The document is a presentation by Thomas Gelf on Puppet's certificate management and security, highlighting the importance of understanding certificates, Public Key Infrastructure (PKI), and certificate lifecycles within the Puppet Enterprise framework. It covers topics such as certificate signing, revocation, and the use of the REST API for managing Puppet environments. Additionally, it provides insights into best practices for security, distributed setups, and potential vulnerabilities associated with Puppet's handling of SSL certificates.








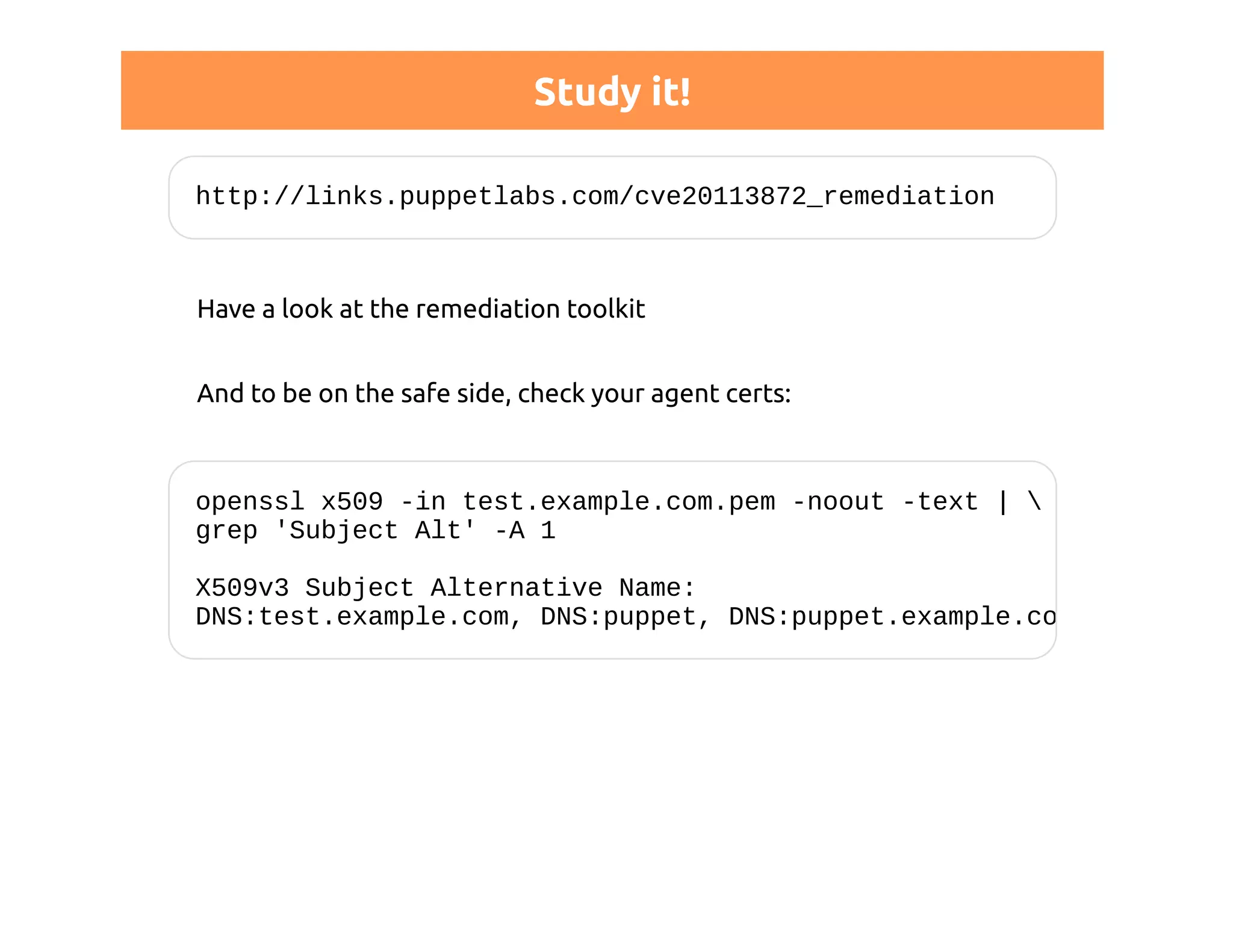
![Permissions
http://docs.puppetlabs.com/guides/rest_auth_conf.html
# auth.conf
# allow all nodes to store their own reports
path ~ ^/report/([^/]+)$
method save
allow $1](https://image.slidesharecdn.com/puppetca-certificatesexplainedthomasgelf-141024045837-conversion-gate02/75/Puppet-Camp-Duesseldorf-2014-Thomas-Gelf-Puppet-CA-certificates-explained-36-2048.jpg)
![Configuration for such a setup
One CA is more than enough:
[master]
ca = false
[agent]
ca_server = ca.example.com
Optionally, still experimental: DNS SRV records](https://image.slidesharecdn.com/puppetca-certificatesexplainedthomasgelf-141024045837-conversion-gate02/75/Puppet-Camp-Duesseldorf-2014-Thomas-Gelf-Puppet-CA-certificates-explained-40-2048.jpg)
![Chain of trust
Since 3.2.1 you can use intermediate CAs to delegate trust
# http://docs.puppetlabs.com/puppet/3/reference
# /config_ssl_external_ca.html
[agent]
ssl_client_ca_auth = $certdir/issuer.pem
Tell Apache about your chain:
SSLCertificateChainFile "/path/to/ca_bundle.pem"](https://image.slidesharecdn.com/puppetca-certificatesexplainedthomasgelf-141024045837-conversion-gate02/75/Puppet-Camp-Duesseldorf-2014-Thomas-Gelf-Puppet-CA-certificates-explained-41-2048.jpg)


![Don't like trouble?
Before generating your CA:
[master]
ca_ttl = 20y
Leave your company in time
NB: expiration > 2038-01-19 == bad idea](https://image.slidesharecdn.com/puppetca-certificatesexplainedthomasgelf-141024045837-conversion-gate02/75/Puppet-Camp-Duesseldorf-2014-Thomas-Gelf-Puppet-CA-certificates-explained-56-2048.jpg)