This document outlines a server and client for remote command execution. The server runs on a specified port, accepts connections from clients, and executes commands sent by the client using a bash process. It returns the output to the client. The client connects to the server, takes input from the user and sends it to the server, and prints the response until it receives a "bye" message. References are provided for the source code and presentation platform used.

![Introduction The Server The Echo Client References
THE SERVER II
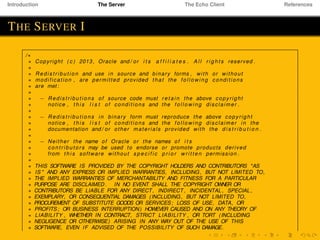
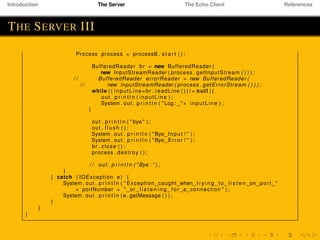
∗/
import java . net . ∗ ;
import java . io . ∗ ;
public class TelnetServer {
public static void main ( String [ ] args ) throws IOException {
i f ( args . length != 1) {
System . err . p r i n t l n ( "Usage : java EchoServer <port number>" ) ;
System . e x i t ( 1 ) ;
}
int portNumber = Integer . parseInt ( args [ 0 ] ) ;
try (
ServerSocket serverSocket =
new ServerSocket ( Integer . parseInt ( args [ 0 ] ) ) ;
Socket clientSocket = serverSocket . accept ( ) ;
P r i n t W r i t e r out =
new P r i n t W r i t e r ( clientSocket . getOutputStream ( ) , true ) ;
BufferedReader in = new BufferedReader (
new InputStreamReader ( clientSocket . getInputStream ( ) ) ) ;
) {
String inputLine ;
String n u l l S t r =null ;
while ( ( inputLine = in . readLine ( ) ) != null ) {
ProcessBuilder processB=new ProcessBuilder ( " bash " , "−c " , inputLine ) ;
processB . redirectErrorStream ( true ) ;](https://image.slidesharecdn.com/8ttz1nwql2ivbgu5uwr3-signature-f5aa2eeab0317103d0fb5e8f2499850e617839f0d48c9d5ac13820c585fb0c35-poli-151117125228-lva1-app6892/85/Remote-Command-Execution-8-320.jpg)
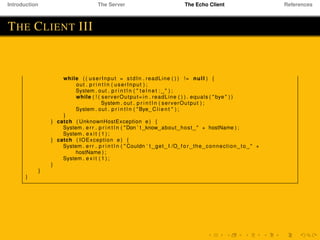
![Introduction The Server The Echo Client References
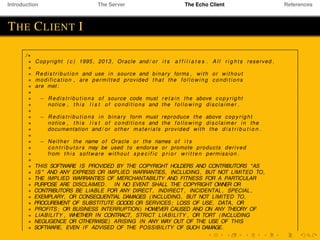
THE CLIENT II
∗/
import java . io . ∗ ;
import java . net . ∗ ;
public class TelnetClient {
public static void main ( String [ ] args ) throws IOException {
i f ( args . length != 2) {
System . err . p r i n t l n (
"Usage : java TelnetClient <host name> <port number>" ) ;
System . e x i t ( 1 ) ;
}
String hostName = args [ 0 ] ;
int portNumber = Integer . parseInt ( args [ 1 ] ) ;
try (
Socket echoSocket = new Socket ( hostName , portNumber ) ;
P r i n t W r i t e r out =
new P r i n t W r i t e r ( echoSocket . getOutputStream ( ) , true ) ;
BufferedReader in =
new BufferedReader (
new InputStreamReader ( echoSocket . getInputStream ( ) ) ) ;
BufferedReader stdIn =
new BufferedReader (
new InputStreamReader ( System . in ) )
) {
String userInput , serverOutput ;](https://image.slidesharecdn.com/8ttz1nwql2ivbgu5uwr3-signature-f5aa2eeab0317103d0fb5e8f2499850e617839f0d48c9d5ac13820c585fb0c35-poli-151117125228-lva1-app6892/85/Remote-Command-Execution-11-320.jpg)