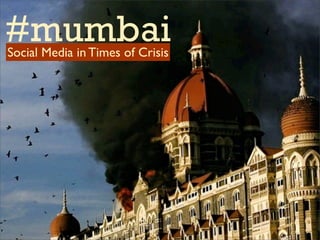
Role of Social Media during the Mumbai Attacks
•
24 likes•5,931 views
Social media played an important role in reporting on the 2008 Mumbai terrorist attacks. [1] Citizens used Twitter to share information and photos from the scene, providing real-time updates. [2] However, some information spread on social media was inaccurate, with widely varying casualty estimates. [3] The challenges of balancing immediacy versus accuracy in crisis reporting using social media are discussed.
Report
Share
Report
Share
Download to read offline
Recommended
Cybersecurity awesome mix vol. II

A collection of musical masterpieces that may have very well been inspired by the best (or the worst, it depends how you look at it) hacks recorded in the second half of 2016.
How News Websites Spread (and Debunk) Online Rumors, Unverified Claims and Mi...

This is a summary of some of the research contained in my Tow Center report, which can be downloaded here: http://towcenter.org/research/lies-damn-lies-and-viral-content/ It examines how news sites cover rumors and unverified claims, and examines best practices for debunking misinformation.
Weaponizing data science for social engineering: automate E2E spear phishing ...

"Historically, machine learning for information security has prioritized defense: think intrusion detection systems, malware classification and botnet traffic identification. Offense can benefit from data just as well. Social networks, especially Twitter with its access to extensive personal data, bot-friendly API, colloquial syntax and prevalence of shortened links, are the perfect venues for spreading machine-generated malicious content.
We present a recurrent neural network that learns to tweet phishing posts targeting specific users. The model is trained using spear phishing pen-testing data, and in order to make a click-through more likely, it is dynamically seeded with topics extracted from timeline posts of both the target and the users they retweet or follow. We augment the model with clustering to identify high value targets based on their level of social engagement such as their number of followers and retweets, and measure success using click-rates of IP-tracked links. Taken together, these techniques enable the world's first automated end-to-end spear phishing campaign generator for Twitter."
(Source: Black Hat USA 2016, Las Vegas)
Why You're Still Bored

Infographic for mobile app explains why some people are getting bored with social media.
12 Top Talks from BSides San Francisco 2016

Graphic recording artist SunShine BenBelkacem visualizes the interesting points and key takeaways from some interesting talks presented at BSides San Francisco 2016.
Plug & Play News: Sourcing and Verifying News Online in 2022

Drawing on real-life examples and first-hand accounts of reporting on crisis situations in Eastern Europe, the first version of Plug & Play News was created in 2014 and presented at re:publica Berlin 2015 conference. Regardless of year or location, the tools and methods used to source, verify, and make critical information available to the public in real-time are applicable in similar contexts worldwide.
Recommended
Cybersecurity awesome mix vol. II

A collection of musical masterpieces that may have very well been inspired by the best (or the worst, it depends how you look at it) hacks recorded in the second half of 2016.
How News Websites Spread (and Debunk) Online Rumors, Unverified Claims and Mi...

This is a summary of some of the research contained in my Tow Center report, which can be downloaded here: http://towcenter.org/research/lies-damn-lies-and-viral-content/ It examines how news sites cover rumors and unverified claims, and examines best practices for debunking misinformation.
Weaponizing data science for social engineering: automate E2E spear phishing ...

"Historically, machine learning for information security has prioritized defense: think intrusion detection systems, malware classification and botnet traffic identification. Offense can benefit from data just as well. Social networks, especially Twitter with its access to extensive personal data, bot-friendly API, colloquial syntax and prevalence of shortened links, are the perfect venues for spreading machine-generated malicious content.
We present a recurrent neural network that learns to tweet phishing posts targeting specific users. The model is trained using spear phishing pen-testing data, and in order to make a click-through more likely, it is dynamically seeded with topics extracted from timeline posts of both the target and the users they retweet or follow. We augment the model with clustering to identify high value targets based on their level of social engagement such as their number of followers and retweets, and measure success using click-rates of IP-tracked links. Taken together, these techniques enable the world's first automated end-to-end spear phishing campaign generator for Twitter."
(Source: Black Hat USA 2016, Las Vegas)
Why You're Still Bored

Infographic for mobile app explains why some people are getting bored with social media.
12 Top Talks from BSides San Francisco 2016

Graphic recording artist SunShine BenBelkacem visualizes the interesting points and key takeaways from some interesting talks presented at BSides San Francisco 2016.
Plug & Play News: Sourcing and Verifying News Online in 2022

Drawing on real-life examples and first-hand accounts of reporting on crisis situations in Eastern Europe, the first version of Plug & Play News was created in 2014 and presented at re:publica Berlin 2015 conference. Regardless of year or location, the tools and methods used to source, verify, and make critical information available to the public in real-time are applicable in similar contexts worldwide.
Plug & Play News 

Originally crafted for re:publica 2015 by @TetyUAna, @MaliciaRogue, and @NikiBGD, this is an updated version of Plug & Play News for the European Press Youth Digital Media Literacy Program.
Has the Cyber War Begun?

Essay asks the question... are we already in a cyber war and just don't know it.
5 biggest cyber attacks and most famous hackers

A computer hacker is a computer expert who uses their technical knowledge to achieve a goal or overcome an obstacle, within a computerized system by non-standard means.
President-Elect Trump and the Power of Twitter

Buzzfeed News claimed to have obtained quotes from a European Intelligence source predicting that Trump’s incessant use of Twitter to rant about everything from politics to celebrities would cause American Intelligence-sharing allies to begin filtering the information given to the Trump-party.
World Book Day: Cybersecurity’s Quietest Celebration

We asked a selection of Tripwire friends, and cybersecurity experts for their recommendations for books that lift, educate, and inspire!
PeopleBrowsr Presents The Future of News - An Orwellian Inversion 

A presentation at News Foo Phoenix Ignite by Jodee Rich CEO PeopleBrowsr. The Social Media Revolution is an inverted Orwellian Revolution - Big Data is empowering Little Brother
Using social media in breaking news michelle guido - orlando

Using Social Media in Breaking News, a handout compiled by Michelle Guido for her Planning for Breaking News session at Orlando NewsTrain on May 15-16, 2015. Instructor Michelle Guido offers a a checklist for constructing a breaking-news coverage plan. Guido is a journalist with 25 years of award-winning work across print, digital and television platforms. Most recently, she was managing editor of WESH 2 News, the NBC affiliate in Orlando.
Infowarcon2016 Are you ready Middle East Cyberwar updates v30

Infowarcon 2016 Are you ready Middle East Cyberwar updates
Social and Mobile and Cloud OH MY!

Presented at InnoTech Oklahoma by Tyler Shields on 11-3-2011. All rights reserved.
How to get attention for anything

A rough guide to media manipulation in the attention economy.
Based on Ryan Holidays book " Trust Me, I'm Lying"
Presented at Inbound.org Tokyo Meetup
Social Engineering CSO Survival Guide

Social Engineering CSO Survival Guide, designing leading edge 21st Century Business Models go to www.esgjrconsultinginc.com to learn more about Software/Network Engineering Solutions.
Social Media & Tourism

Numerous presenters at the Social Media Club of Hawaii shared their ideas on "what if" we connected the community, the businesses, and the tourism agencies suing social media to support and grow our visitors. I was the moderator and seeded the discussion with a few ideas of my own. Get links to the broadcast, the tweetstream, and the presenters here on my blog: http://www.barefeetstudios.com/2012/10/26/social-media-and-tourism-lets-talk-together/
26/11: An economic perspective

this is a comprehensive document which contains most of the economic aspects from foreign trade to tourism to political set backs as well as the views regarding future of our country. Jai Hind!
More Related Content
What's hot
Plug & Play News 

Originally crafted for re:publica 2015 by @TetyUAna, @MaliciaRogue, and @NikiBGD, this is an updated version of Plug & Play News for the European Press Youth Digital Media Literacy Program.
Has the Cyber War Begun?

Essay asks the question... are we already in a cyber war and just don't know it.
5 biggest cyber attacks and most famous hackers

A computer hacker is a computer expert who uses their technical knowledge to achieve a goal or overcome an obstacle, within a computerized system by non-standard means.
President-Elect Trump and the Power of Twitter

Buzzfeed News claimed to have obtained quotes from a European Intelligence source predicting that Trump’s incessant use of Twitter to rant about everything from politics to celebrities would cause American Intelligence-sharing allies to begin filtering the information given to the Trump-party.
World Book Day: Cybersecurity’s Quietest Celebration

We asked a selection of Tripwire friends, and cybersecurity experts for their recommendations for books that lift, educate, and inspire!
PeopleBrowsr Presents The Future of News - An Orwellian Inversion 

A presentation at News Foo Phoenix Ignite by Jodee Rich CEO PeopleBrowsr. The Social Media Revolution is an inverted Orwellian Revolution - Big Data is empowering Little Brother
Using social media in breaking news michelle guido - orlando

Using Social Media in Breaking News, a handout compiled by Michelle Guido for her Planning for Breaking News session at Orlando NewsTrain on May 15-16, 2015. Instructor Michelle Guido offers a a checklist for constructing a breaking-news coverage plan. Guido is a journalist with 25 years of award-winning work across print, digital and television platforms. Most recently, she was managing editor of WESH 2 News, the NBC affiliate in Orlando.
Infowarcon2016 Are you ready Middle East Cyberwar updates v30

Infowarcon 2016 Are you ready Middle East Cyberwar updates
Social and Mobile and Cloud OH MY!

Presented at InnoTech Oklahoma by Tyler Shields on 11-3-2011. All rights reserved.
How to get attention for anything

A rough guide to media manipulation in the attention economy.
Based on Ryan Holidays book " Trust Me, I'm Lying"
Presented at Inbound.org Tokyo Meetup
Social Engineering CSO Survival Guide

Social Engineering CSO Survival Guide, designing leading edge 21st Century Business Models go to www.esgjrconsultinginc.com to learn more about Software/Network Engineering Solutions.
What's hot (19)
World Book Day: Cybersecurity’s Quietest Celebration

World Book Day: Cybersecurity’s Quietest Celebration
PeopleBrowsr Presents The Future of News - An Orwellian Inversion 

PeopleBrowsr Presents The Future of News - An Orwellian Inversion
Using social media in breaking news michelle guido - orlando

Using social media in breaking news michelle guido - orlando
Infowarcon2016 Are you ready Middle East Cyberwar updates v30

Infowarcon2016 Are you ready Middle East Cyberwar updates v30
Echo Chamber dan Eksklusifitas Pemikiran di Media Sosial

Echo Chamber dan Eksklusifitas Pemikiran di Media Sosial
Stalking a City for Fun and Frivolity" Defcon Talk

Stalking a City for Fun and Frivolity" Defcon Talk
Viewers also liked
Social Media & Tourism

Numerous presenters at the Social Media Club of Hawaii shared their ideas on "what if" we connected the community, the businesses, and the tourism agencies suing social media to support and grow our visitors. I was the moderator and seeded the discussion with a few ideas of my own. Get links to the broadcast, the tweetstream, and the presenters here on my blog: http://www.barefeetstudios.com/2012/10/26/social-media-and-tourism-lets-talk-together/
26/11: An economic perspective

this is a comprehensive document which contains most of the economic aspects from foreign trade to tourism to political set backs as well as the views regarding future of our country. Jai Hind!
Social media & tourism

This is the presentation I used during a lecture on Social Media & Tourism in Spain (CCT, Murcia, 8 February 2012).
disaster of Mumbai terror attack by vinay

presentation on mitigation measures by gov. of india on the TAJ hotel terror attack.....
Social Media Marketing for the Tourism Industry

Case studies, Tips and Tools for using Social Media for the Tourism Industry.
www.socialeyes.gr
Social Media & Tourism: 10 Tips to Attract Travelers

The importance of using digital, social, mobile and emerging media to attract travelers to destinations is no secret. From overarching strategy to helpful tips and tricks, this presentation covers ways to energize locals to become brand evangelists and help fuel the flow of customers from out of town.
This keynote was originally delivered Ben Grossman at Social Media Breakfast Greater Philly in partnership with Visit Bucks County in May 2011.
Social Media And Tourism

A presentation given to Travel and Tourism professionals as at a seminar run by Blackpool and Lancashire Tourist Board (Feb 08). Social Media for the Travel and Tourism industry. An overview of the social media space and opportunities for harnessing communities in social space.
Viewers also liked (12)
Social Media & Tourism: 10 Tips to Attract Travelers

Social Media & Tourism: 10 Tips to Attract Travelers
Similar to Role of Social Media during the Mumbai Attacks
Funniest Cyber Crimes that actually worked.pptx

This session gives you real-life insights and examples of the most ridiculous cyber-attacks and the smartest cyber-crimes that have occurred over the last 30 years. Each director from CSP tell their own personal stories from working in the industry and from past clients, about the strangest and funniest cyber-crimes they have come across.
Yes, these examples are a laugh, but they also raise awareness of how easy it could be to fall victim to these cyber criminals and their attempts. So, we will be discussing how to protect your business also, and be more aware of their tell-tale signs and attempts to disrupt your business.
The Role of Social Media in Da'awah

The presentation underscores the role of social media in Da'awah related activities
Fake news, its ramifications and tools to check this menace.

What is Fake News, statistics related to it, tools to discover fake news,examples across countries, India scenario in the context of fake news, criticism of these tools and the effect of fake news on POTUS elections.
Does Twitter have a positive impact in the United States?

Just something I whipped up quickly for a debate at school.
Cyber-Stalking Threat to People or Bane to Technology

A day without the use of technology in our lives seems like an impossible mission. We have become entirely dependent on it in divergent ways. Technology has helped us in creating great ideas that we can communicate with people present anywhere on this earth. Apart from the fact that technology has made our lives easy, it also bought in a lot of difficulties. With the massive advancement of technology along with the evolution of time, the crime rate of cyber offences keeps increasing every day. One such cyber assault that requires immediate attention is cyber stalking. Cyber stalking involves continuous or persistent following of a person through electronic media with or without the persons consent. Cyber stalking, unlike the offline stalking, is severe as the identity of the perpetrator is unknown and geographical proximity is no barrier. The severity of cyber talking has increased in the recent times as the current generation is found all the time surfing on their phones or laptops and being busy with social networking media like Facebook, Instagram, Whatsapp and many more. The reason why one may become a cyber-stalker can be because of revenge, obsession, sadism, denial, insult and many more. The post effects of cyber stalking to a victim can be psychologically overwhelming that there are cases where the victims have committed suicide being incapable of coping with the psychological and emotional stress. Cyber stalking can be used to blackmail victims as well. It can also include morphing of the victims image with nude pictures and posting it on public and social websites thus destroying the reputation and dignity of the victim. One of the highly disadvantageous facts in cyber offences is that once such obscene picture of the victim is posted, the post gets shared to more and more people. Therefore even if the perpetrator is found and the origin where the obscene pictures were posted is deleted, it is difficult to find all places where the post has been shared. Thus its high time that more emphasis is laid on introducing effective and efficient laws in field of newly formed cyber offences such as cyber stalking. H. M. Shambhavee "Cyber-Stalking: Threat to People or Bane to Technology" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Volume-3 | Issue-2 , February 2019, URL: https://www.ijtsrd.com/papers/ijtsrd21354.pdf
Paper URL: https://www.ijtsrd.com/management/law-and-management/21354/cyber-stalking-threat-to-people-or-bane-to-technology/h-m-shambhavee
re:publica 2016 #rpTEN: CTRL

Speakers: Estelle Massé, Kirsten Fiedler, Maryant Fernández:
We live in an era of ubiquitous surveillance. Surveillance is however seldom a goal in itself, but part of a larger scheme of socio-political domination. This talk will examine a few pieces of the puzzle leading to societal control: control of your activities via the internet, of your thoughts via the media and of your movement via border surveillance.
Two years after the first Snowden revelations, awareness around governmental and corporate surveillance has entered the mainstream media. Yet, broad resistance has been slow to develop - partly because of the intangible nature of surveillance, and because it is just one piece of a much larger game of control. This talk aims at explaining how society is being controlled through the internet, the media and the surveillance of movements.
The Internet is an unprecedented human rights enabler. But governments and companies have developed a vision to connect people and things whose ultimate goal is to have everyone under control. To what extent do we need the Internet of Things? What are the consequences of using self-measurement apps? Do you think twice before posting something online?
In the past years, technological developments have propelled the possibilities for media control to a whole new level. While political spins and newspeak remain the preferred methods to control the public discourse, the growth of new media platforms has reached a point where companies influence what we buy, how we vote and how we feel. On multiple occasions, Facebook's users have already been subject to experiments in civic-engineering. What is media control and how does it affect us?
Historically, governments had an interest in controlling movement not only within their cities but also at their borders. In the past decade, ubiquitous surveillance has opened up a new range of possibilities for the constant monitoring of our movements by governments. Surveillance of air travellers and refugees RFID devices, thermic cameras, drones are just few examples. What are the consequences of this constant tracking on our rights?
The outcome of the three pieces of the puzzle show that we don't have a right to be different, we censor ourselves, we fear consequences of enjoying our freedoms, our life stops being ours. We will present solutions and creative alternatives to the audience.
Presentation Crisis Communications

This is a presentation I gave at the University of Utah's law school to a class about crisis communications. This is for 2011. The next one is coming soon.
The dark side of IA

The rise of AI now seems inevitable with many experts stating the invention of smart machines will be the biggest ever impact on humanity. Robot rebellions have been a major theme throughout science fiction for many decades, and we need precautionary measures to ensure future superintelligent machines remain under human control.
Similar to Role of Social Media during the Mumbai Attacks (20)
Fake news, its ramifications and tools to check this menace.

Fake news, its ramifications and tools to check this menace.
Does Twitter have a positive impact in the United States?

Does Twitter have a positive impact in the United States?
Cyber-Stalking Threat to People or Bane to Technology

Cyber-Stalking Threat to People or Bane to Technology
More from Corinne Weisgerber
Crisis communication & the Austin Bombings

A crisis communication case study of the Austin package bombings in March 2018.
A Parent's Guide to Keeping Kids Safe Online

Cybersafety workshop for parents on how to keep their children safe on the Internet and when using mobile devices. Developed for the Online Safety Education for Families (OSEF) Program - a program of Oak Hill United Methodist Church Community Ministries.
Disrupting the Disruption in Higher Education - SXSWedu 2015

For years, we've been told that the higher education system is broken and its demise is near. EdTech companies and startups have responded to this doomsday scenario by offering promises of salvation and calls for disruptive innovation. Voices critical of corporate intrusion into higher education are often framed as resisting change. This panel will examine the forces calling for disruption from a pedagogically informed critical perspective and add a much needed faculty voice to the debate. - See more at: http://schedule.sxswedu.com/events/event_EDUP33336
Teaching with Storify, Diigo and HootSuite

Presentation created for the 2014 National Communication Conference in Chicago, IL.
Du professeur connecté à l'étudiant connecté: Vers une pédagogie stratégique ...

Conférence sur les TICE et le rôle des médias sociaux dans l'école numérique donnée le 7 janvier 2014 à l'Université Paris 1, Panthéon, Sorbonne.
Presentation given to the faculty of the Sorbonne University in Paris, France on January 7, 2014. Video of the presentation can be found here: http://bit.ly/2cW8Rm6
The Networked Academic

Condensed version of the "Networked Academic" slideshow to be presented at the 2013 National Communication Association's annual convention in Washington, D.C.
Social Media for Churches

Presentation on social media for church created for the Clergy Leadership Institute social media workshop on May 4th, 2013 in Austin, TX.
Translated title: L'Église et les réseaux sociaux. Kirche und soziale Medien.
Social Media Metrics for Academics

Presentation for an HP Catalyst Online Workshop on how academics can measure the outcomes of their social media efforts — and use those metrics to improve their content and scientific reputation.
Communicating Hurricane Evacuation Orders: A Case Study

This is an old presentation from 2006 on leadership and media communication in the wake of Hurricane Rita. Considering the threat posed by Hurricane Sandy and the extent of the evacuation orders all along the East Coast, I figured it might be a timely presentation to share.
Full citation: Weisgerber, C. & Butler, S. (2006, April). “Should we stay or should we go? Leadership communication in the face of a potentially catastrophic hurricane”. Paper presented to the Crisis Communication Division of the Southern States Communication Association, Dallas, TX.
Negotiating multiple identities on the social web

Presentation on the fragmentation of online identities, the inadequacy of the personal branding metaphor and the idea of the multiverse as a new metaphor for thinking about online identity. For a transcript of the keynote, see this blog post: http://academic.stedwards.edu/socialmedia/blog/2011/11/16/negotiating-multiple-identities-on-the-social-web-goffman-fragmentation-and-the-multiverse/
Re-envisioning Modern Pedagogy: Educators as Curators

Presentation given at SXSWedu on March 6, 2012. The podcast of the presentation can be found here: http://audio.sxsw.com/2012/podcasts/edu/06_Re_envisioning_Pedagogy.mp3
Building Thought Leadership through Content Curation

Presentation given at WebCom Montreal, November 16, 2011
Social Media & Interreligious Understanding

Slides from a presentation for Campus Ministry, titled: "Social Media Sites and Interreligious Understanding." In this presentation I discuss the challenges sparked by misrepresentation of religions in social media and methods for civil discourse and dialogue.
Empowering students through personal learning networks

Presentation on "Empowering Students through Personal Learning Networks" given at SXSWedu on Wednesday, 03/09. Listen to the podcast of our presentation here: http://audio.sxsw.com/2011/podcasts/EDU/EmpoweringStudents_Weisgerber.mp3
Curating news

Slides on news curation from my St. Edward's University Interactive Media: Production and Design class. Discusses news curation, examines Andy Carvin's use of Twitter news curation and explains how to curate news using tools such as Twitter lists, Twitter widgets, Storify and Paper.li.
Egypt's role in highlighting 21st century Internet issues

Slides from my social media class discussing the 21st century Internet issues raised by the recent protests in Egypt and the Egyptian government's decision to shut down the Internet
Re-interpreting the Social Media Dream

Illusions of Empowerment: Re-interpreting the Social Media Dream. Paper presented to the Human Communication and Technology Division/Critical & Cultural Studies Division at the 2010 Annual Convention of the National Communication Association.
PRSSA Twitter Workshop

Slidedeck for a Twitter workshop for the St. Edward's University PRSSA chapter
More from Corinne Weisgerber (20)
Disrupting the Disruption in Higher Education - SXSWedu 2015

Disrupting the Disruption in Higher Education - SXSWedu 2015
Du professeur connecté à l'étudiant connecté: Vers une pédagogie stratégique ...

Du professeur connecté à l'étudiant connecté: Vers une pédagogie stratégique ...
Communicating Hurricane Evacuation Orders: A Case Study

Communicating Hurricane Evacuation Orders: A Case Study
Re-envisioning Modern Pedagogy: Educators as Curators

Re-envisioning Modern Pedagogy: Educators as Curators
Building Thought Leadership through Content Curation

Building Thought Leadership through Content Curation
Empowering students through personal learning networks

Empowering students through personal learning networks
Egypt's role in highlighting 21st century Internet issues

Egypt's role in highlighting 21st century Internet issues
Recently uploaded
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
Essentials of Automations: Optimizing FME Workflows with Parameters

Are you looking to streamline your workflows and boost your projects’ efficiency? Do you find yourself searching for ways to add flexibility and control over your FME workflows? If so, you’re in the right place.
Join us for an insightful dive into the world of FME parameters, a critical element in optimizing workflow efficiency. This webinar marks the beginning of our three-part “Essentials of Automation” series. This first webinar is designed to equip you with the knowledge and skills to utilize parameters effectively: enhancing the flexibility, maintainability, and user control of your FME projects.
Here’s what you’ll gain:
- Essentials of FME Parameters: Understand the pivotal role of parameters, including Reader/Writer, Transformer, User, and FME Flow categories. Discover how they are the key to unlocking automation and optimization within your workflows.
- Practical Applications in FME Form: Delve into key user parameter types including choice, connections, and file URLs. Allow users to control how a workflow runs, making your workflows more reusable. Learn to import values and deliver the best user experience for your workflows while enhancing accuracy.
- Optimization Strategies in FME Flow: Explore the creation and strategic deployment of parameters in FME Flow, including the use of deployment and geometry parameters, to maximize workflow efficiency.
- Pro Tips for Success: Gain insights on parameterizing connections and leveraging new features like Conditional Visibility for clarity and simplicity.
We’ll wrap up with a glimpse into future webinars, followed by a Q&A session to address your specific questions surrounding this topic.
Don’t miss this opportunity to elevate your FME expertise and drive your projects to new heights of efficiency.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI)
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Recently uploaded (20)
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
Essentials of Automations: Optimizing FME Workflows with Parameters

Essentials of Automations: Optimizing FME Workflows with Parameters
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...

Empowering NextGen Mobility via Large Action Model Infrastructure (LAMI): pav...
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Role of Social Media during the Mumbai Attacks
- 1. #mumbai Social Media in Times of Crisis
- 2. Timeline of the Reporting on Social Media Sites
- 3. CBS Story on Citizen Journalism
- 6. 80 tweets sent to Twitter via SMS every five seconds - (Source: CNN)
- 7. #mumbai tweets: peak of roughly 1,000/hr Screenshot courtesy of Gauvra Mishra, taken at 12:18 pm India time 11/28
- 8. Vinu’s stream “ Taken late night Nov 26 at Colaba. Arranged in the order I took the snaps as I visited this place - 15 mins after I heard the sound. 2 mins walking distance from my house. “
- 10. Google Map of the attack sites Use of geo-tagging
- 12. A Question of Accuracy
- 13. A Question of Accuracy “Sure, lots of Twitter messages are flat out wrong and can spread disinformation. But as Ingram notes in his blog post above, other people tend to immediately correct those errors. Bad information is quickly drowned out by good information.” - Michael Arrington, TechCrunch
- 14. A Question of Accuracy “Sure, lots of Twitter quot;It was actually an messages are flat out incoherent, rumour- wrong and can spread fueled mob operating in disinformation. But as a mad echo chamber of Ingram notes in his blog tweets, re-tweets and re- post above, other people re-tweets. During the tend to immediately hour or so I followed on correct those errors. Bad Twitter there were wildly information is quickly differing estimates of drowned out by good the numbers killed and information.” injured - ranging up to 1,000.quot; - Michael Arrington, TechCrunch - Blogger Tim Mallon (Source: CNN)
- 17. Did the Indian government originate that message? Amy Gahran, an editor of the Poynter Institute's E-Media Tidbits blog tracked down the original message to a Twitter user named Mark Bao, who is a high school junior based in Boston.
- 18. ? Food for Thought • What is more important in reporting: immediacy or accuracy? • Who/what is the media nowadays? • How can we apply the social media lessons learned from this incident to PR? • Does social media feed terrorists sensitive info? Could it be used as a terrorism tool?
- 19. Credits Dr. Corinne Weisgerber St. Edward’s University Blog: http://socialmediaprclass.blogspot.com Email: corinnew@stedwards.edu Opening Slide Photo Credit: Surag (Flickr:.rGz)
