- The document discusses various patterns and techniques the author has found useful when working with Puppet modules over 10+ years, including some that may be considered unorthodox or anti-patterns by some.
- Key topics covered include optimization of reusable modules, custom data types, Bolt tasks and plans, external facts, Hiera classification, ensuring resources for presence/absence, application abstraction with Tiny Puppet, and class-based noop management.
- The author argues that some established patterns like roles and profiles can evolve to be more flexible, and that running production nodes in noop mode with controls may be preferable to fully enforcing on all nodes.

![Custom Data Types
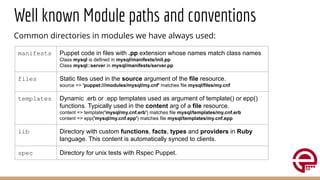
Puppet 4 comes with a rich type system for any kind of data, like:
String, Boolean, Integer, Array, Hash, Pattern, Struct, Undef...
It's possible to create custom data types to filter and validate our data.
They are shipped in the types dir of a module.
They are named and located in the module namespace:
Stdlib::Absolutepath is defined in stdlib/types/absolutepath.pp
New data types can use any other native or custom data type:
type Stdlib::Absolutepath = Variant[Stdlib::Windowspath, Stdlib::Unixpath]
Puppetlabs-stdlib module provide many useful additional data types.
Any module can provide its own types. IE, puppetlabs' ntp/types/poll_interval.pp:
type Ntp::Poll_interval = Integer[4, 17]](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-6-320.jpg)
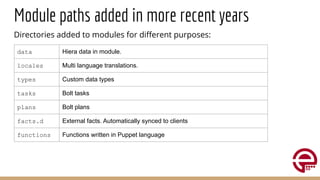
![Bolt Tasks
They are scripts, in any language, which can be remotely executed via Bolt.
They are placed in the tasks dir, for each tasks we have the script and its json
metadata descriptor.
They are namespaced with the module, for example:
tp::test is placed under tp/task/test.sh with meta in tp/task/test.json
Scripts can access arguments via env vars with prefix PT_ or an input json.
tp/task/test.json
{ "description": "Run tp test on target nodes",
"parameters": {
"app": {
"description": "The application to test",
"type": "Optional[String[1]]"
} } }
tp/task/test.sh
#!/usr/bin/env bash
declare tp_options
PATH=$PATH:/usr/local/bin
[[ -n "${PT_app}" ]] && tp_options="${PT_app}"
tp test $tp_options](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-7-320.jpg)
![Plans
Orchestrated set of tasks that can be run on different hosts based on custom
logic according to the exit status of other runs.
They can be written in Yaml or in Puppet language and are shipped in the
plans dir.
Puppet plans have .pp extension and syntax similar to classes:
plan amazon_aws::create_kubernetes_cluster is defined in
amazon_aws/plans/create_kubernernes_cluster.pp
Can have parameters and special functions like run_task or run_puppet:
plan amazon_aws::create_kubernetes_cluster(
String[1] $cidr_block, [...]
) {
$responses=run_task("amazon_aws::iam_aws_list_roles", "localhost")
$role_list=$responses.first.value["roles"]
[...]](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-8-320.jpg)
![Functions in Puppet language
Are placed in the functions directory, have .pp extension and are written in Puppet
language. Their syntax is similar to classes or defines. For example, the function
psick::template is defined in psick/functions/template.ppand can look as follows:
function psick::template(
Optional[String] $filename,
Hash $parameters = {}
) >> Optional[String] {
if $filename and $filename !='' {
$ext=$filename[-4,4]
case $ext {
'.epp': { epp($filename, { parameters => $parameters } ) }
'.erb': { template($filename) }
default: { file($filename) }
}
} else {
undef
}
}](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-10-320.jpg)
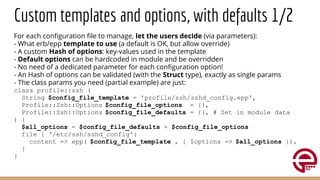
![Custom templates and options, with defaults 2/2
User Hiera data, in the control-repo, can look as follows:
profile::ssh::config_file_options:
'PermitRootLogin': 'yes'
In the module Hiera data we can set the default options:
profile::ssh::config_file_defaults:
'PermitRootLogin': 'no'
'ListenAddress': "%{facts.networking.ip}"
The used epp template can be as follows:
PermitRootLogin <%= $options['PermitRootLogin'] %>
ListenAddress <%= $options['ListenAddress'] %>
The custom Profile::Ssh::Options type to validate the above can be like:
type Profile::Ssh::Options = Struct[{
Optional[PermitRootLogin] => Enum['yes','no'],
Optional[ListenAddress] => Stdlib::IP::Address, [...] ]}](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-17-320.jpg)
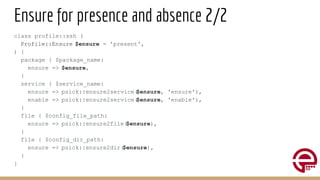
![Ensure for presence and absence 1/2
Puppet manages what we tell it to manage.
Any resource added in a class should be easily removable.
Any class should have an $ensure parameter which:
● Is applied AS IS to the managed package(s) to eventually allow Hiera
driven management of the version to install, or use latest
● Is adapted via custom functions for the other resources.
When you have to remove what a class has added, is enough to set on Hiera:
class_name::ensure: 'absent'
A Custom data type can be created to validate the possible values for $ensure:
type Profile::Ensure = Variant[ Boolean,
Enum['present', 'absent', 'latest'],
Pattern[/d+(.d+)*/]]](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-18-320.jpg)
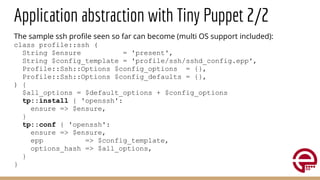
![Application abstraction with Tiny Puppet 1/2
Puppet is about abstracting resources from the underlying OS.
Tiny Puppet (example42-tp) is about abstracting applications.
It provides defines that can manage installation and configuration of
potentially any application on any OS, managing also the relevant package
repositories or dependencies, and leaving to used full freedom to manage
files in the way we want.
Can replace, potentially, any module where just packages, services and files
are managed.
Tiny Puppet is ideal for the sysadmin who knows how to configure her/his
files and wants to have freedom in choosing how to manage them (erb/epp
templates, source, content...) without having to study a dedicated module and
make it do what [s]he wants.](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-20-320.jpg)
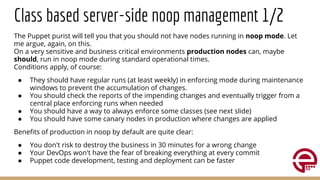
![Class based server-side noop management 2/2
We can control noop behaviour for each class, leveraging on trlinkin-noop module
with params as follows in a class:
class profile::ssh (
Boolean $noop_manage = false,
Boolean $noop_value = false,
) {
if $noop_manage {
noop($noop_value)
}
[... class resources ...] }
When profile::ssh::noop_manage: true the noop() function is invoked with
the $noop_value which adds the noop metaparameter to all the resources in the
same scope. This, according to $noop_value allows to:
● false Enforce application of the class resources also when client runs in noop
● true Test in noop mode the class resources when client runs normally](https://image.slidesharecdn.com/modulesofthetwenties-210415155301/85/Modules-of-the-twenties-23-320.jpg)