Embed presentation
Download as PDF, PPTX




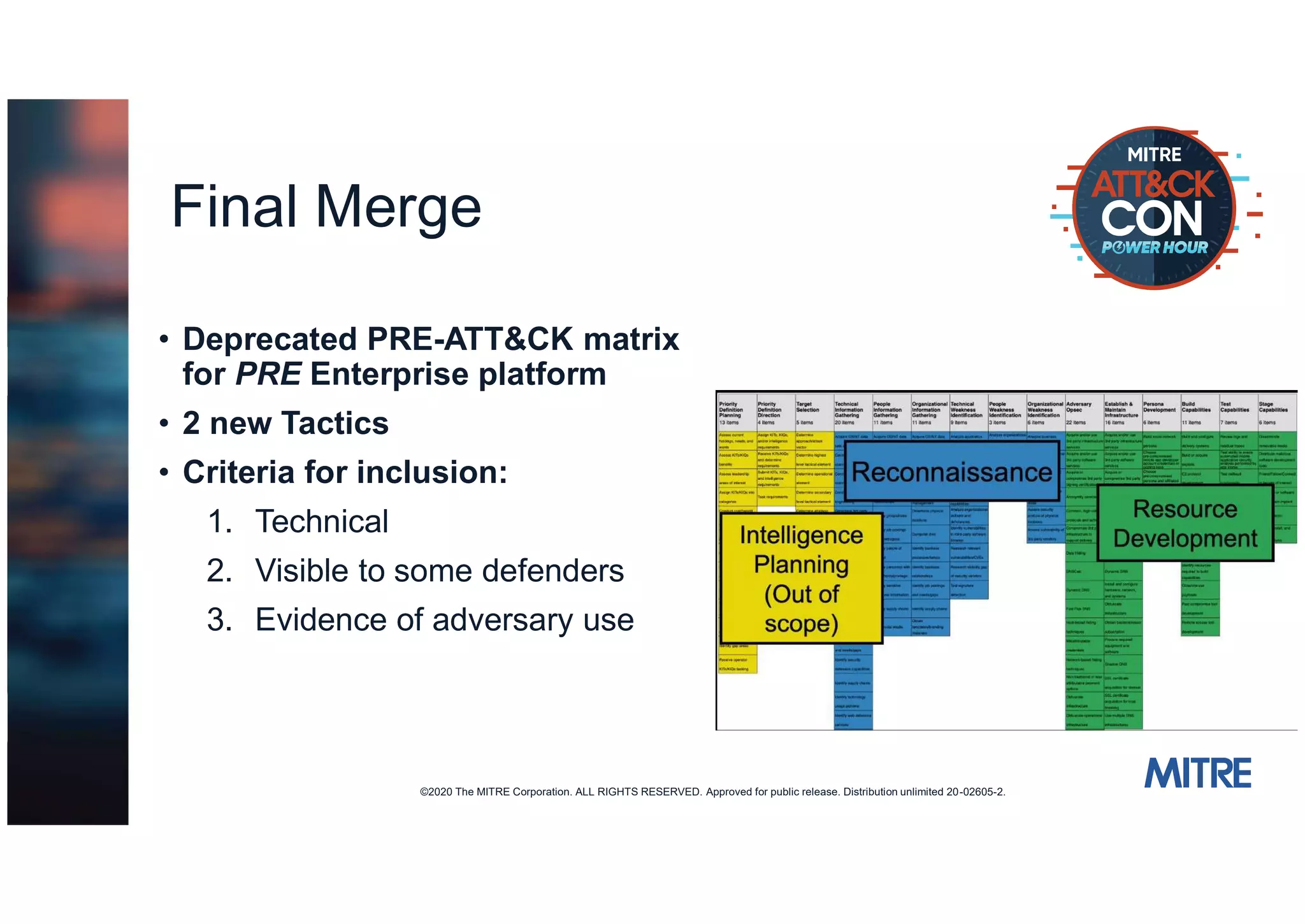

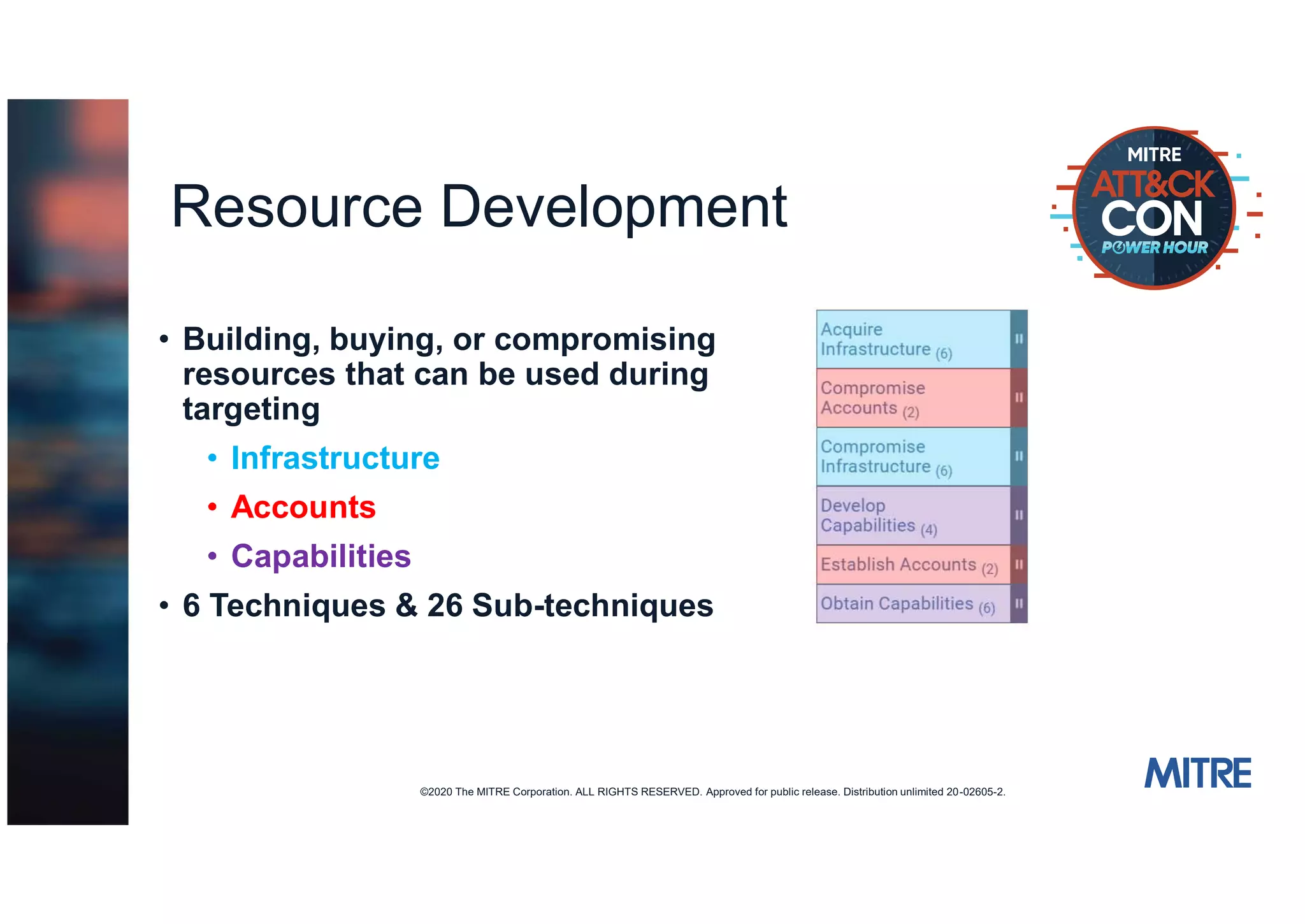



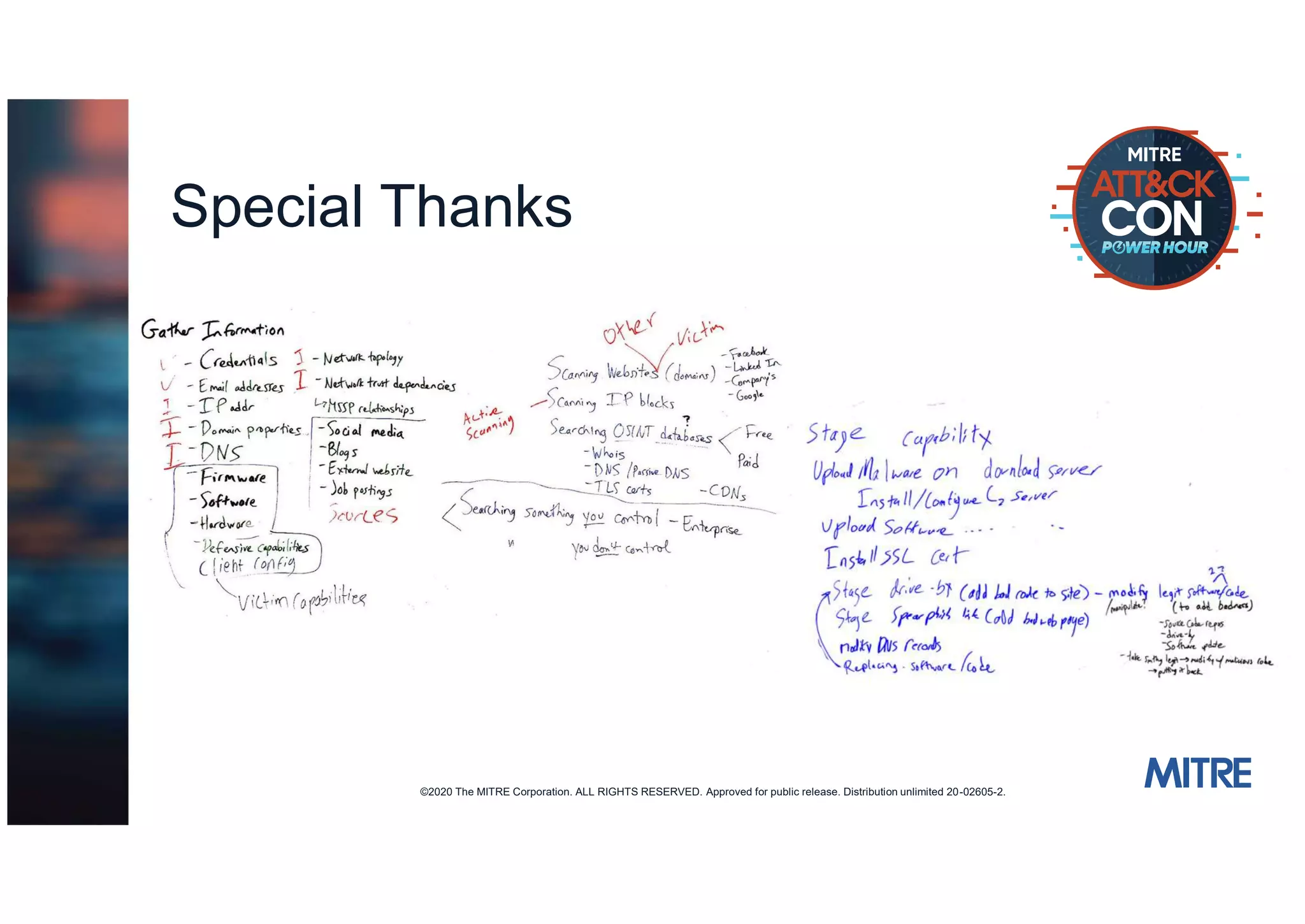

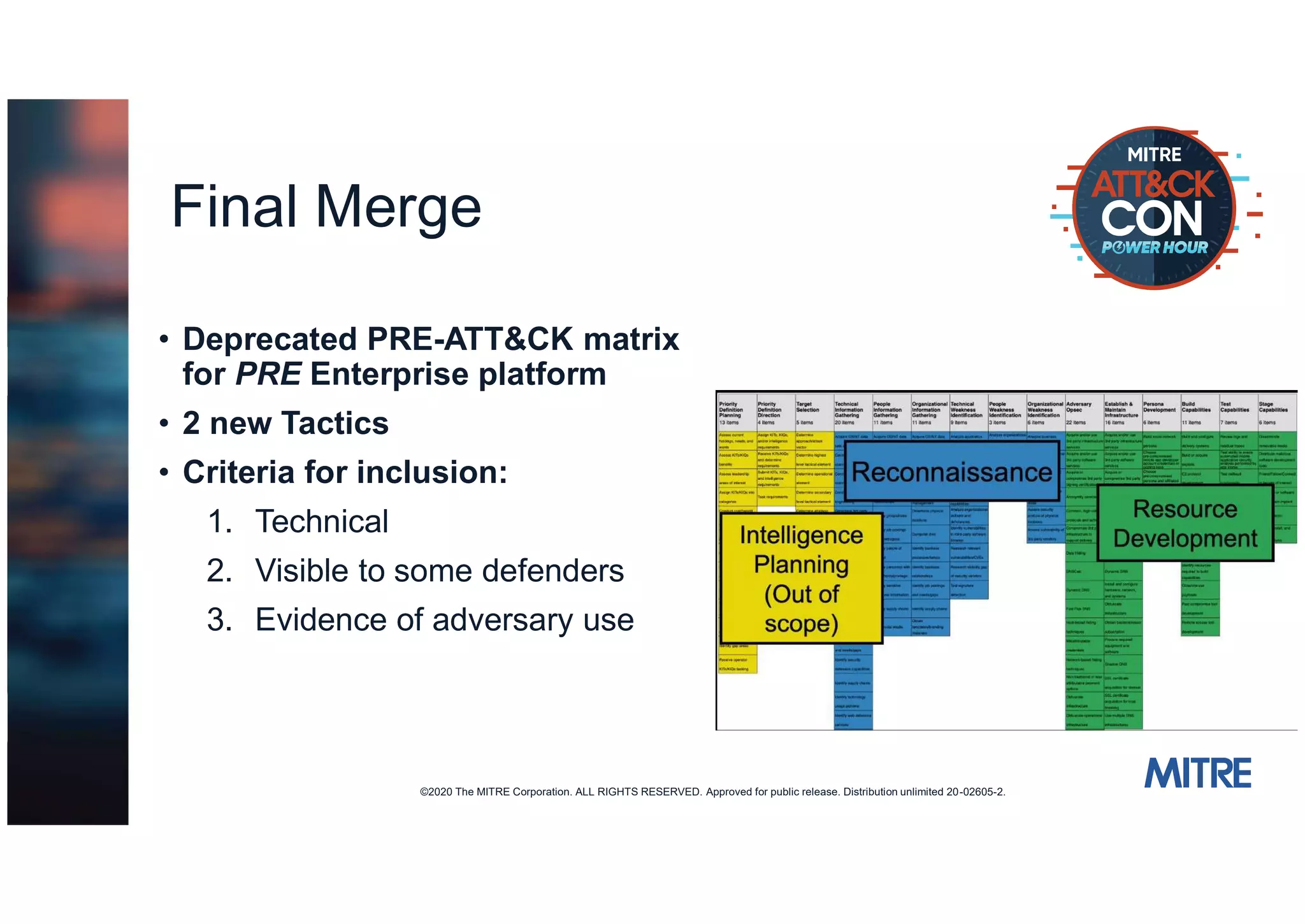
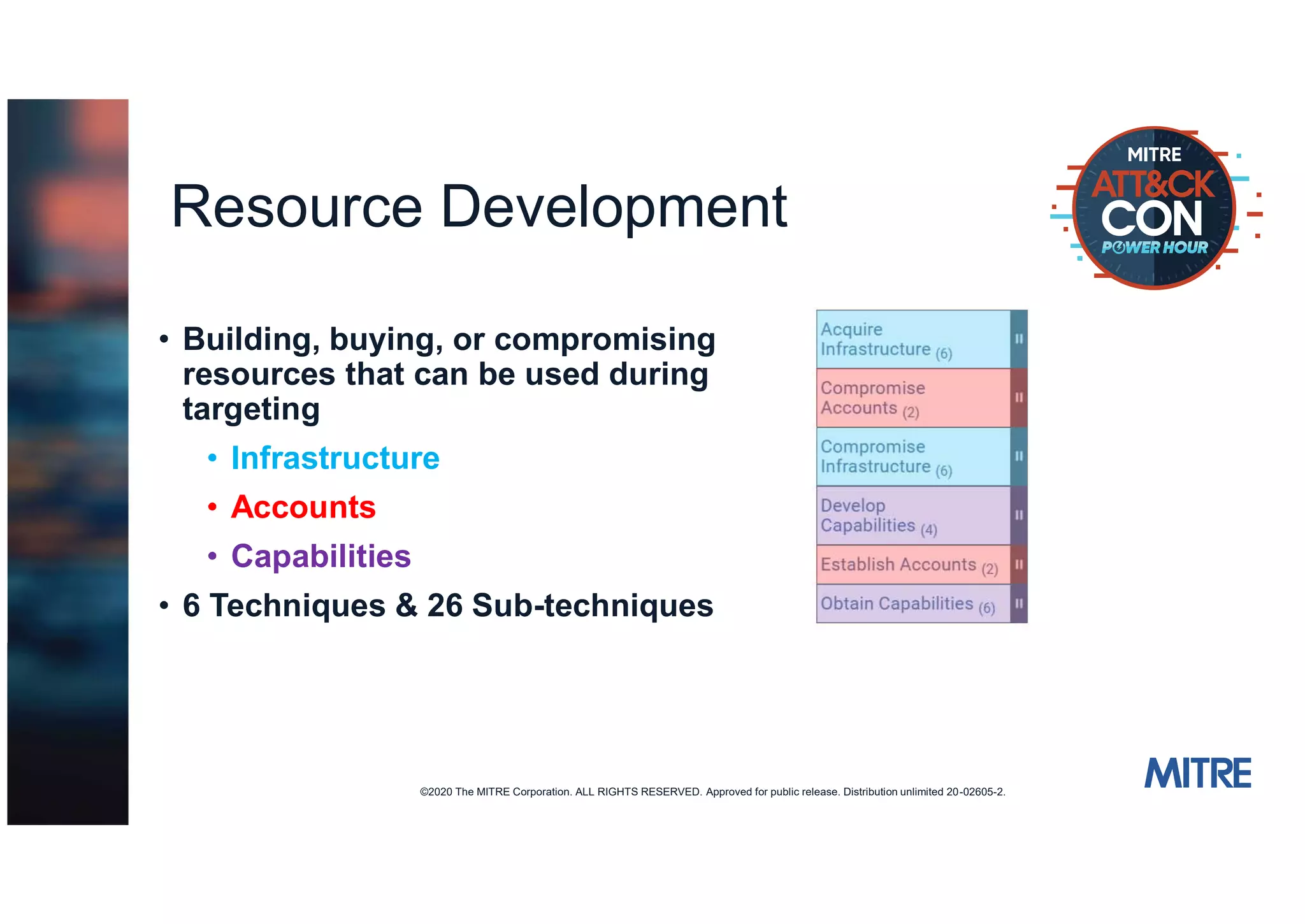
The document discusses changes made to the PRE-ATT&CK framework. It introduced two new pre-compromise tactics - Reconnaissance and Resource Development. Reconnaissance covers techniques for actively or passively gathering victim information. Resource Development covers techniques for building, buying, or compromising resources that can be used in targeting. The document encourages feedback and contributions to further improve PRE-ATT&CK.