The document presents a project report on a blockchain ecosystem for medical data management, submitted by students from Koneru Lakshmaiah Education Foundation for their bachelor's degree in computer science engineering. It explores the application of blockchain technology to securely store and share medical records while addressing challenges such as scalability and data privacy. The report consists of various sections including an introduction to blockchain, theoretical analysis, experimental results, and recommendations for implementation in healthcare.
![KONERU LAKSHMAIAH EDUCATION FOUNDATION 10
1.2 History
The 2008 monetary crisis caused tons of individuals to lose trust in banks as sure third
parties. Many questioned whether banks were the simplest guardians of the world
economic system. Bad investment choices by major banks had tested ruinous, with ripple
consequences.
Bitcoin — conjointly projected in 2008 — conferred an alternate.
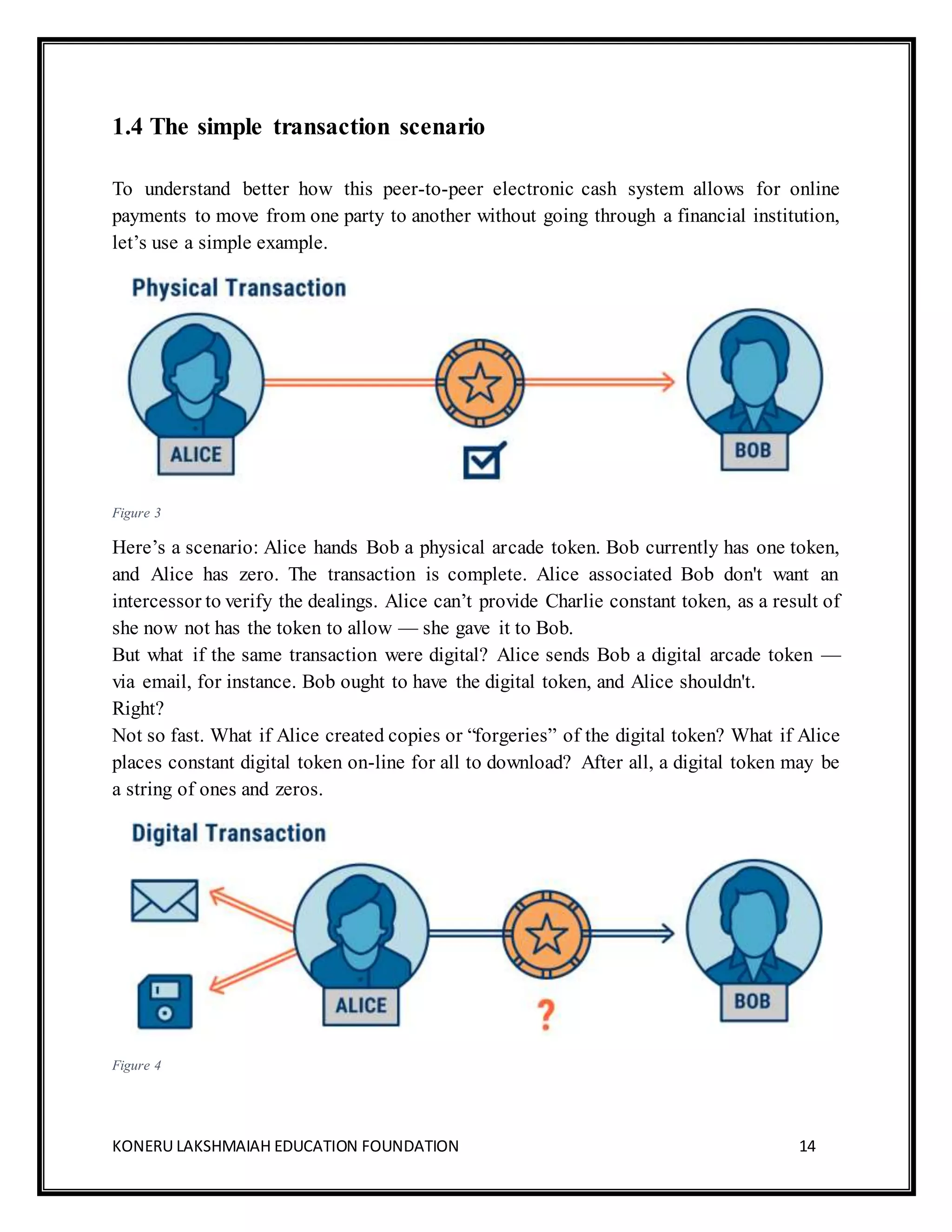
According to its whitepaper, Bitcoin is a “peer-to-peer electronic cash system” that
“allow[s] for online payments to be sent directly from one party to another without going
through a financial institution.”
In alternative words, Bitcoin created digital transactions attainable while not a “trusted
negotiate.” The technology allowed this to happen at scale, globally, with cryptography
doing what institutions like commercial banks, financial regulators, and central banks
accustomed do: verify the legitimacy of transactions and safeguard the integrity of the
underlying plus.
Bitcoin is a decentralized, public ledger. There is no sure third-party dominant the ledger.
Anyone with bitcoin will participate within the network, send and receive bitcoin, and even
hold a copy of this ledger if they want to. In that sense, the ledger may be involved with all
kinds of transactions varying from criminals to bankers.
Since the ledger is defined with certain limit of existence only certain Bitcoins around 21M
can be mined and operated in the chain. Because of this cover on the number of bitcoins in
circulation, which will eventually be reached, bitcoin is inherently resistant to inflation.
That means that a lot of bitcoin can’t be written at a whim and scale back the worth of the
currency.
All participants should comply with the ledger’s rules to use it.
Bitcoin is politically decentralized — no single entity runs bitcoin — but centralized from
a data standpoint — all participants (nodes) agree on the state of the ledger and its rules.
A bitcoin or a group action can’t be modified, erased, copied, or cast – everyone would
apprehend.](https://image.slidesharecdn.com/blockchainecomunezfinal-181221104140/75/Simple-Blockchain-Eco-System-for-medical-data-management-10-2048.jpg)
![KONERU LAKSHMAIAH EDUCATION FOUNDATION 20
2. LITERATURE SURVEY
2.1 MedRec prototype for electronic health records[4]
For MedRec, the block content represents information possession and viewership
permissions shared by members of a personal, peer-to-peer network. Blockchain
technology supports the utilization of “smart contracts,” which permit a North American
nation to alter and track bound state transitions (such as a modification in viewership rights,
or the birth of a new record in the system). Via sensible contracts on AN Ethereum
blockchain, we log patient-provider relationships that associate a medical record with
viewing permissions and data retrieval instructions (essentiallydata pointers) for execution
on external databases.
2.2 Bigchain DB 2.0: The Blockchain Database [5]
BigchainDB is termed a blockchain information as a result of it's some blockchain
properties and a few information properties. The original style started with a information
and extra some blockchain characteristics like decentralization, immutability, and owner-
controlled assets. The idea was that the resulting system would inherit the desirable
properties of the database such as low latency, high transaction rate, and high capacity.
BigchainDB may be a blockchain information: it's each blockchain properties and database
properties. That combination makes it helpful for a good style of use cases, including
supply chain, IP rights management, digital twins & IoT, identity, data governance, and
immutable audit trails. BigchainDB 2.0 is now production-ready for many use cases.
2.3 Applications of BlockchainTechnology beyond Cryptocurrency [6]
The application of the Blockchain idea and technology has big on the far side its use for
Bitcoin generation and transactions. The properties of its security, privacy, traceability,
inherent data provenance and time-stamping has seen its adoption beyond its initial
application areas. The Blockchain itself and its variants area unit currently want to secure
any form of transactions, whether it be human-to-human communications or machine-to-
machine. Its adoption seems to be secure particularly with the world emergence of the
Internet-of-Things. Its localized application across the already established world net is
additionally terribly appealing in terms of guaranteeing information redundancy and thus
survivability. The Blockchain has been particularly known to be appropriate in developing](https://image.slidesharecdn.com/blockchainecomunezfinal-181221104140/75/Simple-Blockchain-Eco-System-for-medical-data-management-20-2048.jpg)
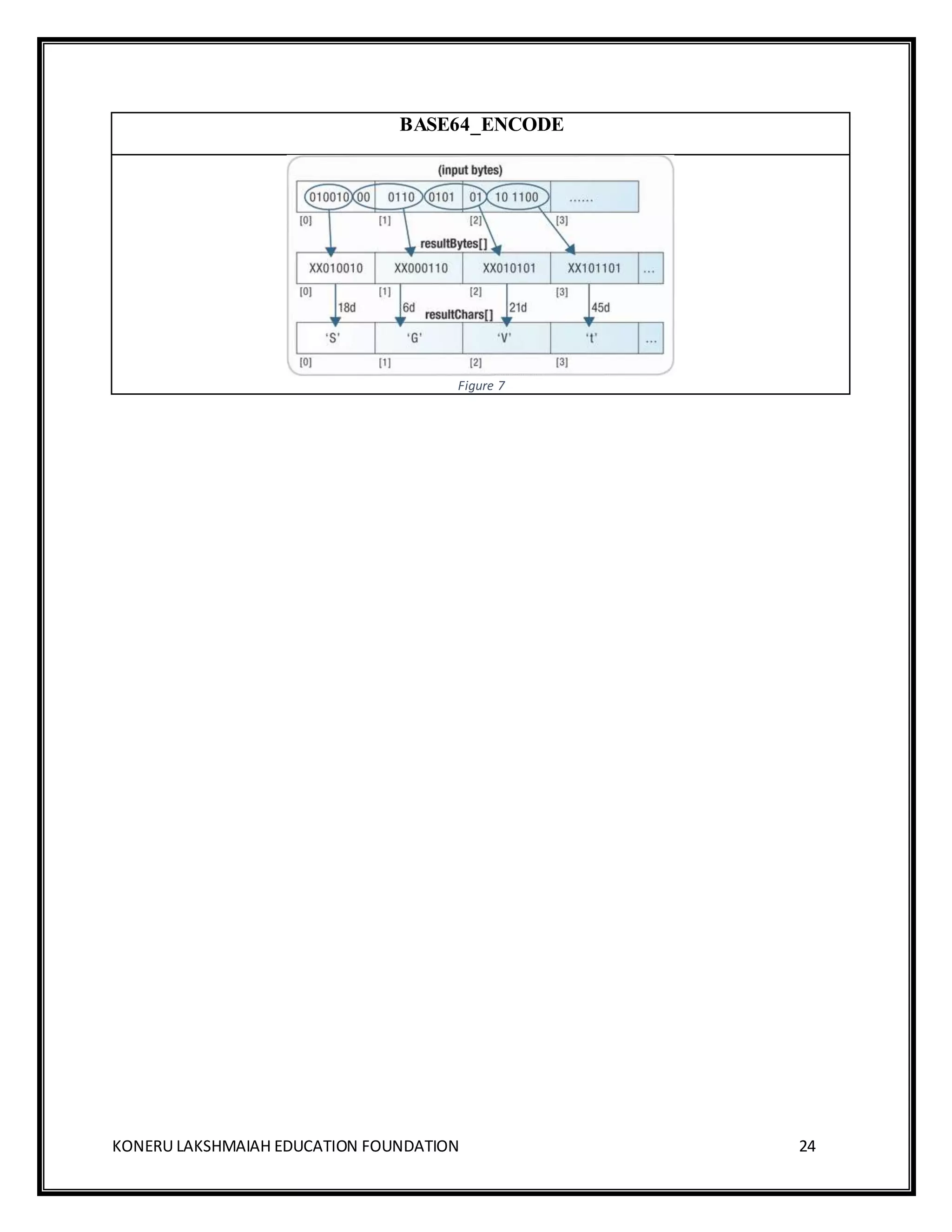
![KONERU LAKSHMAIAH EDUCATION FOUNDATION 26
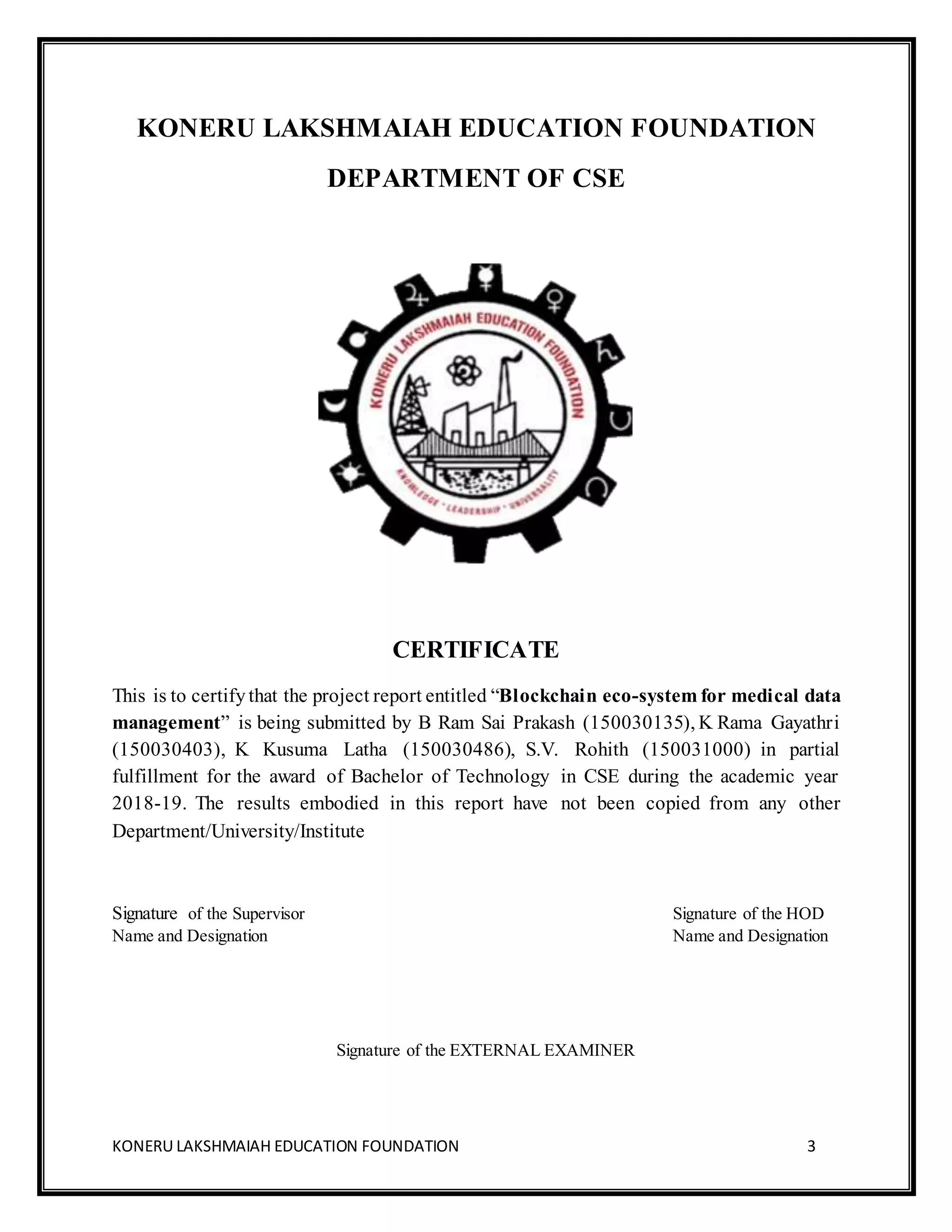
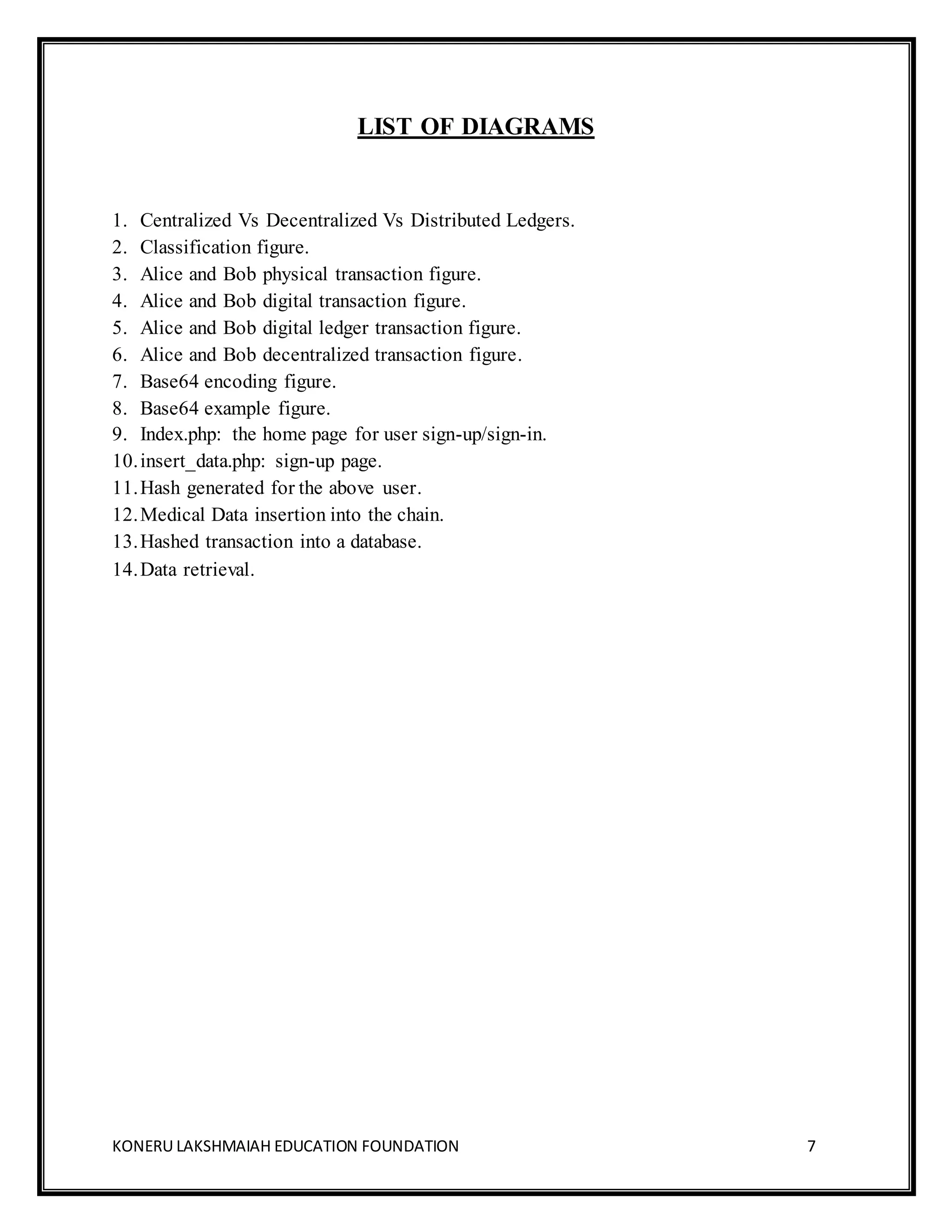
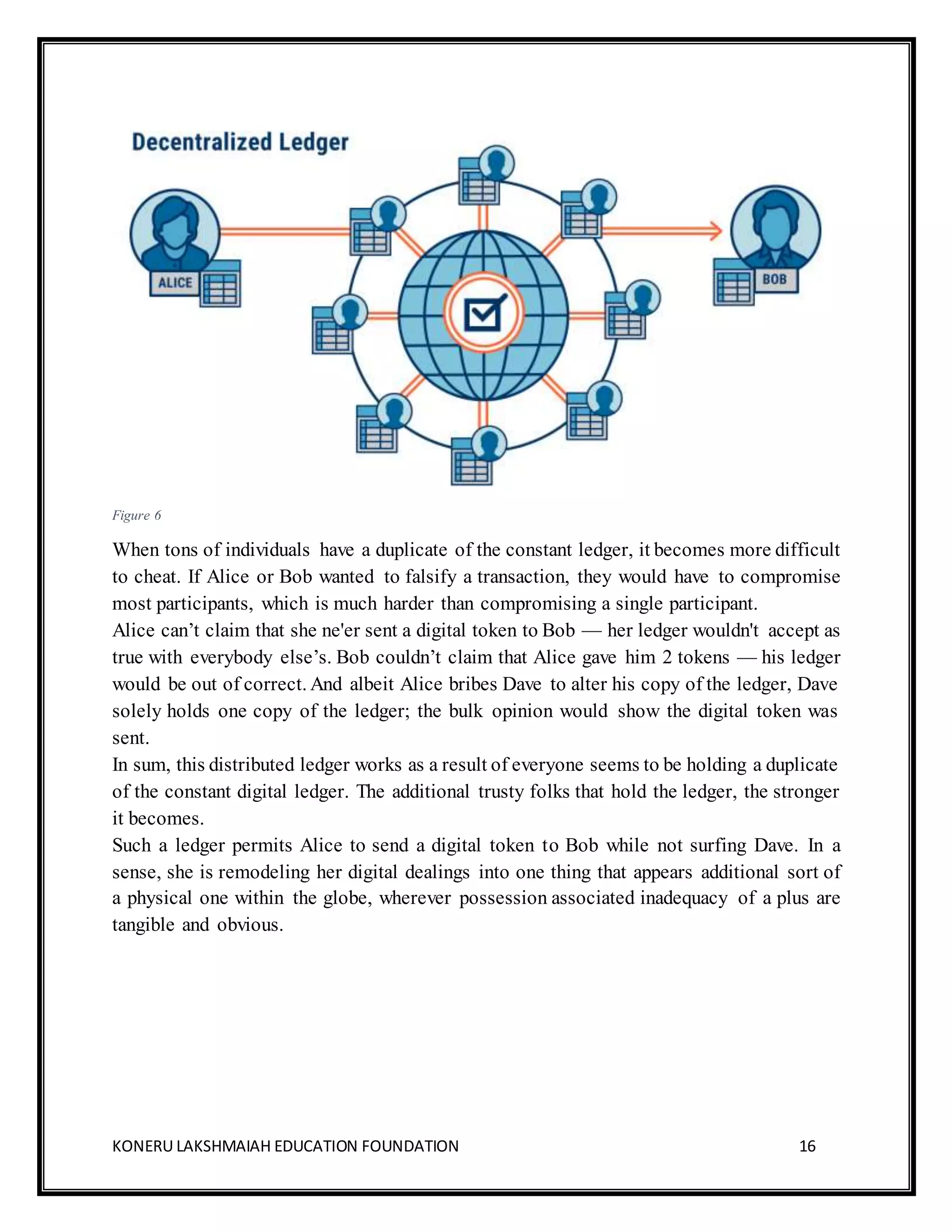
$var=$_SESSION['id'];
include 'includes/connect_db.php';
if(isset($_POST['submit']))
{
$data=mysqli_real_escape_string ($con, $_POST['entry']);
$i=0;
$ans=1;
while($ans==1)
{
$encr=hash ('sha256’, $i.$var);
$sql="SELECT * FROMhealth_data where trans_id='$encr';";
$res=mysqli_query ($con, $sql);
if(mysqli_num_rows($res)>0)
$i=$i+1;
else
$ans=0;
}
$sql="INSERT INTO health_data (trans_id, data) VALUES ('$encr','$data');";
mysqli_query ($con, $sql);](https://image.slidesharecdn.com/blockchainecomunezfinal-181221104140/75/Simple-Blockchain-Eco-System-for-medical-data-management-26-2048.jpg)
![KONERU LAKSHMAIAH EDUCATION FOUNDATION 27
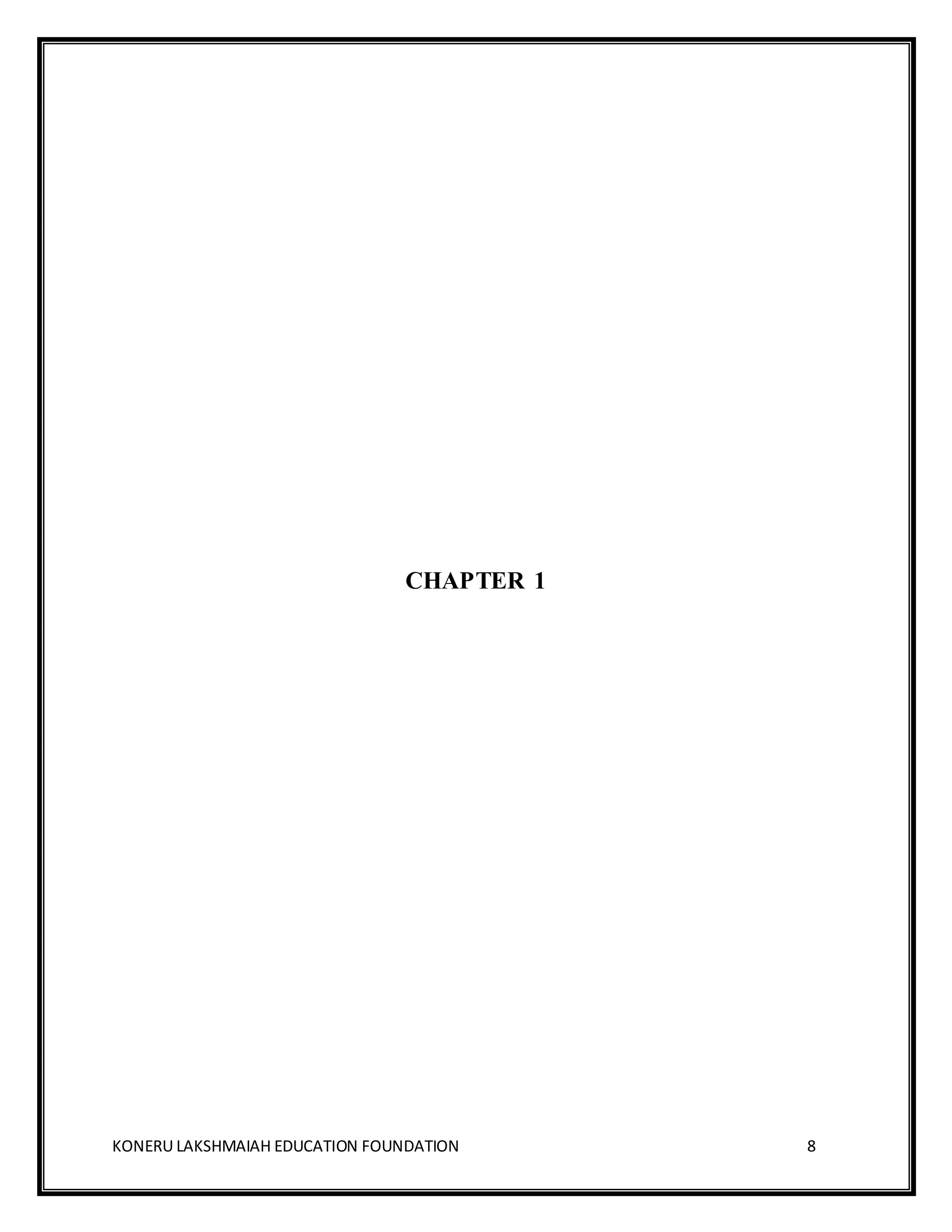
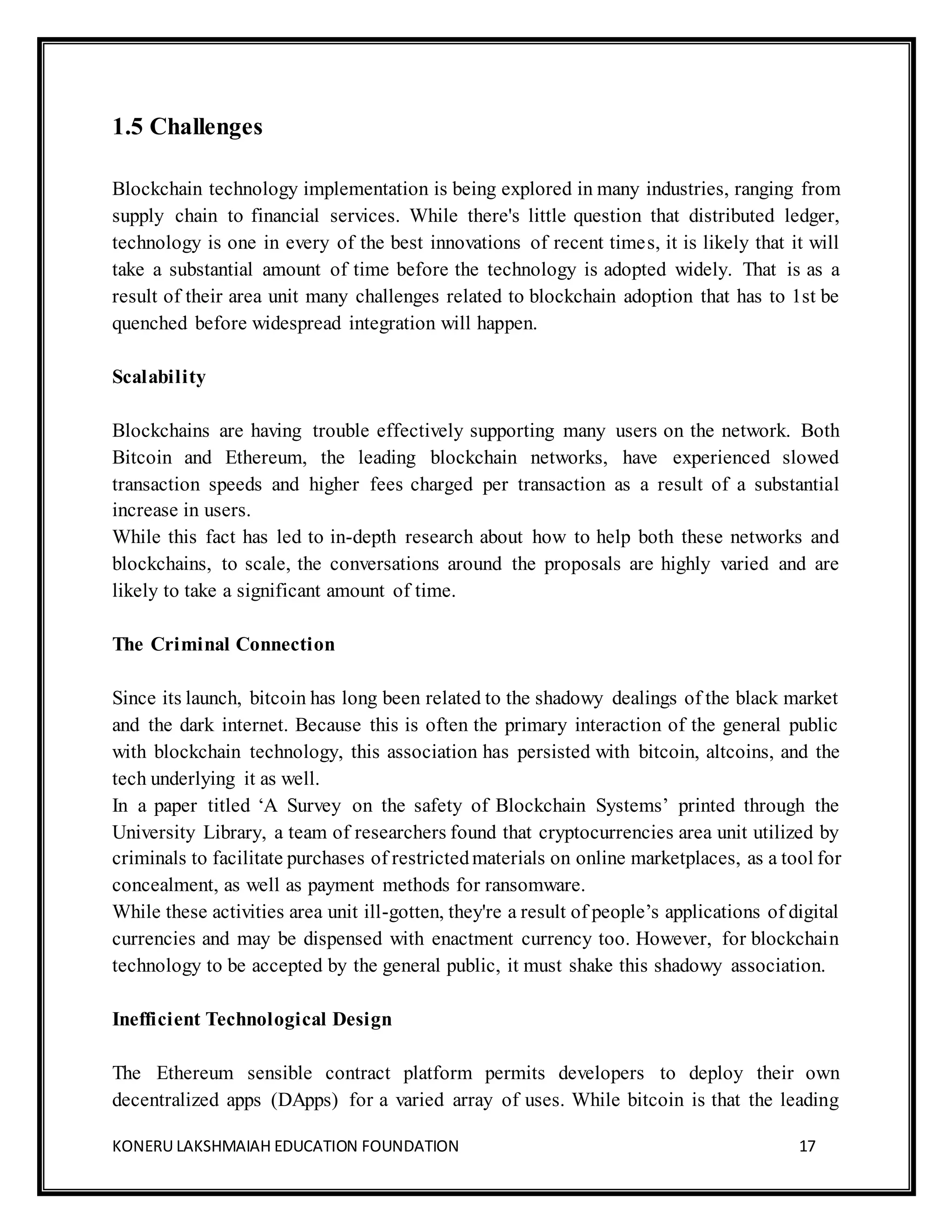
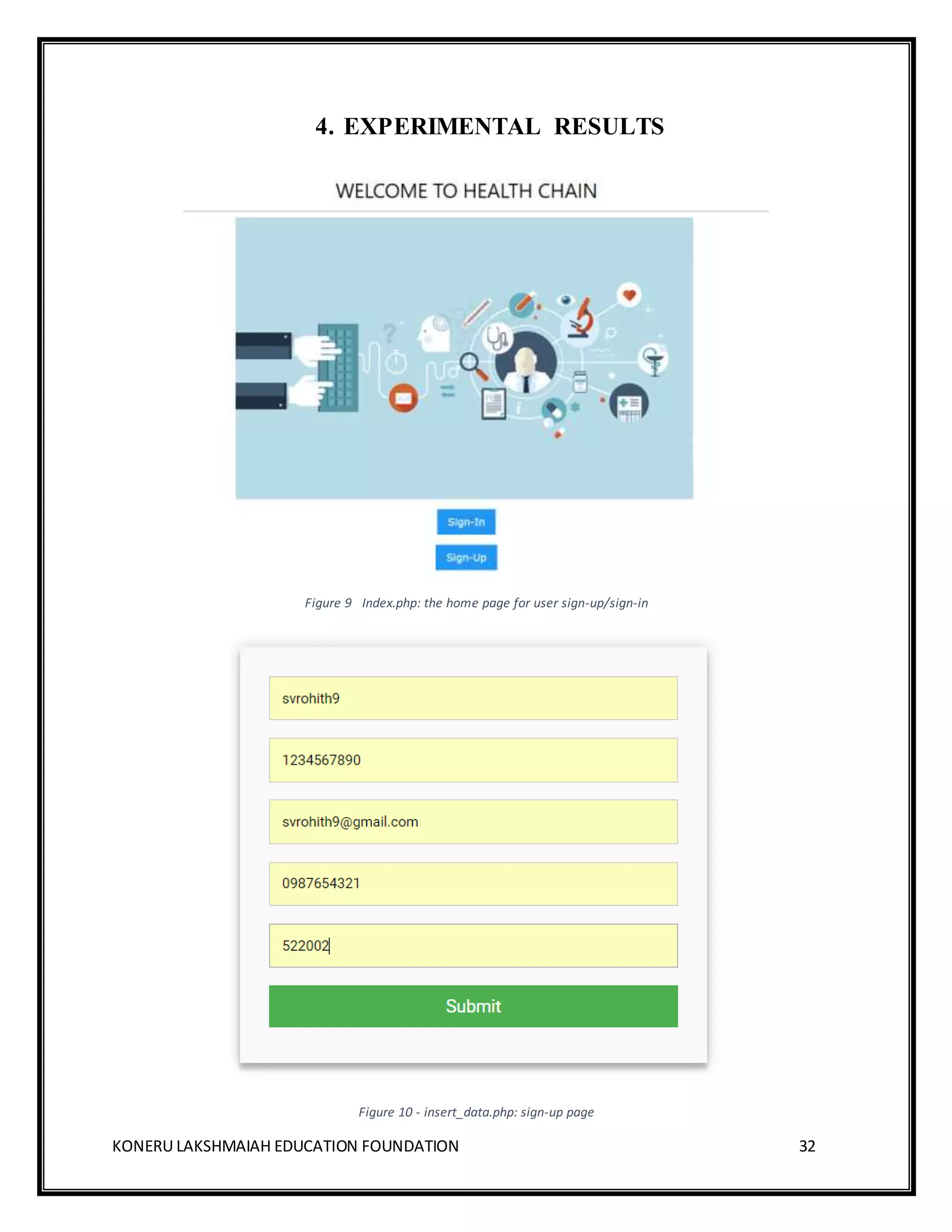
3.3 Hashing Techniques
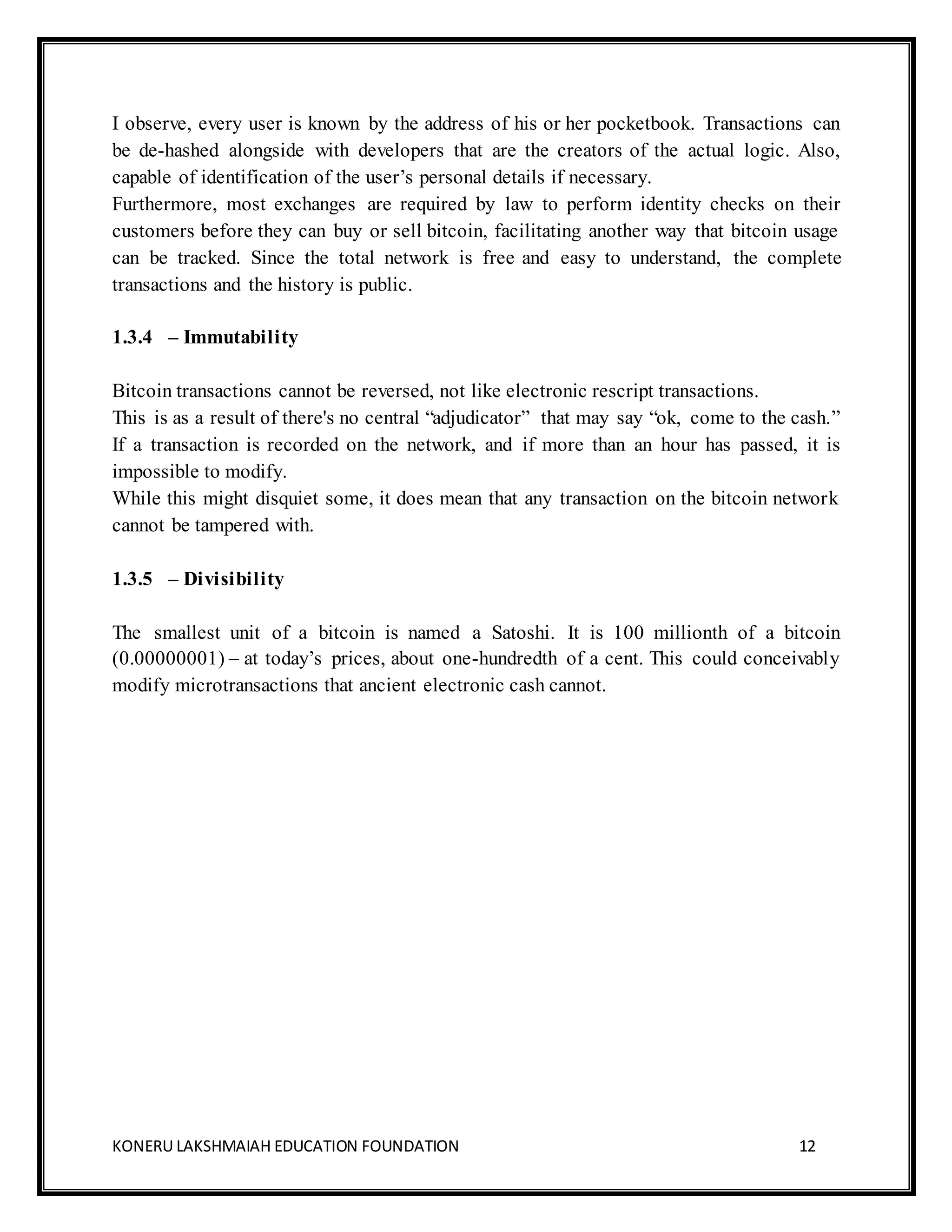
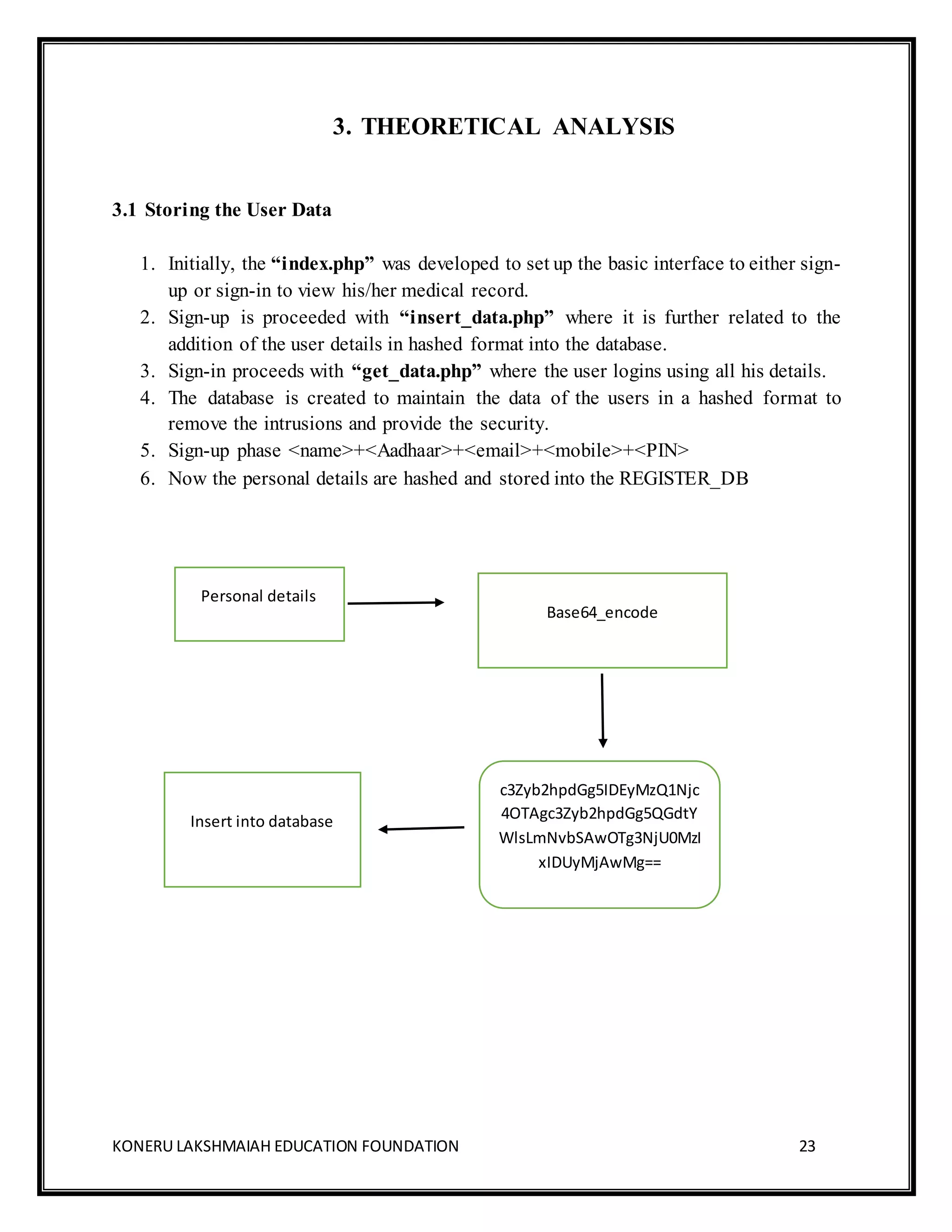
3.3.1 BASE64_ENCODING
1. It takes 3 bytes and each byte consists of 8 bits.
2. The encoding process is done using two different steps.
3. The first step is to convert 3 bytes into 4 numbers of 6 bits. Each character in
ASCII standard consists of 7 bits.
4. Now the 4 individual six bits are calculated to produce 4 values, which is
later converted into corresponding values.
5. Corresponding values are [0-25] =[A-Z], [26-51] =[a-z], [52-61] = [0-
9],62=’+’, 63=’/’.
Example
Figure 8
100110111010001011101001
1001101 100010 101010 101111
38 58 11 41
m6Lp](https://image.slidesharecdn.com/blockchainecomunezfinal-181221104140/75/Simple-Blockchain-Eco-System-for-medical-data-management-27-2048.jpg)
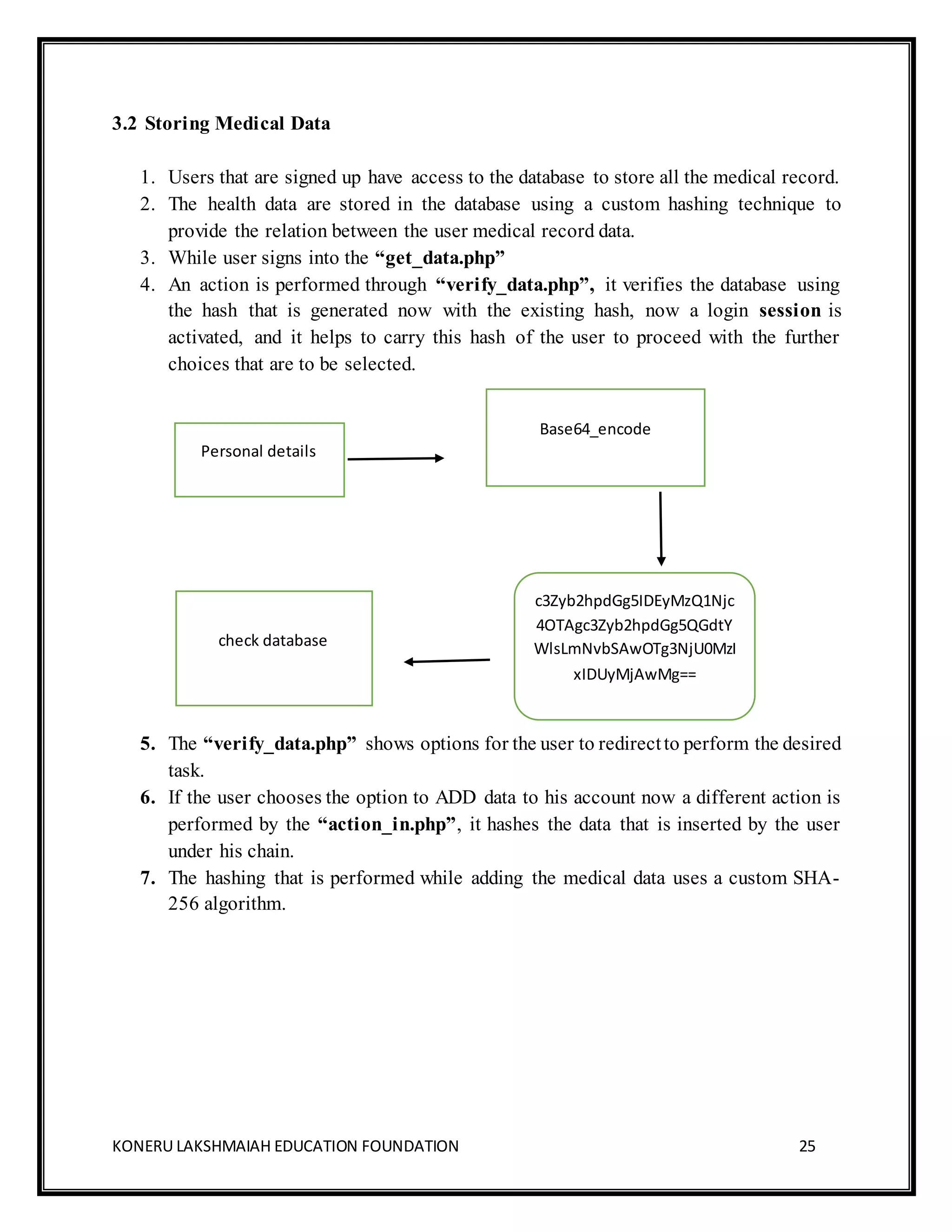
![KONERU LAKSHMAIAH EDUCATION FOUNDATION 29
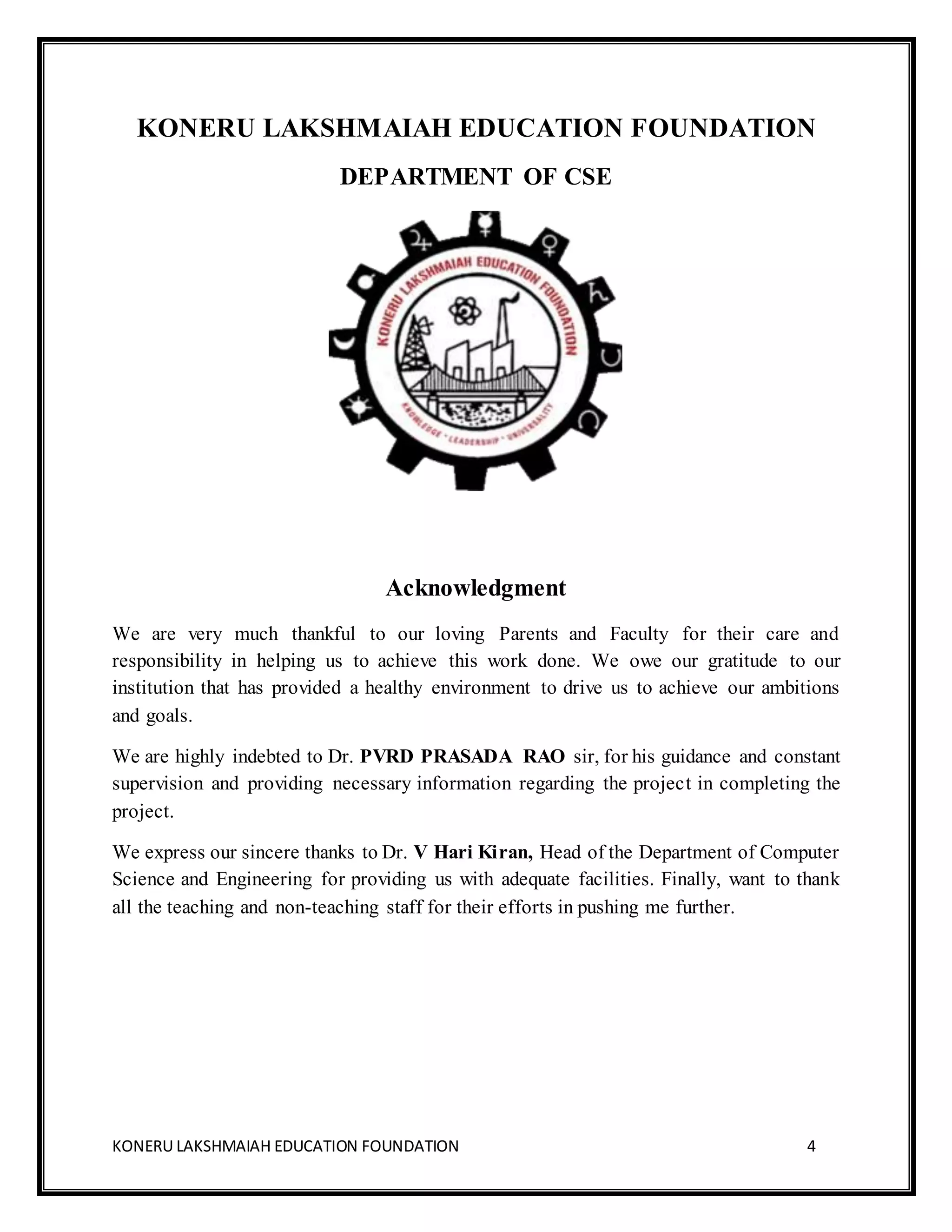
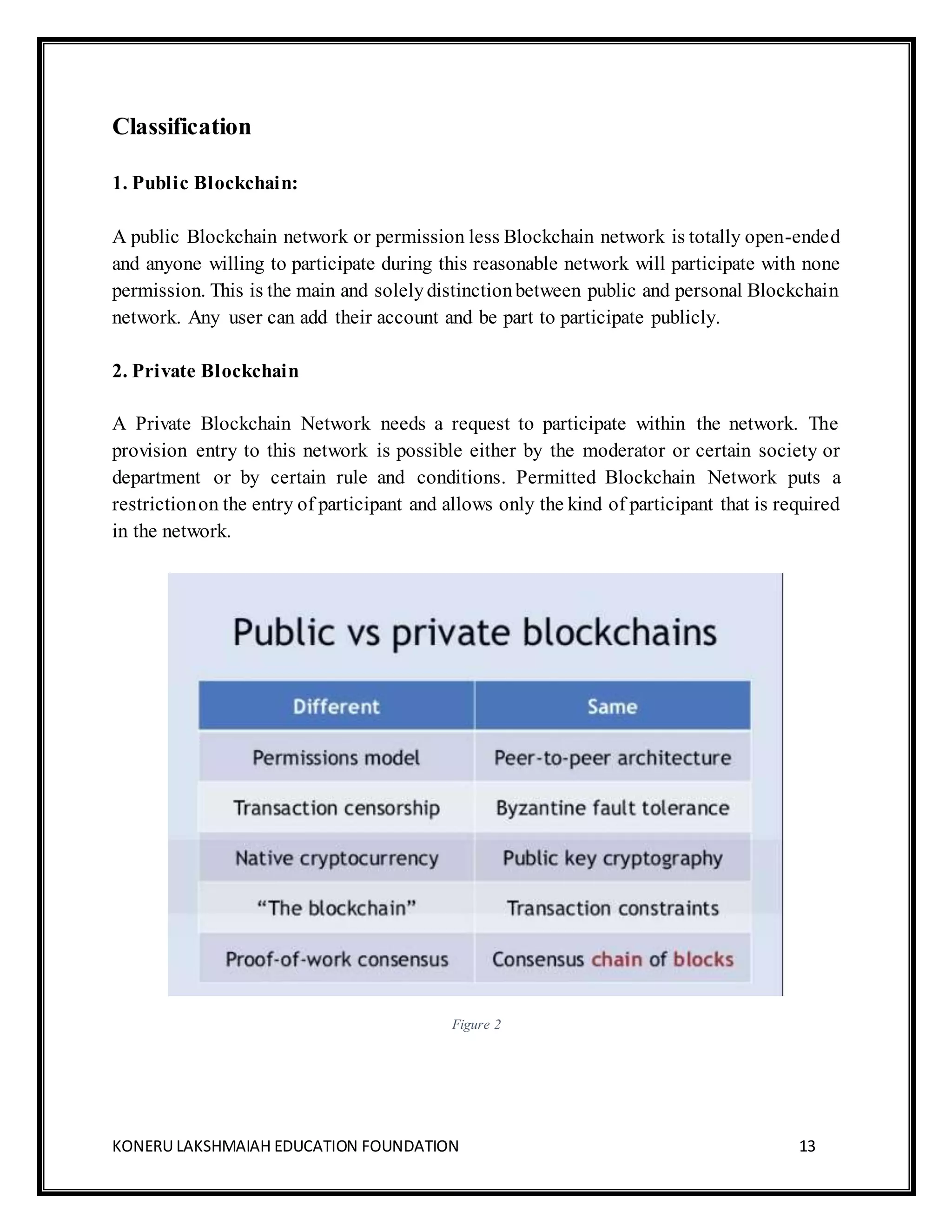
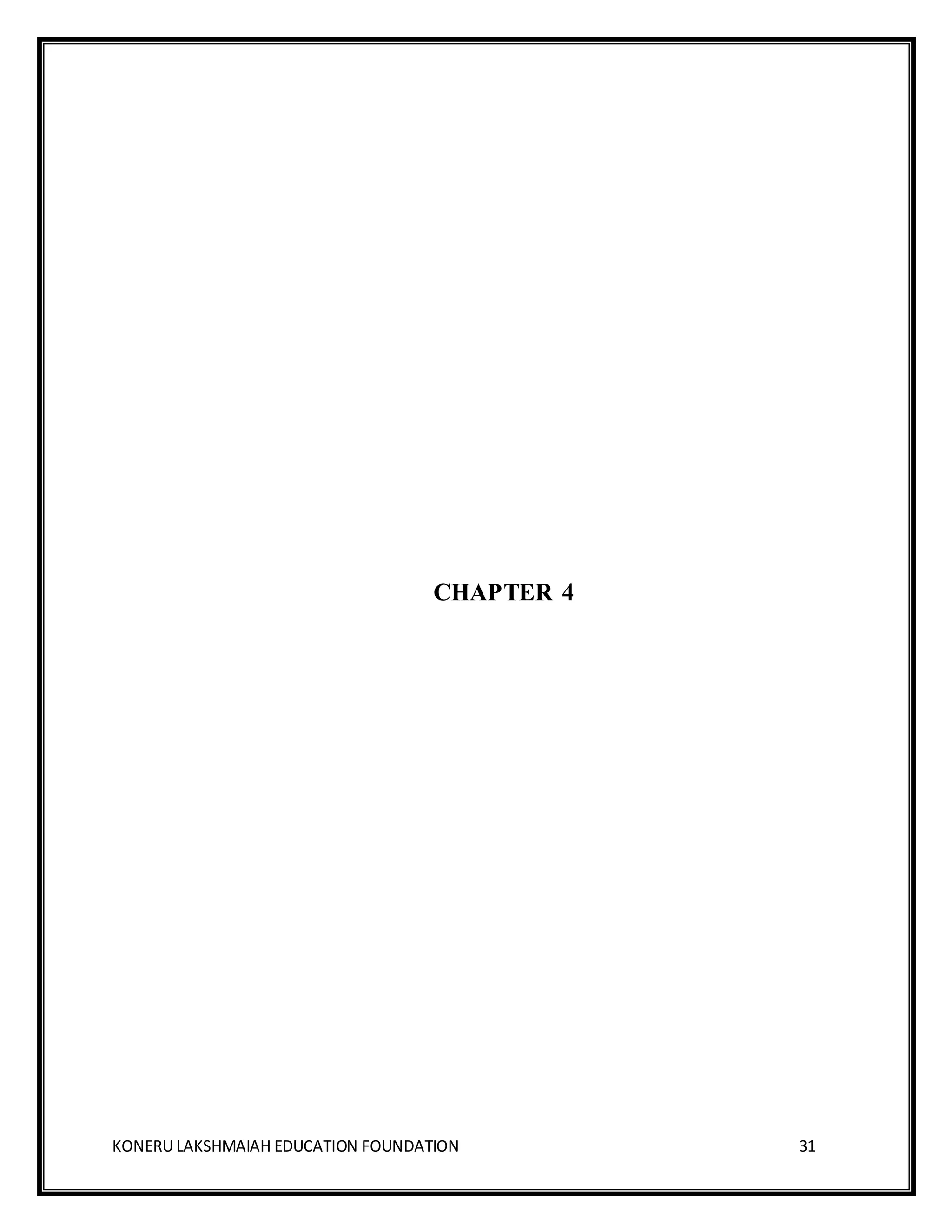
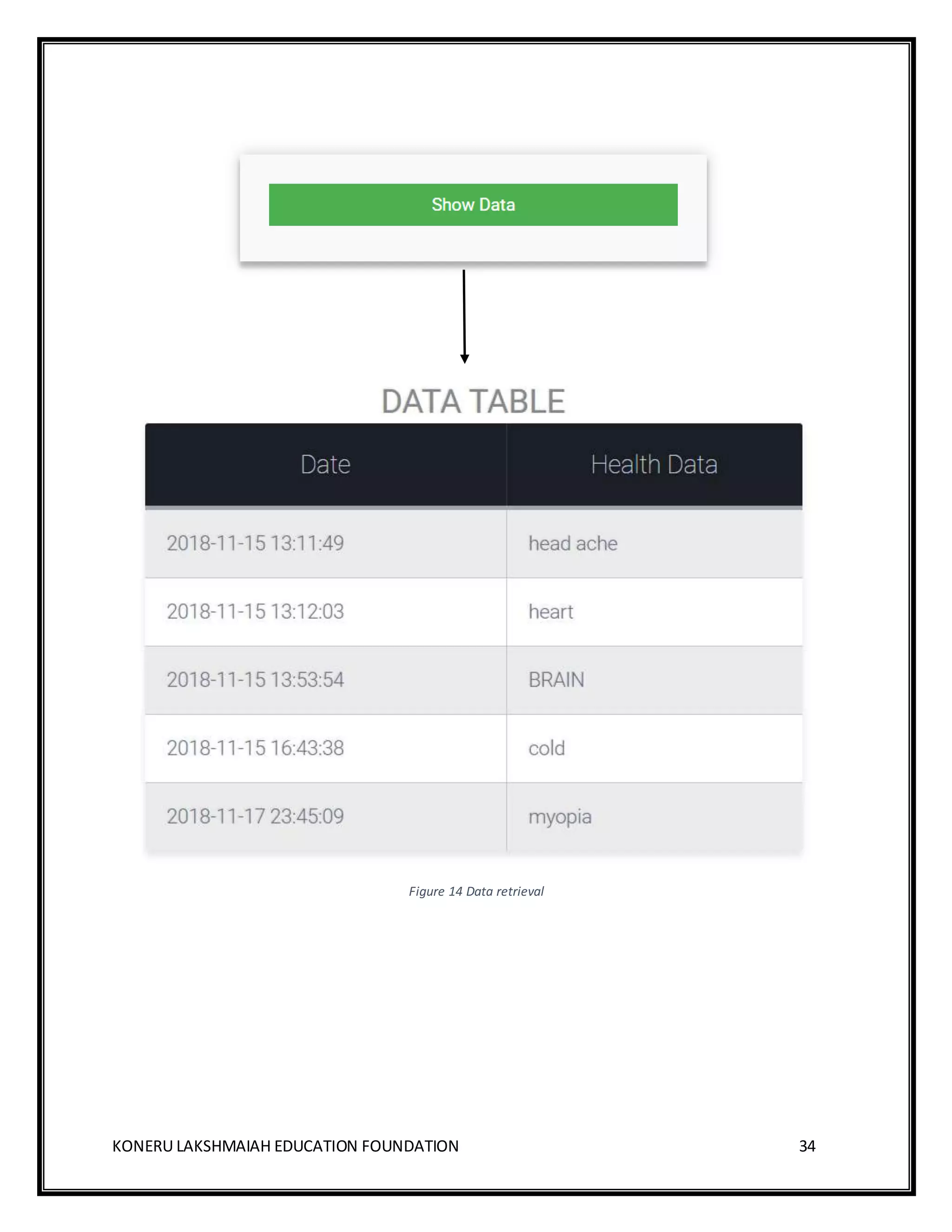
3.4 Data Retrieval
The Medical data is stored as text along with the default time-stamp that is
automatically generated during the transaction, the transaction id isgenerated during
the insertion query.
$var=$_SESSION['id'];
//echo$var;
include 'includes/connect_db.php';
//echo$data;
$i=0;
$ans=1;
//echo$ans;
while($ans==1)
{
$encr=hash('sha256’, $i.$var);
$sql="SELECT * FROMhealth_datawhere trans_id='$encr';";
$res=mysqli_query($con,$sql);
if(mysqli_num_rows($res)>0)
{
while ($row=mysqli_fetch_assoc($res))
{
echo$row['time'];
echo $row['data'];
?>](https://image.slidesharecdn.com/blockchainecomunezfinal-181221104140/75/Simple-Blockchain-Eco-System-for-medical-data-management-29-2048.jpg)
![KONERU LAKSHMAIAH EDUCATION FOUNDATION 42
8. REFERENCES/BIBLIOGRAPHY
[1]. https://en.wikipedia.org/wiki/Blockchain
[2]. https://mastanbtc.github.io/blockchainnotes
[3]. https://blockchainhub.net/blockchains-and-distributed-ledger-technologies-in-general
[4]. A Case Study for Blockchain in Healthcare: “MedRec” prototype for electronic health
records and medical research data White Paper Ariel Ekblaw, Asaph Azaria, John D. Halamka,
Andrew Lippman https://dci.mit.edu/research/blockchain-medical-records
[5]. BigchainDB: A Scalable Blockchain Database. Marques R, Müller A, De Jonghe D,
McConaghy T, McMullen G, Henderson R, Bellemare S, Granzotto A. '17.
[6]. Applications of Blockchain Technology beyond Cryptocurrency- Annals of Emerging
Technologies in Computing (AETiC) https://arxiv.org/ftp/arxiv/papers/1801/1801.03528.pdf
[7]. https://www.investopedia.com/terms/b/blockchain.asp
[8]. https://blockgeeks.com/guides/what-is-blockchain-technology/
[9]. https://www.cbinsights.com/research/what-is-blockchain-technology
[10]. https://blockgeeks.com/guides/what-is-blockchain-technology](https://image.slidesharecdn.com/blockchainecomunezfinal-181221104140/75/Simple-Blockchain-Eco-System-for-medical-data-management-42-2048.jpg)