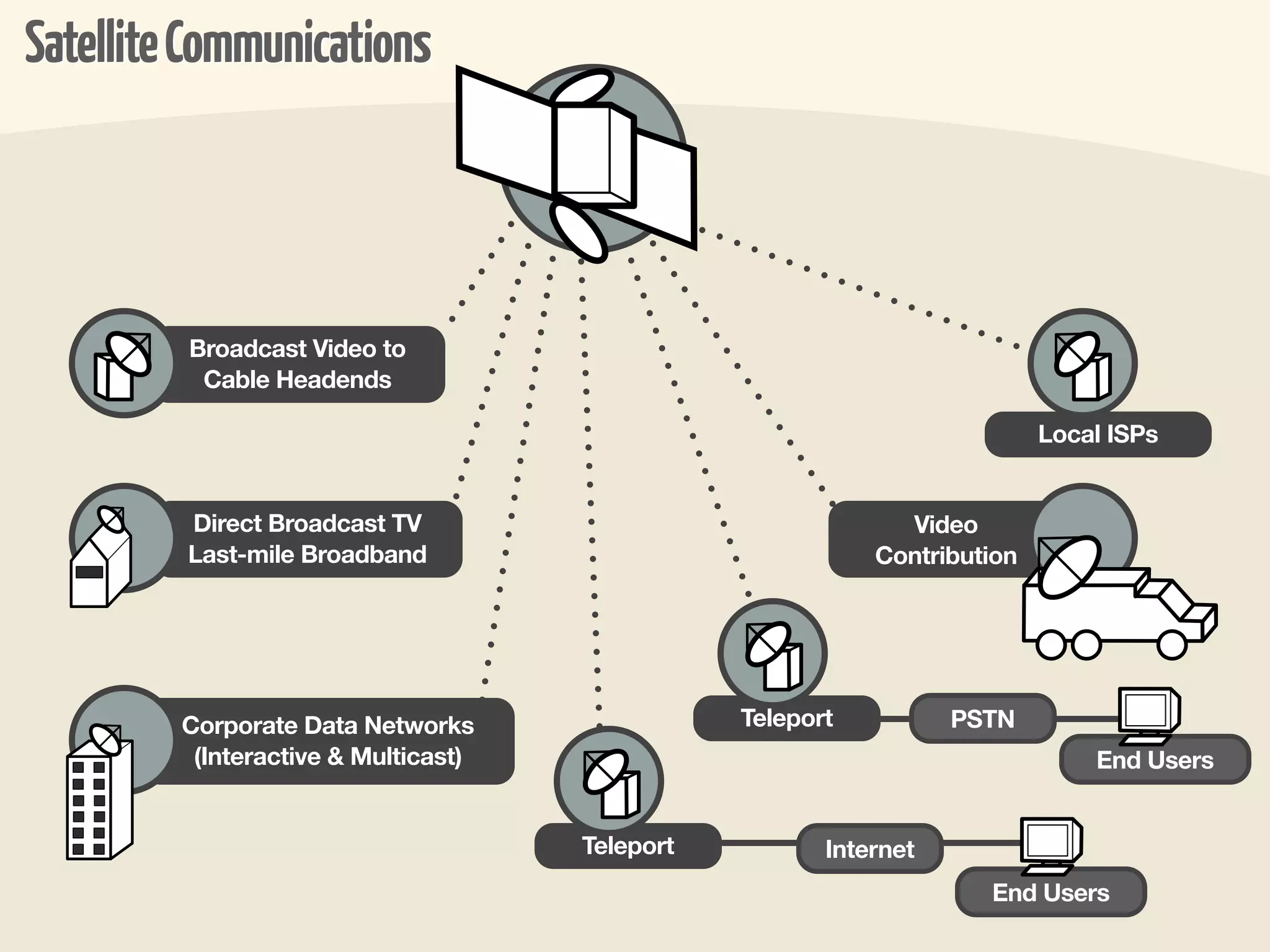
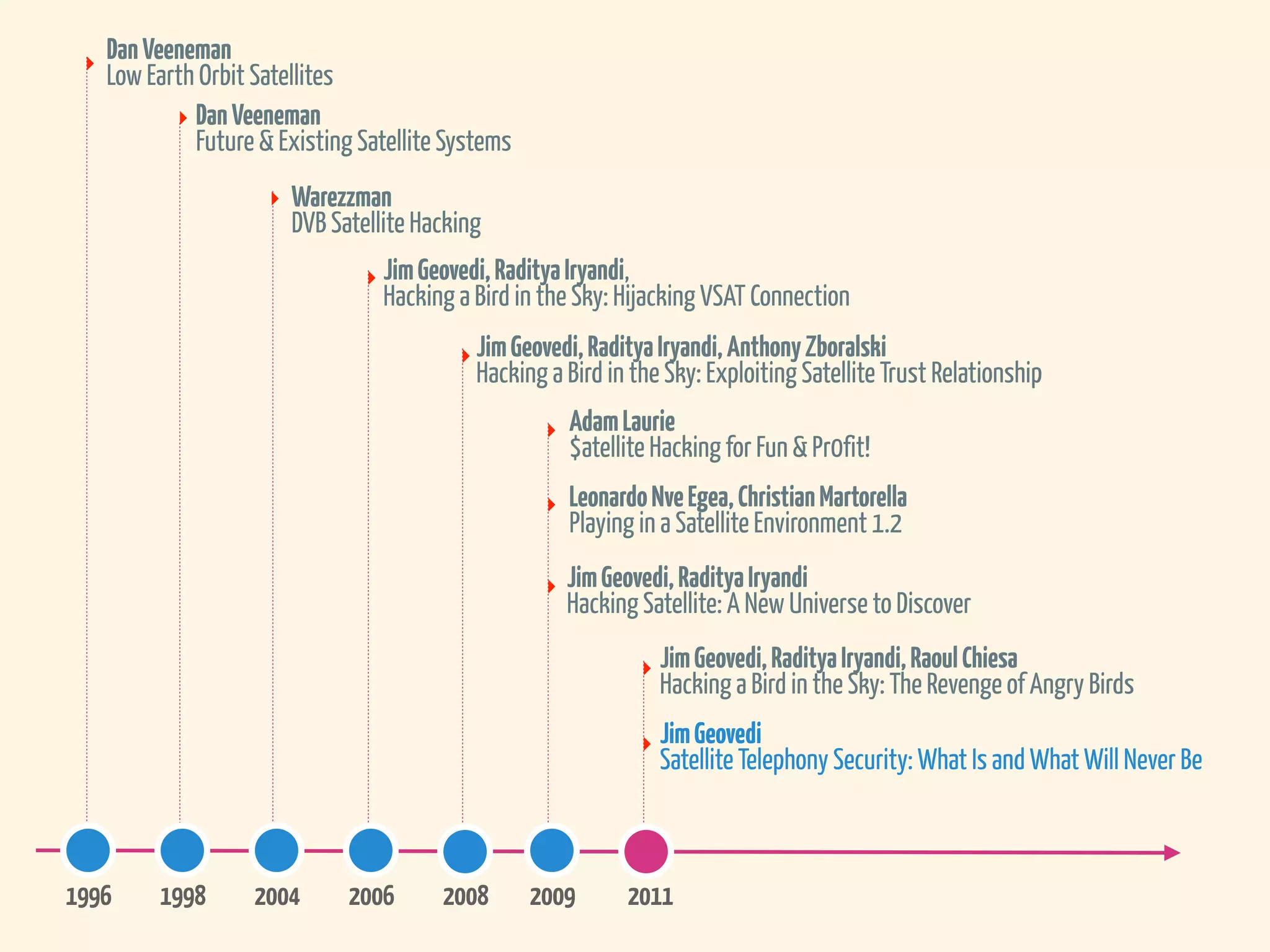
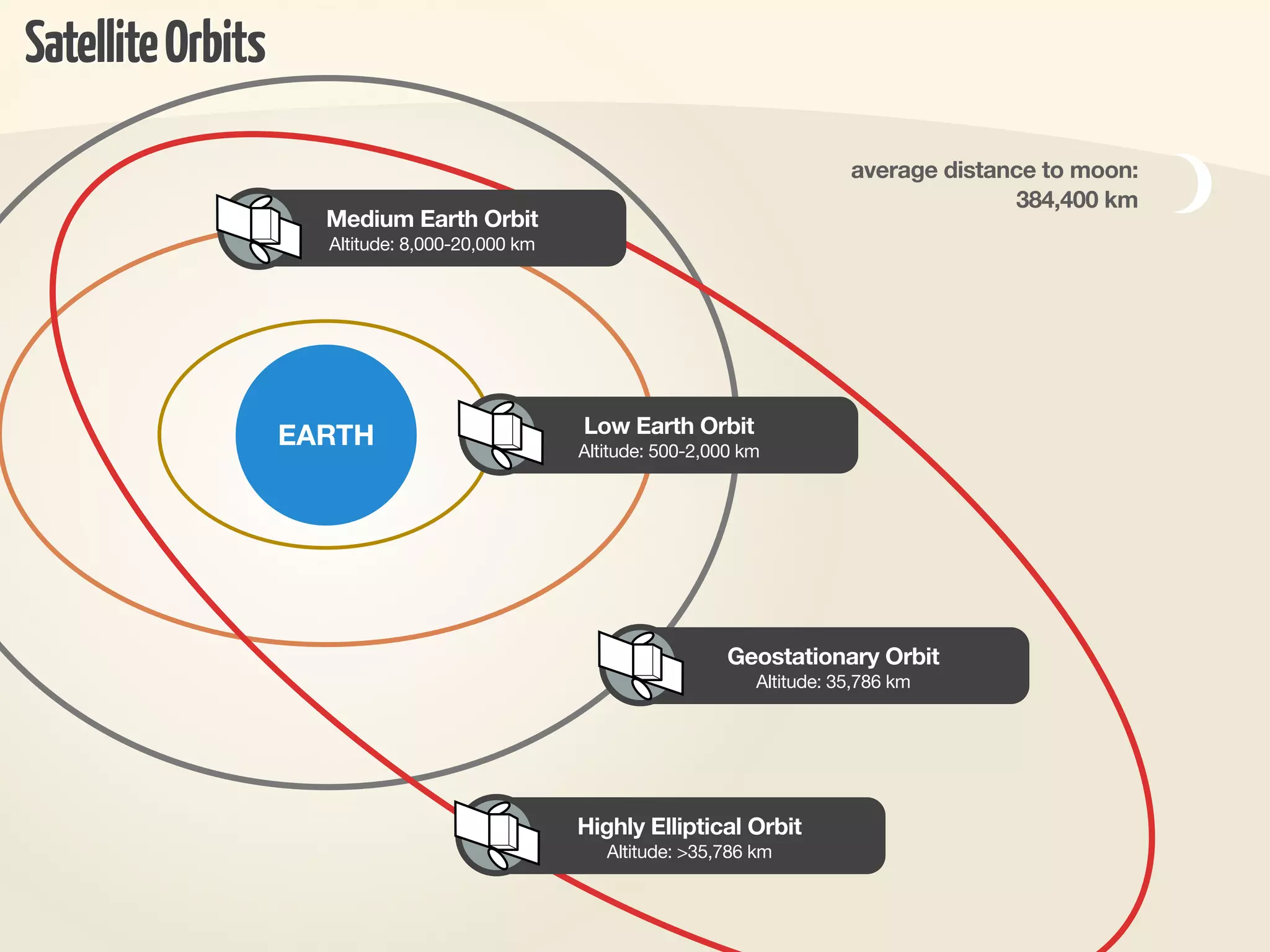
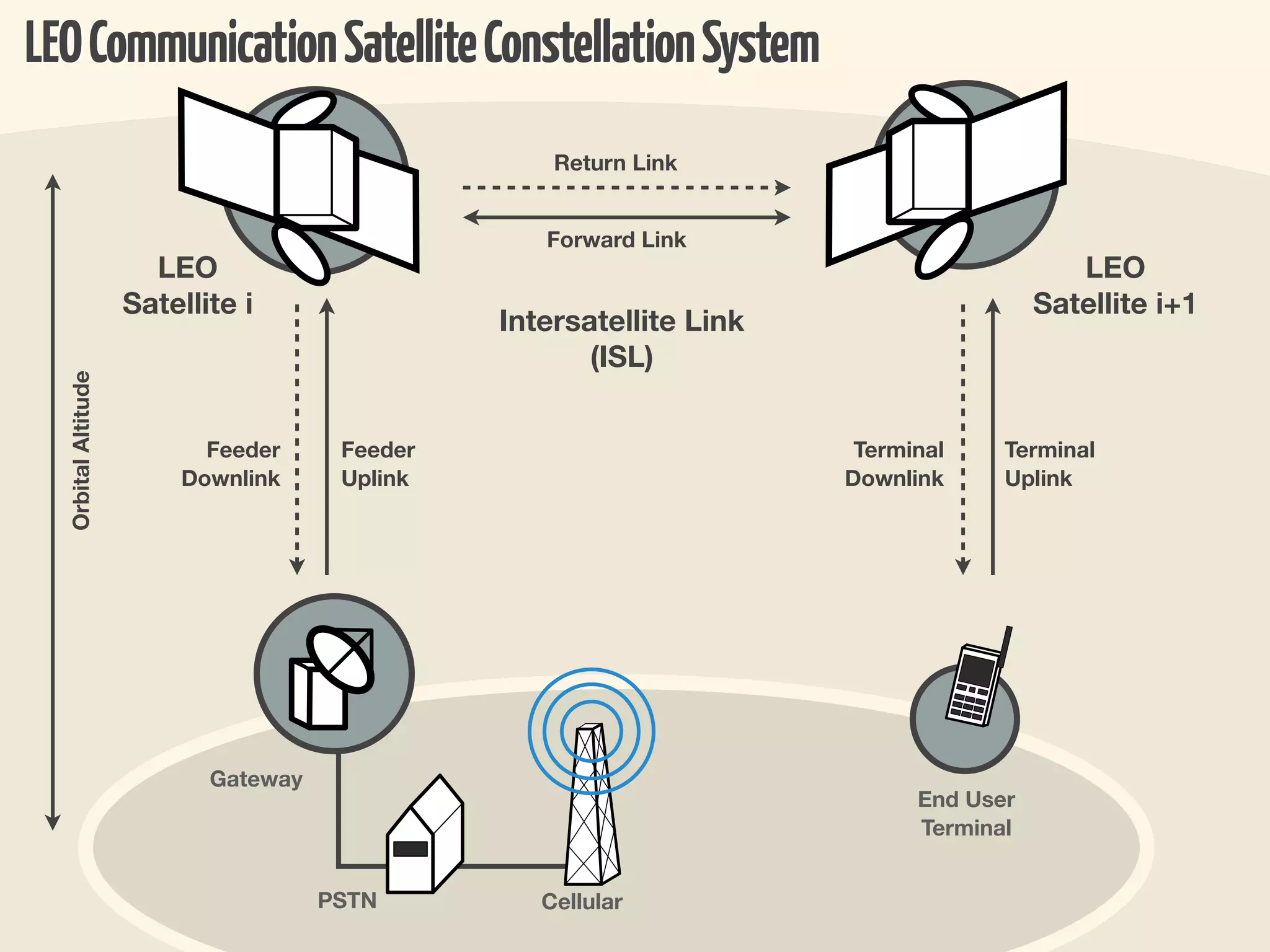
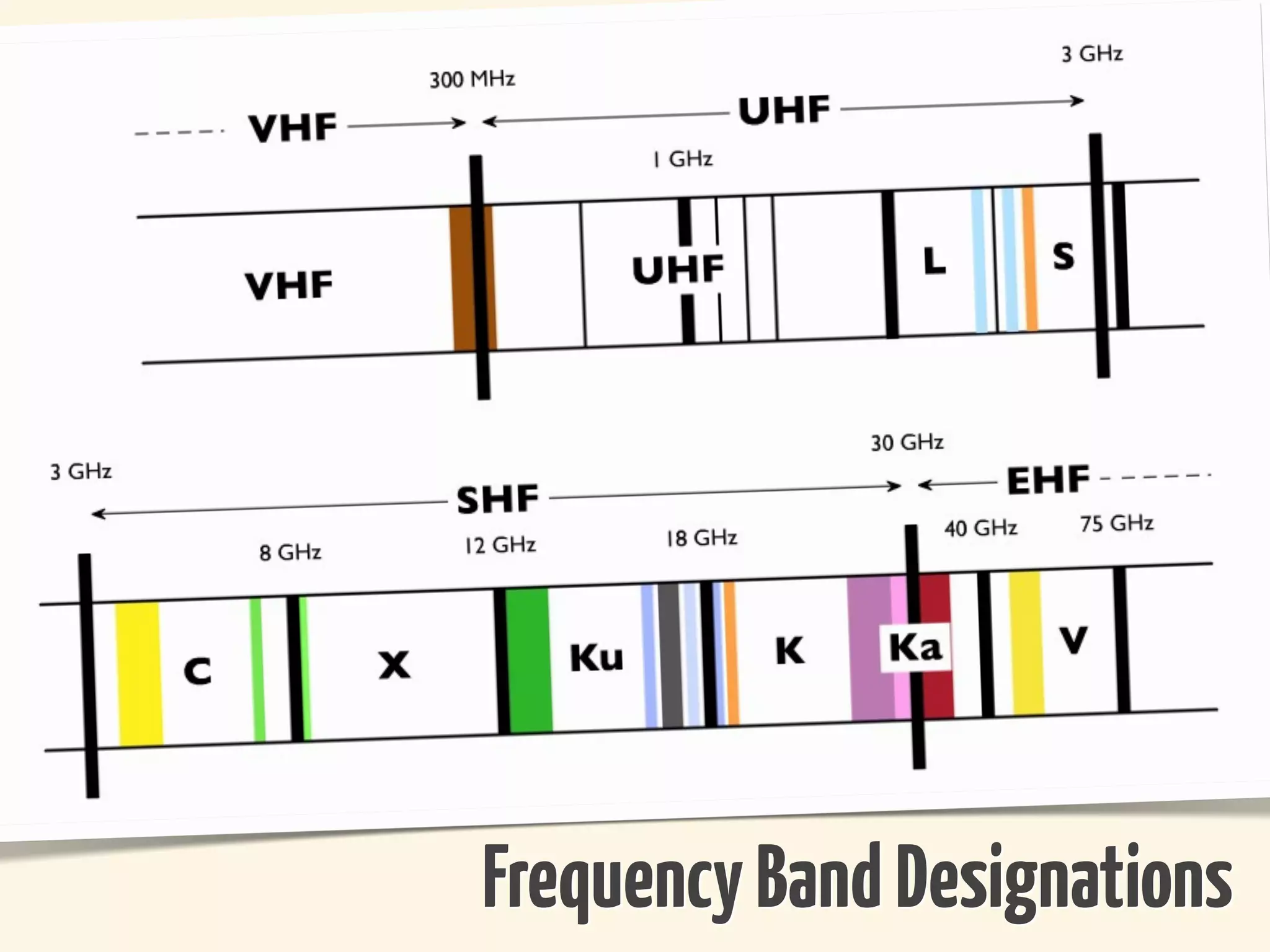
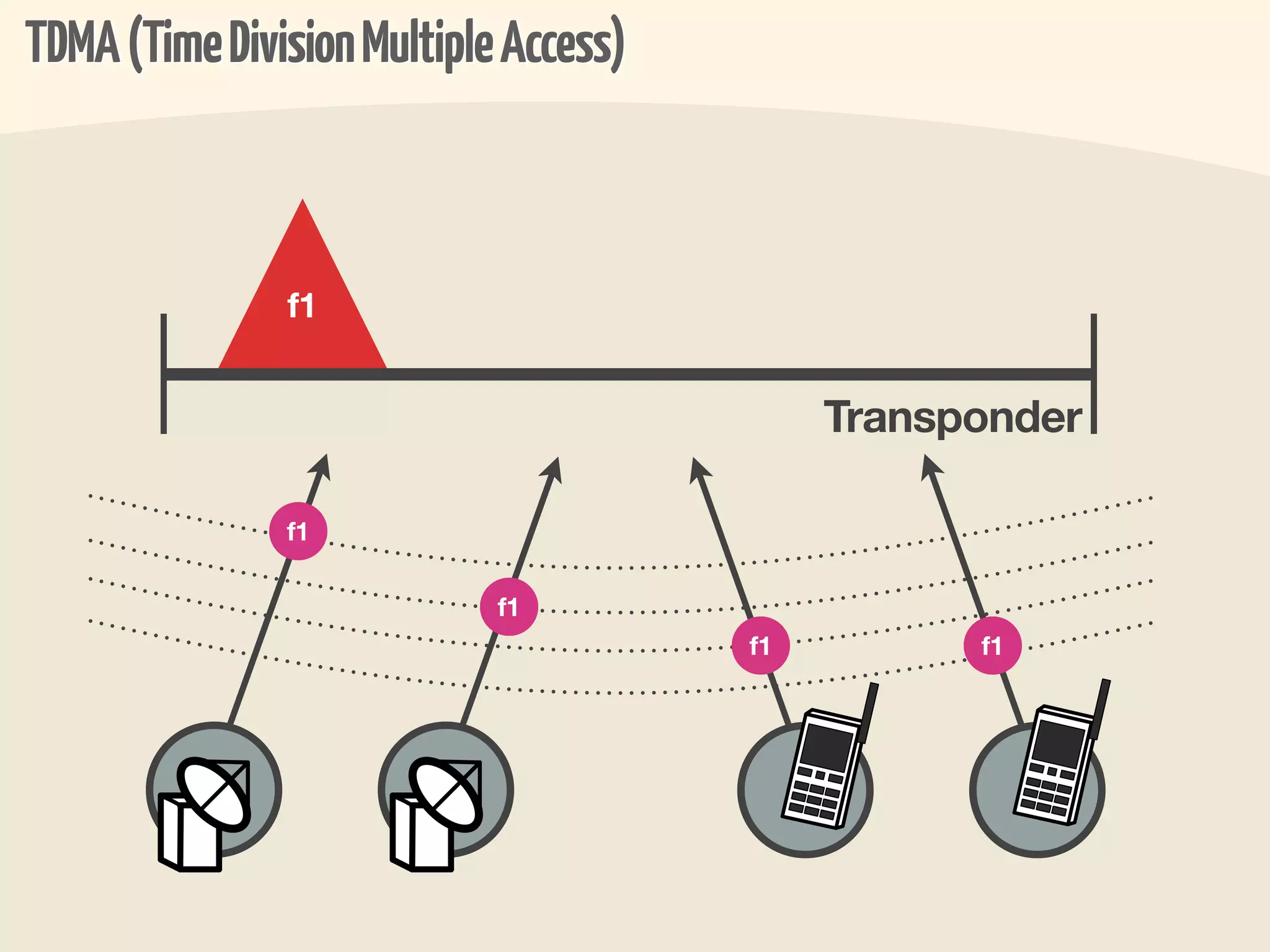
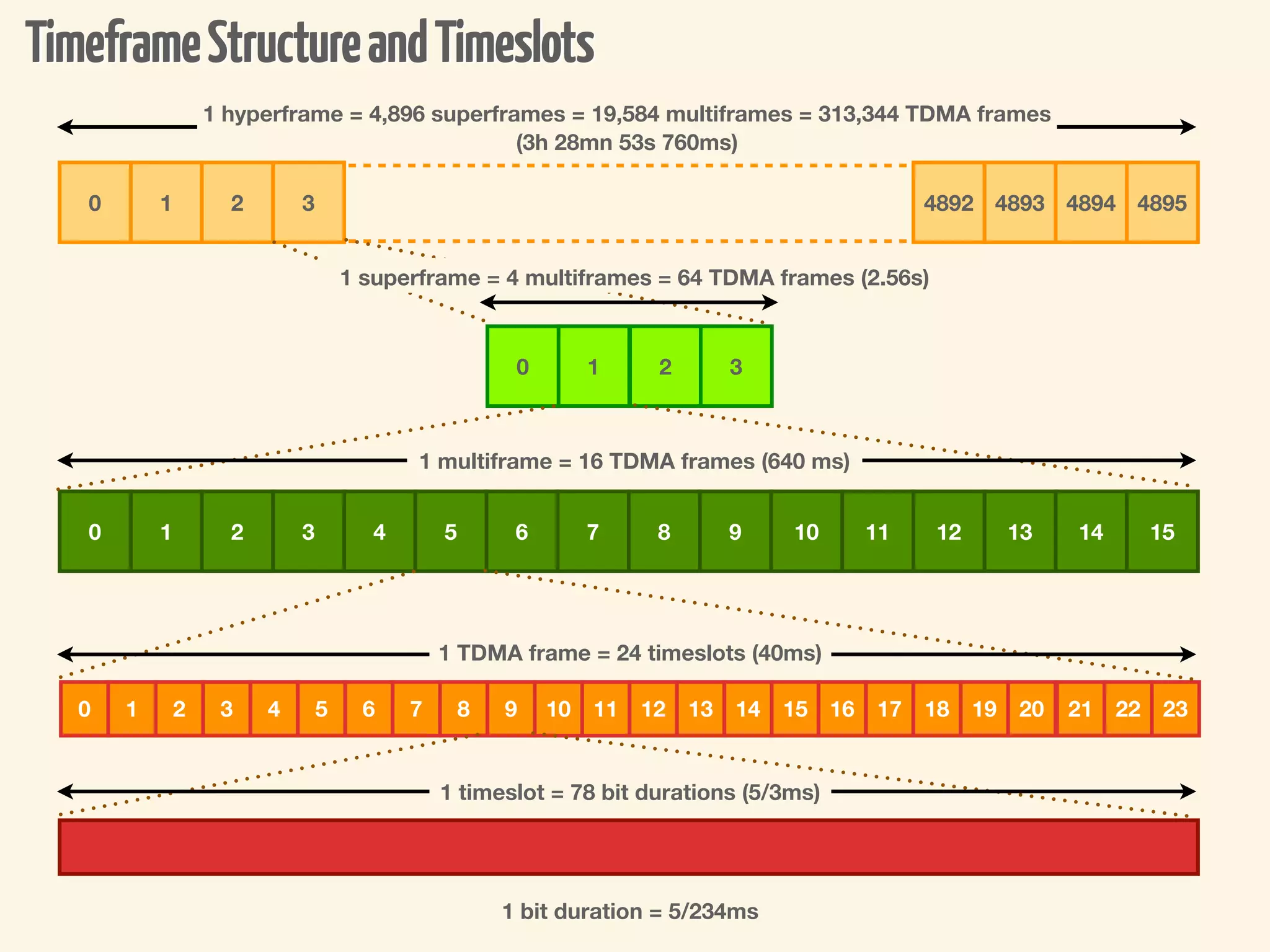
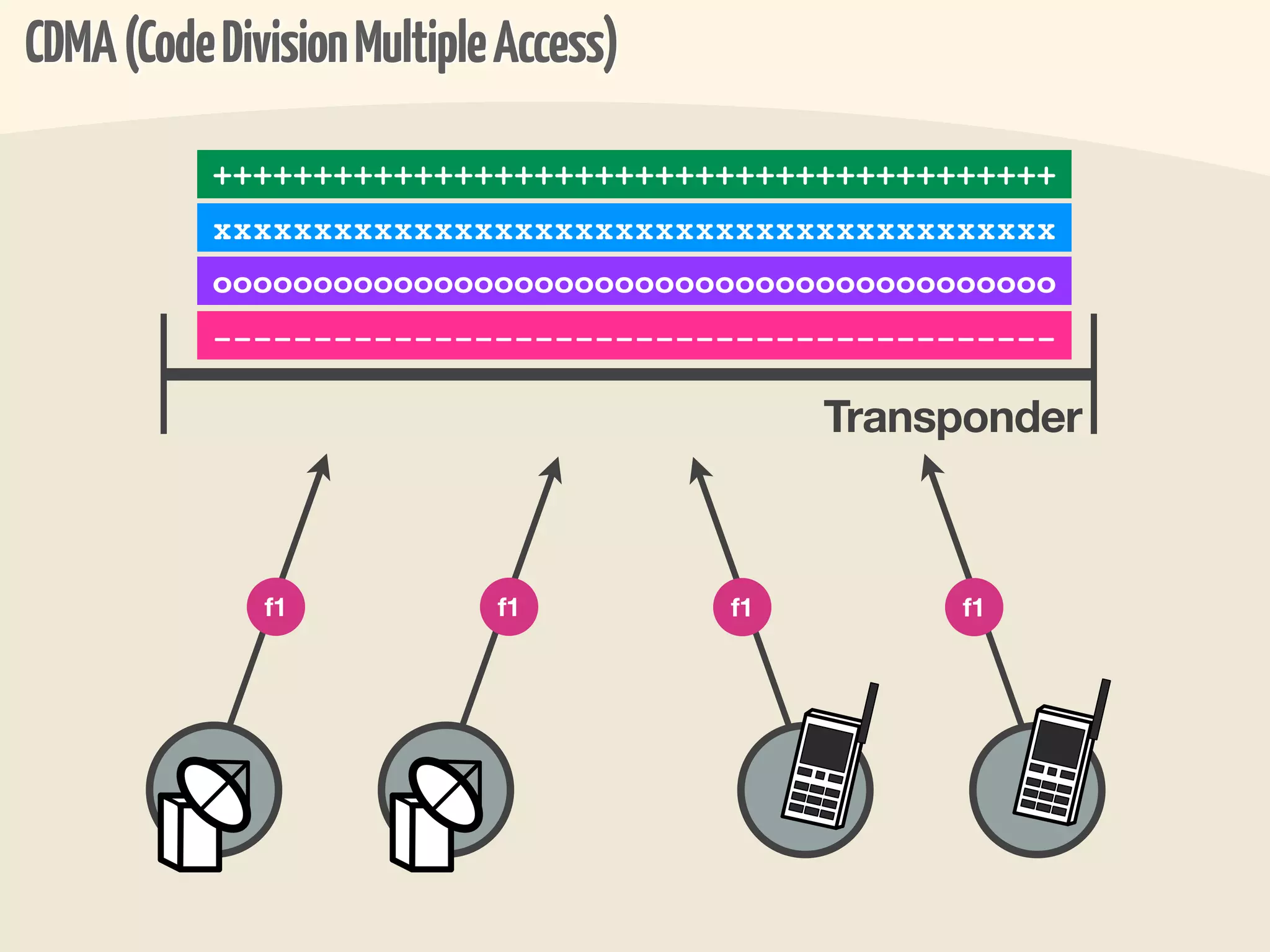
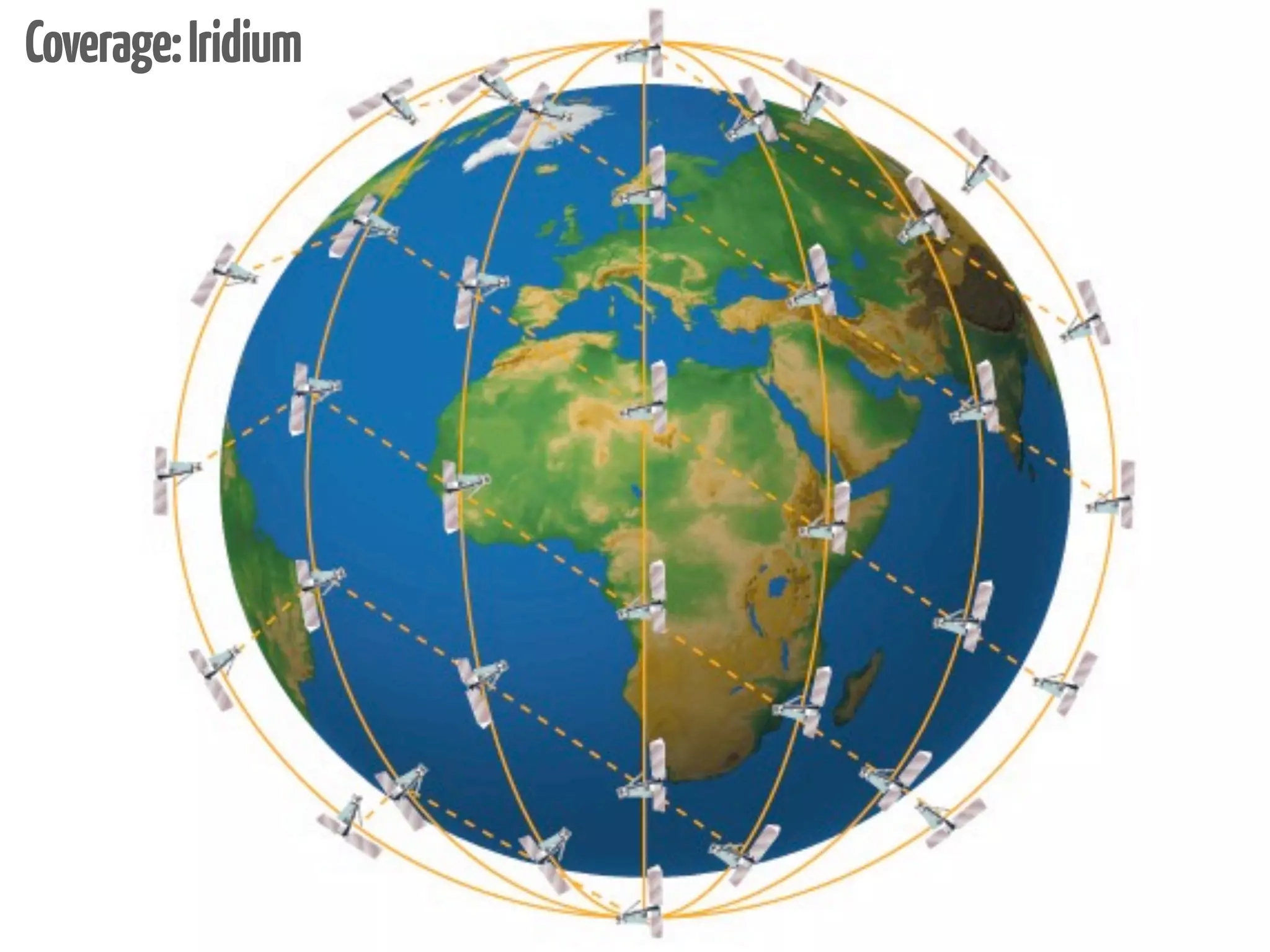
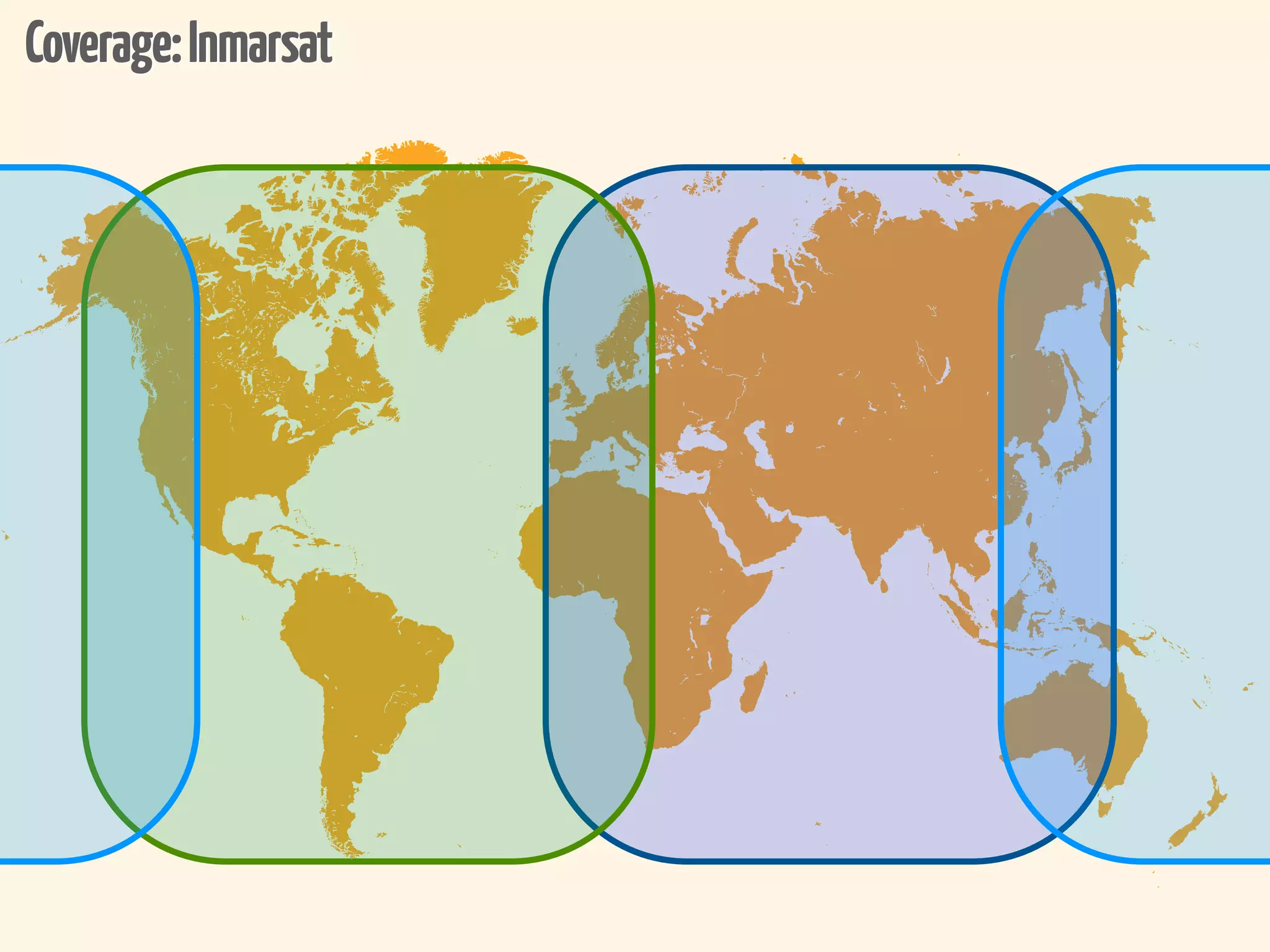
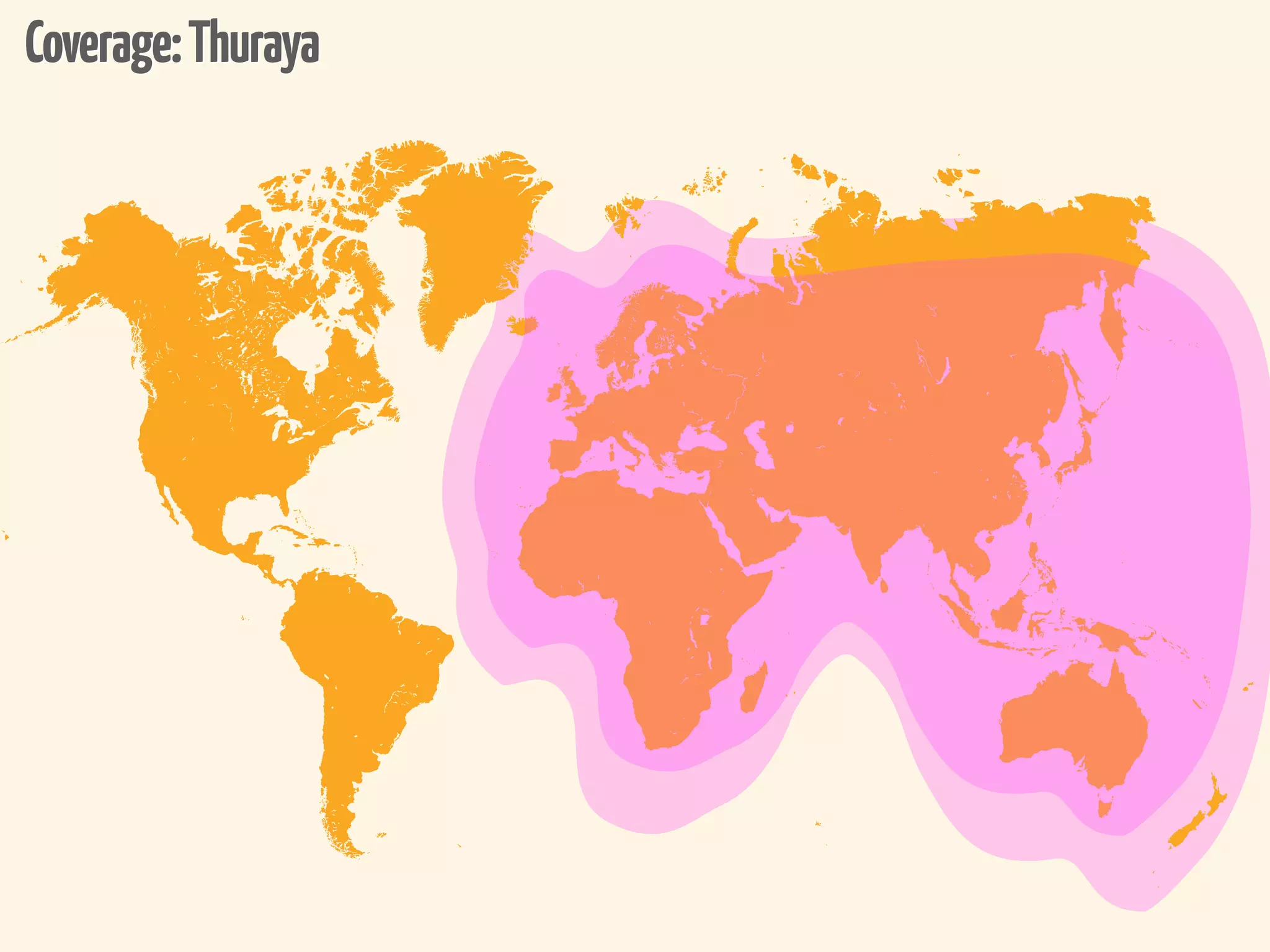
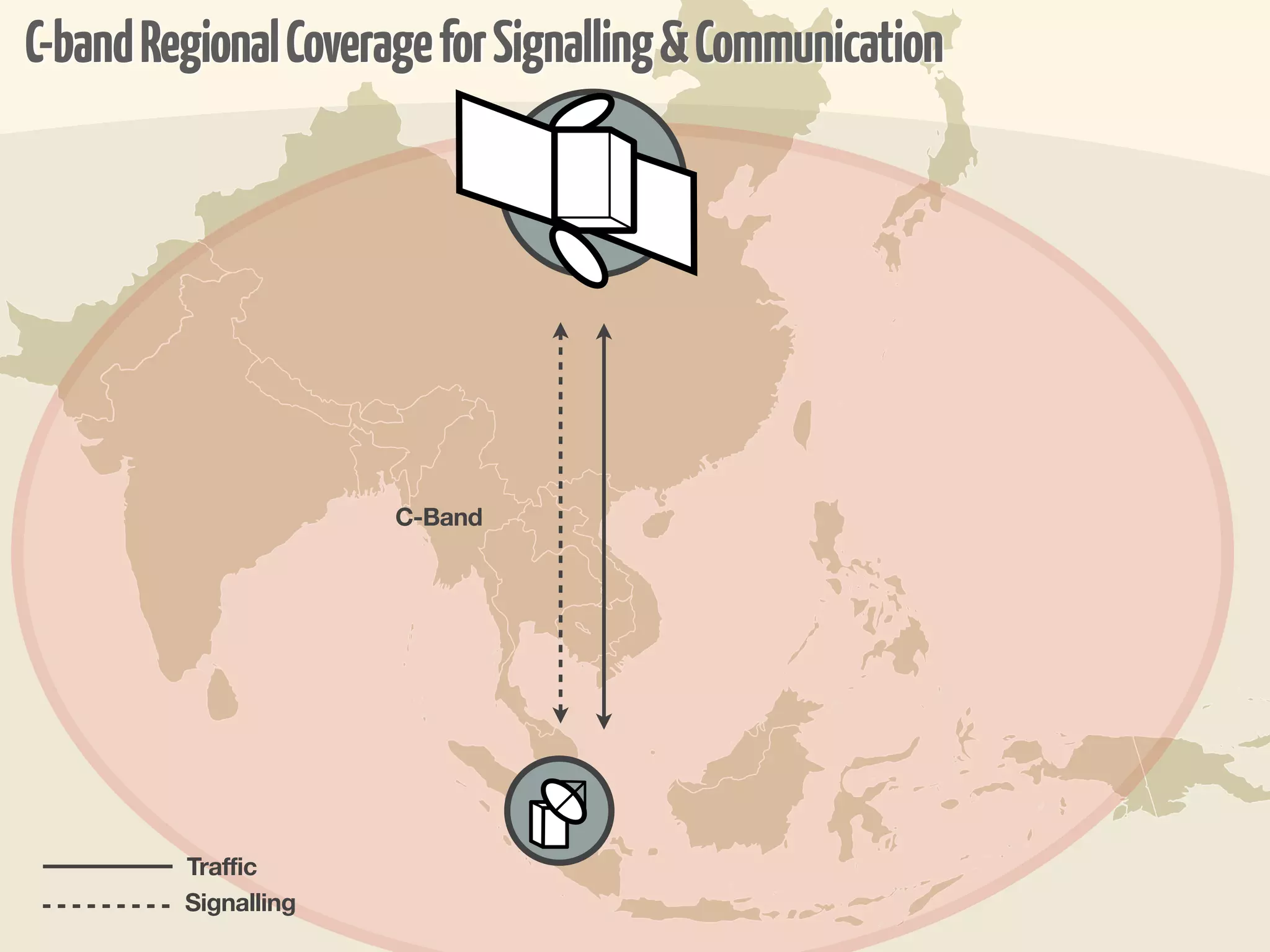
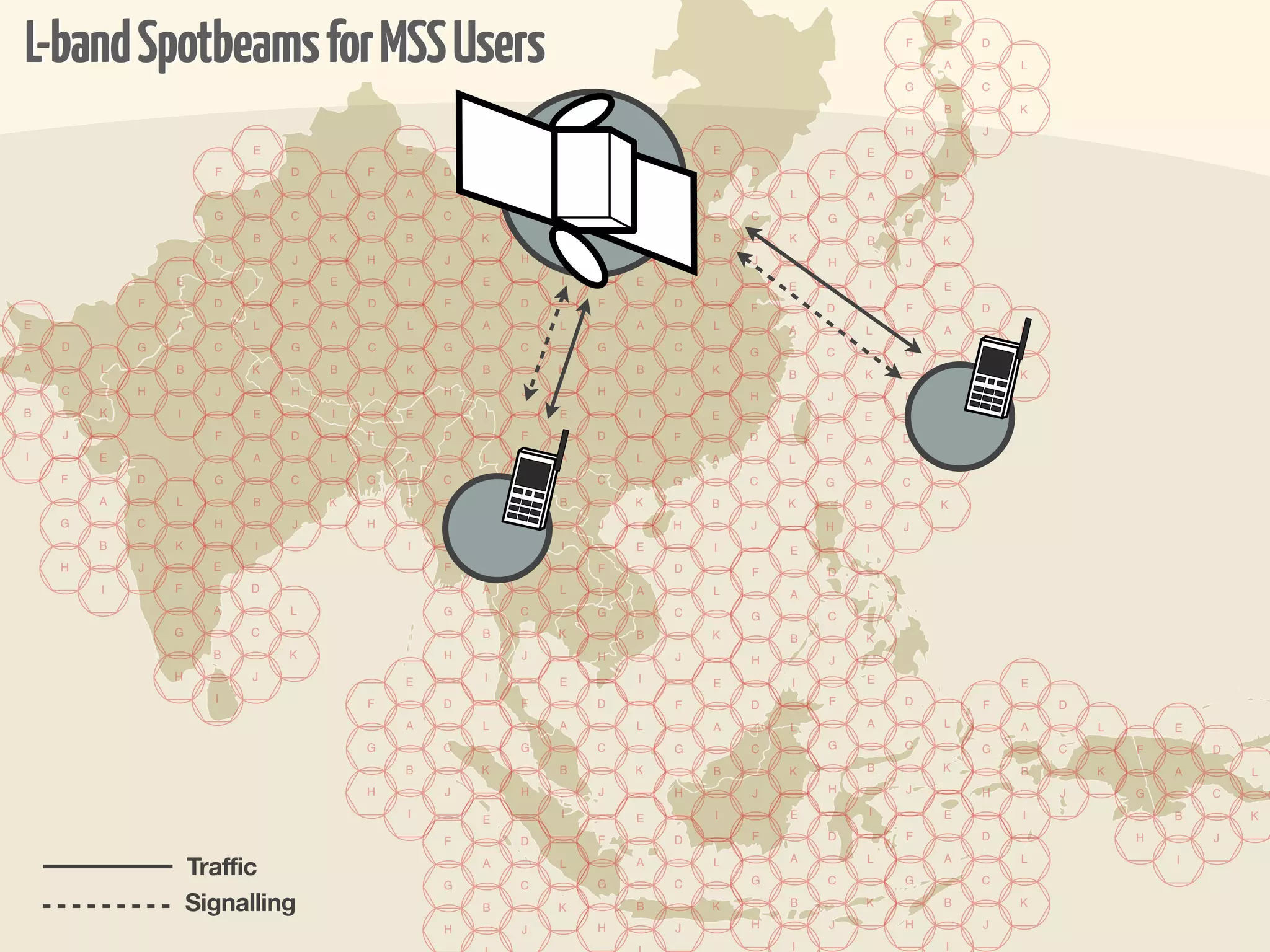
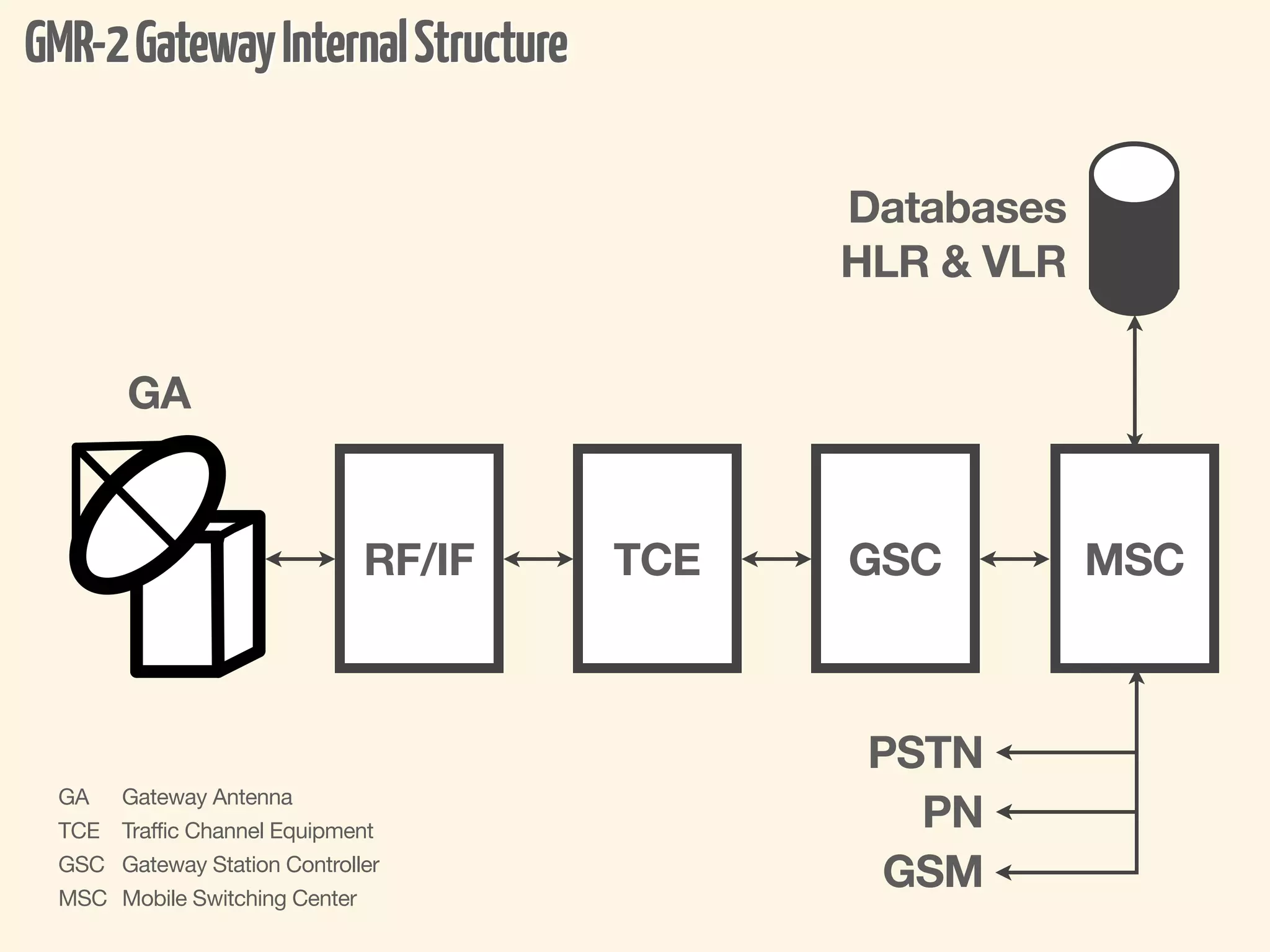
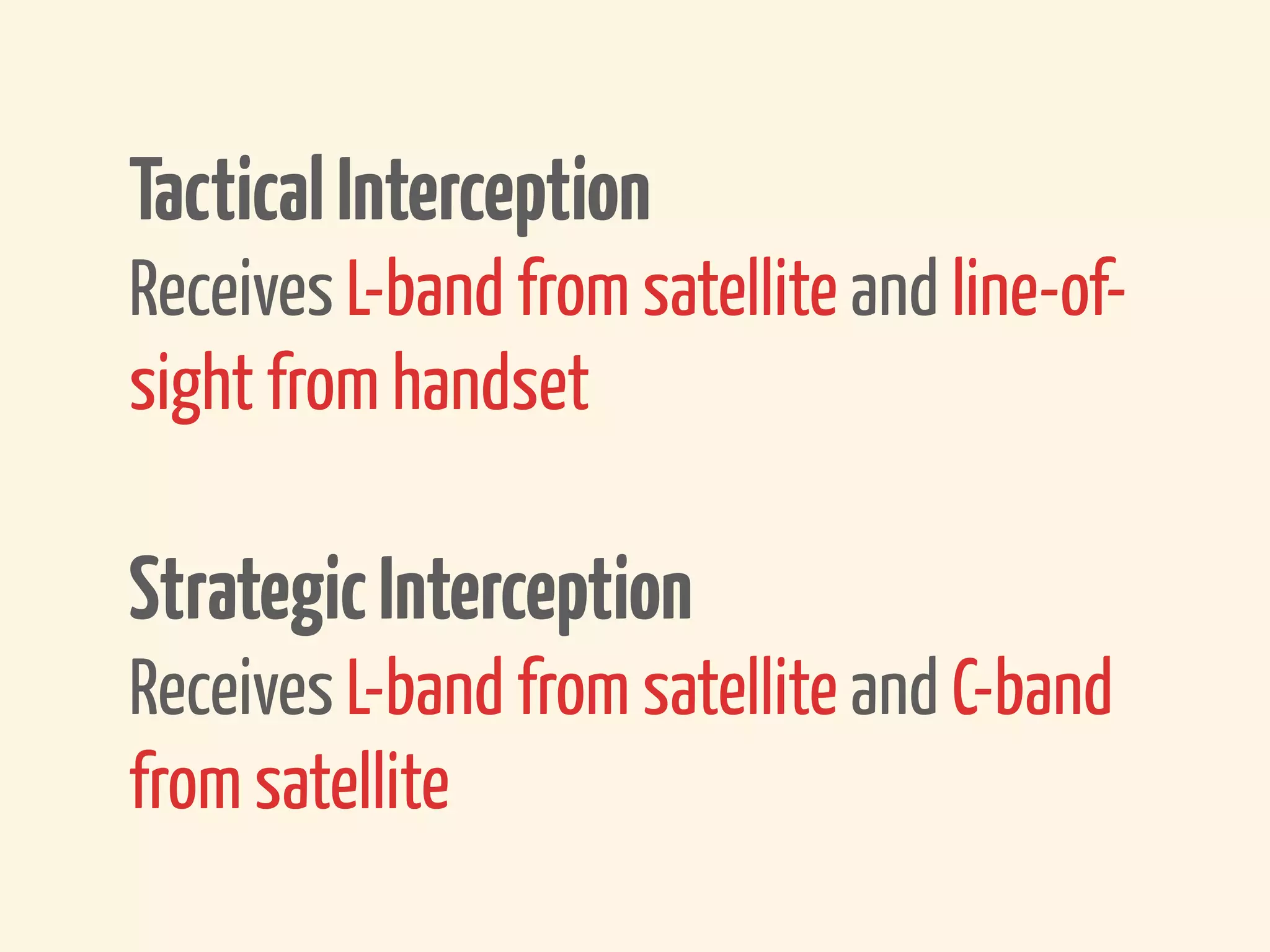
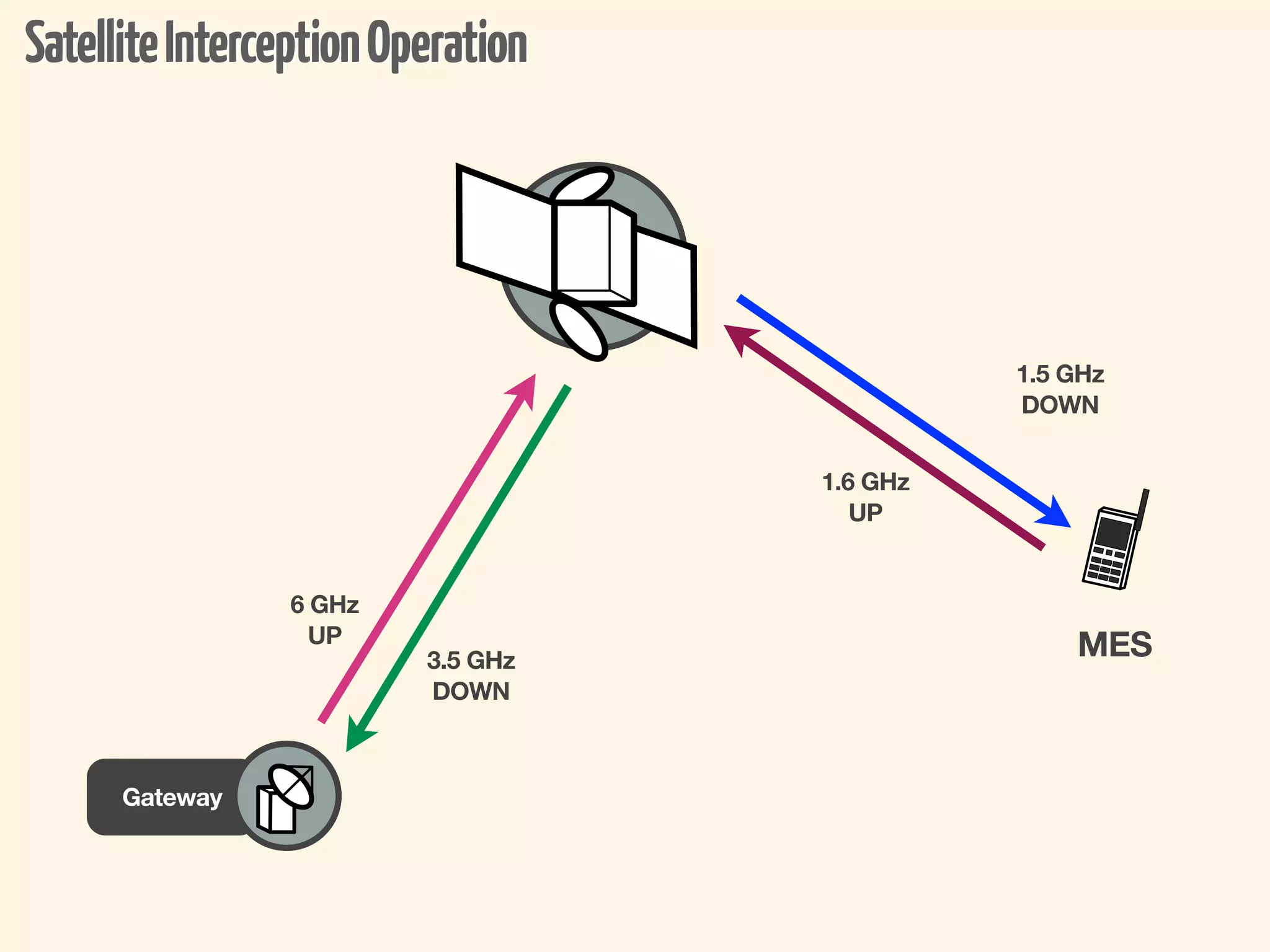
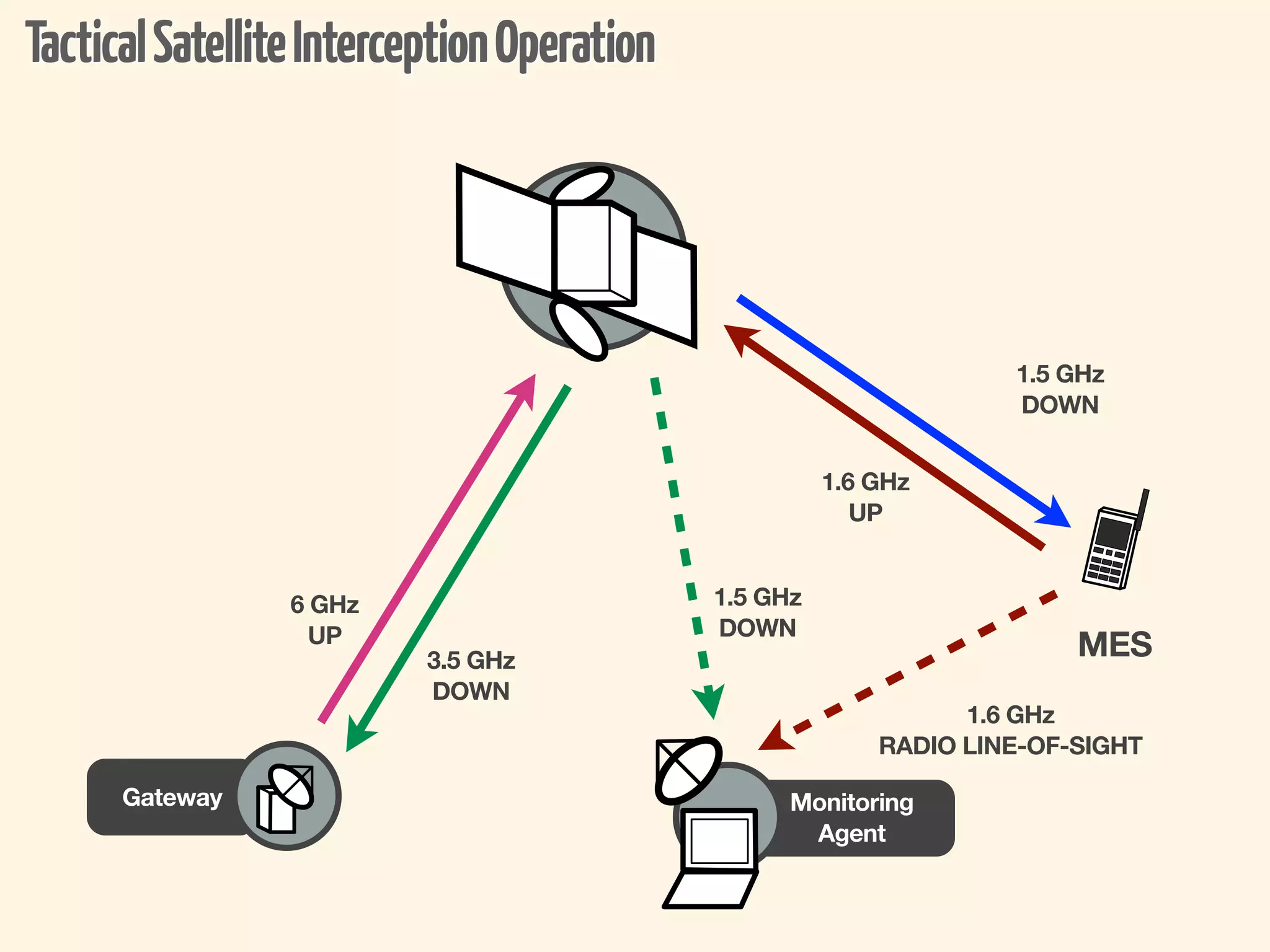
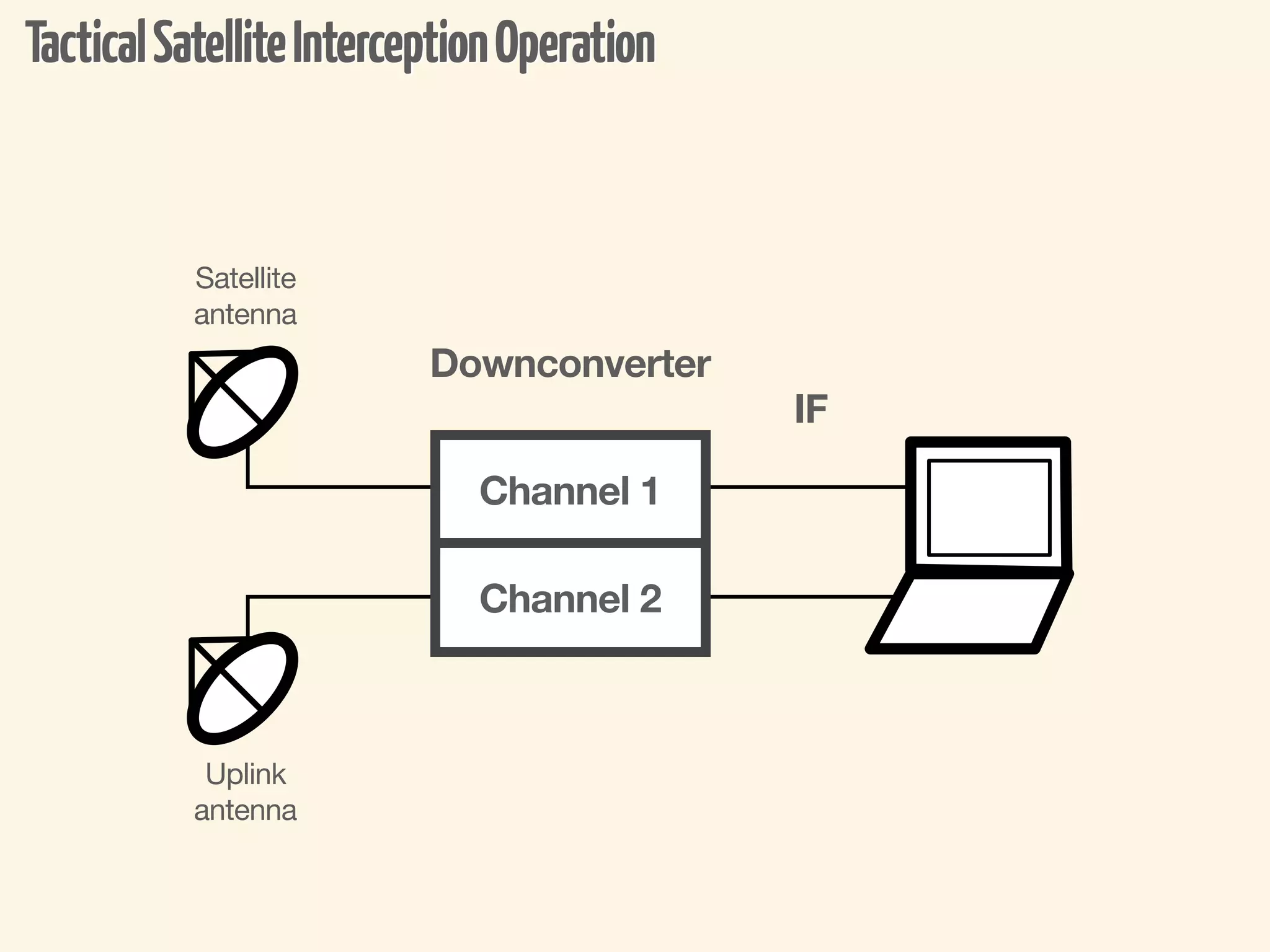
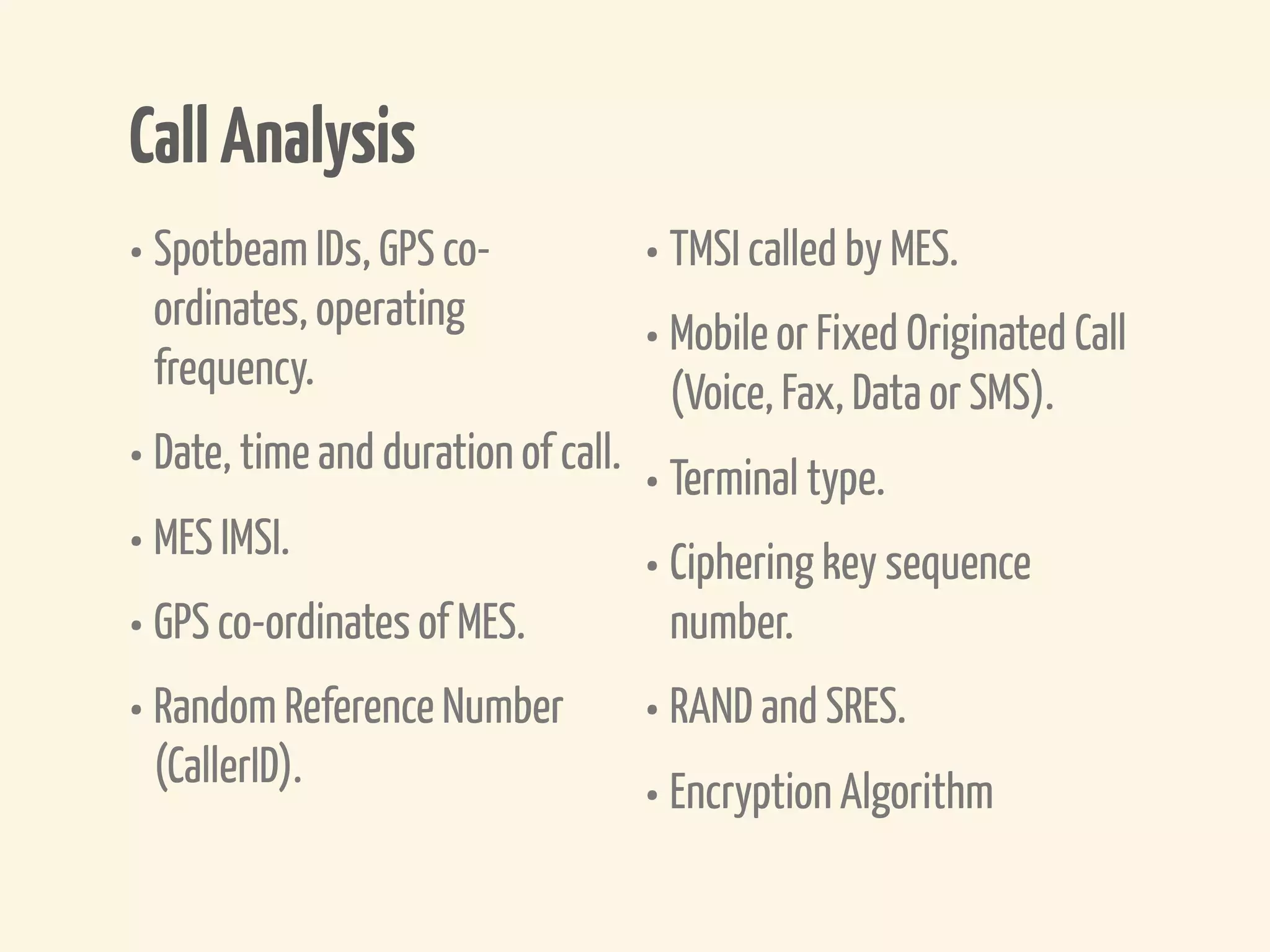
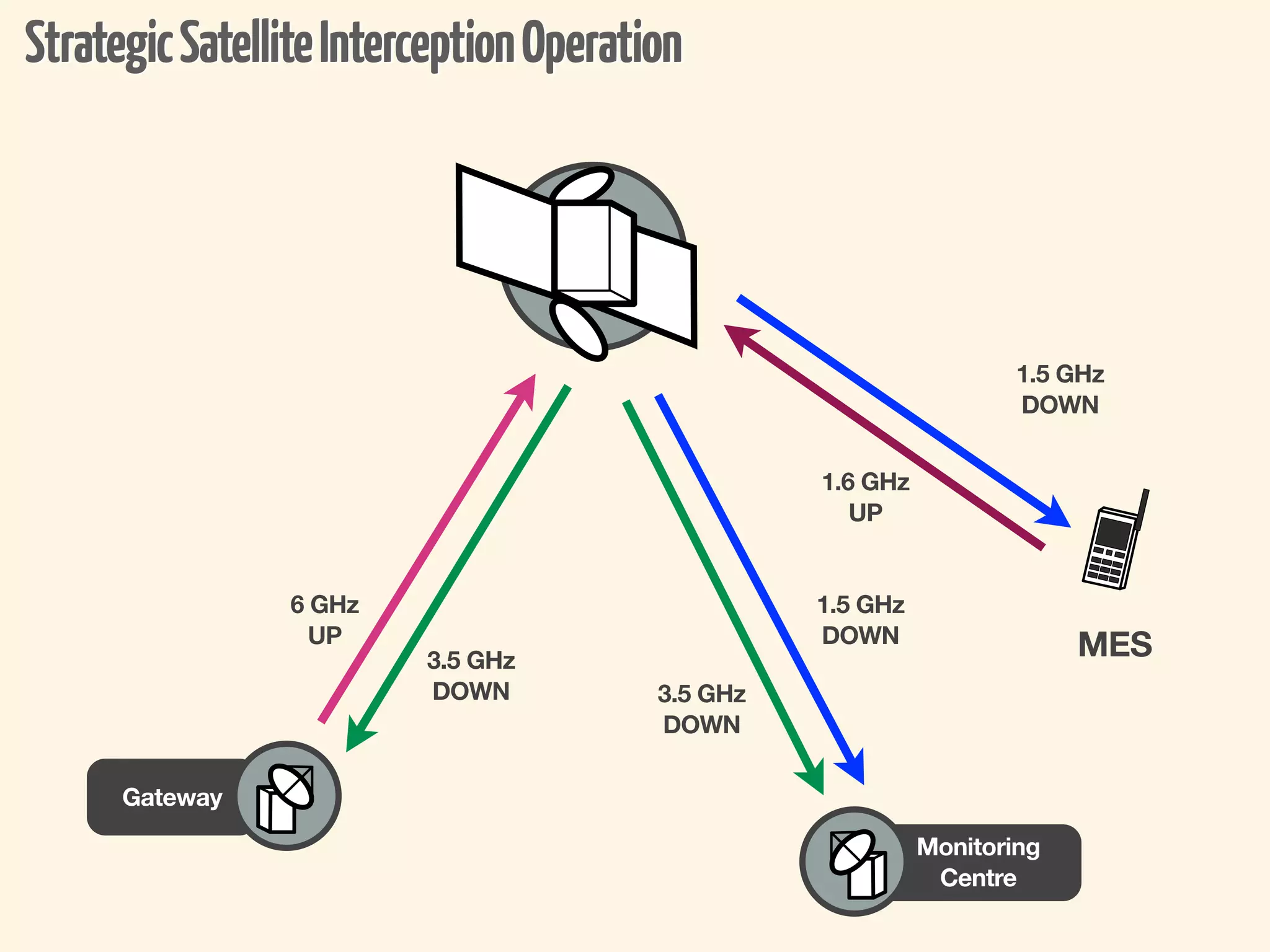
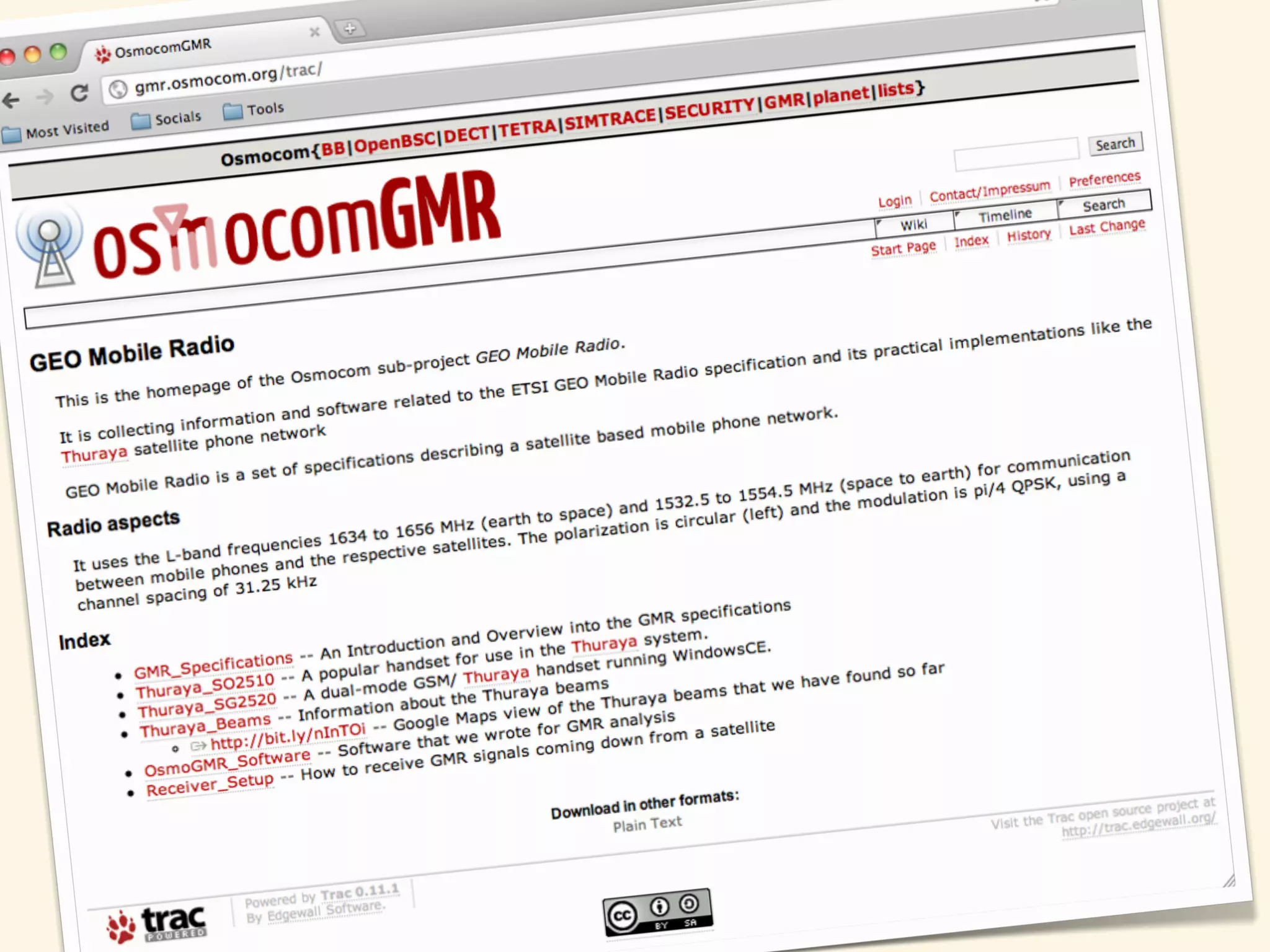
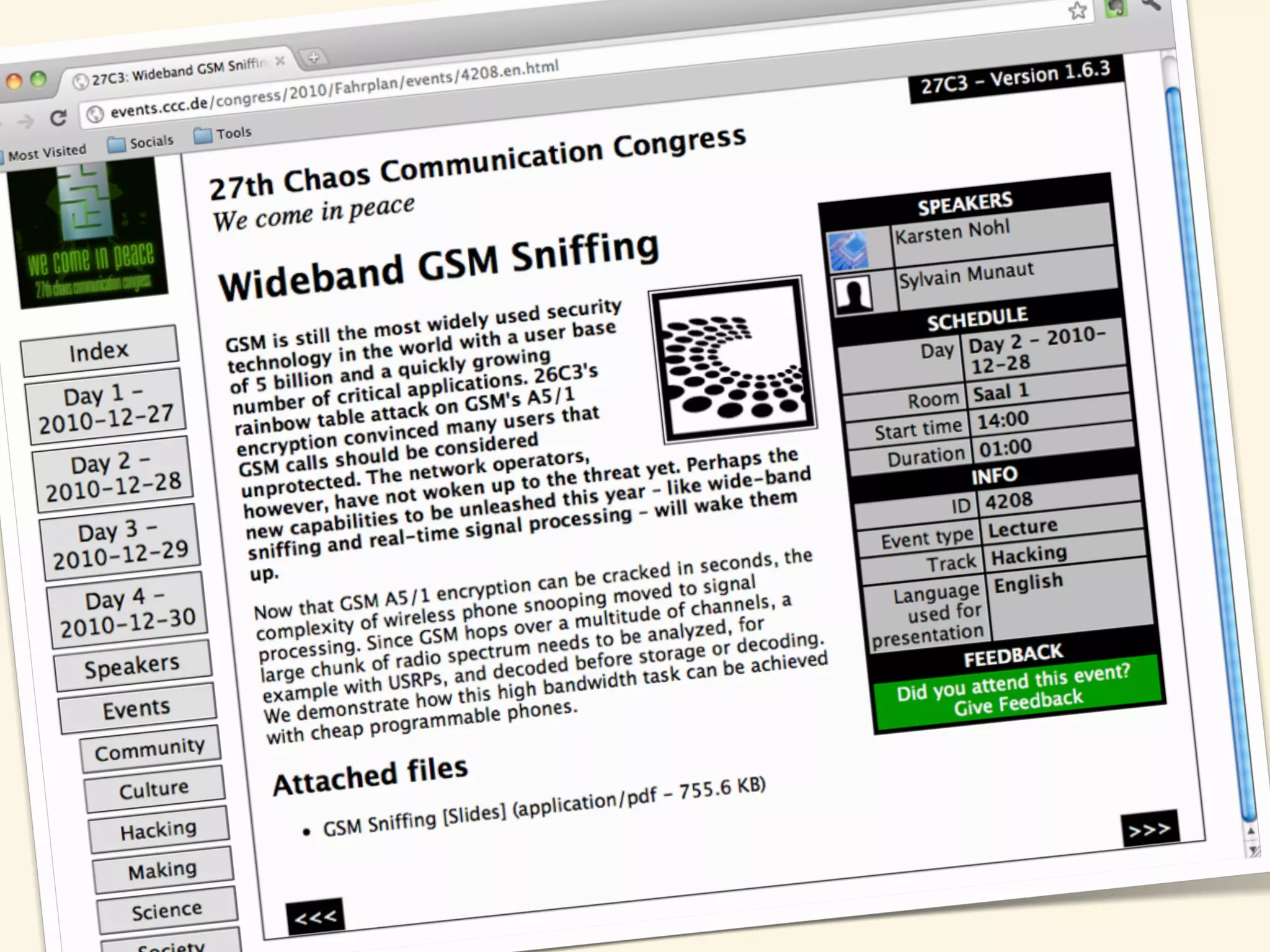
The document discusses the various aspects of satellite telephony security, emphasizing the importance of satellite communications during terrestrial communication failures. It covers different satellite orbits, TDMA and CDMA designations, and operational procedures related to satellite networks. Additionally, it addresses the interception of satellite phone communications, highlighting tactics and methods used for both tactical and strategic interception by law enforcement.