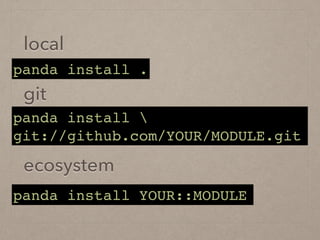
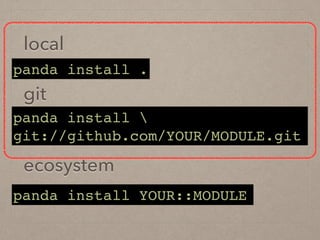
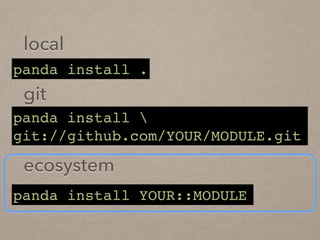
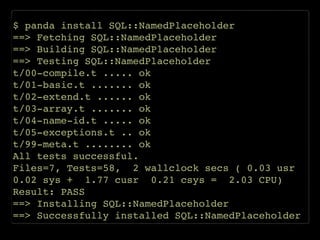
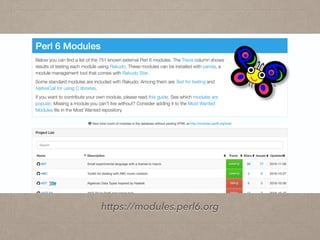
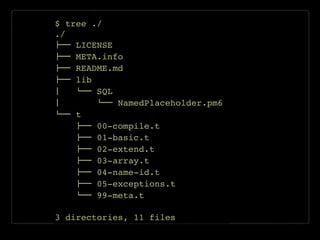
The document discusses how to publish a Perl 6 module. It covers creating modules, writing tests, documenting metadata, installing modules locally or via package managers like panda, and releasing modules to the ecosystem. Key steps include writing Perl 6 code and tests, adding metadata, testing the metadata, pushing to GitHub, and publishing releases to the ecosystem.
![$ curl -s http://ecosystem-api.p6c.org/projects.json | jq '.[] | select( .provides | has("Monitor::Monit"))'
{
"resources": [],
"support": {
"source": "git://github.com/jonathanstowe/Monitor-Monit.git"
},
"tags": [
"monitor",
"api",
"system"
],
"version": "0.0.1",
"test-depends": [
"Test",
"CheckSocket"
],
"auth": "github:jonathanstowe",
"license": "perl",
"perl": "6.c",
"meta6": "0",
"name": "Monitor::Monit",
"build-depends": [],
"authors": [
"Jonathan Stowe <jns+gh@gellyfish.co.uk>"
],
"description": "Provide an interface to the monit monitoring daemon",
"depends": [
"HTTP::UserAgent",
"URI::Template",
"XML::Class"
],
"source-url": "git://github.com/jonathanstowe/Monitor-Monit.git",
"provides": {
"Monitor::Monit": "lib/Monitor/Monit.pm"
}
}](https://image.slidesharecdn.com/20161210yapcltperl6module-161210093346/85/Publishing-a-Perl6-Module-16-320.jpg)
![{
"resources": [],
"support": {
"source": "git://github.com/jonathanstowe/Monitor-Monit.git"
},
...
"auth": "github:jonathanstowe",
"license": "perl",
"perl": "6.c",
"meta6": "0",
"name": "Monitor::Monit",
...
"depends": [
"HTTP::UserAgent",
"URI::Template",
"XML::Class"
],
"source-url": "git://github.com/jonathanstowe/Monitor-Monit.git",
"provides": {
"Monitor::Monit": "lib/Monitor/Monit.pm"
}
}](https://image.slidesharecdn.com/20161210yapcltperl6module-161210093346/85/Publishing-a-Perl6-Module-17-320.jpg)

![use SQL::NamedPlaceholder;!
!
my ($sql, $bind) = bind-named(q[!
SELECT *!
FROM entry!
WHERE!
user_id = :user_id!
], {!
user_id => $user_id!
});!
!
$dbh.prepare($sql).execute(|$bind);](https://image.slidesharecdn.com/20161210yapcltperl6module-161210093346/85/Publishing-a-Perl6-Module-23-320.jpg)
![{!
"name": "SQL::NamedPlaceholder",!
"authors": [ "astj" ],!
"source-url": "ssh://(snip).git",!
"support": {!
"source": "ssh://(snip).git"!
},!
"perl": "6",!
"build-depends": [],!
"provides": {!
"SQL::NamedPlaceholder": "lib/SQL/NamedPlaceholder.pm6"!
},!
"depends": [],!
"test-depends": [!
"Test::META"!
],!
"description": "Perl6 port of p5 SQL::NamedPlaceholder",!
"version": "0.1.0"!
}](https://image.slidesharecdn.com/20161210yapcltperl6module-161210093346/85/Publishing-a-Perl6-Module-27-320.jpg)