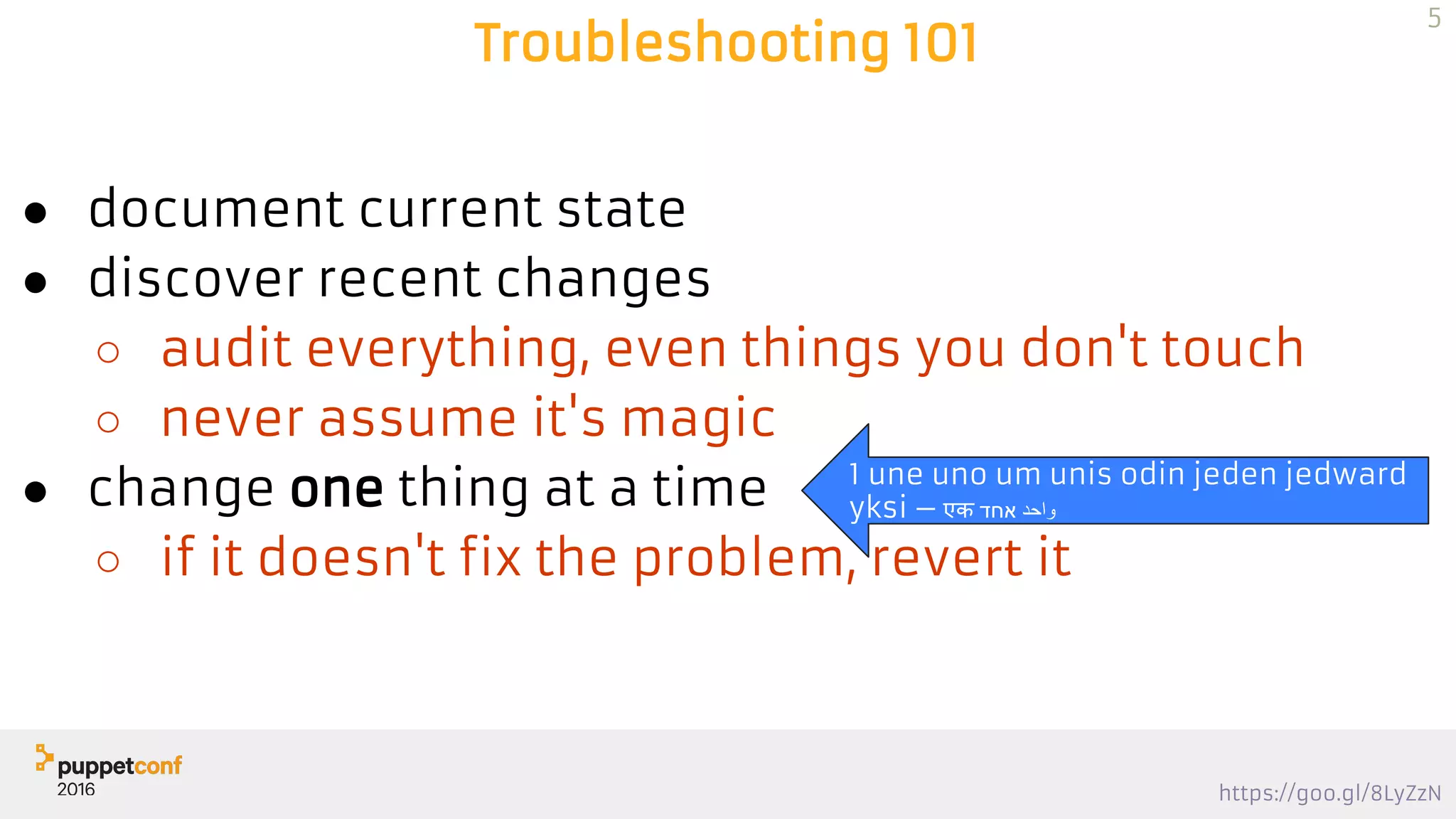
This document provides a comprehensive guide on troubleshooting Puppet, covering issues related to connections, certificates, and catalog compilations. It includes step-by-step instructions for identifying problems, verifying configurations, and using various tools for diagnostics. Key recommendations emphasize understanding the current state, implementing changes incrementally, and utilizing low-level tools to address issues effectively.



![https://goo.gl/8LyZzN
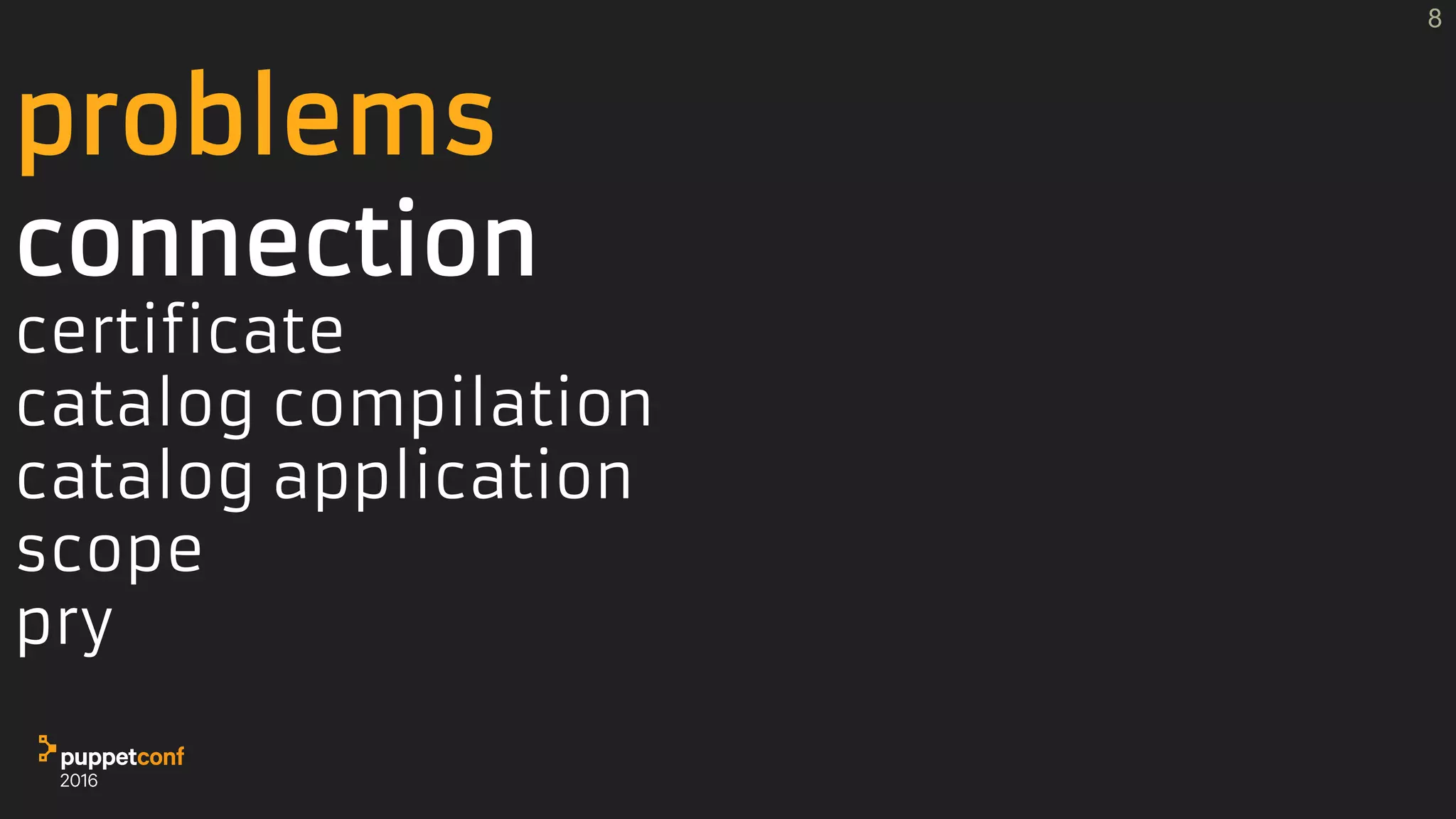
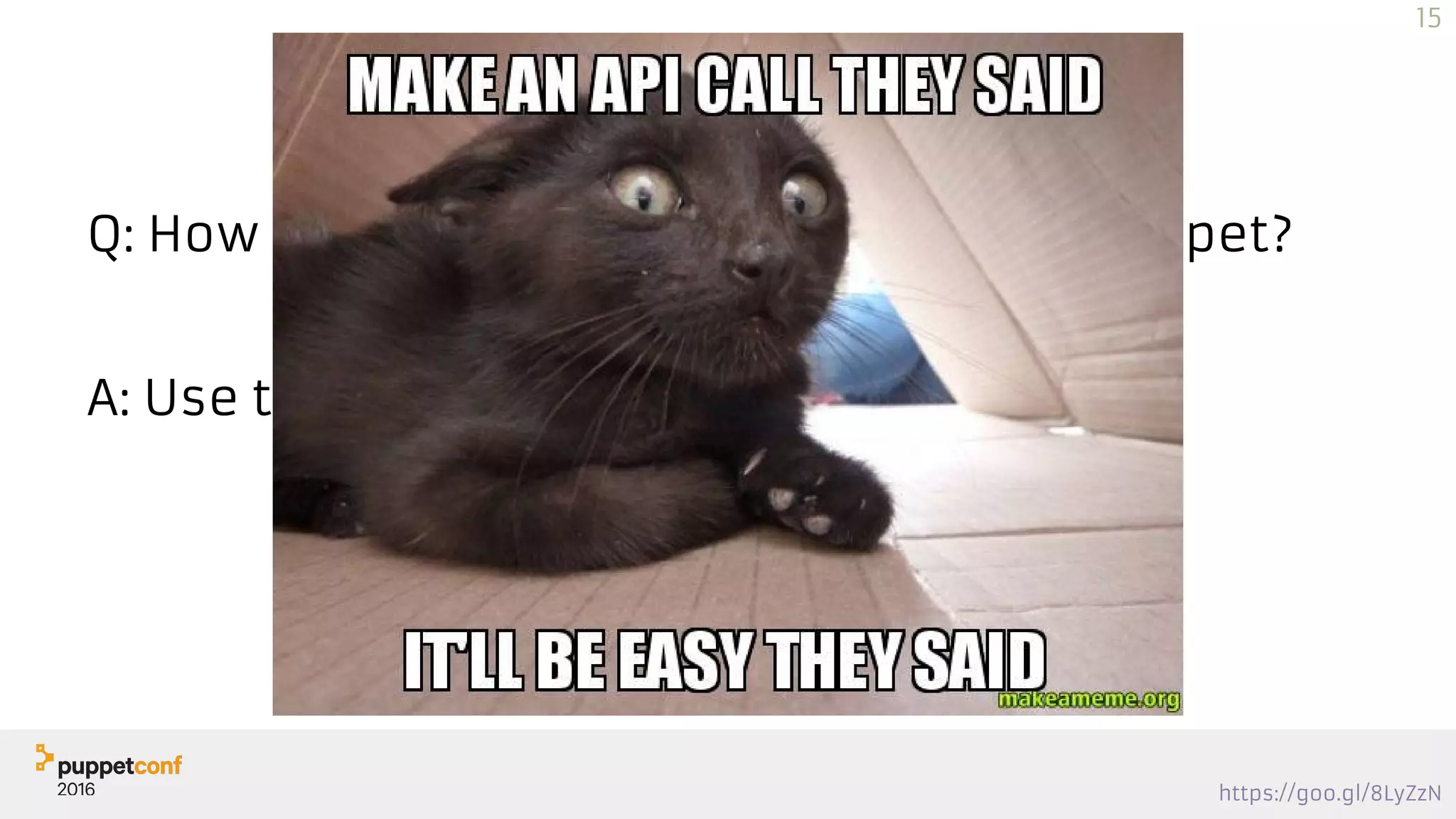
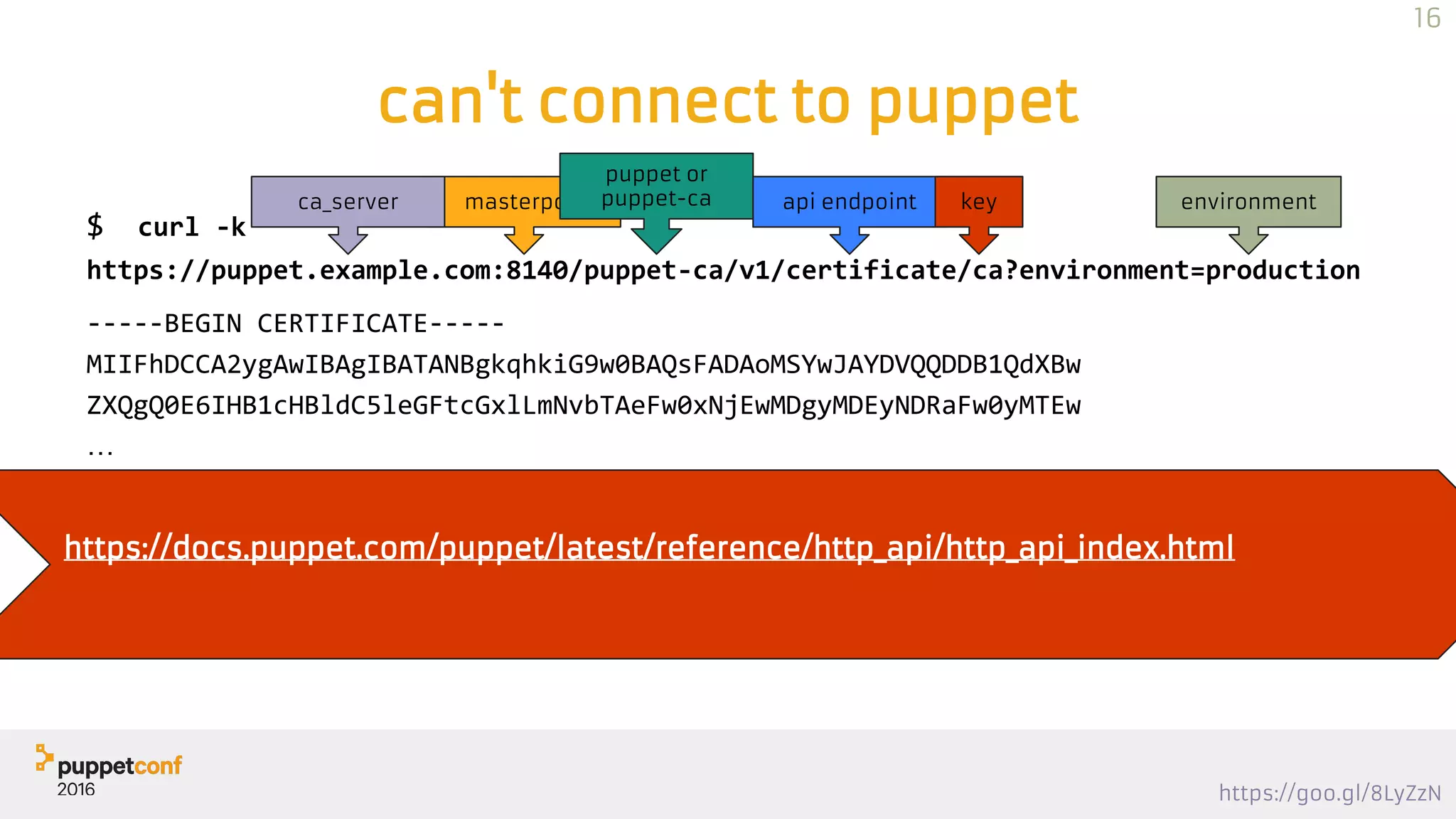
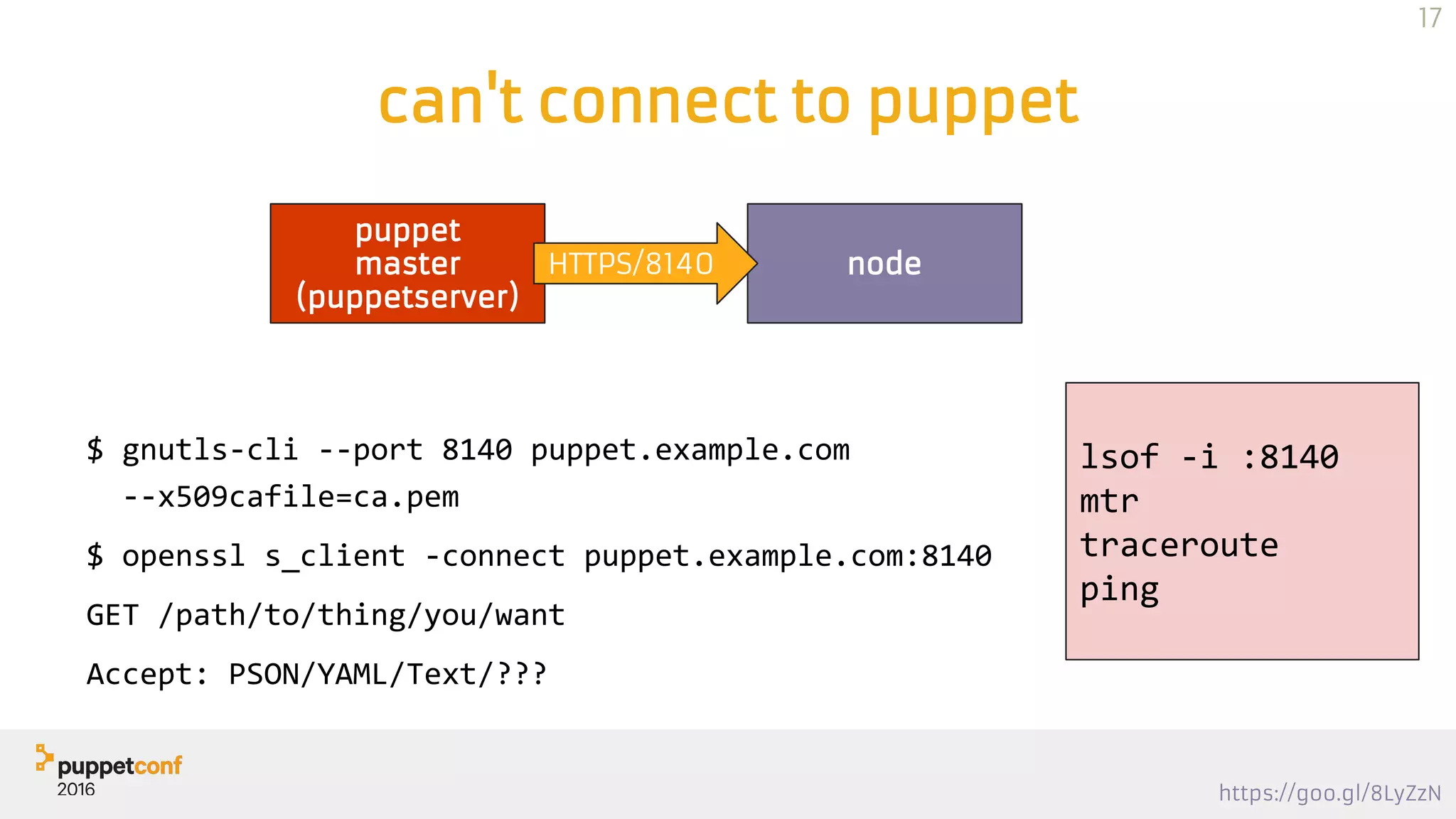
can't connect to puppet
$ curl --cert certs/cottage.pem --key private_keys/cottage.pem.orig --cacert
certs/ca.pem https://puppet.example.com:8140/puppet/v3/environments | jq
…
"environments": {
"production": {
"settings": {
"modulepath": [
"/etc/puppetlabs/code/environments/production/modules",
"/etc/puppetlabs/code/modules",
"/opt/puppetlabs/puppet/modules"
],
"manifest": "/etc/puppetlabs/code/environments/production/manifests",
"environment_timeout": 0,
"config_version": ""
19](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-19-2048.jpg)

![https://goo.gl/8LyZzN
PSON
Puppet JSON → PSON
$ jq <pson>
$ curl … | jq
JQ? sed for JSON
$ jq .environment catalog.pson
$ jq .classes catalog.pson
$ jq '.resources | length' catalog.pson
$ jq '.resources[] | select(.type == "Stage")' catalog.pson
21](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-21-2048.jpg)
![https://goo.gl/8LyZzN
PSON
Puppet JSON → PSON
$ jq <pson>
$ curl … | jq
JQ? sed for JSON
$ jq .environment catalog.pson
$ jq .classes catalog.pson
$ jq '.resources | length' catalog.pson
$ jq '.resources[] | select(.type == "Stage")' catalog.pson
Sometimes it's good to
go...
22](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-22-2048.jpg)




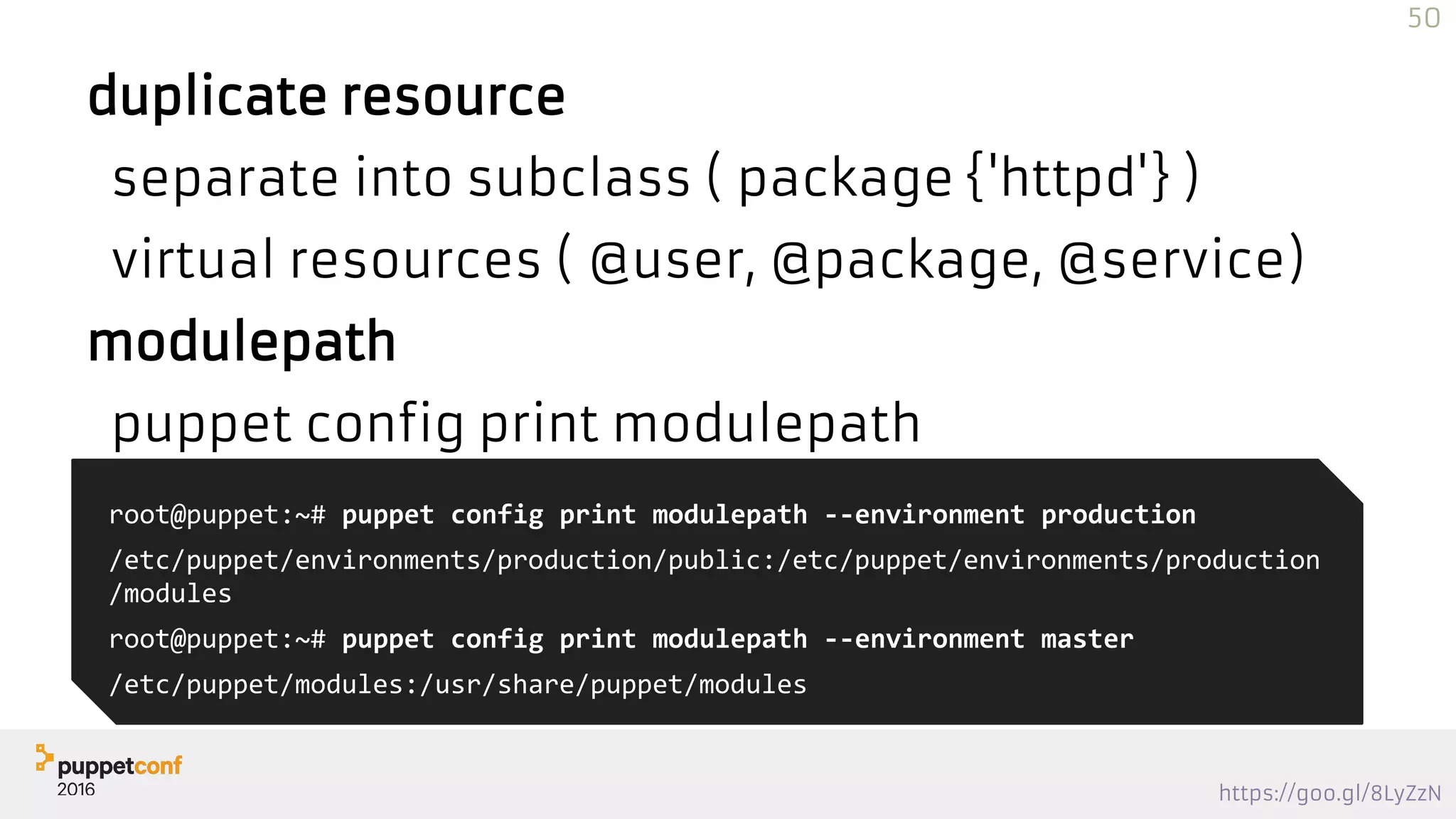
![https://goo.gl/8LyZzN
Compiling
$ sudo puppet master
--compile problem.example.com
--debug --trace
--logdest /tmp/problem.puppet.log
--environment sandbox
{
"data": {
"resources": [
{
"title": "main",
"exported": false,
"tags": ["stage"],
"type": "Stage",
"parameters": {
"before": "Stage[post]",
JSON
Thu Oct 23 14:34:24 -0700 2014 Puppet (debug): Using settings: adding
file resource 'bucketdir':
'File[/var/lib/puppet/bucket]{:loglevel=>:debug, :group=>"puppet",
:ensure=>:directory, :links=>:follow, :owner=>"puppet", :backup=>false,
:mode=>"750", :path=>"/var/lib/puppet/bucket"}'
Thu Oct 23 14:34:24 -0700 2014 Puppet (debug): Using settings: adding
file resource 'publickeydir':
'File[/var/lib/puppet/ssl/public_keys]{:loglevel=>:debug,
:group=>"puppet", :ensure=>:directory, :links=>:follow,
:owner=>"puppet", :backup=>false, :mode=>"755",
:path=>"/var/lib/puppet/ssl/public_keys"}'
Thu Oct 23 14:34:24 -0700 2014 Puppet (debug): Using settings: adding
file resource 'plugindest':
'File[/var/lib/puppet/lib]{:loglevel=>:debug, :ensure=>:directory,
:links=>:follow, :backup=>false, :path=>"/var/lib/puppet/lib"}'
Thu Oct 23 14:34:24 -0700 2014 Puppet (debug): Using settings: adding
file resource 'fileserverconfig':
'File[/etc/puppet/fileserver.conf]{:loglevel=>:debug, :ensure=>:file,
:links=>:follow, :backup=>false, :path=>"/etc/puppet/fileserver.conf"}'
43](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-43-2048.jpg)
: Executing 'echo $((`date +%S` /
86400))'
Debug: Executing 'echo $((`date +%S` / 86400))'
Notice: /Stage[main]/Main/Exec[epoch]/returns: executed successfully
44](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-44-2048.jpg)


![https://goo.gl/8LyZzN
help yourself
function verb() {
erb -P -x -T '-' $1 | ruby -c
is_ok $?
}
function vyaml() {
ruby -ryaml -e "YAML.load_file '$1'"
is_ok $?
}
function ppv() {
puppet parser validate $*
is_ok $?
}
49
function vepp() {
puppet epp validate $*
is_ok $?
}
function is_ok() {
if [ $1 == 0 ]; then
if [[ "$TERM" == *"xterm"* ]] ||
[[ "$TERM" == *"vt100"* ]]; then
echo -e "033[1mSyntax 033[32;1mOk!033[0m"
else
echo "Syntax Ok!"
fi
else
return $1
fi
}](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-49-2048.jpg)

![https://goo.gl/8LyZzN
Bad/Missing Variable
$one = "1"
file {"pcone":
path => "/tmp/pc$one",
ensure => 'directory',
}
file {"pc1":
path => "/tmp/pc1",
ensure => 'file',
}
Info: Caching catalog for puppet.example.com
Error: Evaluation Error: Error while evaluating a Resource
Statement, Cannot alias File[pc1] to ["/tmp/pc1"] at
/root/pc.pp:6; resource ["File", "/tmp/pc1"] already
declared at /root/pc.pp:2 at /root/pc.pp:6:3 on node
puppet.example.com
55](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-55-2048.jpg)
![https://goo.gl/8LyZzN
Bad/Missing Variable
$PC = 'puppetconf'
pc {'one':
place => "/tmp/$PC",
type => "directory",
}
pc {'two':
place => "/tmp/$PC",
type => "file",
}
define pc (
String $place,
String $type,
) {
file {"$title":
path => $place,
ensure => $type,
}
}
Info: Caching catalog for puppet.example.com
Error: Evaluation Error: Error while evaluating a Resource
Statement, Evaluation Error: Error while evaluating a
Resource Statement, Cannot alias File[two] to
["/tmp/puppetconf"] at /root/define.pp:5; resource ["File",
"/tmp/puppetconf"] already declared at /root/define.pp:5 at
/root/define.pp:5:2 at /root/define.pp:15 on node
puppet.example.com
56](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-56-2048.jpg)
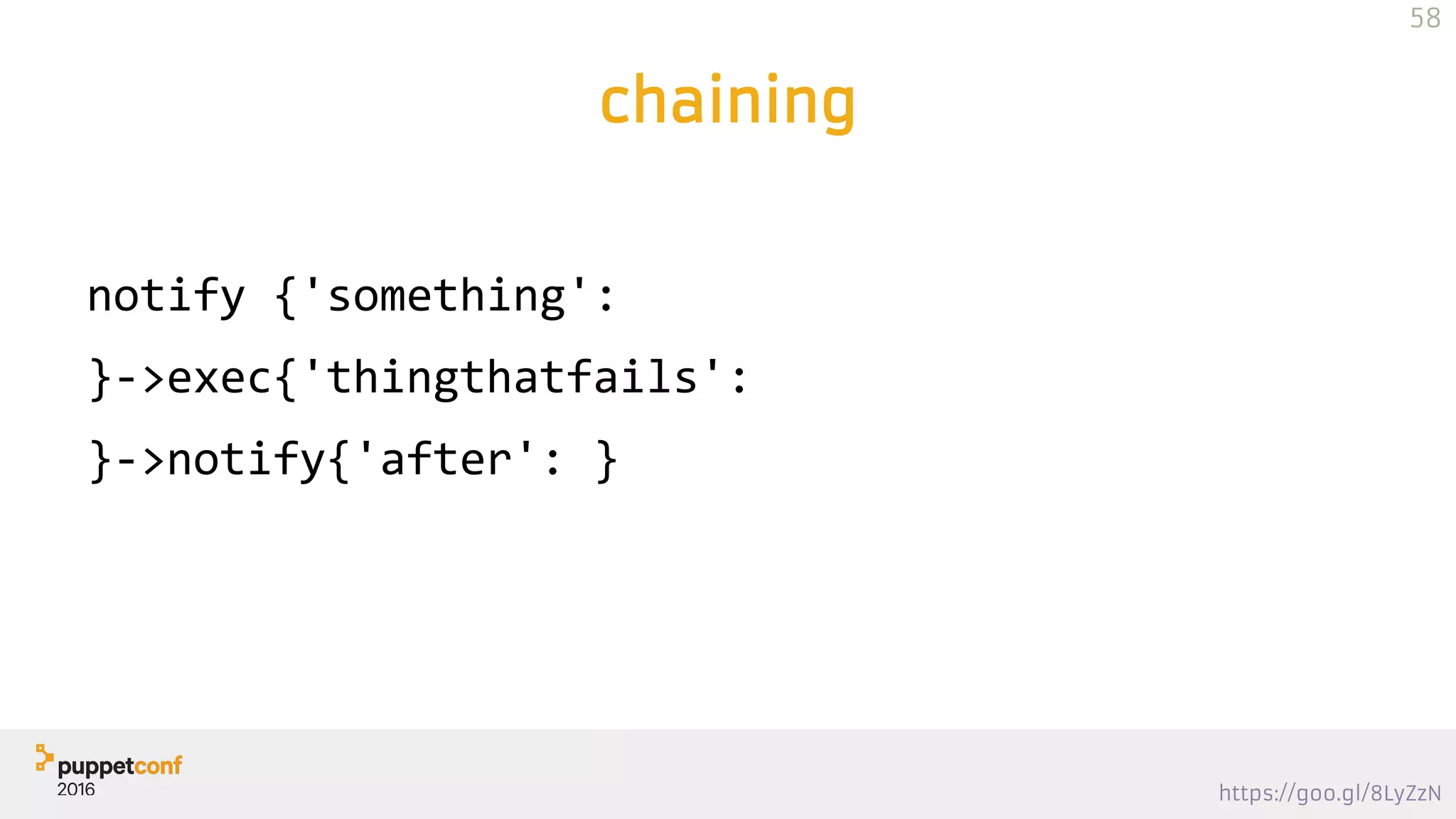
![https://goo.gl/8LyZzN
Checking
exec{'before resolv.conf':
command => '/usr/local/bin/puppet-debug before resolv.conf',
require => Class['debug']
} -> file { '/etc/resolv.conf':
source => template("dns/resolv.conf"),
noop => true,
}
class debug {
file {'puppet-debug':
path => '/usr/local/bin/puppet-debug',
source => 'puppet:///modules/debug/puppet-debug',
mode => 0755,
}
}
59](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-59-2048.jpg)
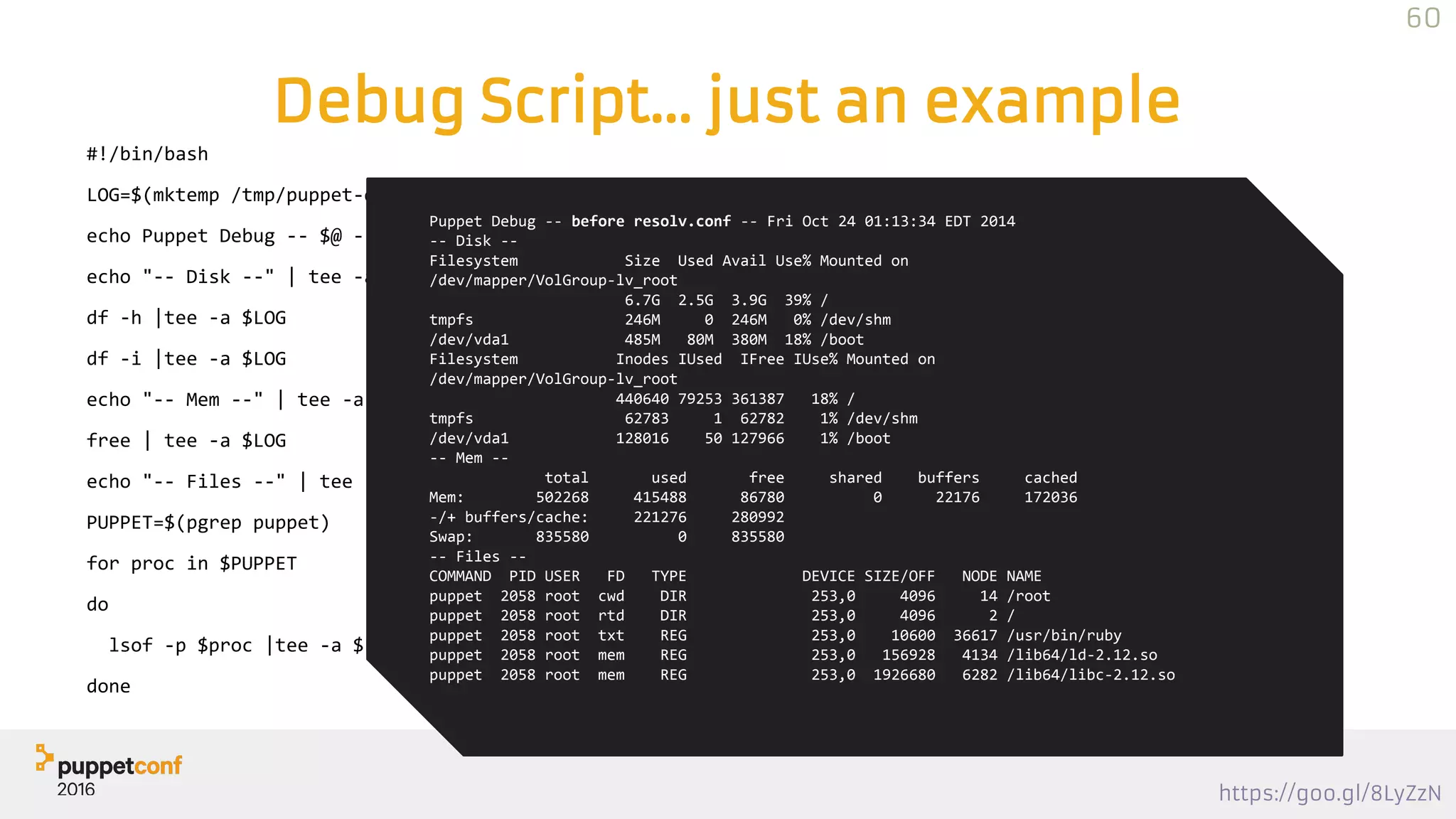
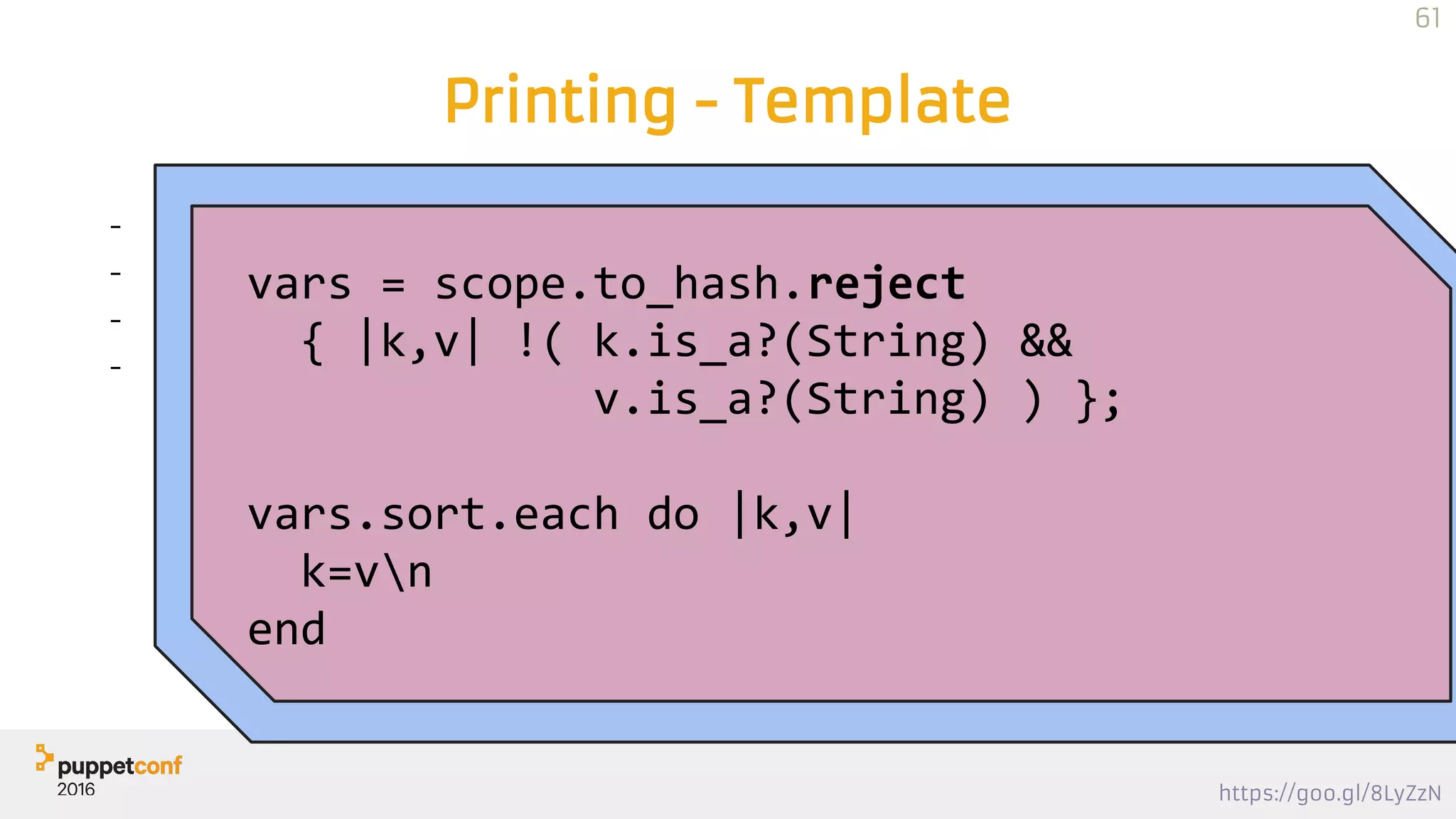

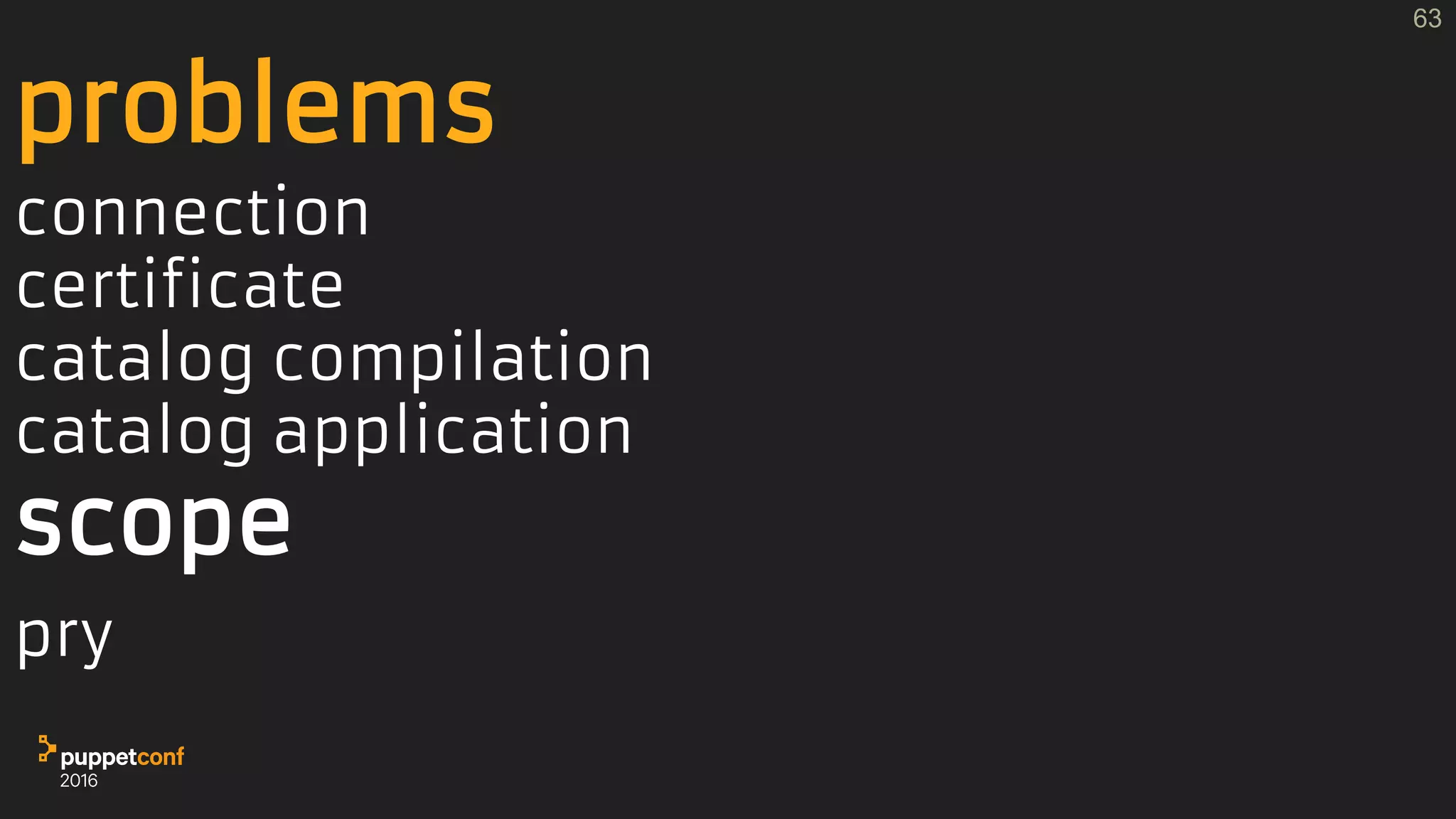
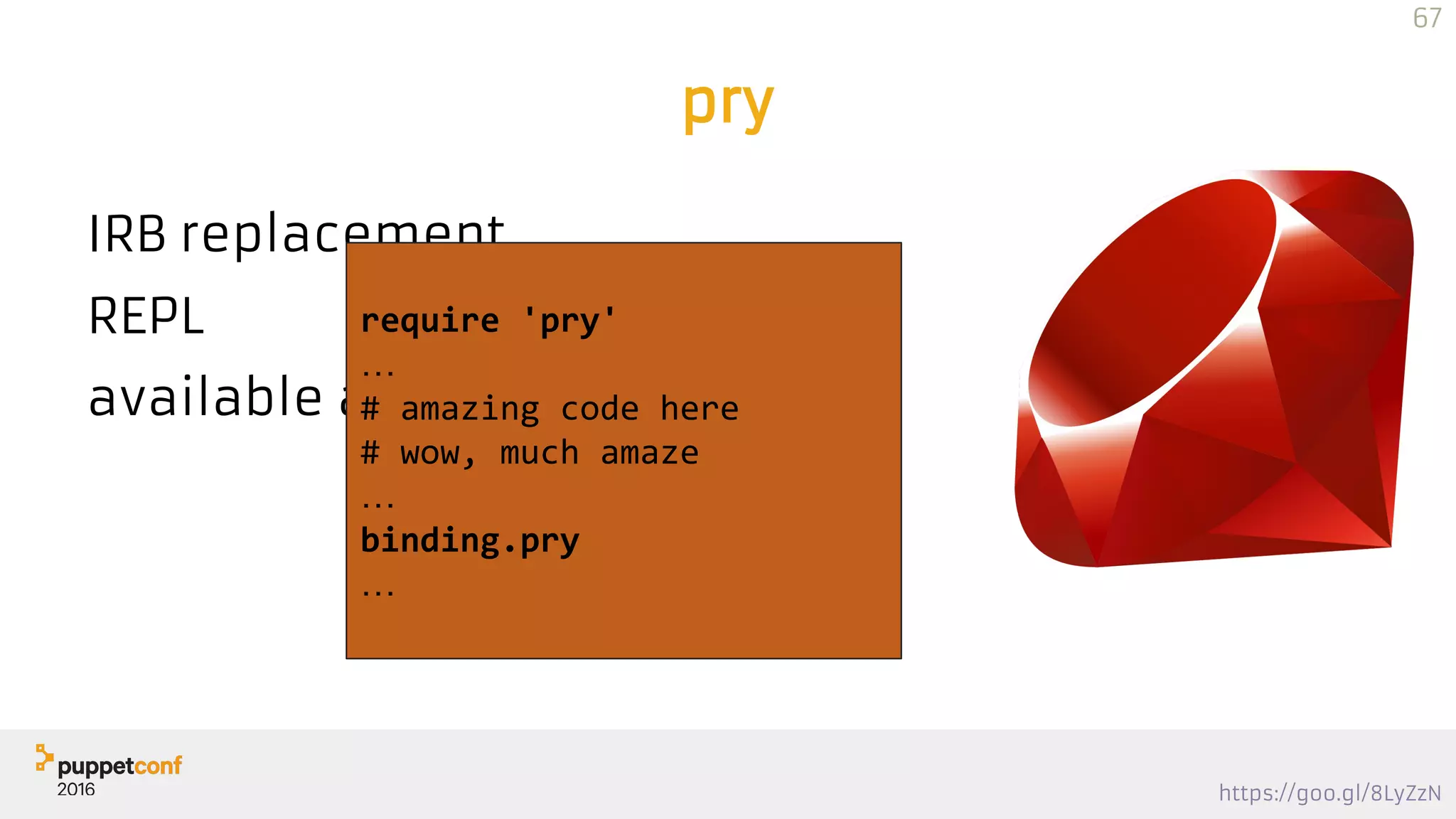
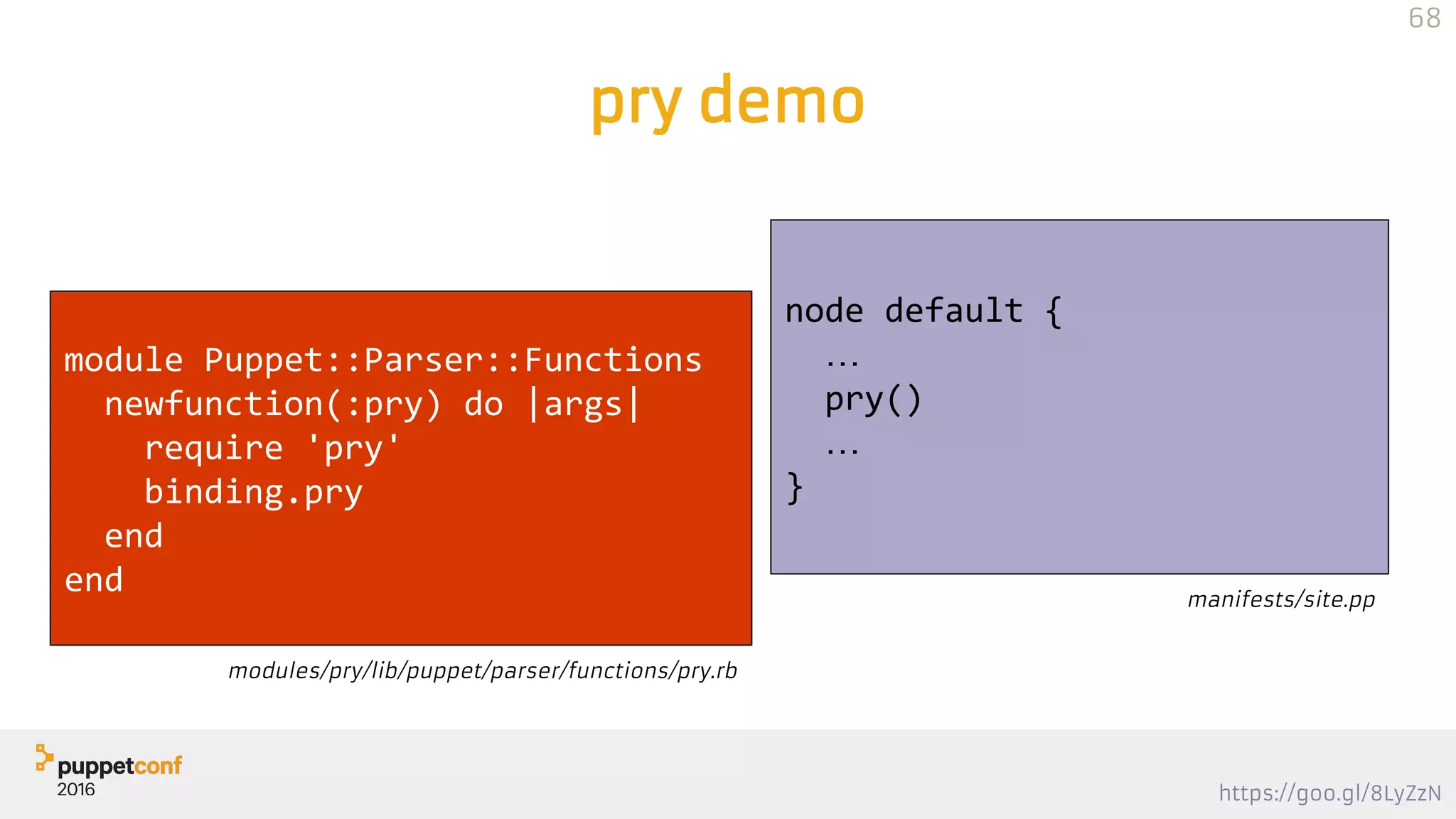
![https://goo.gl/8LyZzN
pry demo
#
69
#
…
From:
/etc/puppetlabs/code/environments/production/modules/pry
/lib/puppet/parser/functions/pry.rb @ line 4
#<Module:0xfb588d1>#real_function_pry:
2: newfunction(:pry) do |args|
3: require 'pry'
=> 4: binding.pry
5: end
[1] pry(#<Puppet::Parser::Scope>)>
puppet agent -tpuppetserver foreground
…
Puppet Server has successfully started and is now ready
to handle requests
exit
…
Puppet Compiled Catalog for xxx.example.com in y.z
seconds
Info: Caching catalog for xxx.example.com
Info: Applying configuration version 'XXX'](https://image.slidesharecdn.com/track2thursuphill-161102164906/75/PuppetConf-2016-Puppet-Troubleshooting-Thomas-Uphill-Wells-Fargo-69-2048.jpg)