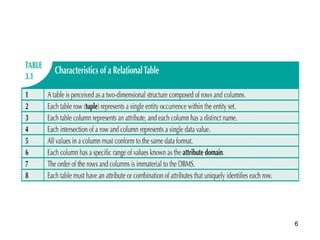
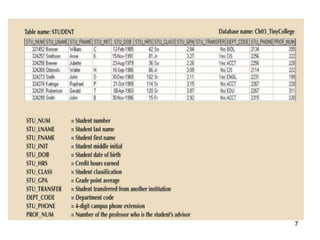
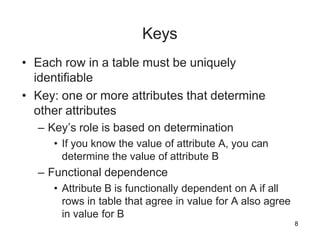
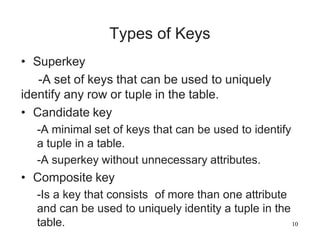
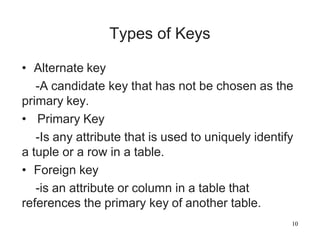
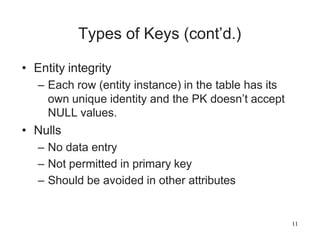
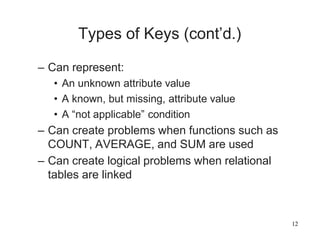
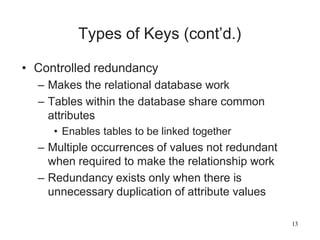
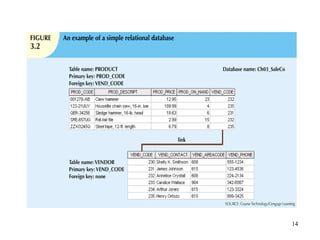
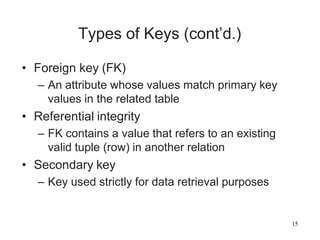
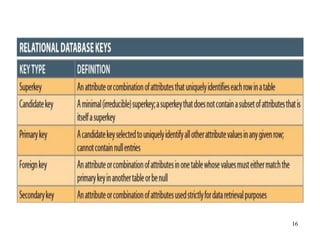
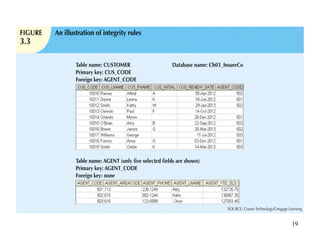
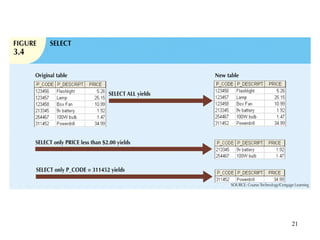
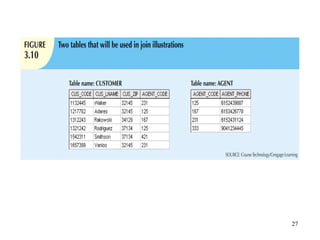
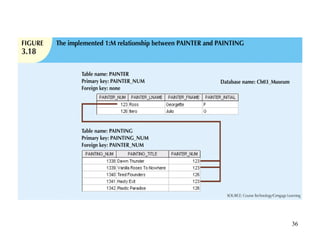
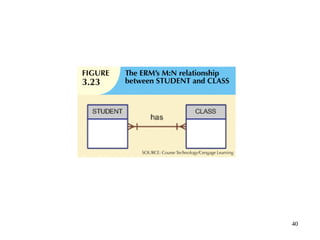
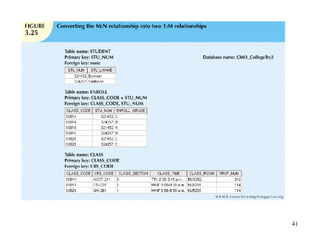
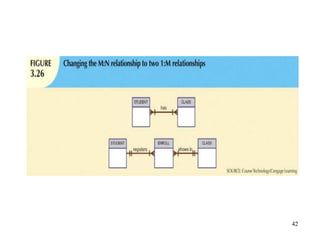
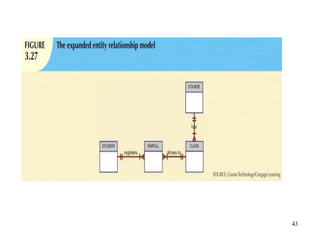
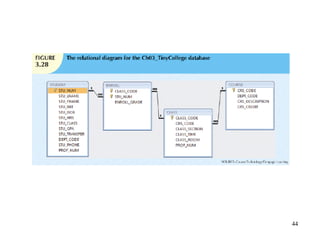
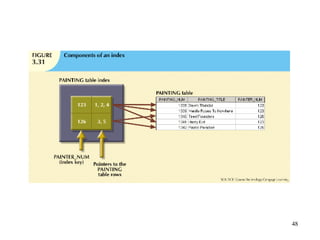
The relational database model offers a logical view of data based on relations composed of rows and columns. Relations are implemented as tables with primary keys to uniquely identify rows. Tables are linked through common attributes and operations like joins. Good design involves identifying entity relationships like one-to-one, one-to-many, and many-to-many and normalizing them.