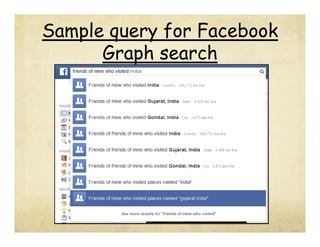
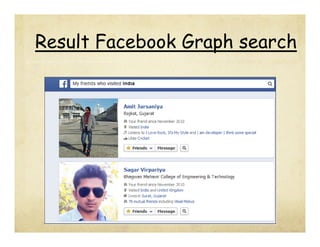
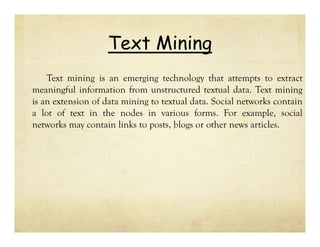
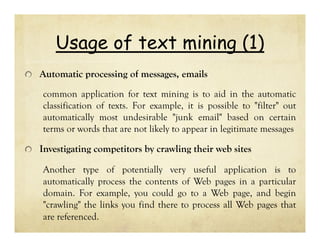
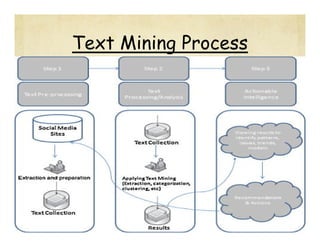
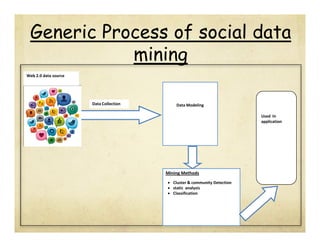
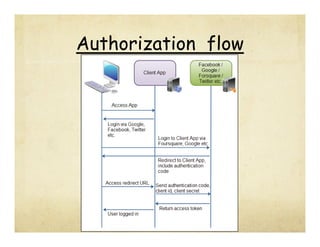
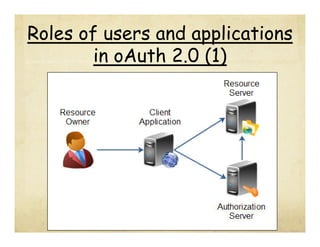
This document discusses social data mining. It begins by defining data, information, and knowledge. It then defines data mining as extracting useful unknown information from large datasets. Social data mining is defined as systematically analyzing valuable information from social media, which is vast, noisy, distributed, unstructured, and dynamic. Common social media platforms are described. Graph mining and text mining are discussed as important techniques for social data mining. The generic social data mining process of data collection, modeling, and various mining methods is outlined. OAuth 2.0 authorization is also summarized as an important process for applications to access each other's data.


![References
[1] PritamGundecha, Huan Liu “Mining Social Media: A Brief
Introduction”, ISBN No 978-0-9843378-3-5
[2] Brain Amento, Loren Terveen , Will Hill “Experiments in Social
Data Mining”.
[3] Roosevelt C. Mosley Jr., FCAS, MAAA “Social Media Analytics:
Data Mining Applied to Insurance Twitter Posts”.
[4] Facebook Development - https://developers.facebook.com/
[5] Twitter Development - https://dev.twitter.com/
[6] Social Networking Statistics & Facts - http://visual.ly/100-socialnetworking-statistics-facts-2012](https://image.slidesharecdn.com/sdmfinal-131102022800-phpapp02/85/Social-Data-Mining-51-320.jpg)