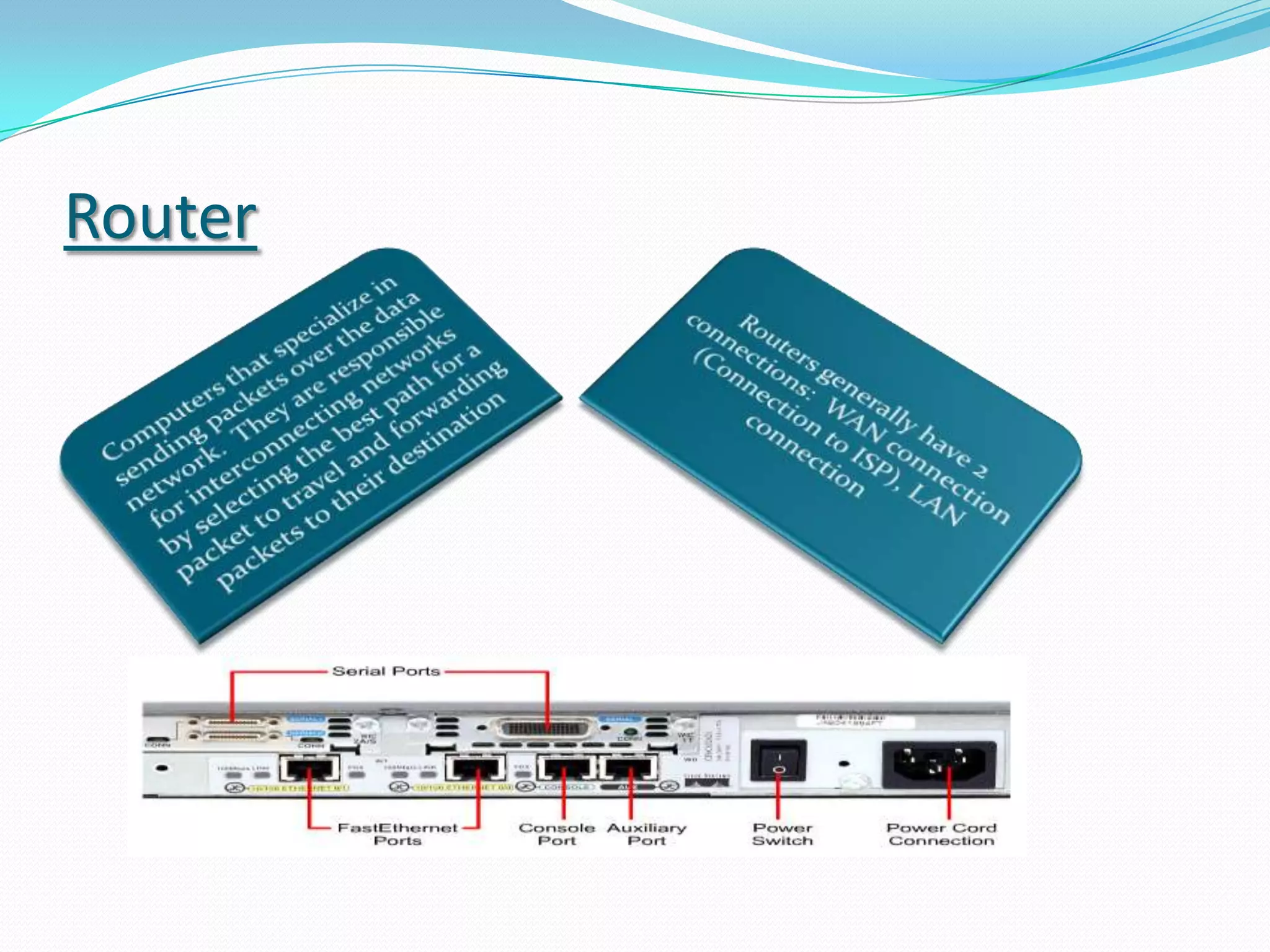
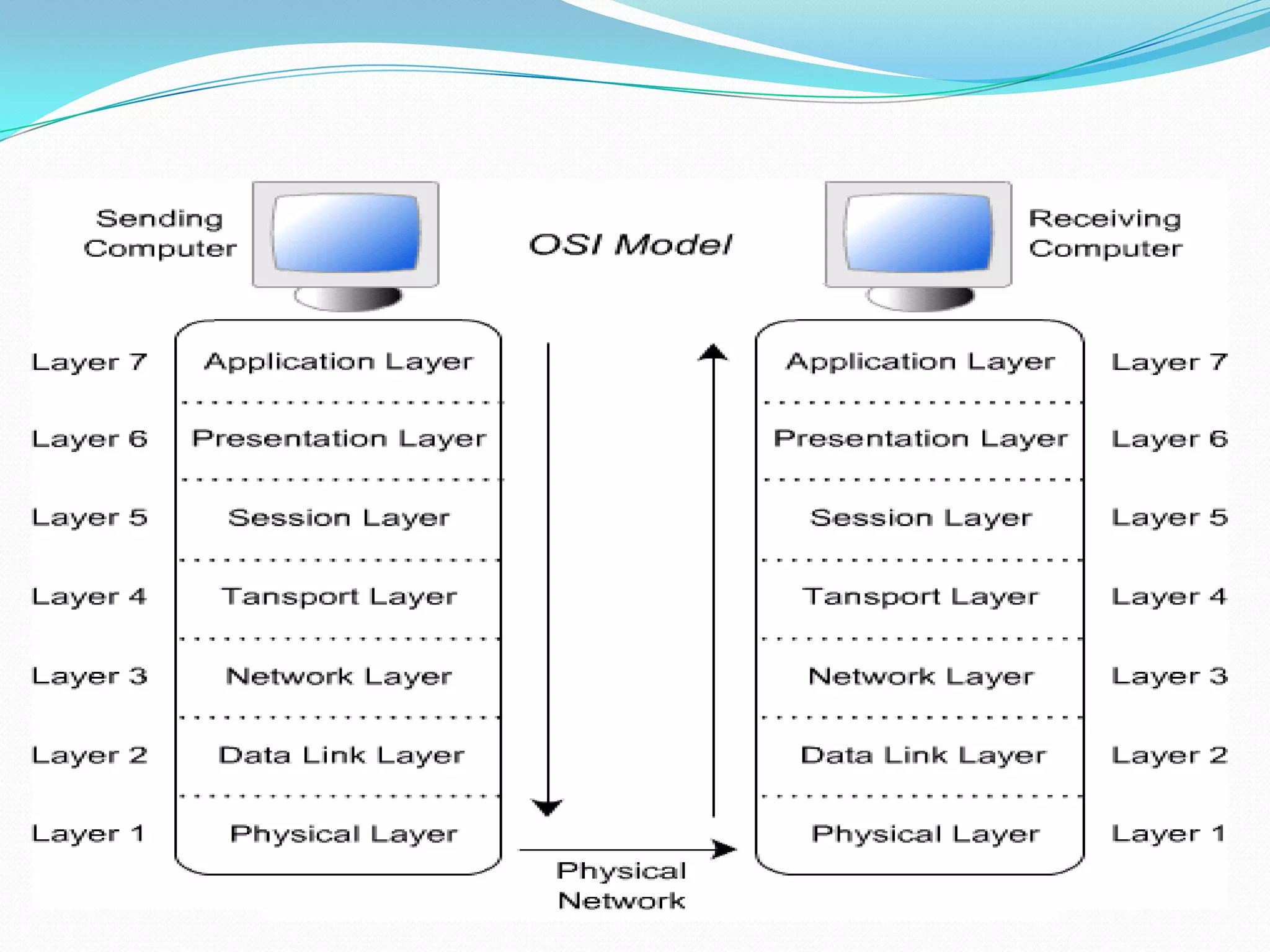
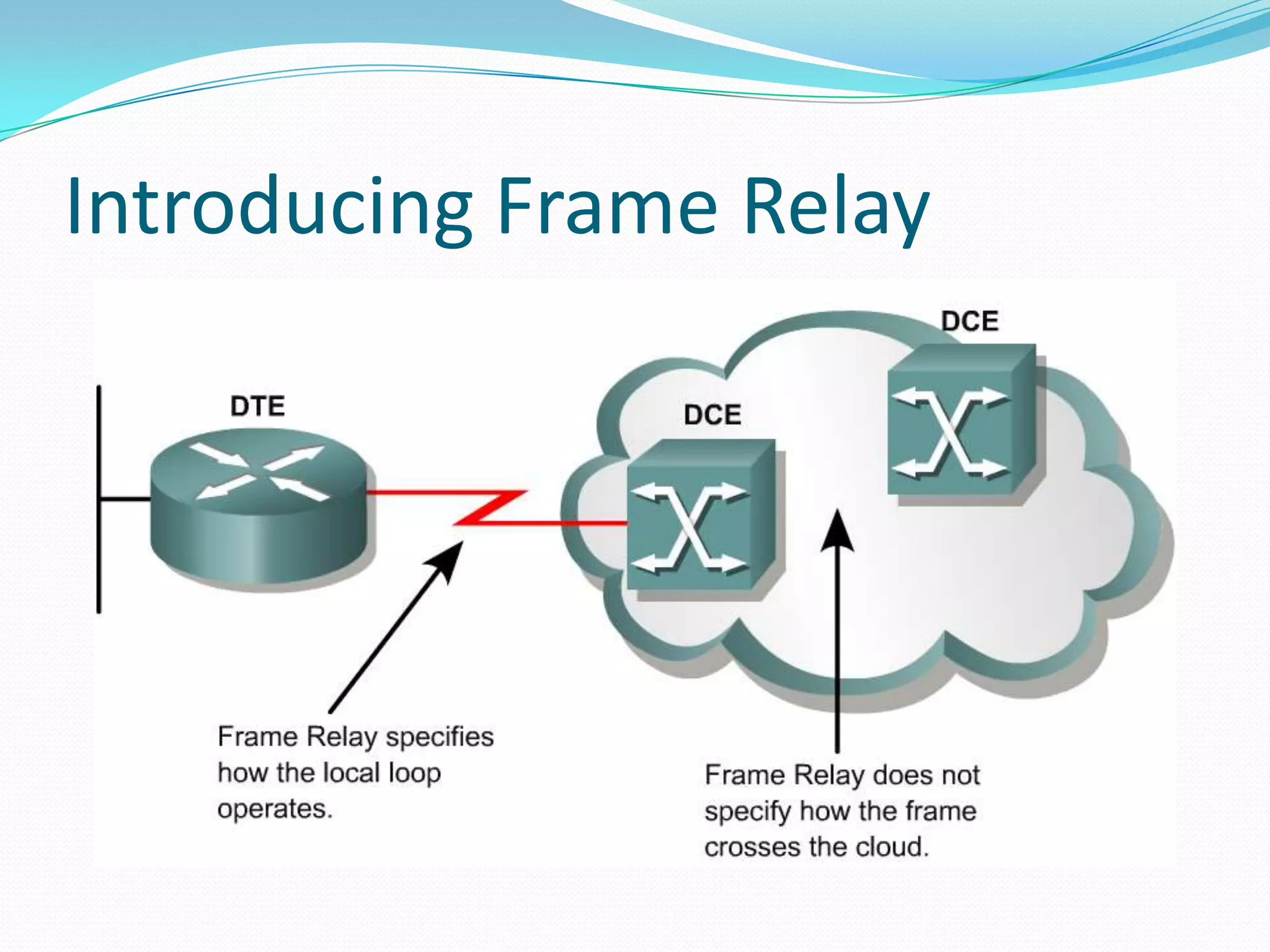
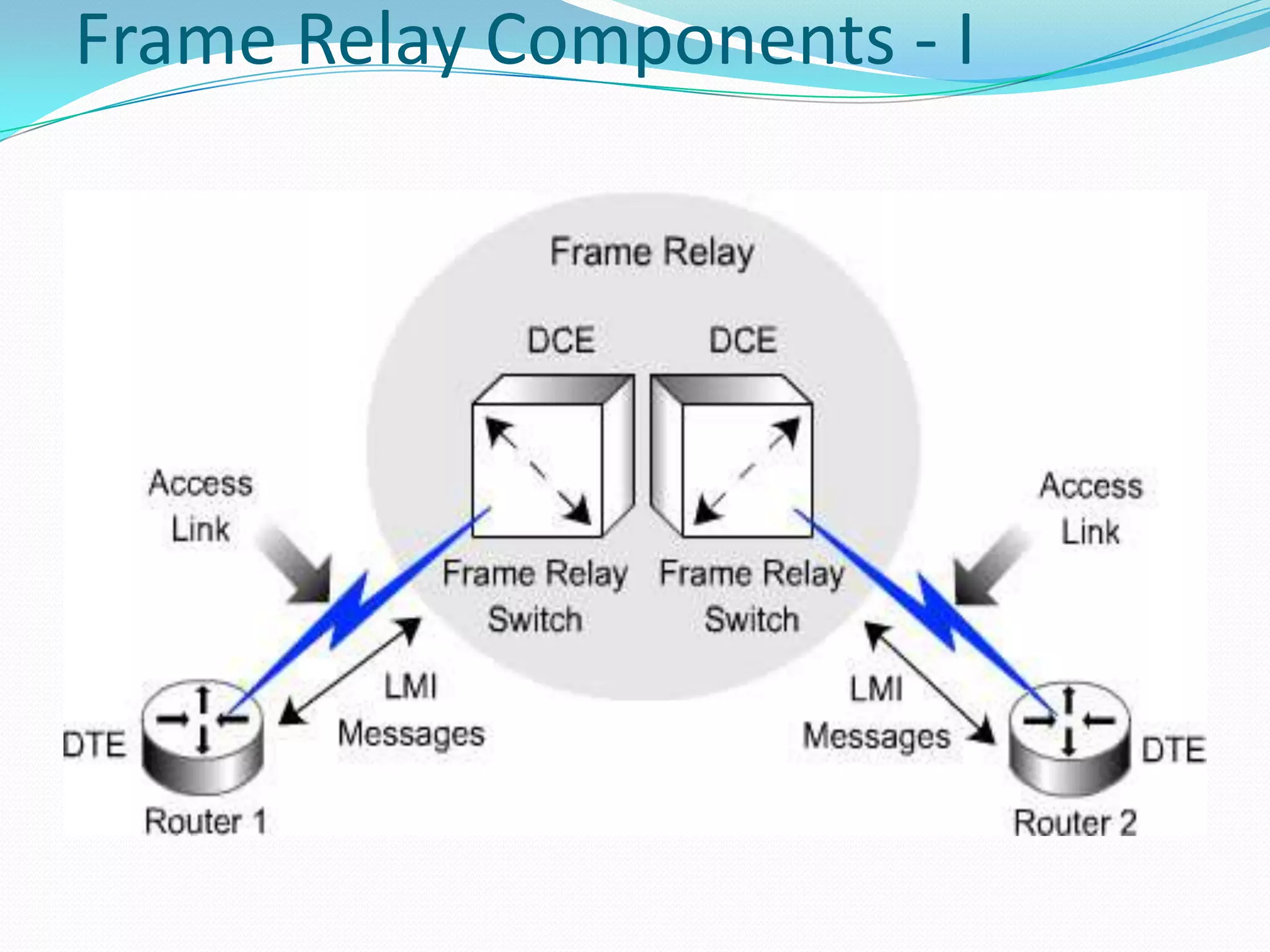
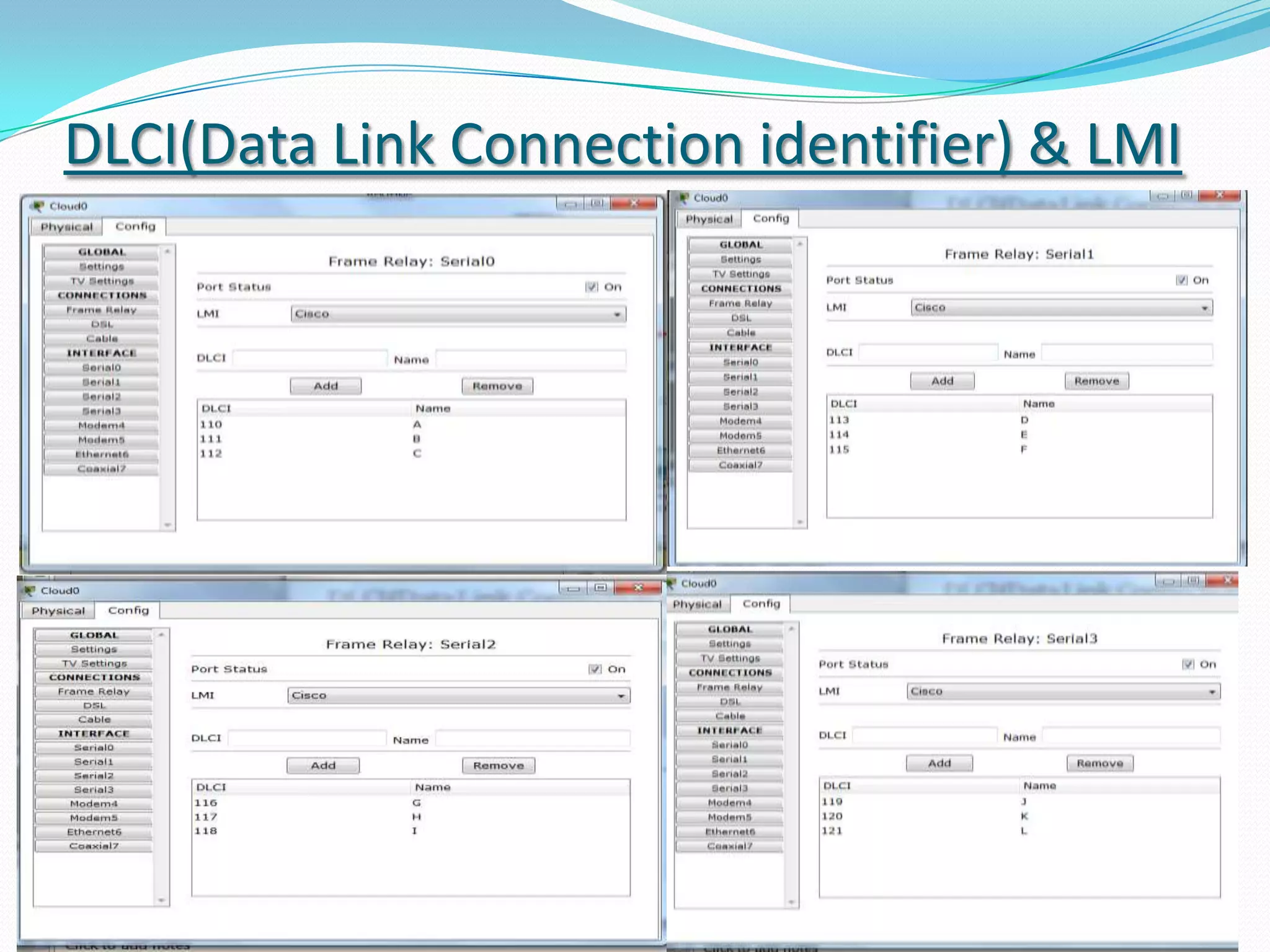
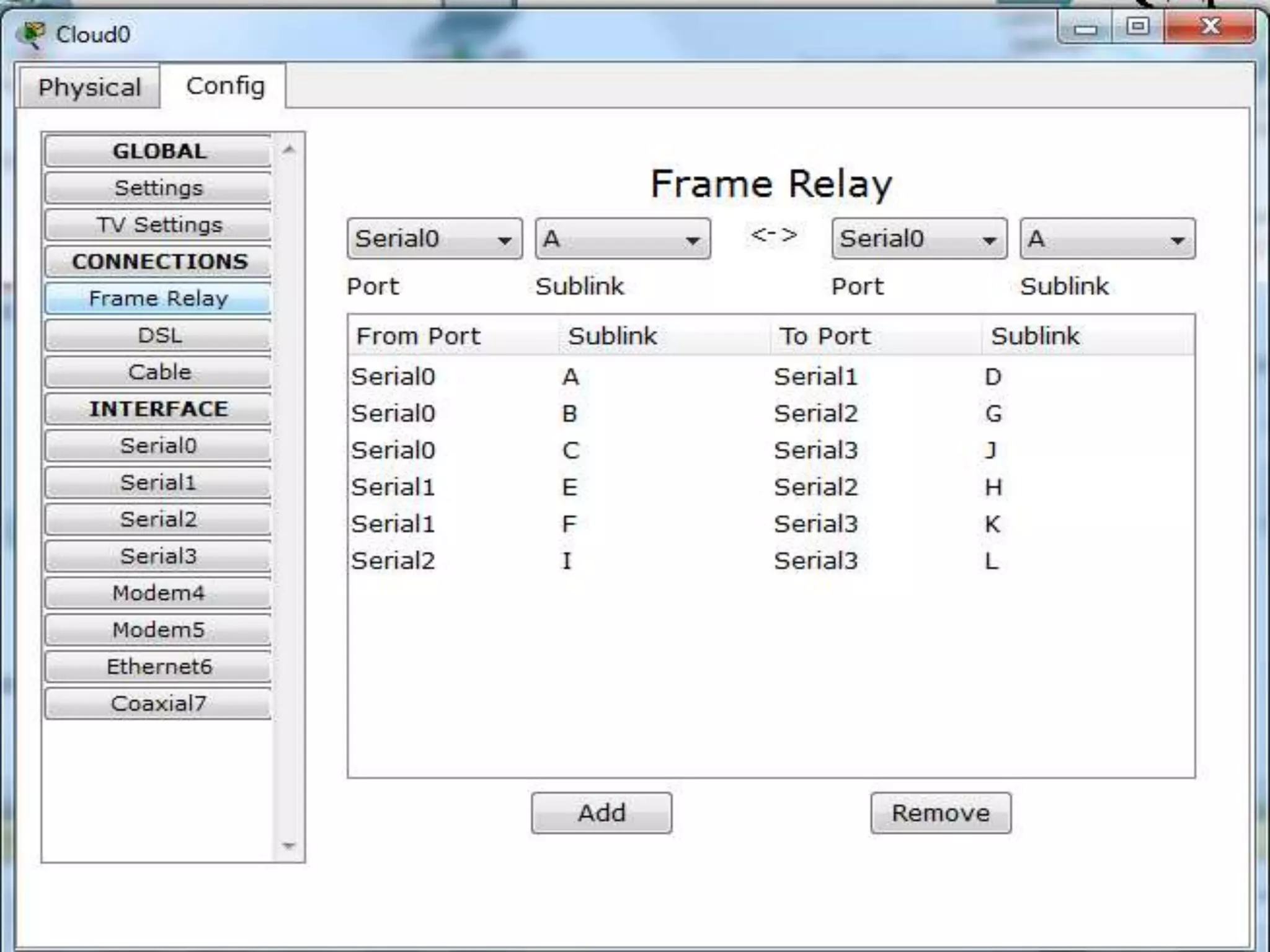
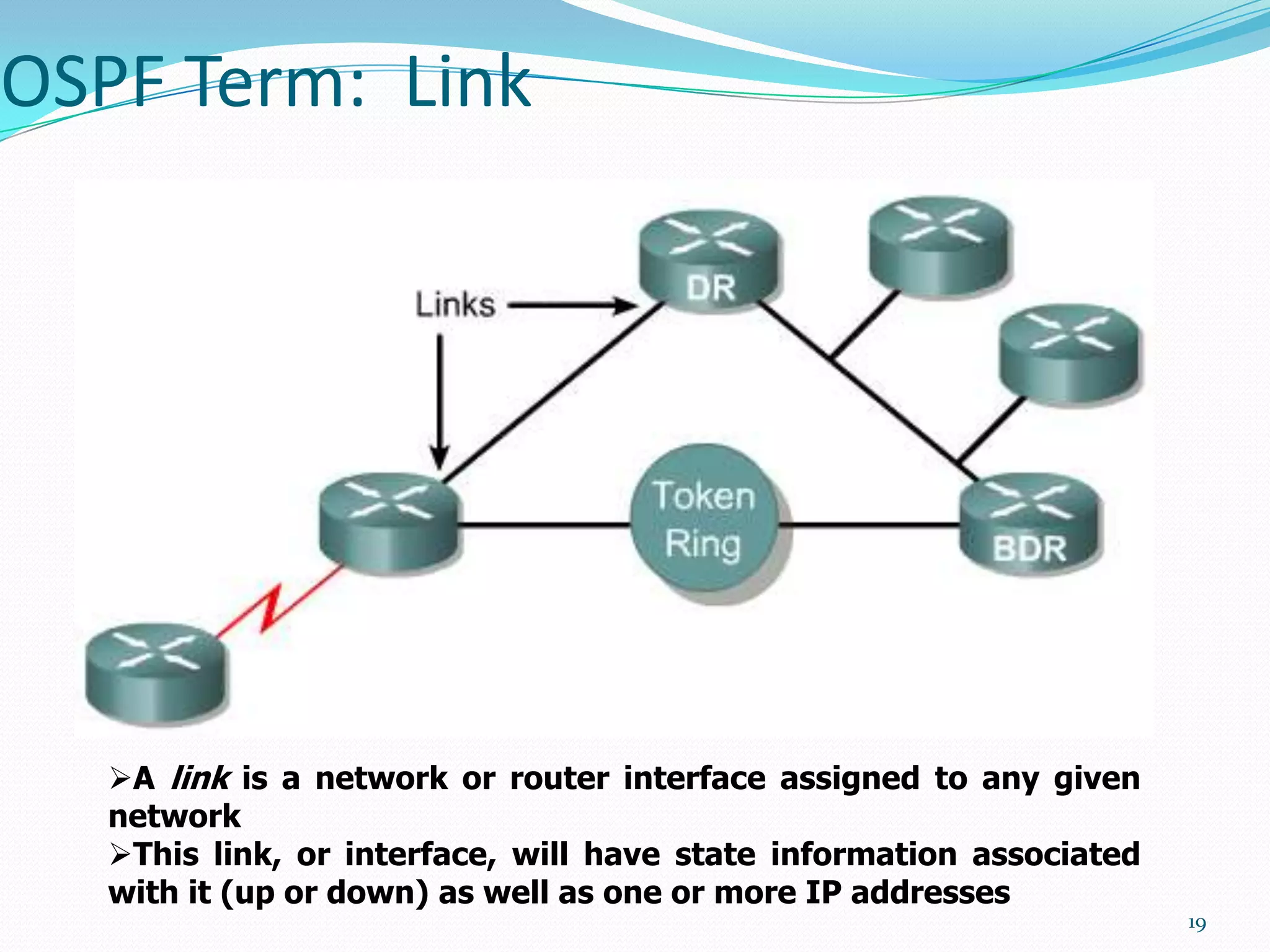
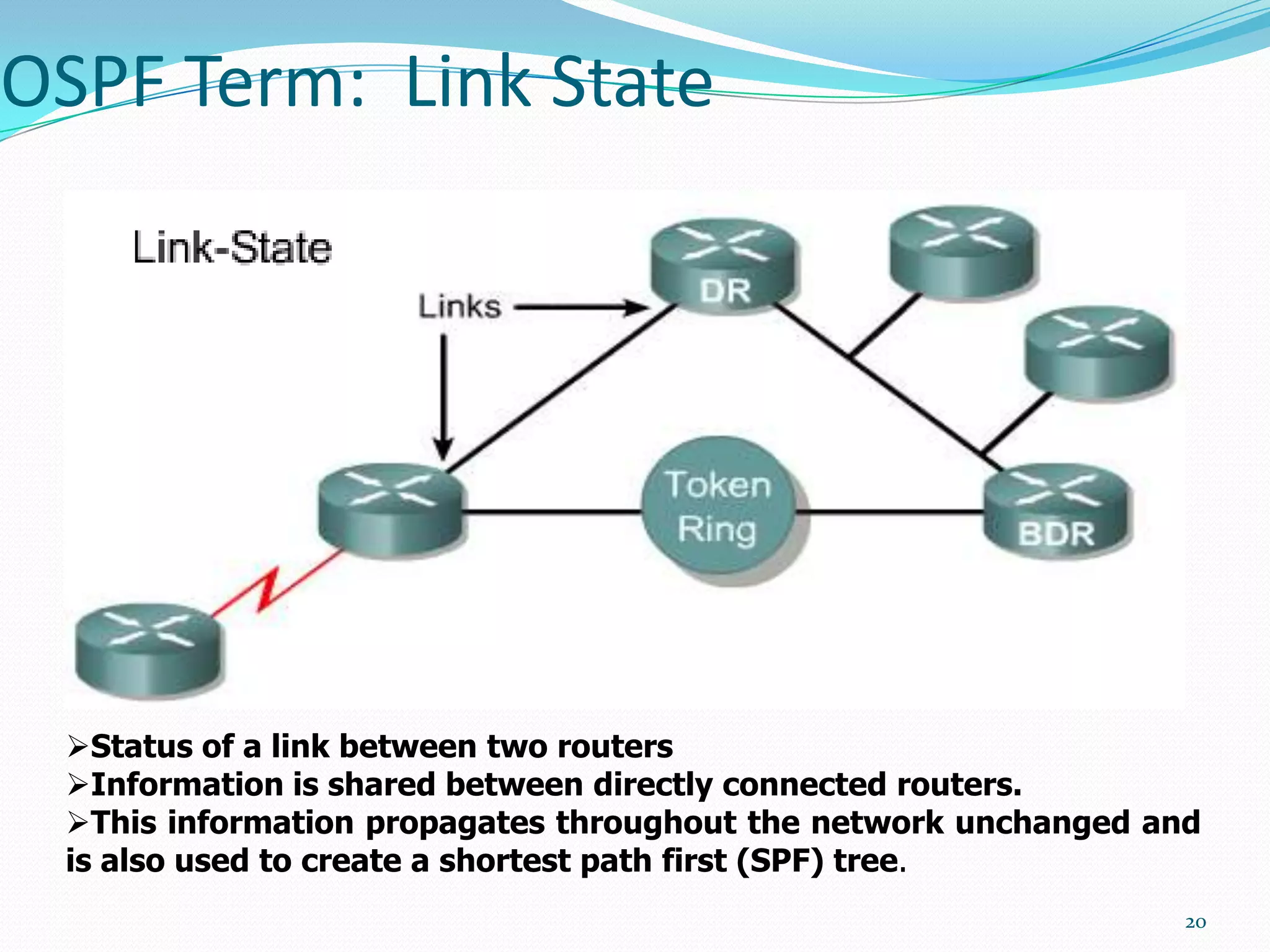
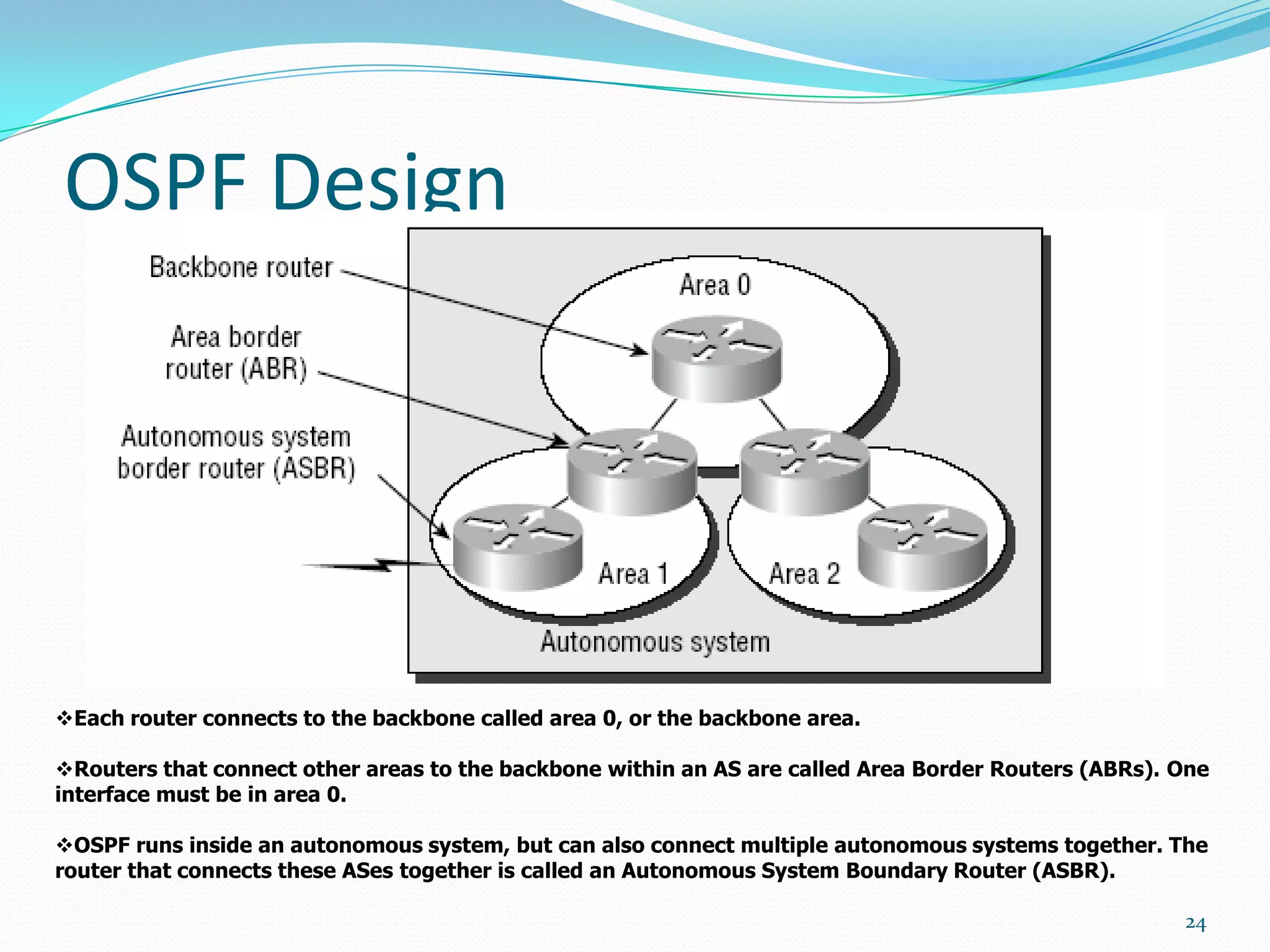
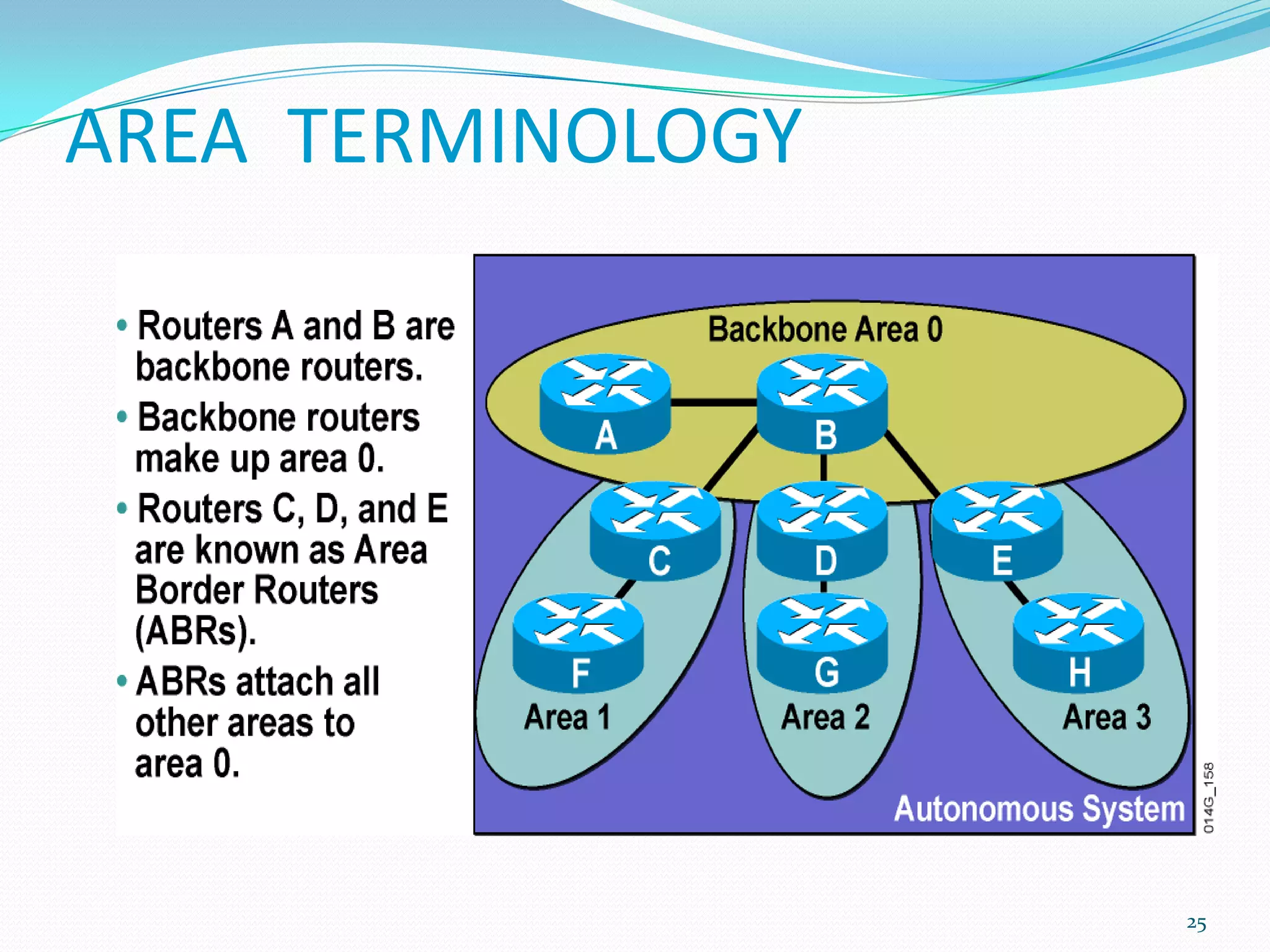
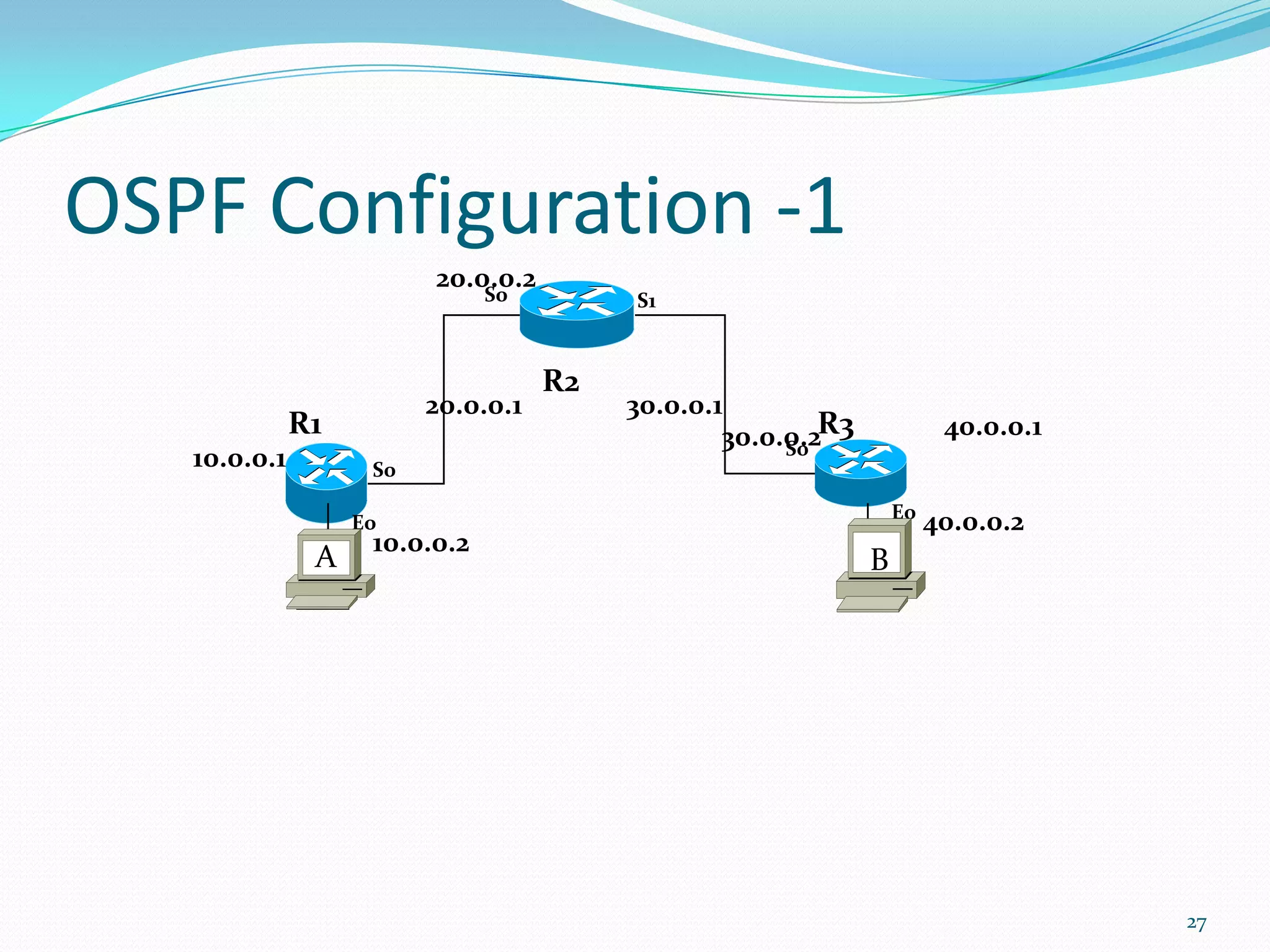
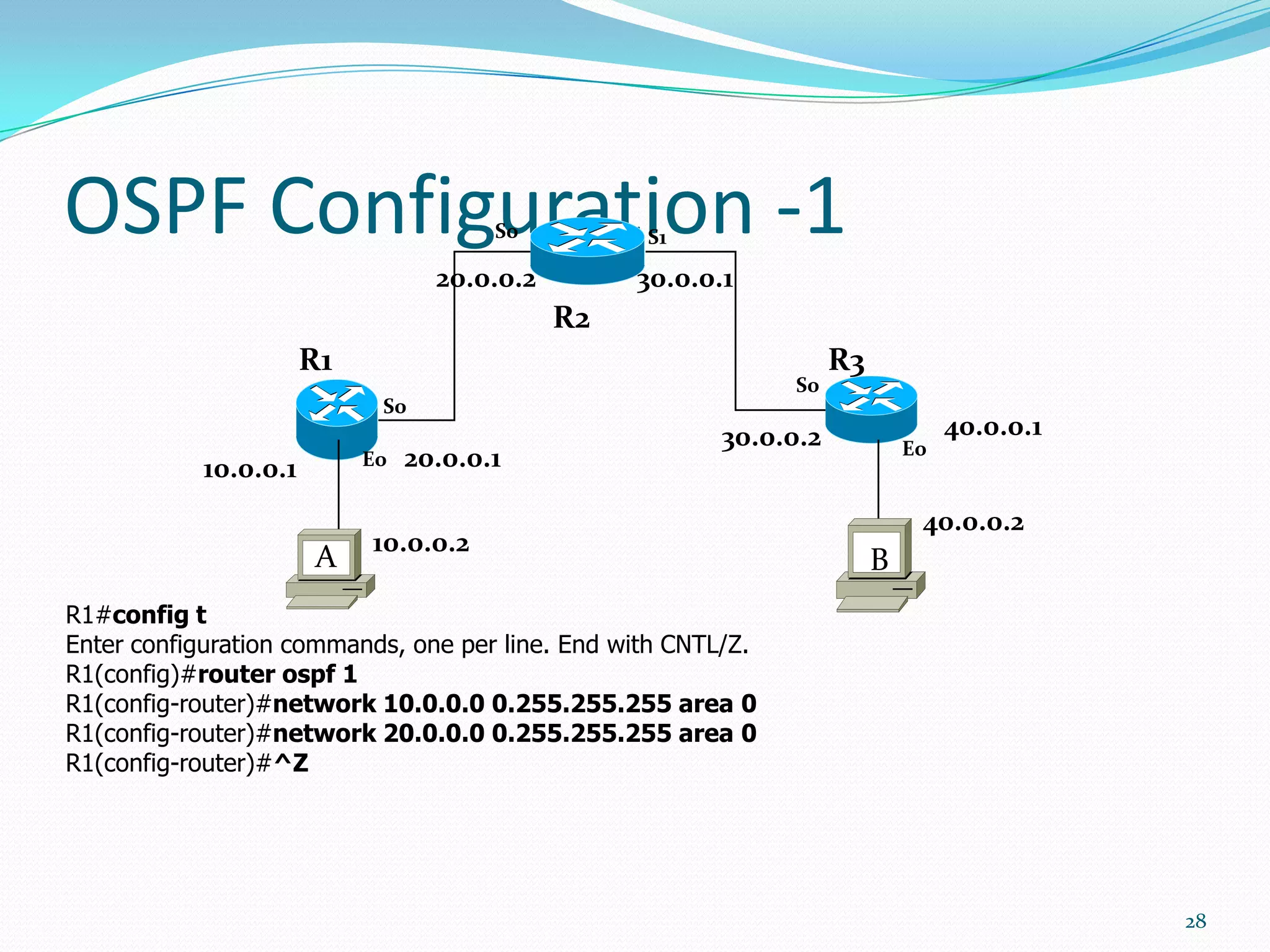
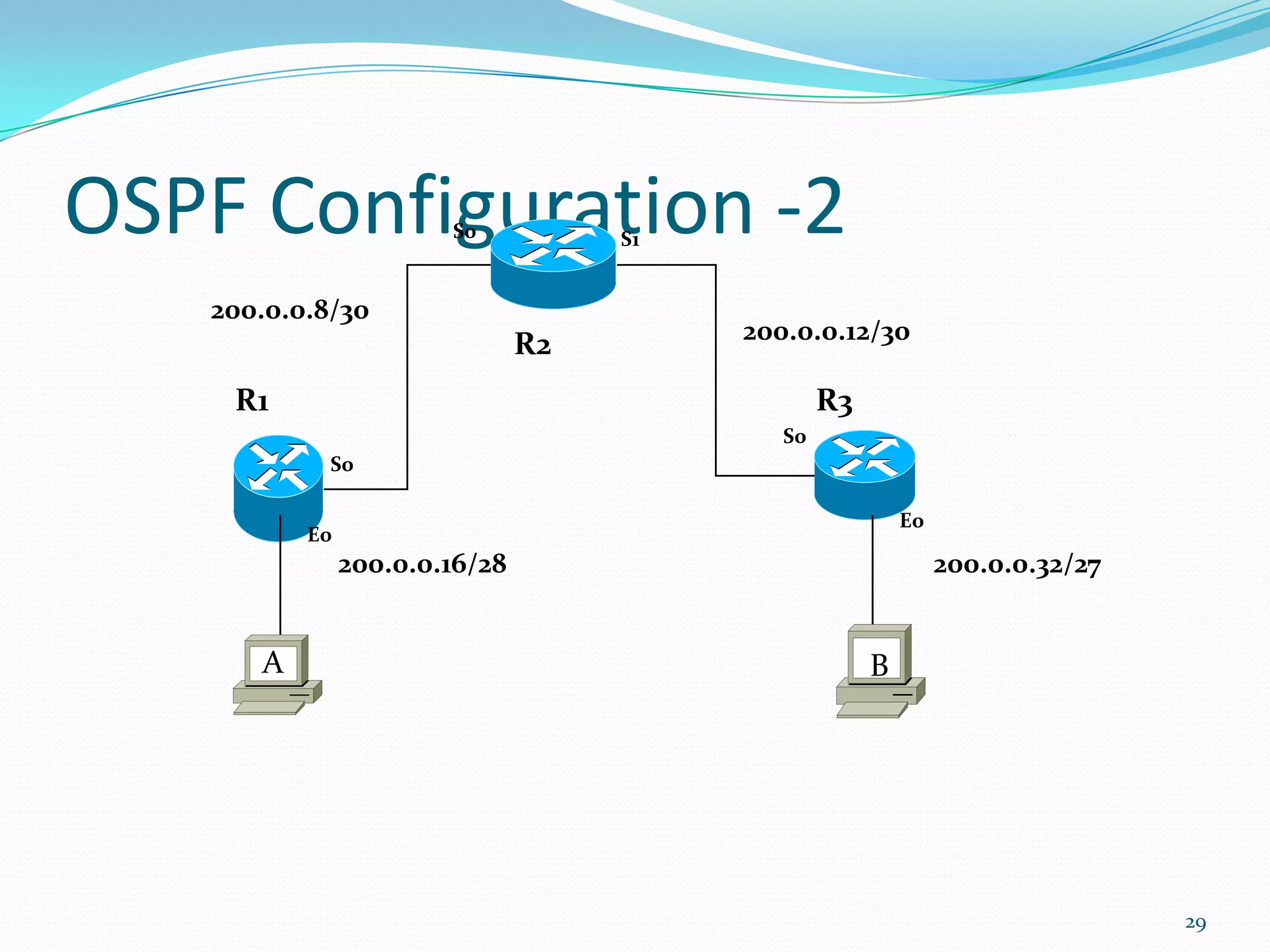
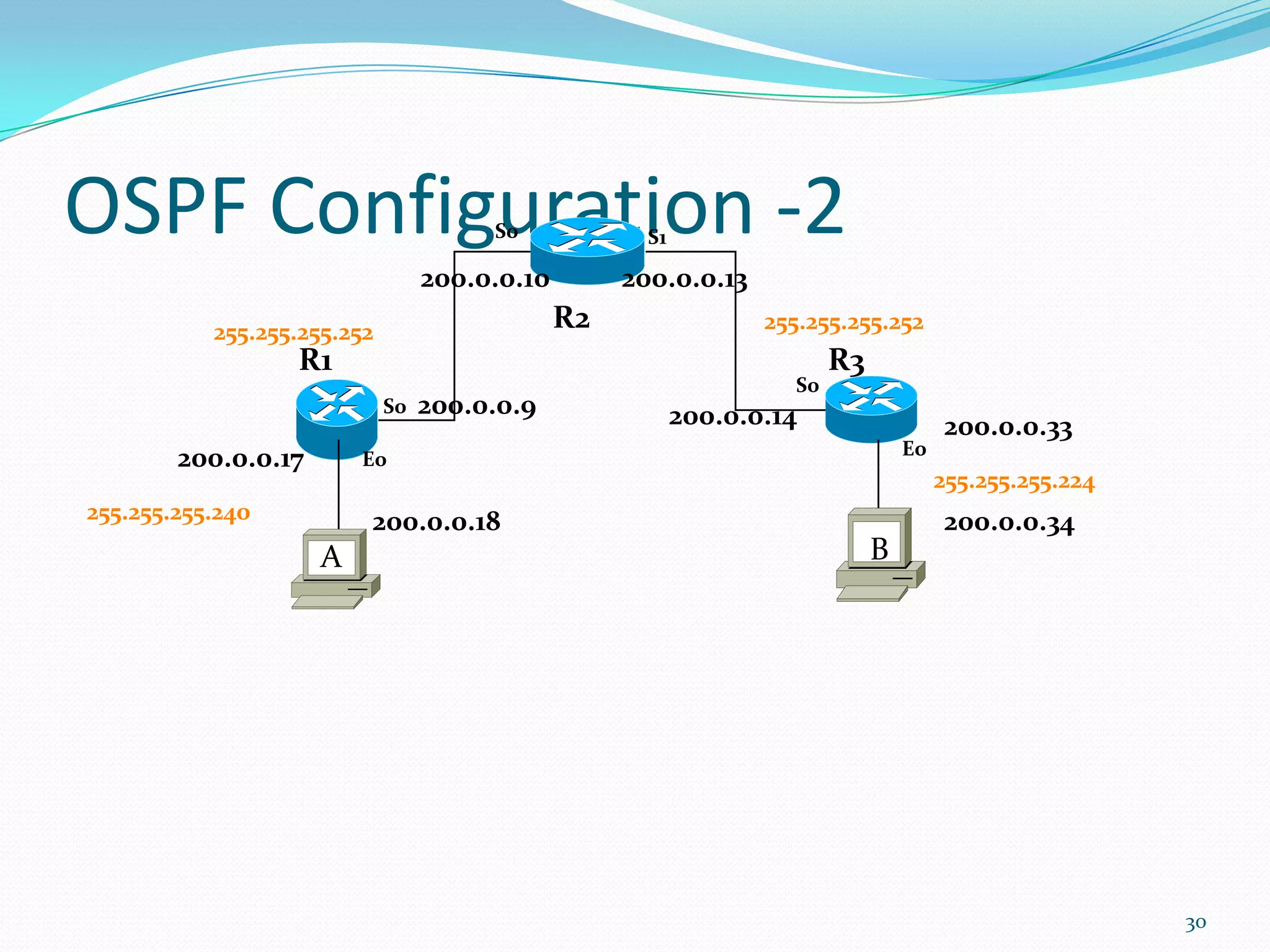
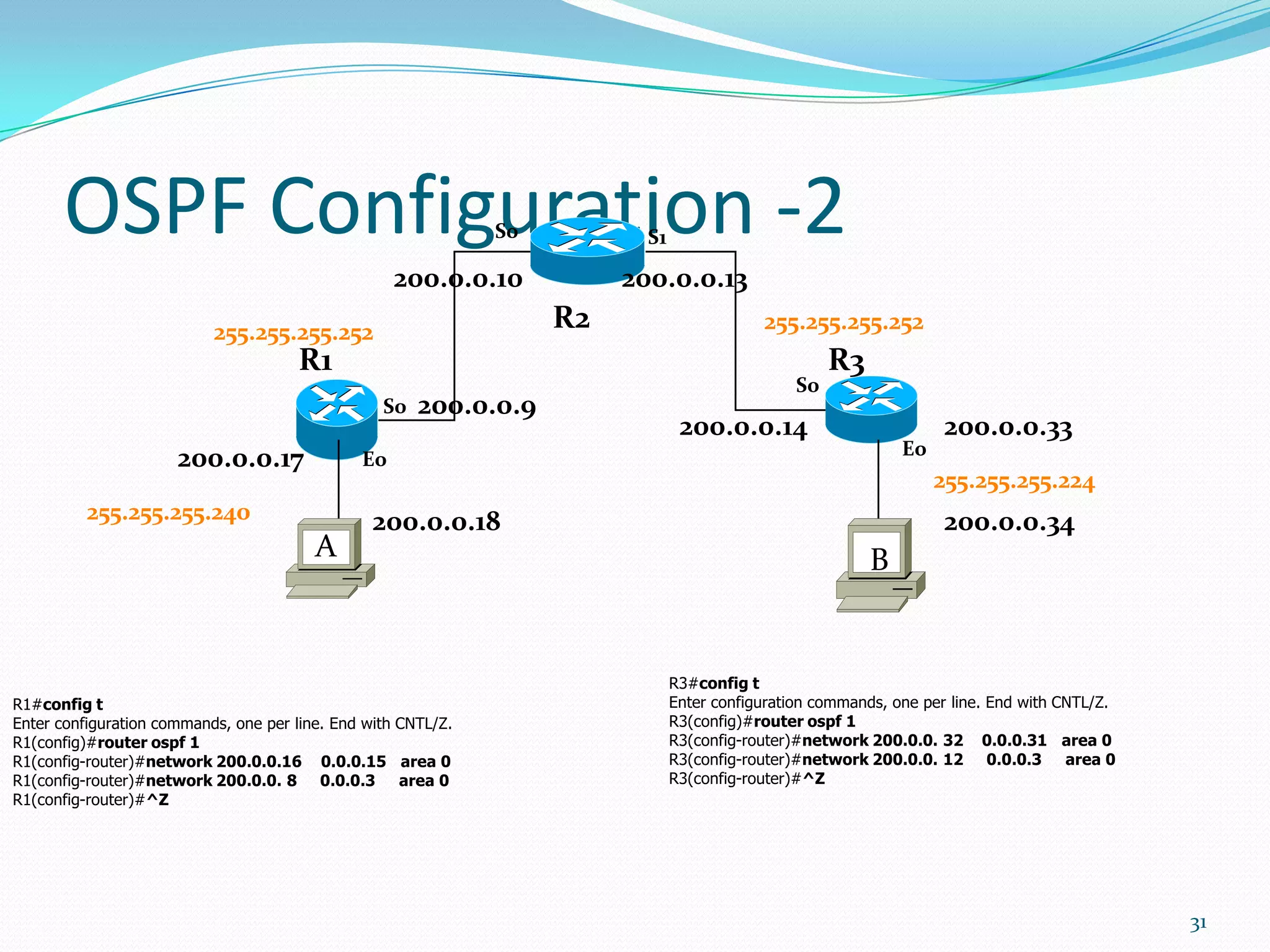
This document discusses networking techniques including Frame Relay and OSPF. It begins with an introduction to Frame Relay, describing its components and operation at the data link layer. It then explains OSPF, including its use of the Dijkstra algorithm for routing, key terms like links and routers, and how it is configured on Cisco devices. The presentation provides an overview of these common wide area network protocols.