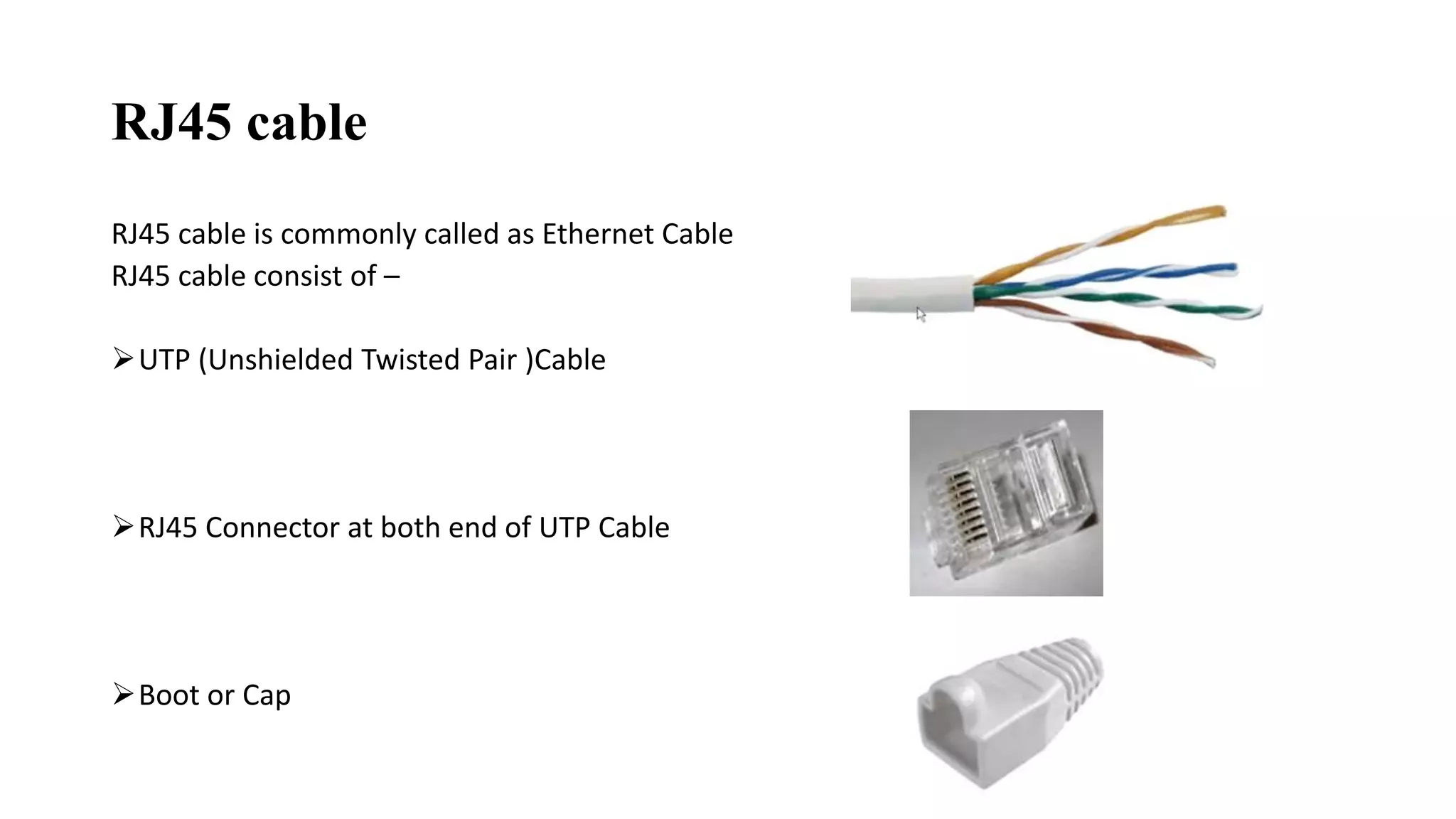
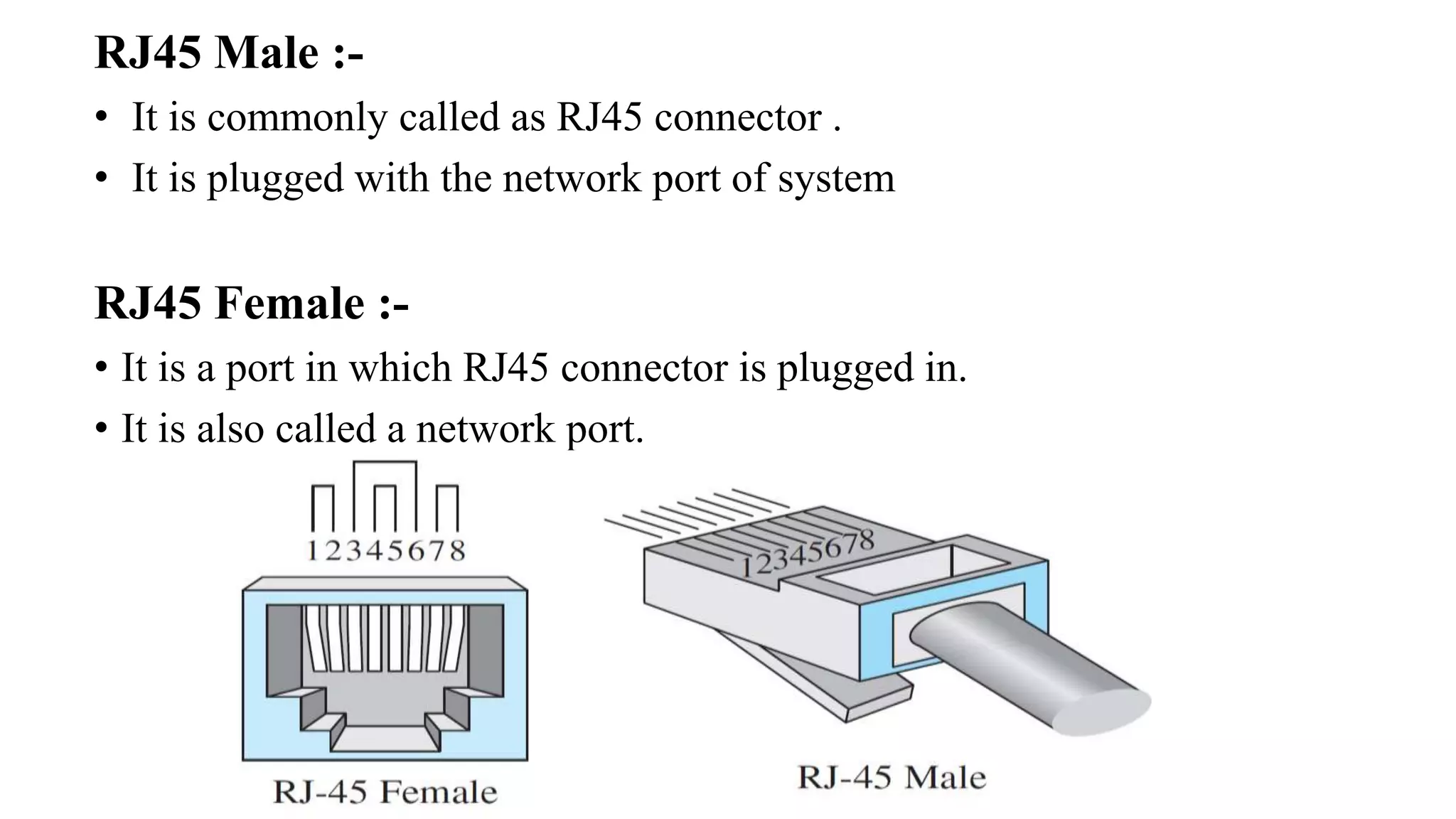
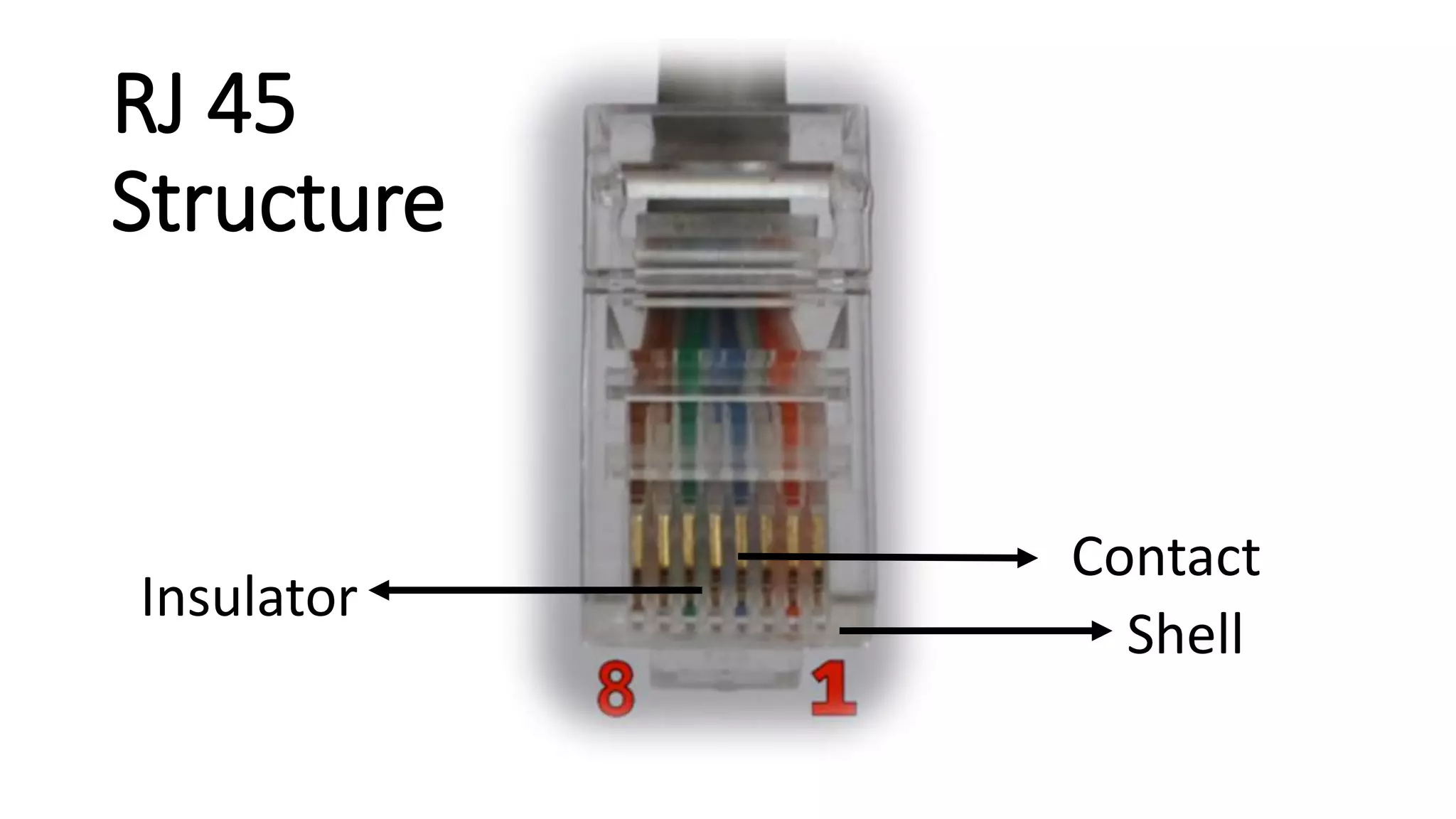
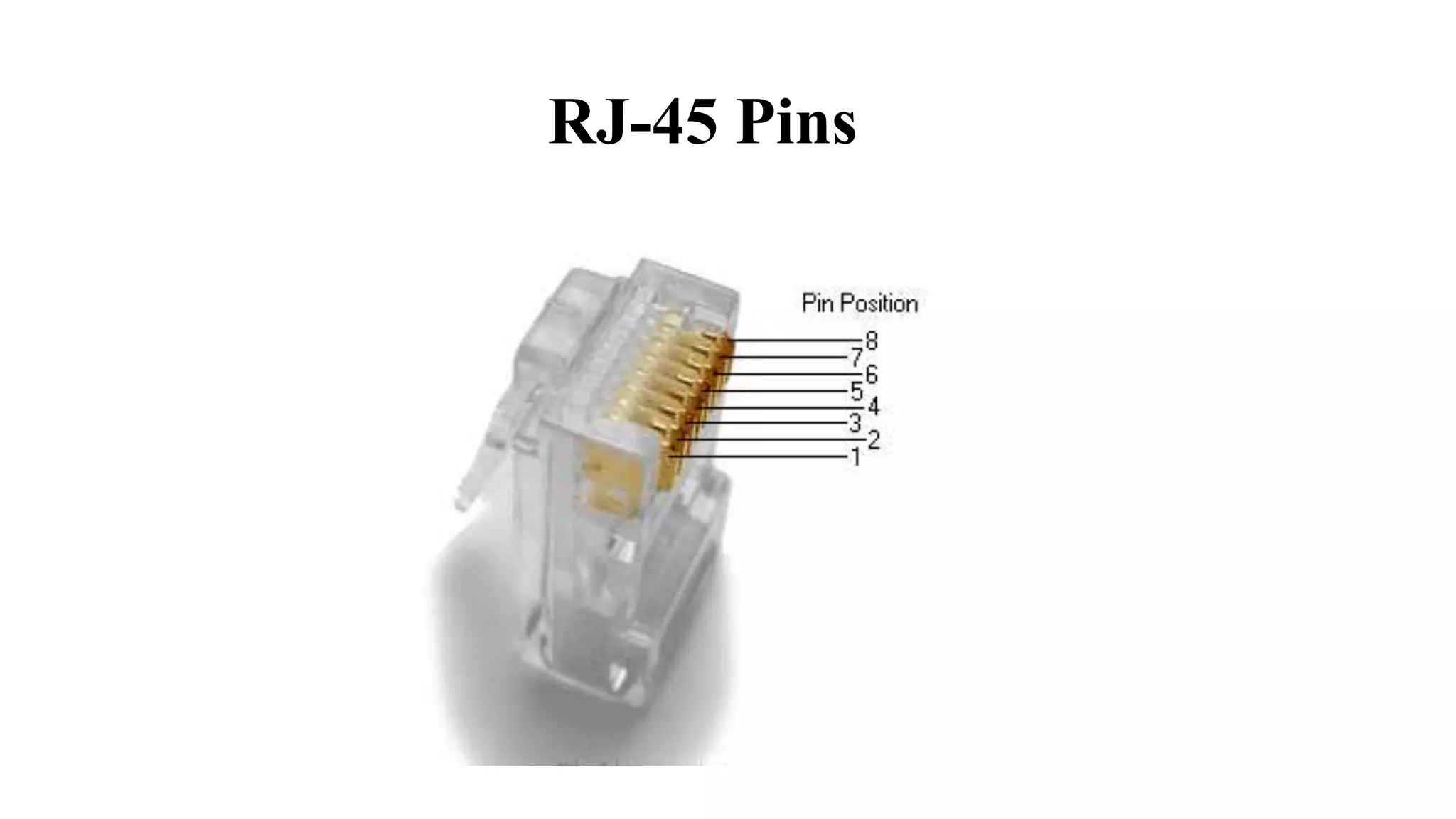
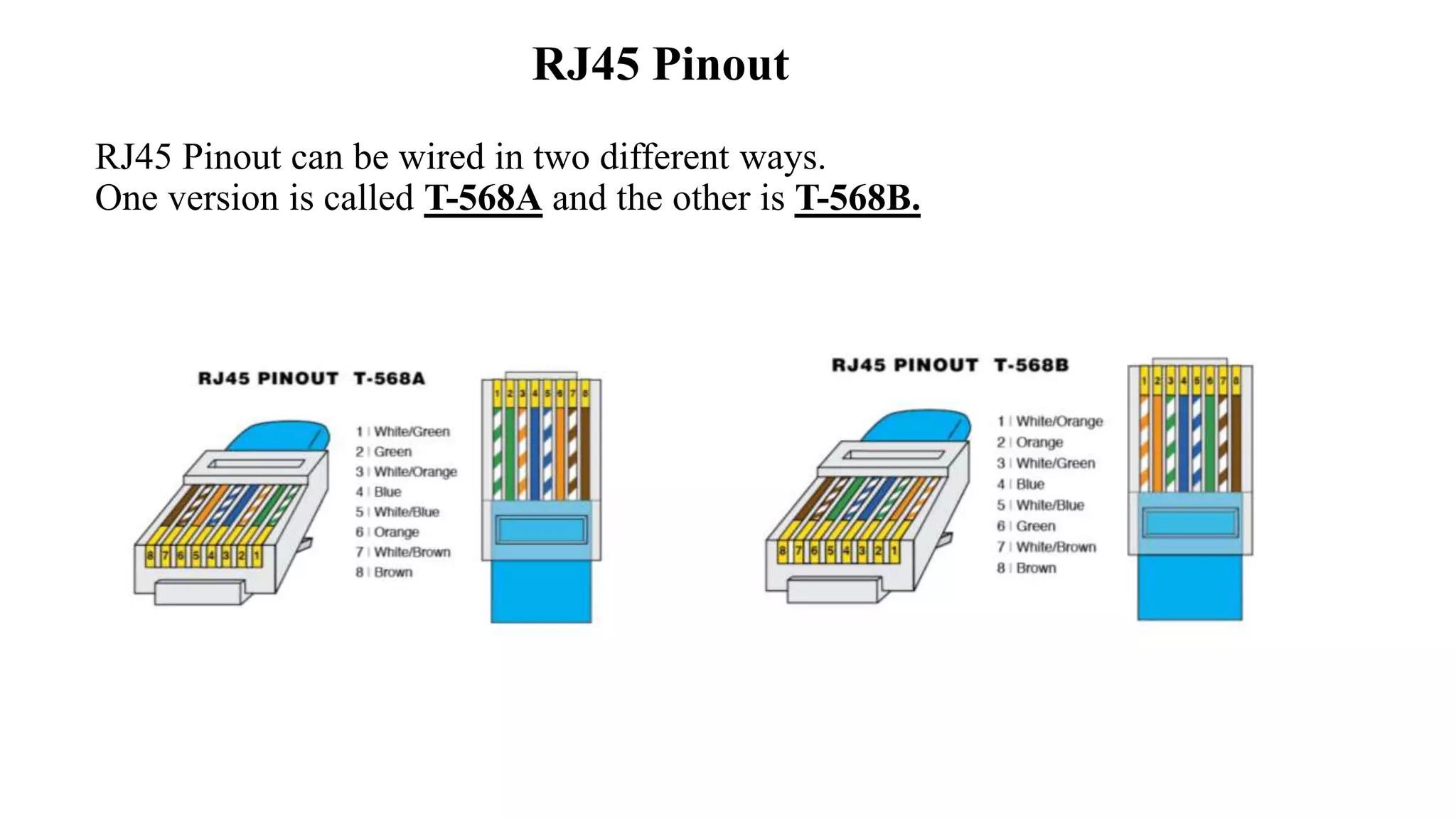
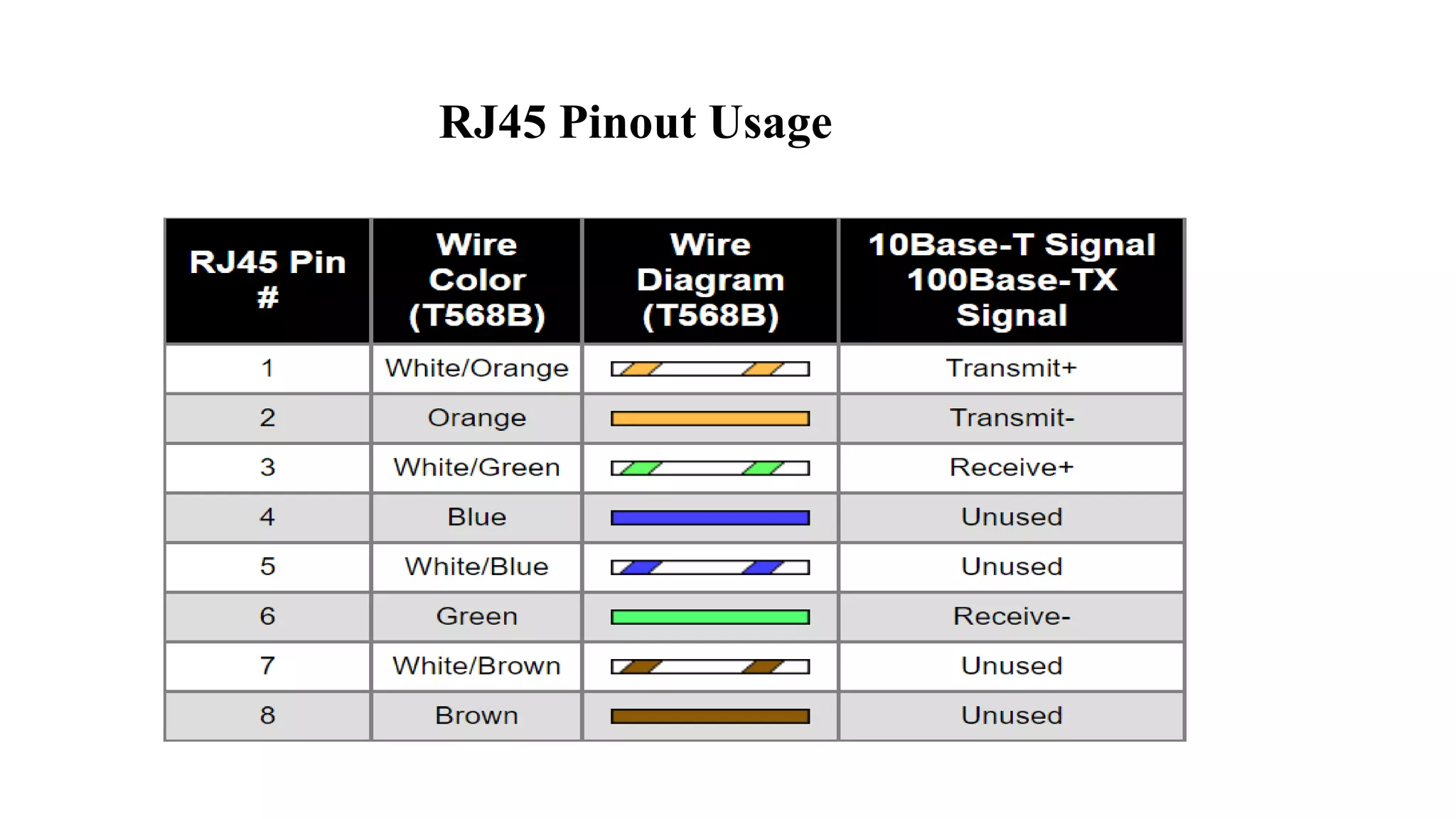
RJ45 is a standardized 8P8C modular connector commonly used for Ethernet cabling. It consists of an unshielded twisted pair cable with an RJ45 connector on each end. The RJ45 connector has eight pins in a specific arrangement and is used to connect devices to networks or each other via twisted pair cables like CAT5. Its standardized design makes it reliable for transmitting digital signals in local area networks and other applications.