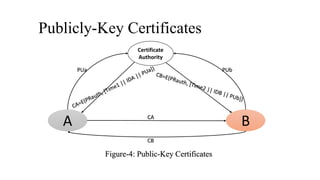
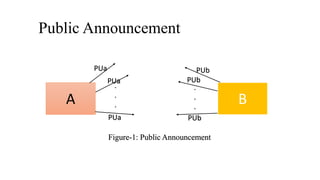
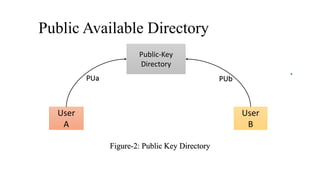
This presentation discusses public key distribution and describes four common methods: public announcement, public directory, public key authority, and public key certificates. Public announcement allows users to broadcast their public keys but is vulnerable to forgery. A public directory provides a trusted central location for keys but can be tampered with. A public key authority further secures the directory by requiring validation through its public key. Public key certificates bind identities to keys with a digital signature from a certificate authority, allowing verification without real-time access to the authority.




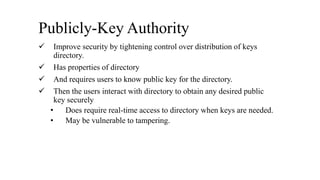
![Publicly-Key Authority
Public-Key
Authority
A B
Figure-3: Public-Key Authority
(3)E(PUb, [IDA || N1])
(6)E(PUa, [N1 || N1])
(7)E(PUb, N2)](https://image.slidesharecdn.com/150147-181011072431/85/Public-Key-Distribution-10-320.jpg)