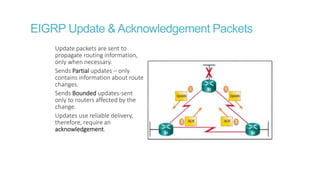
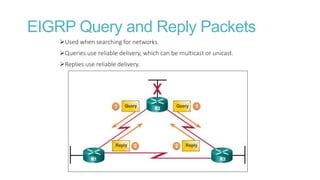
EIGRP is an advanced distance vector routing protocol created by Cisco that uses the Diffusing Update Algorithm to calculate paths and backup paths. It establishes neighbor adjacencies, uses reliable transport for packet delivery, and sends partial and bounded updates only when there are changes.











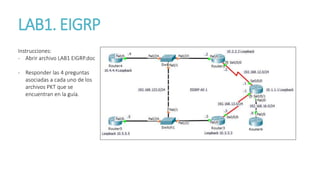
![Verificación
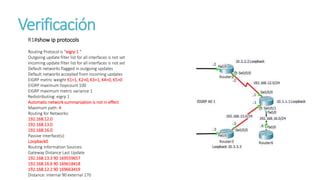
R1#show ip route
Codes: C - connected, S - static, I - IGRP, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type 1, E2 - OSPF external type 2, E - EGP
i - IS-IS, L1 - IS-IS level-1, L2 - IS-IS level-2, ia - IS-IS inter area
* - candidate default, U - per-user static route, o - ODR
P - periodic downloaded static route
Gateway of last resort is not set
10.0.0.0/24 is subnetted, 4 subnets
C 10.1.1.0 is directly connected, Loopback0
D 10.2.2.0 [90/2297856] via 192.168.12.2, 00:09:03, Serial0/0/0
D 10.3.3.0 [90/2297856] via 192.168.13.3, 00:10:19, Serial0/0/1
D 10.6.6.0 [90/156160] via 192.168.16.6, 00:09:29, FastEthernet0/0
C 192.168.12.0/24 is directly connected, Serial0/0/0
C 192.168.13.0/24 is directly connected, Serial0/0/1
C 192.168.16.0/24 is directly connected, FastEthernet0/0
D 192.168.123.0/24 [90/2172416] via 192.168.13.3, 00:10:19, Serial0/0/1
[90/2172416] via 192.168.12.2, 00:08:52, Serial0/0/0](https://image.slidesharecdn.com/eigrpsinpreguntas-160917043249/85/Eigrp-17-320.jpg)