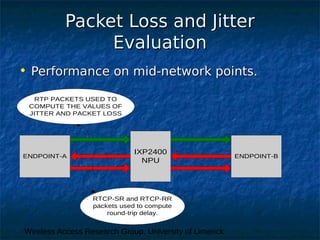
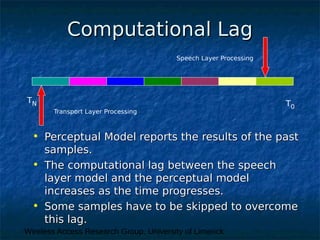
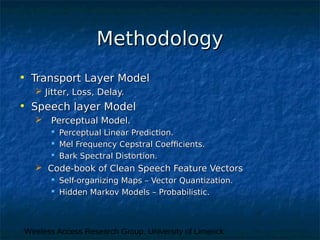
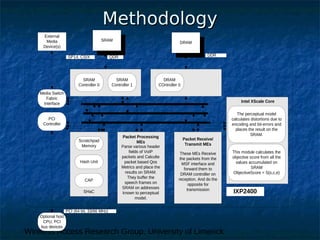
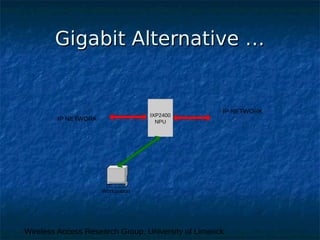
This document discusses research on developing a real-time, non-intrusive model for estimating speech quality over VoIP networks. The research aims to assess speech quality at mid-network points by evaluating both transport layer metrics like packet loss and jitter, as well as speech layer metrics using perceptual models. The current status describes capturing transport metrics from RTP/RTCP and implementing a perceptual model on an IXP2400 processor. Future work involves integrating the transport and speech models, testing under various network conditions, and evaluating the model for multiple calls and low bitrate codecs.