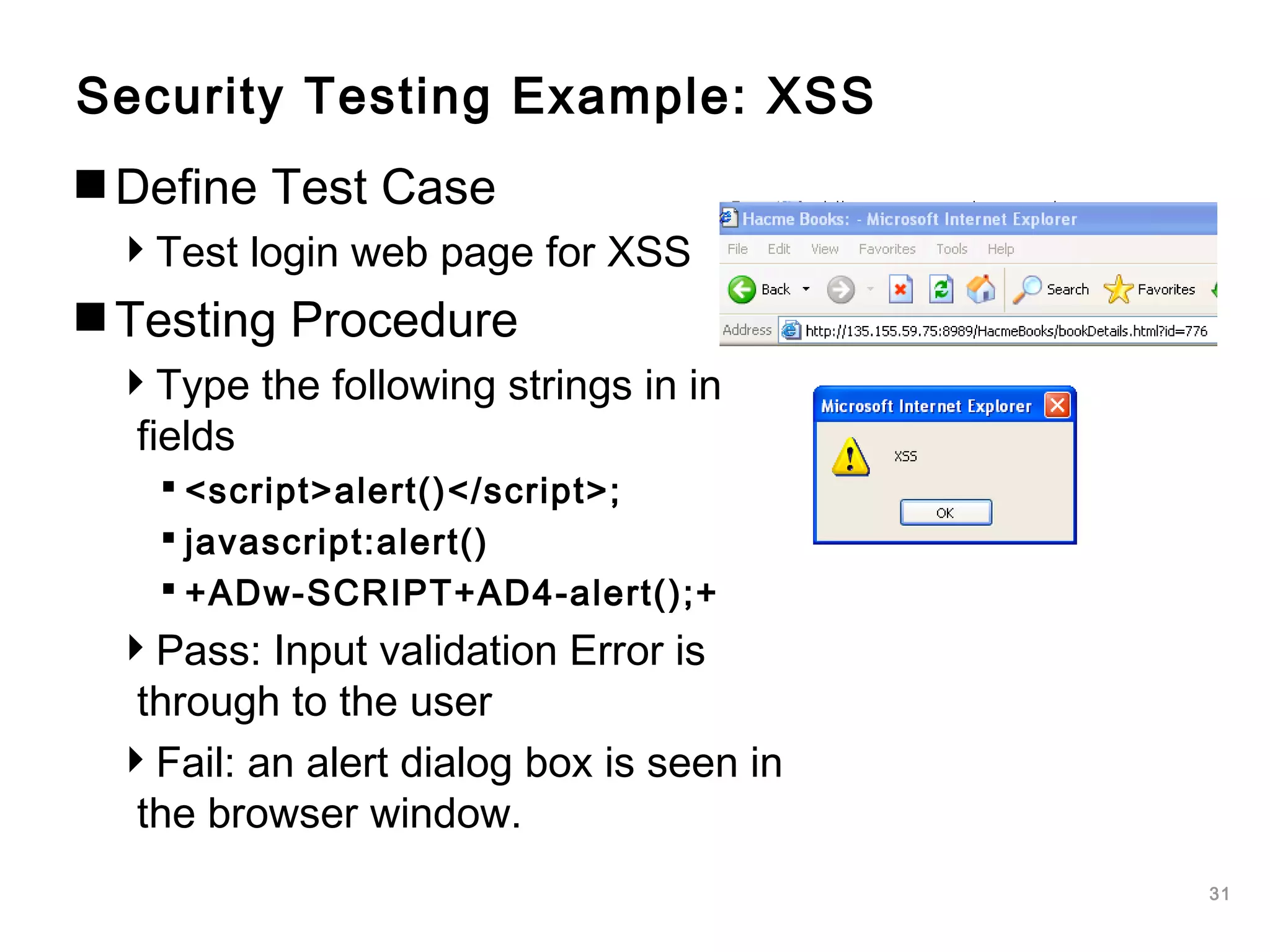
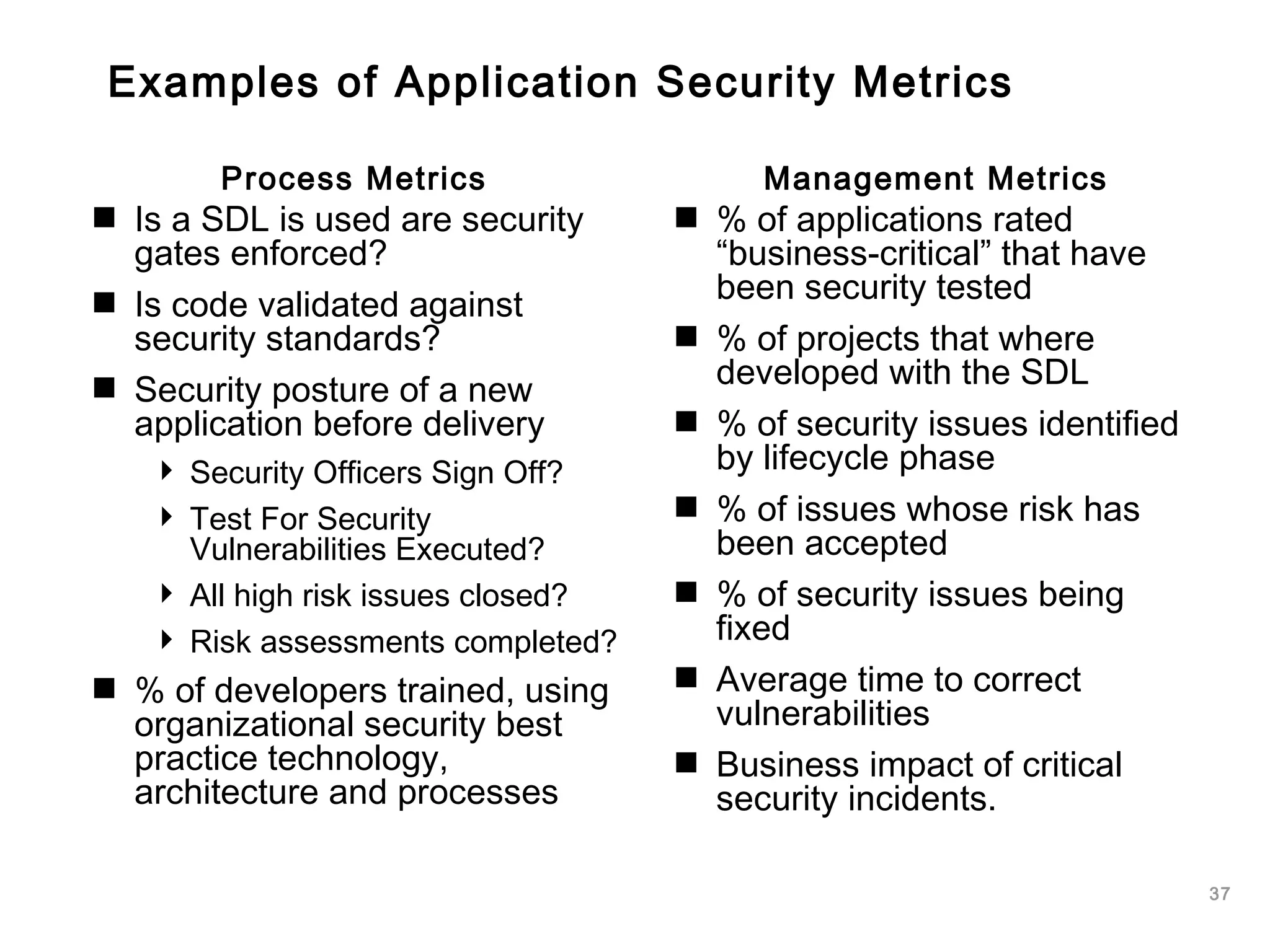
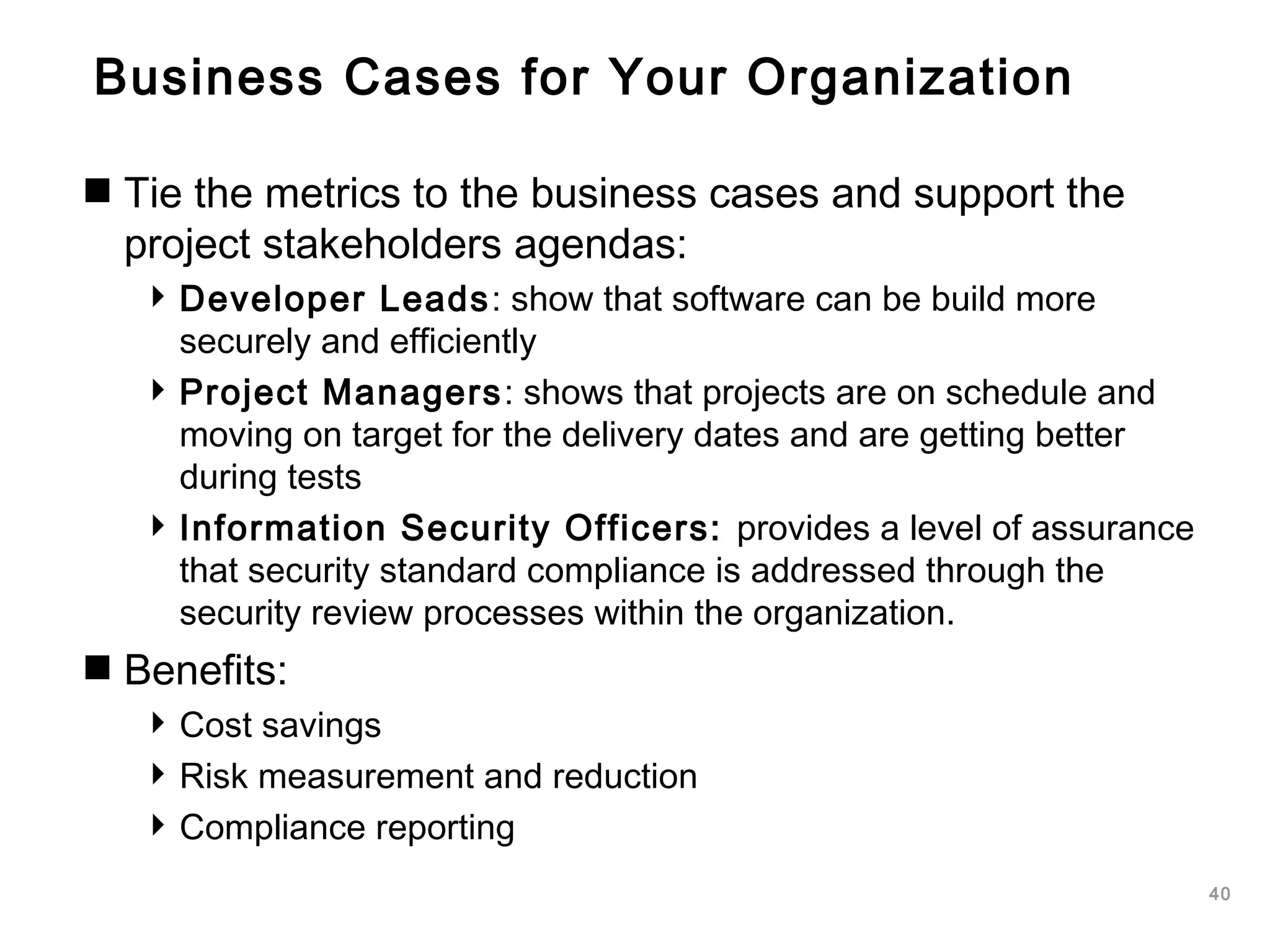
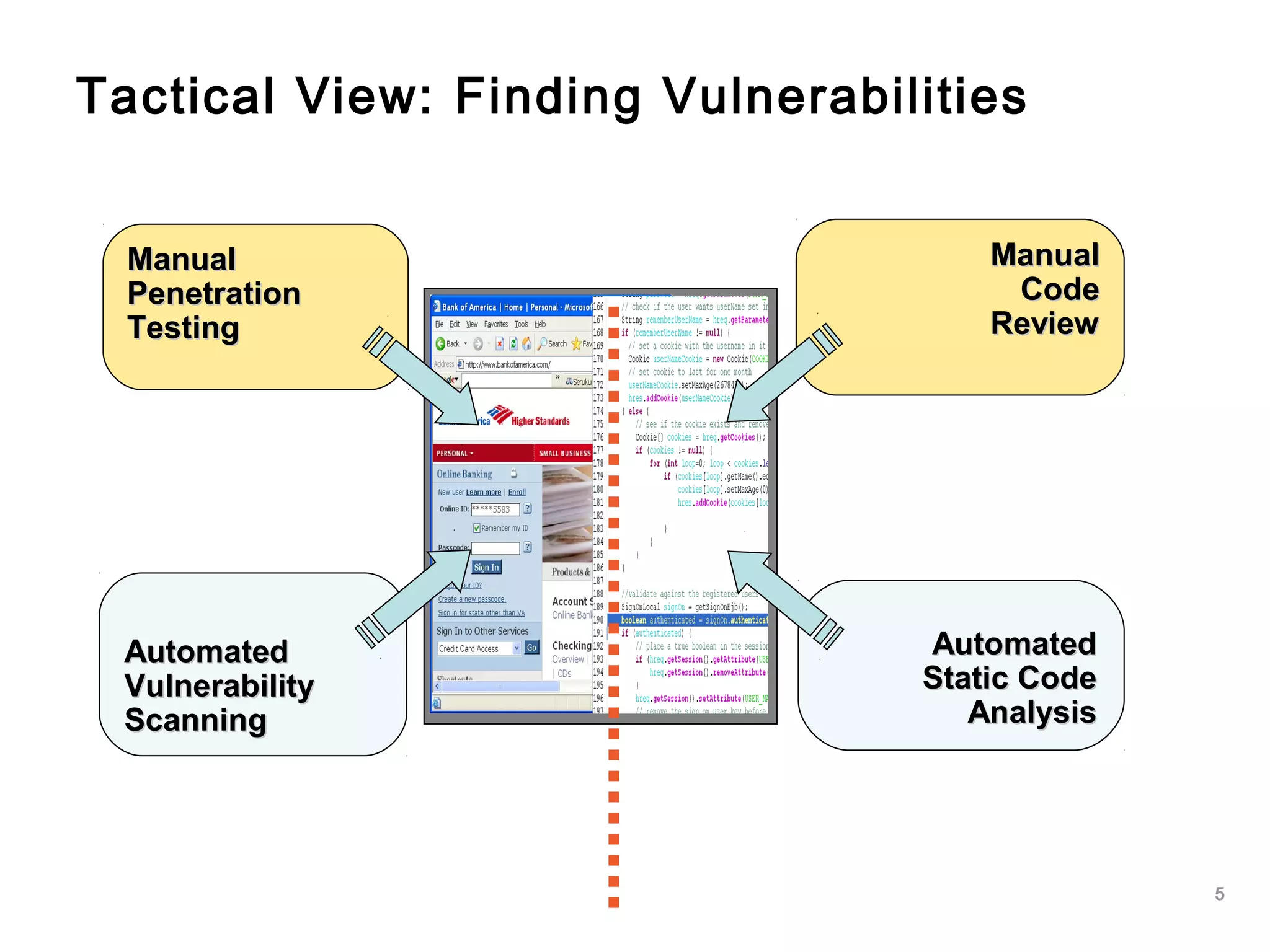
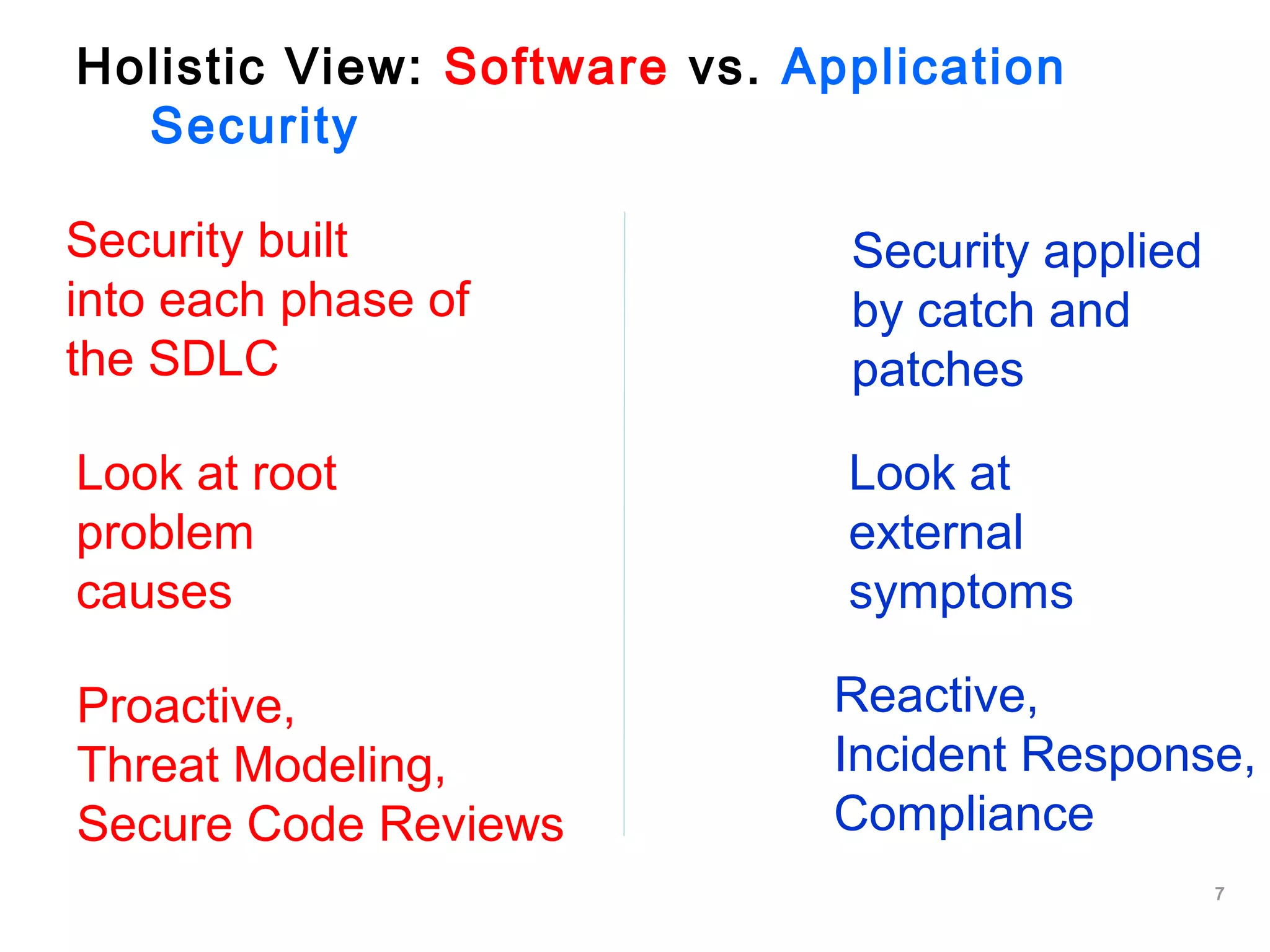
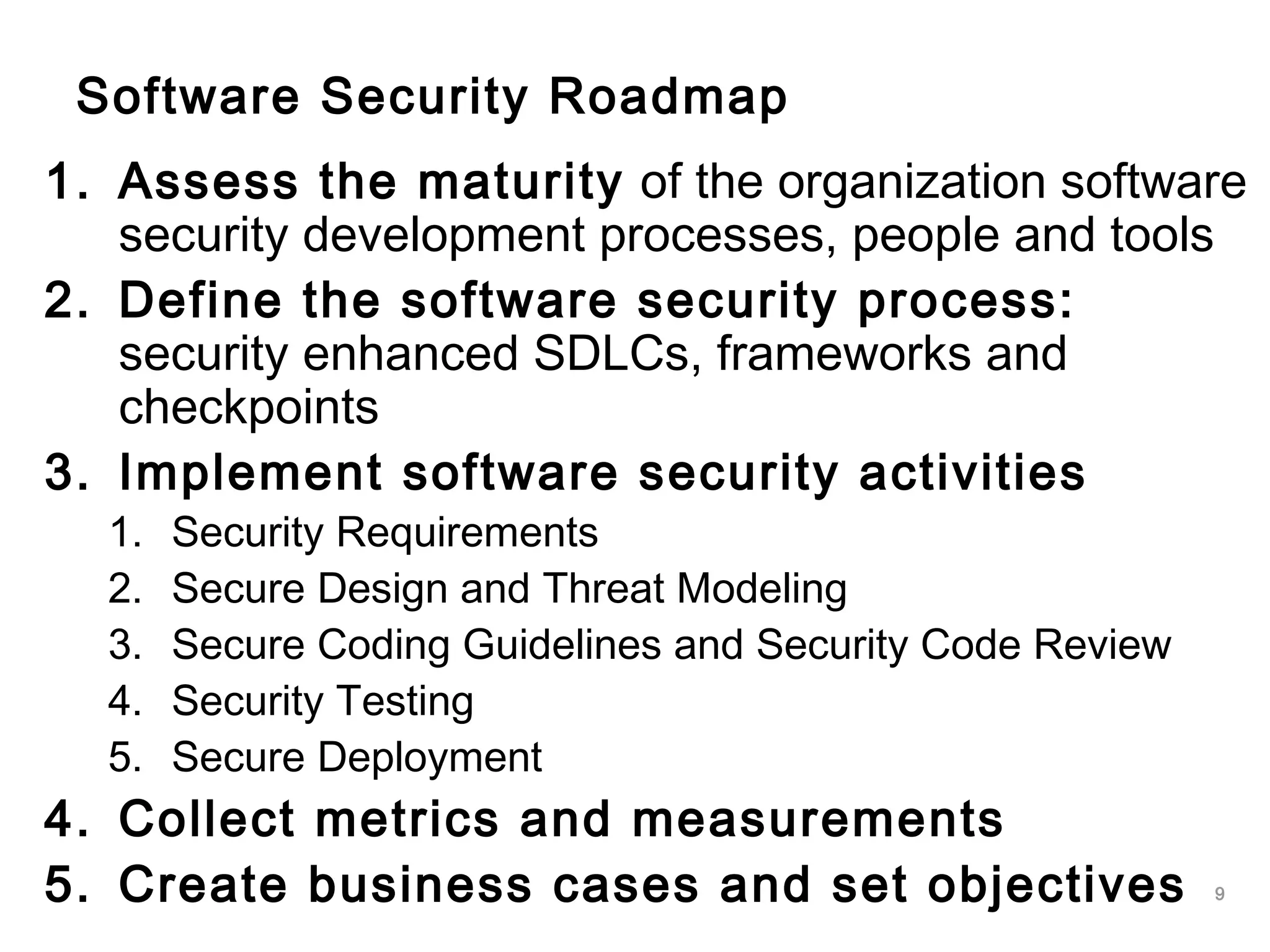
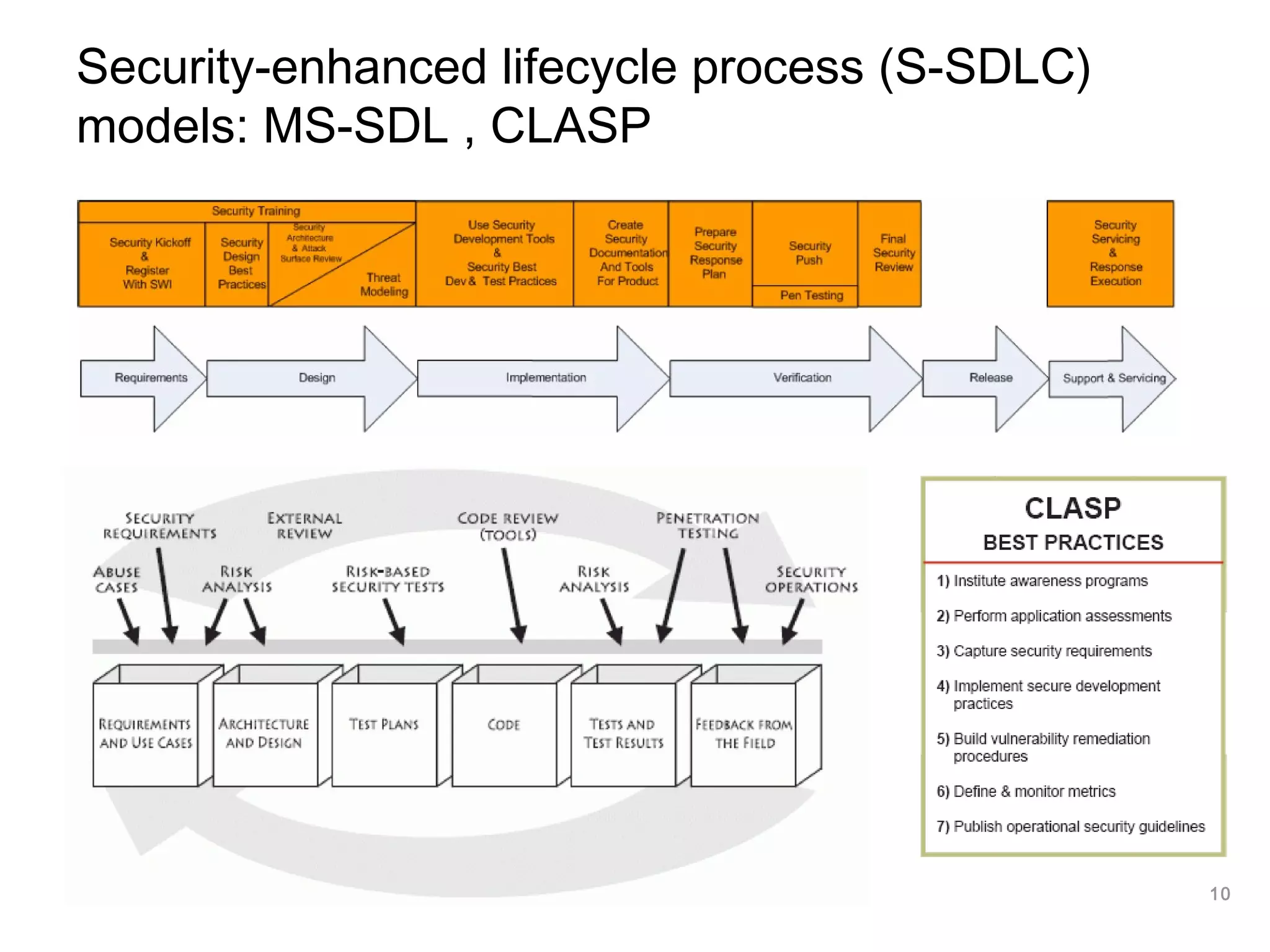
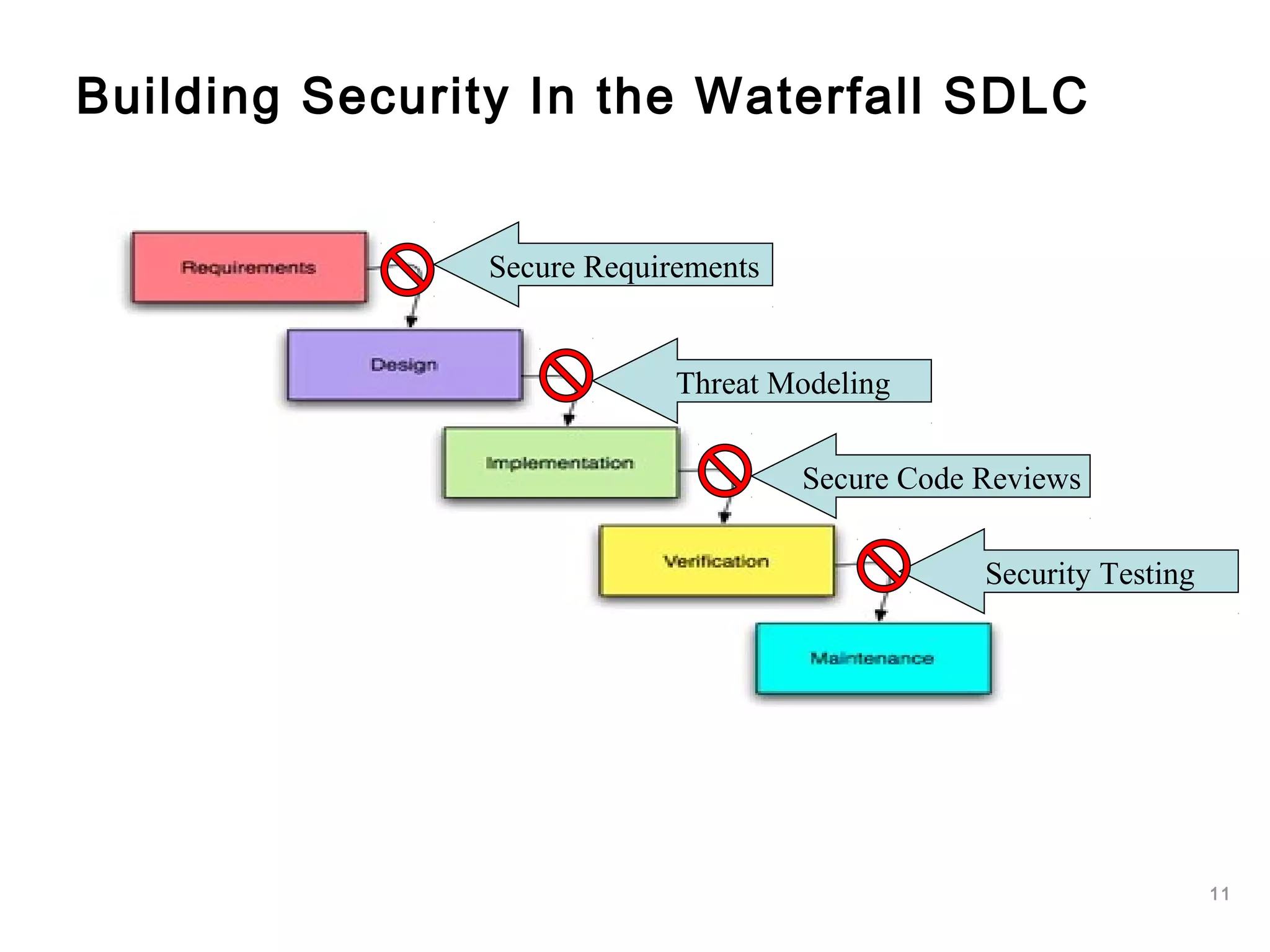
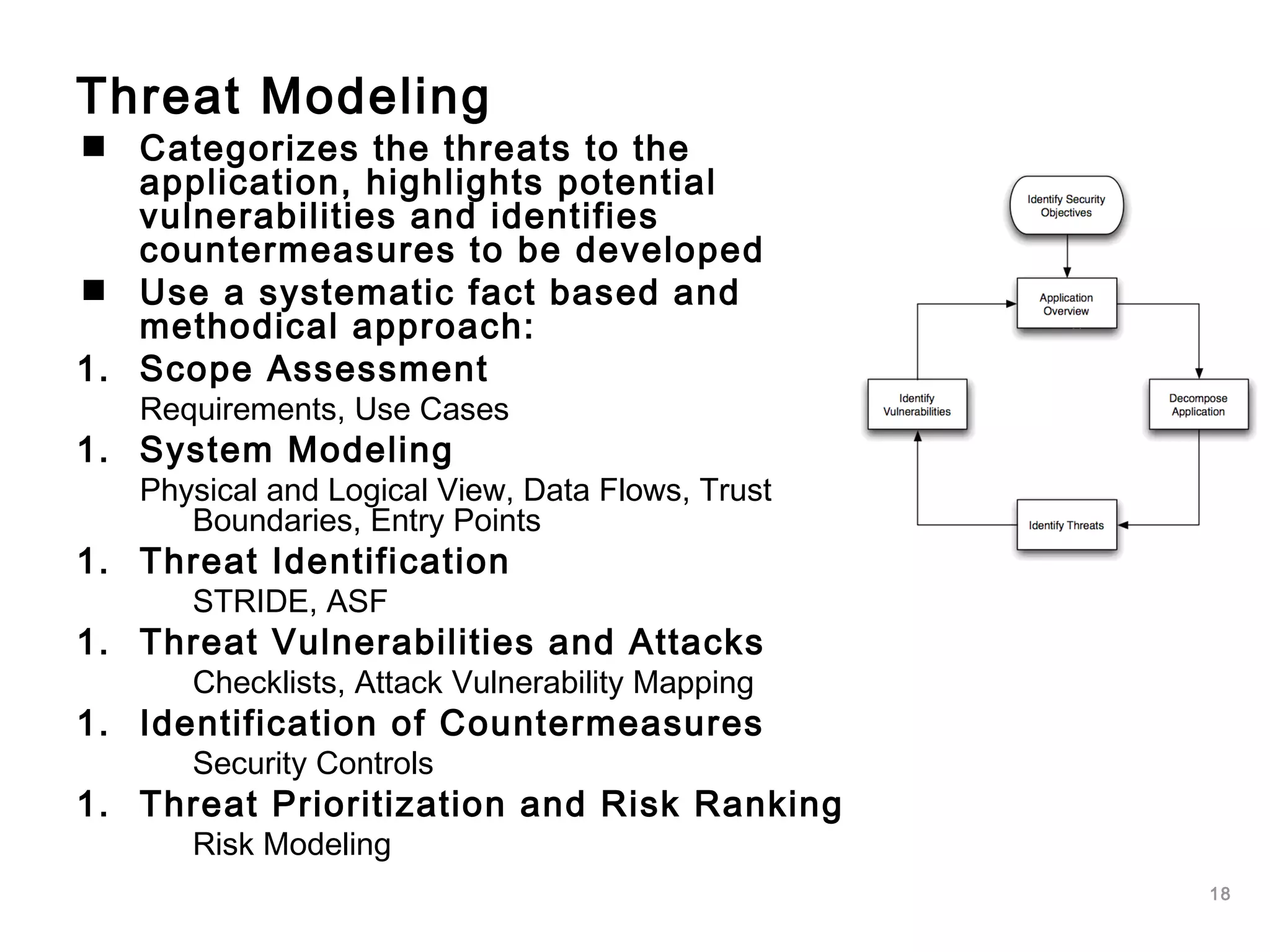
This document outlines an approach to application security that involves assessing maturity, defining a software security roadmap, and implementing security activities throughout the software development lifecycle (SDLC). It discusses security requirements, threat modeling, secure design guidelines, coding standards, security testing, configuration management, metrics, and making business cases to justify security investments. The goal is to manage software risks proactively by building security into each phase rather than applying it reactively through patches.






![26
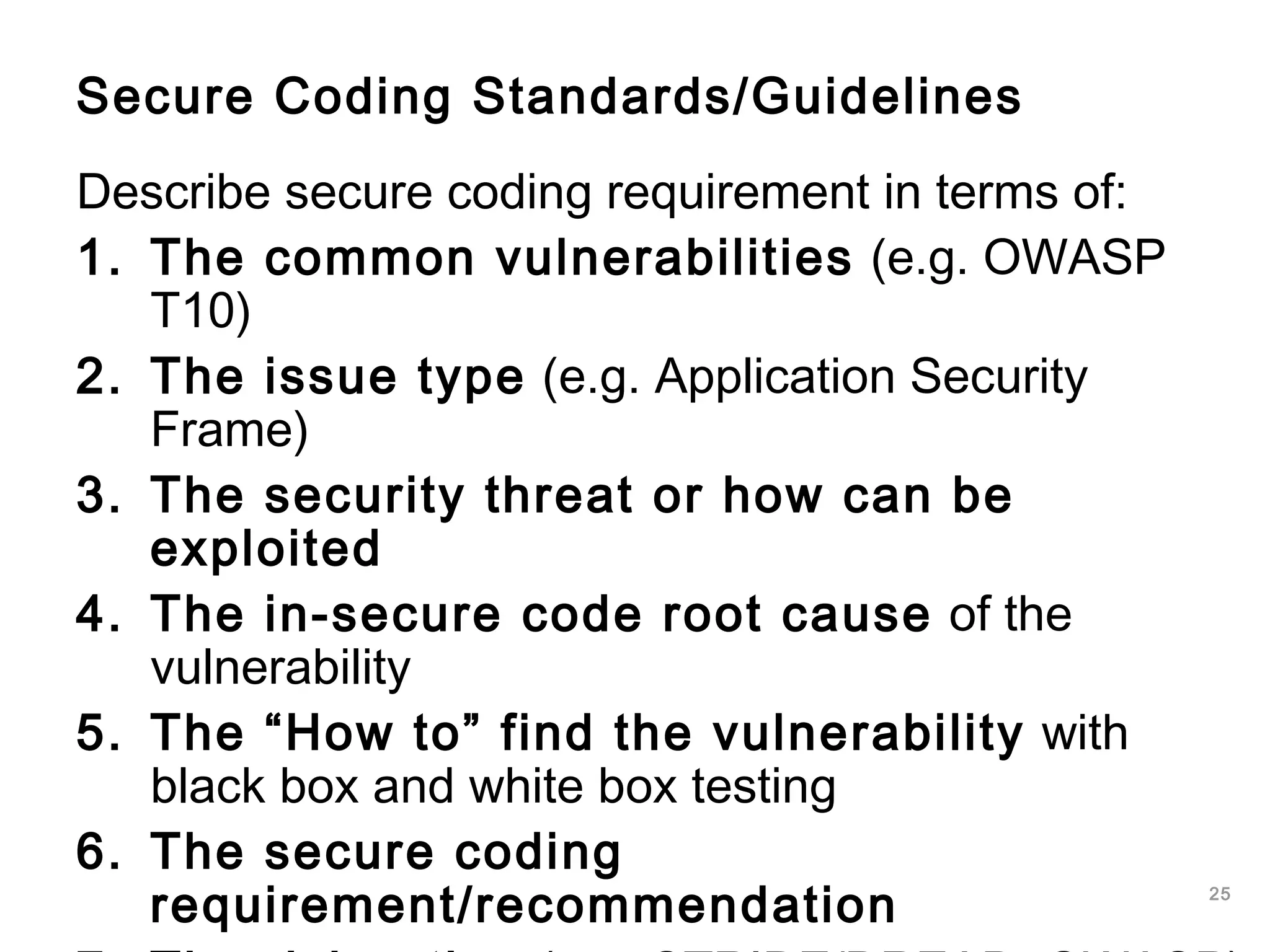
Example SQL Injection - Secure coding
requirements
Use SQL parameterized queries, avoid
dynamic SQL generation:
SELECT * FROM users WHERE username=?
JAVA EE use strongly typed “PreparedStatement”
in .NET use “SqlCommand” with “SqlParameters”
Sanitize input, remove special characters:
' " ` ; * % _ =&|*?~<>^()[]{}$nr
Use custom error messages:
No SQL exception information in error messages](https://image.slidesharecdn.com/softwaresecurityengineering-160330054650/75/Software-security-engineering-26-2048.jpg)